Professional Documents
Culture Documents
Integrating SRX Security in A QFabric Switch Data Center
Uploaded by
Michael LeonardOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Integrating SRX Security in A QFabric Switch Data Center
Uploaded by
Michael LeonardCopyright:
Available Formats
IMPLEMENTATION GUIDE
INtegratINg SrX SerIeS ServICeS gatewayS INto a QFabrIC SwItCh-baSed data CeNter ImplemeNtatIoN guIde
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Table of Contents
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4 Scope . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4 target audience . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4 SrX technical Concepts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4 Security Zones and Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5 Security policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5 ha Chassis Clusters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5 redundancy groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5 redundant ethernet Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6 redundancy group Failover . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6 QFabric System hardware architecture overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6 QFabric and SrX Integration design overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7 use Case 1: QFabric in l2 mode, SrX as the Fhr . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8 use Case 2: QFabric in l2 or l3, vr-based traffic Steering to the SrX . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9 use Case 3: SrX as a low-latency Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10 physical and logical topologies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11 QFabric in l2 mode, SrX as Fhr . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 QFabric in l3 mode, vr-based traffic Steering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13 Implementation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .14 QFabric Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .14 Interface Naming Conventions for QFabric technology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 Interface type Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 SrX Series Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .16 Configuring Inter-vr routing on the SrX Series . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .18 Connecting the SrX Cluster with the QFabric Solution . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20 Ip routing between the SrX Series and QFabric Solution . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20 enabling Services offload (low-latency Firewall) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23 appSecure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25 Configuring appSecure Intrusion policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25 validation testing and Convergence testing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27 Summary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27 appendix a: Configuration Files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28 use Case 1: QFabric in layer 2, SrX as Fhractive/passive and active/active Cluster modes . . . . . . . . . . . . . . . . . . . . . . . 28 QFabric layer 2 Configuration (QF-2pS.conf) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28 SrX delta Configuration to Convert an active/passive Cluster to active/active . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52 use Case 2: QFabric in layer 3 mode, vr-based traffic Steering to SrX as Needed . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52 QFabric Configuration for layer 3 mode with Static routing (QF-3pS-static.conf) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52 SrX Configurationactive/passive Cluster (SrX-3pS-static) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68 use Case 3: SrX with Services offload . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82 SrX delta Configuration for enabling Services offload . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82 appendix b: QFabric Interfaces for Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83 QFabric Interfaces for eX Switches . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83 about Juniper Networks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
List of Figures
Figure 1: QFabric in l2 mode, SrX Series as the Fhr . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8 Figure 2: QFabric in l2 or l3 mode, SrX Series used as firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9 Figure 3: example of data center architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11 Figure 4: QFabric as l2 switch and SrX as Fhr . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 Figure 5: QFabric in l3 mode, SrX for security services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13 Figure 6: Network security zones . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .18 Figure 7: QFabric and SrX links, reth interface and lag . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
List of Tables
table 1: Juniper Networks products used . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11 table 2: Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 table 3: test equipment: traffic generators . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 table 4: Ip and Network address Scheme . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .14
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Introduction
the data center is one of the most intensive deployment locations for networking equipment, consisting of thousands of servers that are accessed by tens of thousands of client systems. the need for large-scale access creates a complex set of data flows and makes it challenging to define the specific profile of network traffic. moreover, because determining firewall deployment and sizing in a data center is a massive effort, firewalls are often deployed in a limited fashion, if deployed at all. another driving factor in the limited use of firewalls is the lack of performance. raw bandwidth limitations, connections per second, and sustained connections have caused architects to distribute security or dispense with it altogether. to address these challenges, Juniper Networks has created a new class of security products. Juniper Networks SrX Series Services gateways provide the ability to scale in ways that were not thought possible in the past. Juniper has leveraged key technologies, such as the Juniper Networks Junos operating system and proven hardware architectures, to create the SrX Series of products. the SrX Series meets the demanding needs of data centers today, with the ability to expand and address customers needs of tomorrow. with the high-end SrX Series gateway products, firewall deployment in the data center becomes natural and reasonable. this document describes various SrX deployment options in a Juniper Networks QFabric technology-based data center.
Scope
this document provides various design considerations and implementation guidelines to deploy firewall services in the QFabric switch-based data center using high-end SrX Series Services gateways. the firewall services in the data center core can provide additional security and help meet compliance requirements by segmenting deployed server networks and securing traffic within server networks. this document briefly reviews the technical concepts of the SrX Series Services gateways related to design and implementation of firewall services. deployment scenarios are based on a single logical switch design. the deployment scenarios and design considerations include: active/passive firewall cluster deployment with SrX acting as the first-hop router (Fhr) for QFabric active/active firewall cluster deployment with SrX acting as the Fhr for QFabric active/passive firewall cluster deployment with QFabric acting as the Fhr for intravirtual router traffic active/active firewall cluster deployment with QFabric acting as the Fhr for intravirtual router traffic active/passive low-latency firewall deployment for latency-sensitive applications In addition, the implementation steps and validated configuration details for the deployment scenarios are presented. the designs were tested for transit traffic latency over various paths that network traffic might take during normal operations in the event of a failure. the designs were validated for convergence for various failure scenarios, such as link failure, network infrastructure device failure, and firewall node failure, to ensure required resiliency. the SrX Series Services gateways support all major dynamic routing protocols. For network integration, we used oSpF as the dynamic routing protocol. For performance and scalability details concerning the SrX Series Services gateways and QFabric, contact your local Juniper account representative. Note: the Juniper Networks mX Series 3d universal edge routers are represented in the diagrams for completeness, however, the mX Series configuration is out of the scope of this document.
Target Audience
this document is intended for architects, network engineers and operators, and those who require technical knowledge regarding integrating the SrX Series with QFabric technology. It is assumed that the reader is familiar with the Junos operating system, knowledgeable about the QFabric family of products, and has basic familiarity with firewall products.
SRX Technical Concepts
the following technical concepts are related to the SrX Series and relevant to firewall deployment: Security zones and interfaces Security policies high availability (ha) chassis clusters redundancy groups redundant ethernet interfaces redundancy group failover
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Security Zones and Interfaces
Interfaces act as a doorway through which traffic enters and exits an SrX Series gateway appliance. many interfaces can share the same security requirements; however, different interfaces can also have different security requirements for inbound and outbound data packets. you can group interfaces with identical security requirements together into a single security zone. Security zones are logical entities to which one or more interfaces are bound. on a single device, you can configure multiple security zones, dividing the network into segments to which you can apply various security options to satisfy the needs of each segment. Security zones also allow administrators to group network addresses in an abstract construct of security zones and define security policies for inter-zone traffic. this approach reduces or eliminates the need for maintaining address lists for security policy. to achieve this, you must define at least two security zones to protect one area of the network from the other. If all interfaces on the firewall share a single security zone, the security policy is defined as an intra-zone policy, and administrators must maintain an address list to specify the source and destination for the security policies. this can be helpful for migrating existing security policies from another firewall platform.
Security Policies
Security zones are the building blocks for security policies. a security zone is a logical entity to which one or more interfaces are bound. a security zone provides a means of distinguishing groups of hosts (user systems and other hosts, such as servers) and their resources from one another to apply different security measures to them. active security policies enforce rules for the transit traffic in terms of which traffic can pass through the firewall, and the actions that must occur on the traffic as it passes through the firewall. by default, a device denies all traffic in all directions. through the creation of policies, you can control the traffic flow from zone to zone by defining the kinds of traffic permitted to pass from specified sources to specified destinations at scheduled times. at the broadest level, you can allow all kinds of traffic from any source in one zone to any destination in all other zones without any scheduling restrictions. at the narrowest level, you can allow only one kind of traffic between a specified host in one zone and another specified host in another zone during a scheduled time interval.
HA Chassis Clusters
to form a chassis cluster, a pair of identical SrX Series devices are combined to act as a single system that enforces the same overall security. For Juniper Networks SrX5600 Services gateway and Juniper Networks SrX5800 Services gateway chassis clusters, the placement and type of Services processing Cards (SpCs) must match in the two clusters. when a device joins a cluster, it becomes a node of that cluster. with the exception of unique node settings and management Ip addresses, nodes in a cluster share the same configuration.
Redundancy Groups
Chassis clustering provides ha of interfaces and services through redundancy groups and primacy within groups. a redundancy group is an abstract construct that includes and manages a collection of objects. It contains objects on both nodes, acting as the primary on one node and backup on the other at all times. when a redundancy group is primary, its objects on that node are active. a redundancy group can be primary on only one node at a time. redundancy groups are independent units of failover. each redundancy group fails over from one node to the other, independent of other redundancy groups. when a redundancy group fails over, all its objects fail over together. three characteristics determine the primacy of a redundancy group: priority configured for the node Node Id (in case of tied priorities) order in which the node comes up Note: If a lower priority node comes up first, it assumes the primacy for a redundancy group and remains as primary if preempt is not enabled. a chassis cluster can include many redundancy groups, some of which might be primary on one node and some primary on another node. alternatively, all redundancy groups can be primary on a single node. one redundancy groups primacy does not affect another redundancy groups primacy. when you initialize a device in chassis cluster mode, the system creates a redundancy group referred to in this document as redundancy group 0. redundancy group 0 manages the primacy and failover between the routing engines on each node of the cluster. the node on which redundancy group 0 is primary determines which routing engine is active in the cluster. a node is considered the primary node of the cluster if its routing engine is the active one.
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
you can configure up to 128 redundancy groups, numbered 1 through 128. each redundancy group contains one or more redundant ethernet interfaces. a redundant ethernet interface is a pseudointerface that contains a pair of physical gigabit ethernet or Fast ethernet interfaces. If a redundancy group is active on node 0, the child links of all associated redundant ethernet interfaces on node 0 are active. If the redundancy group fails over to node 1, the child links of all redundant ethernet interfaces on node 1 become active. you can configure multiple redundancy groups to load-share traffic across the cluster. the traffic for a redundancy group is processed on the node where the redundancy group is active. because more than one redundancy group can be configured, it is possible that the traffic from some redundancy groups is processed on one node, while the traffic for other redundancy groups is processed on the other node, depending on where the redundancy group is active. multiple redundancy groups make it possible for traffic to arrive over an interface of one redundancy group and egress over an interface that belongs to another redundancy group. In this situation, the ingress and egress interfaces might not be active on the same node. when this happens, the traffic is forwarded over the fabric link to the appropriate node. when you configure a redundancy group, you must specify a priority for each node to determine the node on which the redundancy group is primary. the node with the higher priority is selected as primary. the primacy of a redundancy group can fail over from one node to the other. when a redundancy group fails over to the other node, its redundant ethernet interfaces on that node are active and passing traffic.
Redundant Ethernet Interfaces
a redundant ethernet interface is a pseudointerface that includes a physical interface from each node of the cluster. the interface can contain either a pair of Fast ethernet or gigabit ethernet interfaces that are referred to as child interfaces of the redundant ethernet interface (the redundant parent). each redundant ethernet interface can contain only two interfaces, because a cluster contains only two nodes. a redundant ethernet interfaces child interface is associated with the redundant ethernet interface as part of the child interface configuration. the redundant ethernet interfaces child interface inherits most of its configuration from its parent. a redundant ethernet interface inherits its failover property from the redundancy group to which it belongs. a redundant ethernet interface remains active as long as its primary child interface is available and active.
Redundancy Group Failover
For a redundancy group to automatically fail over to another node, its interfaces must be monitored. when you configure a redundancy group, you can specify a set of interfaces that the redundancy group monitors for status (or health) to determine whether the interface is up. a monitored interface can be a child interface of any of its redundant ethernet interfaces. when you configure a monitored interface, you give it a weight. every redundancy group has a threshold tolerance value initially set to 255. when a monitored interface becomes unavailable, its weight is subtracted from the redundancy groups threshold. when the redundancy groups threshold reaches 0, it fails over to the other node. For example, if redundancy group 1 is primary on node 0, on the thresholdcrossing event, redundancy group 1 becomes primary on node 1, and all the child interfaces of its redundant ethernet interfaces begin traffic handling. If the monitored interfaces of a redundancy group on both nodes reach their thresholds at the same time, the redundancy group is primary on the node with the lower node Id, in this case node 0.
QFabric System Hardware Architecture Overview
the QFabric system is a single-layer networking tier that connects servers and storage devices to one another across a high-speed, unified core fabric. you can view the QFabric system as a single, extremely large, nonblocking, highperformance layer 2 and layer 3 switching system. the director software running on the director group allows the main QFabric system administrator to access and configure every device and port in the QFabric system from a single location. although you configure the system as a single entity, the fabric contains four major hardware components. the hardware components can be chassis-based, group-based, or a hybrid of the two. It is important to understand the components and their functions. Director groupa management platform that establishes, monitors, and maintains all components in the QFabric system. a set of director devices run the Junos oS on top of a CentoS foundation. the director group handles tasks such as QFabric system network topology discovery, node and interconnect device configuration and startup, and domain Name System (dNS), dynamic host Configuration protocol (dhCp), and Network File System (NFS) services. the director group also runs the software for management applications, hosts and load-balances internal processes for the QFabric system, and starts additional QFabric system processes as requested.
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Node devicea hardware system located on the ingress of the QFabric system that connects to endpoints (such as servers or storage devices) or external networks, and is connected to the heart of the QFabric system through an interconnect device. you can use a node device similar to how a top-of-rack switch is implemented. by default, node devices connect to servers or storage devices. however, when you group node devices together to connect to a network that is external to the QFabric system, the formation is called a network node group. Interconnect devicethe primary fabric for data plane traffic traversing the QFabric system between node devices. to reduce latency to a minimum, the interconnect device implements multistage Clos switching (Clos refers to a specific type of circuit switching network, first formalized by Charles Clos in1953) to provide nonblocking interconnections between any node device in the system. Control plane networkan out-of-band gigabit ethernet management network that connects all QFabric system components. For example, you can use a group of eX4200 ethernet switches configured as a virtual Chassis to enable the control plane network. the control plane network connects the director group to the management ports of the node and interconnect devices. by keeping the control plane network separate from the data plane, the QFabric system can scale to support thousands of servers and storage devices. For more information about the QFabric hardware and software architecture, see: www.juniper.net/techpubs/en_US/junos11.3/information-products/pathway-pages/qfx-series/qfabric-deployment. html
QFabric and SRX Integration Design Overview
the following use cases show scenarios for a QFabric and SrX integration: QFabric technology in layer 2 (l2) mode, SrX as the Fhr QFabric technology in l2 or layer 3 (l3) mode, virtual routerbased traffic steering SrX Series services offload feature providing a low-latency firewall the SrX Series, which is deployed as a one-arm solution in the three use cases, is sometimes referred to as a firewall on a stick configuration. administrators have the flexibility to selectively define which traffic gets protection through the firewall or bypasses the firewall for certain types of traffic using routing policy configuration. l3 termination can be at the firewall, and inter-vlaN traffic is routed by the firewall. this configuration ensures that traffic to and from vlaNs is always protected using firewall services. For applications that do not require firewall protection, or in cases where sending traffic through firewalls breaks the application (legacy application), vlaNs hosting these applications can be terminated on the QFabric solution or on the mX Series, and communication among the vlaNs can bypass the firewalls. with a one-arm firewall deployment, administrators can virtually keep the firewall inline by terminating the vlaN at the firewall or configuring the routing on the QFabric solution to always send intervirtual routing traffic through the firewall. administrators can also selectively bypass traffic using routing policy control. because this configuration provides flexible deployment options, we will explore the design options with one-arm firewall deployment solutions.
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Use Case 1: QFabric in L2 Mode, SRX As the FHR
In this deployment scenario, the first-hop router (Fhr) is either the SrX Series or the mX Series, depending on which traffic needs firewall policies (or any other l3 equipment). the QFabric solution is strictly an l2 connection, as shown in Figure 1.
With SRX Service INTERNET MPLS/VPN Without SRX Service
IRB RVI Layer 3 Layer 2 MX Series Junos OS IRB
SRX Series
FINANCE
ENGINEERING
MARKETING
Servers
Figure 1: QFabric in L2 mode, SRX Series as the FHR
Storage
In this scenario, only finance servers require the SrX Series security services, so the routing for finance resides on the SrX Series, and the routing for engineering and marketing resides on the mX Series. the SrX Series serves as the Fhr for the finance servers, and the mX Series is the Fhr for the engineering and marketing servers. all traffic from and to finance servers must go through the SrX Series for security policy enforcement. the advantages of this deployment are: large table scale, such as host tables and media access control (maC) address table. using a QFabric solution in l2 mode allows you to use an external routing layer with higher table scales, such as the mX Series. Simple configuration model. each appliance has a dedicated role. the mX Series and the SrX Series handle the routing, the SrX Series handles security, and the QFabric solution handles l2 processing. only a vlaN configuration is required. appropriate design when vlaNs must span different geographic data centers. this deployment also has some drawbacks. traffic that must be routed (inside the QFabric solution) needs to go across the mX Series or SrX Series before returning to the QFabric solution, thus increasing latency and bandwidth consumption.
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Use Case 2: QFabric in L2 or L3, VR-based Traffic Steering to the SRX
In this scenario, the mX Series is the gateway to the outside world, and the SrX Series is used for services. the QFabric solution is the default gateway for the servers.
With SRX Service INTERNET MPLS/VPN
VR-A
Zone A
Layer 3 Layer 2
IRB
IRB
IRB
IRB
MX Series
SRX Series
FINANCE
VR-A
HR
ENGINEERING
VR-B
MARKETING
Servers
Figure 2: QFabric in L2 or L3 mode, SRX Series used as firewall the advantages of this deployment are:
Storage
low and consistent latency for routing because routing happens closer to the endpoints (servers)inside the QFabric solution if no SrX Series services are needed. Full separation of the data center from the outside world, with the mX Series as the gateway between them, and dedicated to Internet-bound traffic only and leveraging advanced features (mplS/vplS). only intervirtual router (vr) traffic that needs security services goes to the SrX Series for security policy enforcement. only traffic that needs to reach the outside world exits the QFabric system. the drawbacks to this deployment are: Splitting the routing functionality between three devices makes the configuration more complex than use Case 1. vrs must be used on the QFabric side for traffic isolation, with a correct mapping of the traffic to the appropriate security zone on the SrX Series or to the appropriate integrated routing and bridging (Irb) on the mX Series. limited table scale, such as host tables. If a customer wants to create a security zone on a per vr basis and apply those security policies to inter-vr traffic, the QFabric solution must act as the Fhr, and the SrX Series is used for firewall and other security services only. to avoid capacity or scaling problems, administrators should take into account that the QFabric solution must route a significantly higher volume of traffic that does not require services.
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Note: In traditional data center architectures, virtual router redundancy protocol (vrrp) is required to secure gateway redundancy for l3 devices. however, with the QFabric architecture, vrrp is not necessary because a QFabric solution is a single logical switch, therefore multiple devices running as gateways are not required. within a network node group, high availability of a gateway is built in already. For example, in Figure 6, the SrX Series cluster connects to two QFabric nodes, which are part of a network node group. to the SrX Series cluster, it is the same as connecting to different ports on different line cards on a single switch. these line cards and ports are fully synchronized at the QFabric director level. because protocols are not needed to ensure switchover between devices, users do not have to configure vrrp among network node groups.
Use Case 3: SRX As a Low-Latency Firewall
Implementing firewalls within the data center has always been a challenge because firewalls usually introduce considerable latency because they have to analyze the packets for security processing. often times, latency-sensitive applications are bypassed for this reason. Juniper Networks offers a low-latency firewall solution that works in conjunction with QFabric technology, which has interface-to-interface latency of approximately 2 microseconds (ms) at small scale, growing slowly to about 10 ms at the largest scale. this use case deploys the SrX Series as a low-latency firewall with QFabric technology in customer environments in which business applications require segmentation while still maintaining extremely low latency. the SrX Series offers the licensed software feature, services offloading, which provides a mechanism for achieving low latency where it is desired. Services offloading processes fast-path packets in the network processor instead of in the Services processing unit (Spu). this method reduces the latency that arises when packets are forwarded from network processors to Spus for processing and back to I/o cards (IoCs) for transmission. Services offloading reduces packet-processing latency by 500% to 600%. when the first packet arrives at the interface, the network processor forwards it to the Spu. If the Spu verifies that the traffic is qualified for services offloading, a services-offload session is created on the network processor, and subsequent fast-path packets are processed in the network processor. If the traffic does not qualify for services offloading, a normal session is created on the network processor. Note: Services offloading is supported only on the SrX1400 Services gateway and the SrX3000 and SrX5000 lines with Flex IoC in the Junos oS release 11.4. Services offloading has certain limitations. For more information, see the Junos oS release Notes limitations section.
10
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Physical and Logical Topologies
Figure 3 shows the high-level physical topology of the lab validation test configuration. the tables list the products and software used.
WAN Edge / WAN Services
MX480
QFX3500 for WAN Edge
Security Services
EX4200 Virtual Chassis for OoB Management
QFX3500 for Security Services QFabric Interconnect QFabric Directors
SRX Series Cluster
QFX3500 as ToR for Connecting Servers EX4200 Virtual Chassis as ToR for Connecting Servers with 1G Connections
Rack Mount Servers, 10G Dual-homed
Servers, 10G Dual-homed
Servers, 1G Dual-homed to EX Series Virtual Chassis
Figure 3: Example of data center architecture
Table 1: Juniper Networks Products Used
Device
QFX3500 QFX3008-I QFX3100 eX4200-48t SrX5800
Description and Quantity
QFabric Node (8) QFabric Interconnect (2) QFabric director (2) virtual chassis for management connections of QFabric components (8) and highdensity servers with 1 g connections. (2) high-end appliance (2 chassis in the cluster) SrX5k re-13-20 (1+1, total two in the cluster) SrX5k dpC 4X 10ge (2+2, total four in the cluster) SrX5k SpC (2+2, total four in the cluster) SrX5k Flexible IoC (1+1, total two in the cluster) SrX5k FIoC 4x10ge port module (1+1, total two in the cluster) mX Series 3d universal edge router re-S-2000 (quantity 2+2, total four in test bed) mpC 3d 16x 10ge (quantity 1+1, total 2 in test bed)
Software Version
Junos 11.3X30 Junos 11.3X30 Junos 11.3X30 Junos 12.1r2.9 Junos 12.1r2
mX480
Junos 12.1r2
Copyright 2013, Juniper Networks, Inc.
11
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Table 2: Servers
Device
Ibm x3550 m4
Description and Quantity
rack mount x Series server with 10g NIC/CNas (emulex, Intel)
Software Version
mS windows Server 2008r2 x64 Sp1 CentoS linux mS windows Server 2008r2 x64 Sp1
Ibm hS22 blade in bC type h
blade server with Xeon Cpu and 10g CFF NIC/CNa (emulex/Intel/Qlogic)
Table 3: Test Equipment: Traffic Generators
Device
Spirent test Center
Description and Quantity
Spirent test Center with 1g and 10g ports, for l2/l3 and l4/l7 traffic
Software Version
3.90 for l4/7 3.95 for l2/l3
QFabric in L2 Mode, SRX As FHR
In this configuration, the QFabric solution is in l2 mode, and the server vlaNs (111-113,121-123, 211-213, and 221-223) are terminated on two virtual routers (a and b) on the SrX Series. as shown in Figure 4, vr-C on the SrX Series represents the Internet virtual router that is used for communicating with the mX Series for the Internet and connections to other data centers. vr-a has two zones: a1 and a2. vr-b has two zones: b1 and b2.
MX Series VR-C SRX Series
VR-C
Zone C1
301 302 303
10.210.1.0/24 10.210.2.0/24 10.210.3.0/24
QFabric
VR-B
Zone B2 Zone B1
223 222 221 213 212 211
10.210.223.0/24 10.210.222.0/24 10.210.221.0/24 10.210.213.0/24 10.210.212.0/24 10.210.211.0/24
VR-A
Zone A2 Zone A1
123 122 121 113 112 111
10.210.123.0/24 10.210.122.0/24 10.210.121.0/24 10.210.113.0/24 10.210.112.0/24 10.210.111.0/24
Zone Zone Zone A1 A2 B1
Zone B2
Figure 4: QFabric as L2 switch and SRX as FHR
12
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
QFabric in L3 Mode, VR-based Traffic Steering
In this configuration, the QFabric solution is in l3 mode, and the server vlaNs (111-113,121-123, 211-213, and 221-223) are terminated on four virtual routers ( a1, a2, b1, and b2) on the QFabric solution, as shown in Figure 5. Intravirtual routing is handled by the QFabric solution. when a server from one virtual router wants to communicate with another server in another virtual router, it must go through the SrX appliance for security policy evaluation and enforcement. vr-a on the SrX Series provides the routing for the inter-vr traffic between vr-a1 and vr-a2. vr-a has security zones (a1, a2) on the SrX Series. Similarly, vr-b provides the routing for intervirtual router traffic between vr-b1 and vr-b2. vr-C on the SrX Series represents the Internet virtual router used for communicating with the mX Series for the Internet and connections to other data centers. vr-a and vr-b on the SrX Series never communicate directly to the outside world. they go through vr-C for security purposes.
MX Series VR-C SRX Series VR-C
Zone C1 301 302 303 10.210.1.0/24 10.210.2.0/24 10.210.3.0/24
QFabric
VR-B
Zone B2 Zone B1
220 210
10.210.220.0/24 10.210.210.0/24 VR-B1 10.210.211.0/24 10.210.212.0/24 10.210.213.0/24 Zone B1
VR-B2 10.210.221.0/24 10.210.222.0/24 10.210.223.0/24 Zone B2
VR-A
Zone A2 Zone A1
120
10.210.120.0/24
VR-A2 10.210.111.0/24 10.210.112.0/24 10.210.113.0/24 10.210.121.0/24 10.210.122.0/24 10.210.123.0/24 VR-A1 111 113 112 Zone A1 Zone A2
110
10.210.110.0/24
123 123 123 122 122 122 121 121 121
Figure 5: QFabric in L3 mode, SRX for security services table 4 lists the Ip addresses and network addressing schemes used for both the validation configuration and the logical diagrams (Figures 4 and 5). appendix a provides the QFabric and SrX Series configurations for the three use cases. Note: the networks in table 4 were used for the QFabric solution as the l2 switch (use Case 1). this information is helps understand the logical topologies depicted in Figures 4 and 5 and the device configurations in appendix a.
Copyright 2013, Juniper Networks, Inc.
13
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Table 4: IP and Network Address Scheme
Network IPv4 Space VLAN Virtual Router on SRX Series
vra vra vra vra vra vra vra vra vrb vrb vrb vrb vrb vrb vrb vrb vrC vrC vrC
Security Zone on SRX Series
a1 a1 a1 a1 a2 a2 a2 a2 b1 b1 b1 b1 b2 b2 b2 b2 C1 C1 C1
Virtual Router on QFabric
vra1 vra1 vra1 vra1 vra2 vra2 vra2 vra2 vrb1 vrb1 vrb1 vrb1 vrb2 vrb2 vrb2 vrb2 -
For Hosts or Infrastructure
Infrastructure. (SrX-QF) hosts hosts hosts Infrastructure. (SrX-QF) hosts hosts hosts Infrastructure. (SrX-QF) hosts hosts hosts Infrastructure. (SrX-QF) hosts hosts hosts Infrastructure. (SrX-QF-mX) Infrastructure. (SrX-QF-mX) Infrastructure. (SrX-QF-mX)
net110 net111 net112 net113 net120 net121 net122 net123 net210 net211 net212 net213 net220 net221 net222 net223 net301 net302 net303
10.210.110.0/24 10.210.111.0/24 10.210.112.0/24 10.210.113.0/24 10.210.120.0/24 10.210.121.0/24 10.210.122.0/24 10.210.123.0/24 10.210.210.0/24 10.210.211.0/24 10.210.212.0/24 10.210.213.0/24 10.210.220.0/24 10.210.221.0/24 10.210.222.0/24 10.210.223.0/24 10.210.1.0/24 10.210.2.0/24 10.210.3.0/24
110 111 112 113 120 121 122 123 210 211 212 213 220 221 222 223 301 302 303
Implementation
this section reviews the implementation steps for deploying the SrX Series and QFabric solution in the data center.
QFabric Configuration
deploying or bring up the QFabric system is not described. we are assuming that the QFabric architecture has been initialized by a certified specialist and is ready to be configured. a QFabric switch has three types of node groups: Server node group (SNg)by default, every node device that joins the QFabric switch is placed within an automatically generated SNg that contains one node device. SNgs connect to servers and storage devices. redundant SNg (rSNg)you can assign two node devices in an rSNg. when grouped together, you can create link aggregation groups (lags) that span the interfaces on both node devices to provide resiliency and redundancy. Network node group (NNg)you can assign up to eight node devices in an NNg. when grouped together, the node devices within an NNg connect to other routers running routing protocols such as oSpF and bgp. In this guide, we are connecting the SrX Series to the NNg. by default, all QFabric nodes are identified by serial number. however, managing devices by serial number can be a challenge. to simplify the management process, you can identify QFabric nodes by more user-friendly descriptions, such as the physical location (row and rack) or node numbers, as shown in the following code snippet. Configuring aliases for the Node devices
set fabric aliases node-device P4336-C Node15 set fabric aliases node-device P4649-C Node16
Configuring the role of the Node devices
set fabric resources node-group NW-NG-0 network-domain set fabric resources node-group NW-NG-0 node-device Node15 set fabric resources node-group NW-NG-0 node-device Node16
14
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Interface Naming Conventions for QFabric Technology
the standard Junos oS port naming convention is a three-level identifier: interface_name-fpc/pic/port_no. the Flexible pIC Concentrator (FpC) is the first level, and it provides the slot location within the chassis. For QFabric architecture, the three-level identification poses a significant challenge for management because QFabric technology can scale to include up to 128 QFabric nodes, and there is no concept of a slot with QFabric nodes. therefore, the interface naming convention has been enhanced for QFabric technology to four levels, with an added chassis-level identifier. the new interface naming scheme is QFabric Node:interface_name-fpc/pic/port. the QFabric node can be either the serial number or the assigned alias name. Note: this interface naming convention applies only to physical interfaces. For logical interfaces such as lags, use node-group:interface_name-fpc/pic/slot. routed vlaN interfaces (rVIs) follow the standard naming convention used by Juniper Networks eX Series ethernet Switches, which is vlan.x.
netadmin@qfabric> show interfaces Node15:xe-0/0/10 Physical interface: row1-rack1:xe-0/0/10, Enabled, Physical link is Up Interface index: 49182, SNMP ifIndex: 7340572 Link-level type: Ethernet, MTU: 1514, Speed: 10Gbps, Duplex: Full-Duplex, BPDU Error: None, MAC-REWRITE Error: None, Loopback: Disabled, Source filtering: Disabled, Flow control: Disabled Interface flags: Internal: 0x0 CoS queues : 12 supported, 12 maximum usable queues Current address: 84:18:88:d5:b3:42, Hardware address: 84:18:88:d5:b3:42 Last flapped Input rate Output rate : 2011-09-06 21:10:51 UTC (04:20:44 ago) : 0 bps (0 pps) : 0 bps (0 pps)
Interface Type Configuration
the following sections cover common configurations for ports and vlaNs. QFabric architecture follows the same configuration context as eX Series switches. If you are familiar with configuring eX Series switches, the only difference is the interface naming convention. there are three different interface types: access, trunk, and routed interface. Just as with any other Junos oS platform, interface configurations are performed under the interface stanza. you can configure the access and trunk ports on any node groups. routed interfaces are limited to routed vlaN interface (rvI) or NNg ports. Note: Configuring post-mode access is optional. If the port mode is not defined, the default port mode is access. routed interfaces can be either rvI or l3 ports on an NNg. rvI is a logical l3 interface that provides routing between different networks. the following example shows physical l3 interface configurations on both an NNg and rvI. l3 routed port on an NNg
set Node15:xe-0/0/0.0 family ethernet-switching port-mode access set Node15:xe-0/0/1.0 family ethernet-switching port-mode trunk set Node15:xe-0/0/0.0 family inet address 1.1.1.1/24
Configuring an rvI and binding It to the vlaN
set vlan.1250 family inet address 10.83.100.1/24 set vlans v1250 l3-interface vlan.1250
For more information about l3 implementations for QFabric deployment options, see: www.juniper.net/us/en/local/pdf/implementation-guides/8010083-en.pdf For more information on how to configure node groups, see: www.juniper.net/us/en/local/pdf/implementation-guides/8010082-en.pdf
Copyright 2013, Juniper Networks, Inc.
15
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
SRX Series Configuration
Configuring for High Availability
devices deployed in the data center must ensure consistent service delivery, and the accessibility of the network dictates the availability of the data centers services. For an ha security infrastructure, one word describes the greatest challenge: state. most modern devices track the state of the traffic going through the device. when a failure occurs between two active security devices, the state must be shared between them. If the state is not shared, the secondary firewall drops the existing sessions because it is not aware of the state. when a stateful device is deployed, it is important to ensure service continuity so that state can be shared between devices. the primary goal is to ensure that the SrX Series remains operational despite data plane or control plane loss if failure occurs. the SrX Series platform introduces a new idea to ha design that allows it to fail over the control plane or data plane between chassis. In this hybrid design, the two devices act as one large chassis. the two different systems distribute across the two units as compared to a traditional active/backup cluster in which one device does all the operations while the other device remains idle. the control plane portion of the cluster is the routing engine (re). the re can fail over between the two chassis, with the first node passing traffic while the second node maintains the active re. In the event of a failure, the system that is running on the failed chassis fails over to the second chassis. this is done in a stateful manner for all traffic passing through the device. the only traffic that is lost is what is in the device or wires that fail. In the data center, this provides ease of deployment of active/backup, with the flexibility that the second chassis can provide some backup services. to configure two SrX Series nodes as an ha chassis cluster, physically connect the two devices (back-to-back for the fabric and control ports) and ensure that they are the same models.
Configuring a Cluster on the SRX Series Device
to configure a chassis cluster, you specify the following: Cluster Id and node Id Control port Fabric port the following steps are common for all deployment scenarios: 1. Configuring the chassis cluster
2. Configuring redundancy groups 3. Connecting between SrX Series nodes for the cluster 4. Configuring redundant ethernet interfaces 5. Configuring security zones 6. Configuring security policies
Configuring SRX Series Nodes for the Chassis Cluster
the cluster Id must be between 1 and 15. In each cluster, the node Id must be between 0 and 1. Cluster Id 0 unsets the cluster. you must reboot after the cluster Ids are configured.
set set set set set
chassis cluster chassis cluster chassis cluster interfaces fab0 interfaces fab1
cluster-id <0 and 15> node <0 and 1> reboot control-ports fpc 6 port 0 control-ports fpc0 port0 fabric-options member-interfaces xe-3/0/0 fabric-options member-interfaces xe-9/0/0
16
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Configuring Redundancy Groups
redundancy group 0 is reserved for the routing engine. Numbers 1 to 127 are reserved for the interfaces. the node priority determines which node is active for any given redundancy group. the active/passive and active/active SrX Series chassis cluster configuration is achieved by setting appropriate node priority for different redundancy groups and the state of monitored interfaces. the following configuration monitors all interfaces that are part of redundancy group 1.
set set set set set set set set set set set set
chassis chassis chassis chassis chassis chassis chassis chassis chassis chassis chassis chassis
cluster cluster cluster cluster cluster cluster cluster cluster cluster cluster cluster cluster
redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group redundancy-group
0 0 1 1 1 1 1 1 1 1 1 1
node 0 priority 100 node 1 priority 200 node 0 priority 100 node 1 priority 200 interface-monitor xe-4/0/0 weight 255 interface-monitor xe-4/0/1 weight 255 interface-monitor xe-4/0/2 weight 255 interface-monitor xe-4/0/3 weight 255 interface-monitor xe-16/0/0 weight 255 interface-monitor xe-16/0/1 weight 255 interface-monitor xe-16/0/2 weight 255 interface-monitor xe-16/0/3 weight 255
Configuring Redundant Ethernet Interfaces
you next configure the redundant ethernet (reth) interfaces and assign the child interfaces (physical interfaces) to the parent redundant ethernet interface. the reth interface is assigned to a redundancy group. the active node of the redundancy group determines which interface forwards traffic between the pair of physical interfaces that belong to the reth interface.
set interfaces xe-4/0/0 gigether-options redundant-parent reth1 set interfaces xe-4/0/1 gigether-options redundant-parent reth1 set interfaces reth1 redundant-ether-options redundancy-group 1
then you configure the logical interface properties for the reth interface. the logical interface is assigned an Ip address and runs dynamic routing protocols for network integration. the child interfaces inherit this configuration.
set set set set set set
interfaces interfaces interfaces interfaces interfaces interfaces
reth1 reth1 reth1 reth1 reth1 reth1
vlan-tagging redundant-ether-options redundancy-group 1 unit 111 vlan-id 111 unit 111 family inet address 10.210.111.1/24 unit 112 vlan-id 112 unit 112 family inet address 10.210.112.1/24
Configuring Security Zones
Security zones distinguish groups of hosts and their resources from one another. you can then apply different security measures to the interfaces bound to the security zone. here we create the security zones and assign the logical interfaces to each zone. you also must enable the protocols supported on these interfaces.
set set set set set set set
security security security security security security security
zones zones zones zones zones zones zones
security-zone security-zone security-zone security-zone security-zone security-zone security-zone
A1 A1 A1 A1 A1 A1 A1
address-book address net111 10.210.111.0/24 address-book address net112 10.210.112.0/24 address-book address net113 10.210.113.0/24 host-inbound-traffic system-services all interfaces reth1.111 interfaces reth1.112 interfaces reth1.113
Copyright 2013, Juniper Networks, Inc.
17
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
SRX Series VR-C
Zone C1
QFabric C1 - ISP
VR-B
Zone B2 Zone B1 Zone A2 Zone A1
SrvGroup - B2 SrvGroup - B1 SrvGroup - A2 SrvGroup - A1
VR-A
Figure 6: Network security zones
Configuring Security Policies
after the security zones are configured, you define the security policies between the zones. Security policies enforce a set of rules for transit traffic, identifying which traffic can pass through the firewall and the actions taken on the traffic as it passes through the firewall.
set security policies from-zone A1 to-zone A2 policy A1_to_A2-all-permit description Policy to allow all traffic from A1 to A2 (test 112A) set security policies from-zone A1 to-zone A2 policy A1_to_A2-all-permit source-address any set security policies from-zone A1 to-zone A2 policy A1_to_A2-all-permit destination-address any set security policies from-zone A1 to-zone A2 policy A1_to_A2-all-permit application any set security policies from-zone A1 to-zone A2 policy A1_to_A2-all-permit permit set security policies from-zone A1 to-zone A2 policy A1_to_A2-all-permit count
match match match then then
Note: by default, the Junos oS denies all traffic through an SrX Series device. you can change this behavior by configuring a standard security policy that permits certain types of traffic.
Configuring Inter-VR Routing on the SRX Series
In our test configuration, we created the routing configuration with the following assumptions: routing instances on the SrX Series allow for easy routing separation between virtual routers. we use three virtual routers: vra, vrb, and vrC. vra and vrb know little about the rest of the world and have simple configurations. vrC communicates with the rest of the world (public Internet, other data centers) and learns more than vra and vrb. the default route for vra and vrb is to point traffic to vrC (static route 0.0.0.0/0 next-table vrC.inet.0). vrC learns about networks in vra and vrb through route leaking using a routing information base (rIb) group configuration. In large cloud or hosted data center deployments in which multi-tenancy is a requirement, each vr on the QFabric solution can represent a customer, and each vr on the SrX Series can be assigned to an individual customer. this configuration maintains separation throughout the network, although the vrs are using the same physical infrastructure. Customers can choose not to enable inter-vr routing on the SrX Series to maintain strict separation of the routing tables. Note: Creating a static route to place packets into the other routing table works only in one direction because the Junos oS prevents the creation of routing loops if someone attempts to add another static route in the opposite direction.
18
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
a rIb group is used for route leaks between vrs. rIb groups are created under the main routing instance. the order of the routing tables rIb group statements is important. routes from the first table are imported to other tables. to configure rIb groups: 1. under interface-routes, enable importing interface routes through the rIb group.
2. under static, enable importing static routes through the rIb group. 3. under ospf, enable importing oSpF learned routes (from QFabric) through the rIb group (to vrC).
root@srx001-0# show routing-options rib-groups { VRA-in { import-rib [ VRA.inet.0 VRC.inet.0 ]; } VRB-in { import-rib [ VRB.inet.0 VRC.inet.0 ]; } } root@srx001-0# show routing-instances VRA { instance-type virtual-router; interface reth1.110; interface reth1.120; routing-options { interface-routes { rib-group inet VRA-in; } static { rib-group VRA-in; route 0.0.0.0/0 next-table VRC.inet.0; route 10.210.111.0/24 next-hop 10.210.110.2; } (part of config omitted)
} VRC { instance-type virtual-router; (part of config omitted) }
} protocols { ospf { rib-group VRA-in; area 0.0.0.0 { interface reth1.110; interface reth1.120; } } }
Copyright 2013, Juniper Networks, Inc.
19
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
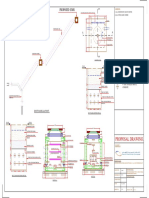
Connecting the SRX Cluster with the QFabric Solution
we configured the links between the QFabric solution and the SrX Series as reth interfaces on the SrX side and lag on the QFabric side. In active/active mode, two reth interfaces are configured (reth1 and reth2). In active/passive mode, only reth1 is configured. Four 10gbe links on the SrX side are part of the reth interface with a reported capacity 20 gbps. only two links are used at a time (from the active SrX chassis, one at a time). the links on the QFabric side are configured as two lag links, each with two 10g ports terminated to different nodes in the NNg. Figure 7 shows two links with the same color (gray or black); the color denotes that they belong to the same QFabric lag. the SrX Series uses only one of these at a time.
SRX Series
SRX001 xe-0/0/0 xe-0/1/0 Node 15: QFX3500 xe-0/0/0 Node 15: xe-0/0/1 QFX015
SRX Series
SRX001 xe-1/0/0 xe-1/1/0 Node 15: QFX3500 xe-0/0/2 Node 15: xe-0/0/3 QFX015
xe-0/2/0 xe-12/2/0
xe-1/2/0
RETH1
xe-0/2/0 xe-12/2/0
xe-1/2/0
RETH2
xe-13/2/0
xe-13/2/0
xe-12/0/0 xe-12/1/0 SRX002
Node 16: xe-0/0/0 QFX3500 Node 16: xe-0/0/1 QFX016 SRX002
xe-13/0/0 xe-13/1/0
Node 16: xe-0/0/2 QFX3500 Node 16: xe-0/0/3 QFX016
On QFX Series, side LAG has 2 member links. Total 2 LAGs.
Figure 7: QFabric and SRX links, reth interface and LAG the resiliency tests show no signs of traffic loss after link recovery between the SrX Series and the QFabric side because of the nonrevertive behavior of the reth interfaces. after a member link fails and failover to another SrX chassis occurs, even if the original link recovers, the reth interface does not switch traffic back to prevent traffic losses in case of link flapping. you can view the reth interface on the SrX Series as two tied lags, one terminating on node 0 and the other on node 1, with the rule that only one of them passes traffic at a time. In Figure 7, only one reth member on the active SrX cluster node is used to pass the traffic. For more information, see: http://kb.juniper.net/InfoCenter/index?page=content&id=TN10
IP Routing Between the SRX Series and QFabric Solution
when the QFabric solution acts as an l3 switch, it is routing Ip traffic between networks (isolated using vlaNs). you can create routing instances on the QFabric side to limit Ip visibility between parts of the network. the SrX Series routes the traffic between hosts belonging to the different routing instances on the QFabric side. on the SrX Series, we need to define security zones to match every routing instance on the QFabric side. you can group the security zones using vrs on the SrX Series. the SrX Series needs to know about all the networks that are terminated on the QFabric side. you can do this by provisioning static routes on the SrX Series or by running a dynamic routing protocol between the SrX and QFabric sides. both routing configurations were tested.
Static Routing
Static routes route traffic from the SrX Series to the QFabric side and vice versa. the SrX Series must be configured with static routes for all networks configured on the QFabric solution. In the following configuration, vlaNs 110113 connect the QFabric side with the SrX Series, with default routing pointing to the SrX (10.210.11.1). two other routing instances are omitted in the following code snippet.
20
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Configuring Routing on QFabric
root@QFabric# show routing-instances A1 { instance-type virtual-router; interface vlan.110; interface vlan.111; interface vlan.112; interface vlan.113; routing-options { static { route 0.0.0.0/0 next-hop 10.210.110.1; } } A2 {
instance-type virtual-router; interface vlan.120; interface vlan.121; interface vlan.122; interface vlan.123; routing-options { static { route 0.0.0.0/0 next-hop 10.210.120.1; }
Configuring Static Routing on SRX
we want to import rIb groups from inet vra-in. For every network on the QFabric side, we have added a corresponding static route on the SrX Series.
root@srx001-0# show routing-instances VRA { instance-type virtual-router; interface reth1.110; interface reth1.120; routing-options { interface-routes { rib-group inet VRA-in; } static { rib-group VRA-in; route 0.0.0.0/0 next-table VRC.inet.0; route 10.210.111.0/24 next-hop 10.210.110.2; route 10.210.112.0/24 next-hop 10.210.110.2; route 10.210.113.0/24 next-hop 10.210.110.2; route 10.210.121.0/24 next-hop 10.210.120.2; route 10.210.122.0/24 next-hop 10.210.120.2; route 10.210.123.0/24 next-hop 10.210.120.2; } } }
Copyright 2013, Juniper Networks, Inc.
21
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Dynamic Routing
oSpF was used to exchange routing information between the SrX and QFabric sides. the QFabric solution still uses a default route to point to the SrX Series because it is the only router in this context. Note: It is important to enable oSpF in the main routing instance, even if other critical configuration is in other routing instances; otherwise, the Junos oSpF process does not start.ecurity policy for the zone must enable oSpF for inbound traffic.
Configuring OSPF Routing on QFabric
root@QFabric# show routing-instances A1 { instance-type virtual-router; interface vlan.110; interface vlan.111; interface vlan.112; interface vlan.113; routing-options { static { route 0.0.0.0/0 next-hop 10.210.110.1; } router-id 10.210.110.2; } protocols { ospf { domain-id 10.210.110.2; area 0.0.0.0 { interface vlan.110; interface vlan.111 { passive; } interface vlan.112 { passive; } interface vlan.113 { passive; } } } } } A2 { instance-type virtual-router; interface vlan.120; interface vlan.121; interface vlan.122; interface vlan.123; routing-options { static { route 0.0.0.0/0 next-hop 10.210.120.1; } router-id 10.210.120.2; } protocols { ospf { domain-id 10.210.120.2; area 0.0.0.0 { interface vlan.120;
22
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
interface vlan.121 { passive; } interface vlan.122 { passive; } interface vlan.123 { passive; }
Configuring OSPF Routing on SRX
root@srx001-0# show routing-instances VRA { instance-type virtual-router; interface reth1.110; interface reth1.120; routing-options { interface-routes { rib-group inet VRA-in; } static { rib-group VRA-in; route 0.0.0.0/0 next-table VRC.inet.0; } } protocols { ospf { rib-group VRA-in; area 0.0.0.0 { interface reth1.110; interface reth1.120; } } } }
Enabling Services Offload (Low-Latency Firewall)
to enable the service-offloading feature: 1. use IoCs on the SrX Series that have more than one interface per network processor. only intra-networkprocessing flows can be offloaded. For the SrX5000 platform, the choice is a flexible IoC (SrX5K-FpC-IoC) and matching port modules (for example, SrX-IoC-4Xge-XFp).
2. add a license for the Services offload feature. 3. Configure the cluster to work in active/passive mode. active/active is not supported. 4. enable services offloading for each pIC that you want to use, and reboot to apply the changes. For example: set chassis node 0 fpc 0 pic 0 services-offload 5. Configure services offloading for specific flows in the security policy. For example:
set security policies from-zone A1 to-zone C1 policy A1_to_C1-permit2 then permit services-offload
Copyright 2013, Juniper Networks, Inc.
23
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Some useful commands for troubleshooting services offload include: show chassis cluster status show chassis fpc pic-status show system license usage show security flow session show security flow session services-offload show security policies from-zone a1 to-zone C1 policy-name a1_to_C1-permit2 detail show configuration security policies from-zone a1 to-zone C1 policy a1_to_C1-permit2 the following code snippet enables the services offload feature.
node 0 { fpc 4 { pic 0 { services-offload; } pic 1 { services-offload; } } } node 1 { fpc 4 { pic 0 { services-offload; } pic 1 { services-offload; } } } root@srx001-0# show security policies from-zone A1 to-zone C1 policy A1_to_C1permit2 description Policy to specifically permit some traffic from A1 to C1 for testing Service Offload; match { source-address net111; destination-address net303; application [ junos-http junos-udp-any ]; root@srx001-0# show chassis } then { permit { services-offload; } count; }
24
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
AppSecure
beyond basic network segmentation and security policy control, the SrX Series offers multiple security features to protect data center assets. appSecure is a suite of next-generation security capabilities that utilize advanced application identification and classification to deliver greater visibility, enforcement, control, and protection over the network. working in conjunction with the other security services offered by the SrX Series, appSecure provides a deep understanding of application behaviors and weaknesses to prevent application-borne threats that are difficult to detect and stop. For more information on appSecure and its features, see: www.juniper.net/us/en/local/pdf/datasheets/1000327-en.pdf
Configuring AppSecure Intrusion Policies
testing intrusion prevention system (IpS) and intrusion detection and prevention (Idp) features on the SrX Series is done by targeting specific Ftp commands. the following are the four major steps involved: 1. update the security package at https://services.netscreen.com/cgi-bin/index.cgi .
2. Create the Idp policy. 3. Set the Idp policy as an active policy. only one policy can be active at a time. 4. apply the Idp policy for traffic that matches the security policy. verification was done by initiating an Ftp session from zone C1 to the server in zone a1. the server responds and executes commands, except for file transfers where the filename matches *.exe. the SrX Series drops the session (flow) because it is enforcing the Idp policy.
The following snippet shows the IDP configuration. root@srx001-0# show security idp idp-policy C1A1-ftp1 { rulebase-ips { rule 1 { match { from-zone C1; source-address any; to-zone A1; destination-address any; application default; attacks { custom-attacks ftp1; } } then { action { drop-connection; } notification { log-attacks; } } } } } active-policy C1A1-ftp1; custom-attack ftp1 { severity major; attack-type { signature { context ftp-get-filename; pattern .*\.\[exe\]; direction any } }
Copyright 2013, Juniper Networks, Inc.
25
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} security-package { url https://services.netscreen.com/cgi-bin/index.cgi; } root@srx001-0# show security policies from-zone C1 to-zone A1 policy C1_to_A1permit1 description Policy to specifically permit some traffic from C1 to A1 for two networks (test 151A); match { source-address any; destination-address [ net111 net112 ]; application [ junos-http junos-ftp ]; } then { permit { application-services { idp; } } count; }
Configuring AppSecure Application Firewalls
the appSecure appFw feature is configured on the SrX Series. In the following code snippet, we configure appFw to block traffic for dropbox while not blocking similar traffic (tCp port 80) to other services.
root@srx001-0# show security application-firewall rule-sets FileSync-deny { rule Dropbox { match { dynamic-application [ junos:DROPBOX junos:DROPBOX-LAN-SYNC ]; } then { deny; } } default-rule { permit; } } root@srx001-0# show security policies from-zone A1 to-zone C1policy A1_to_C1permit3 description Policy to specifically permit some traffic from A1 to C1 (including public Internet) and test app-services; match { source-address net111; destination-address any; application [ junos-http junos-https ]; } then { permit { application-services { application-firewall { rule-set FileSync-deny; } } } count; }
26
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Validation Testing and Convergence Testing
the three use case designs have been successfully validated. Convergence testing was performed for the following traffic flows to test resiliency and ha for the firewall deployment. traffic between various vlaNs on the QFabric switch traffic between various vrs for permitting and denying traffic on the SrX Series traffic between various security zones within the vrs to check security policy enforcement appSecure IpS and appFw features on the SrX Series the following failure scenarios have been tested for full convergence of the network: access link failure QFabric to active SrX Series link failure active SrX Series device failure QFabric node failure SrX Series chassis cluster control link failure SrX Series chassis cluster fabric link failure For details concerning configuration and convergence test results, contact your local Juniper account representative.
Summary
this document explores the different options for integrating a high-speed firewall in the QFabric switch-based data center network. the data center network presents multiple firewall integration points and possibilities for seamlessly fitting in to specific customer environments. regardless of the deployment model, the need for a high-speed, low-latency, service-ready firewall system in the data center is paramount. more data centers are consolidating. as more applications are being hosted within these data centers and more complex traffic patterns evolve, additional security and less compromise are required. the Juniper Networks SrX5000 product line offers systems that are data center ready and are architected to support the data centers of today, as well as fulfill specific and individual customer requirements as the data center network transitions and evolves to meet future demands and challenges.
Copyright 2013, Juniper Networks, Inc.
27
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Appendix A: Configuration Files
the following is a complete configuration for the deployment featured in this guide.
Use Case 1: QFabric in Layer 2, SRX As FHRActive/Passive and Active/ Active Cluster Modes QFabric Layer 2 Configuration (QF-2PS.conf)
system { root-authentication { encrypted-password $1$pKp3TsxD$wKH8888alHlYz6SaSQEW9.; ## SECRET-DATA } } chassis { node-group NW-NG-0 { aggregated-devices { ethernet { device-count 48; } } } node-group RSNG-1 { aggregated-devices { ethernet { device-count 48; } } } node-group RSNG-2 { aggregated-devices { ethernet { device-count 48; } } } } interfaces { interface-range LAG1-ae0 { member Node01:xe-0/0/0; member Node02:xe-0/0/0; ether-options { 802.3ad RSNG-1:ae0; } } interface-range LAG1-ae1 { member Node01:xe-0/0/1; member Node02:xe-0/0/1; ether-options { 802.3ad RSNG-1:ae1; } } interface-range LAG1-ae2 { member Node01:xe-0/0/2; member Node02:xe-0/0/2; ether-options { 802.3ad RSNG-1:ae2; } }
28
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interface-range LAG1-ae11 { member Node01:ge-0/0/11; member Node02:ge-0/0/11; ether-options { 802.3ad RSNG-1:ae11; } } interface-range LAG1-ae12 { member Node01:ge-0/0/12; member Node02:ge-0/0/12; ether-options { 802.3ad RSNG-1:ae12; } } interface-range LAG1-ae13 { member Node01:ge-0/0/13; member Node02:ge-0/0/13; ether-options { 802.3ad RSNG-1:ae13; } } interface-range LAG1-ae14 { member Node01:ge-0/0/14; member Node02:ge-0/0/14; ether-options { 802.3ad RSNG-1:ae14; } } interface-range LAG1-ae15 { member Node01:ge-0/0/15; member Node02:ge-0/0/15; ether-options { 802.3ad RSNG-1:ae15; } } interface-range LAG1-ae16 { member Node01:ge-0/0/16; member Node02:ge-0/0/16; ether-options { 802.3ad RSNG-1:ae16; } } interface-range LAG1-ae17 { member Node01:ge-0/0/17; member Node02:ge-0/0/17; ether-options { 802.3ad RSNG-1:ae17; } } interface-range LAG1-ae18 { member Node01:ge-0/0/18; member Node02:ge-0/0/18; ether-options { 802.3ad RSNG-1:ae18; } }
Copyright 2013, Juniper Networks, Inc.
29
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
interface-range LAG1-ae19 { member Node01:ge-0/0/19; member Node02:ge-0/0/19; ether-options { 802.3ad RSNG-1:ae19; } } interface-range LAGR1-ae0 { member Node15:xe-0/0/0; member Node16:xe-0/0/0; ether-options { 802.3ad NW-NG-0:ae0; } } interface-range LAGR1-ae1 { member Node15:xe-0/0/1; member Node16:xe-0/0/1; ether-options { 802.3ad NW-NG-0:ae1; } } interface-range LAGR1-ae2 { member Node15:xe-0/0/2; member Node16:xe-0/0/2; ether-options { 802.3ad NW-NG-0:ae2; } } interface-range LAGR1-ae3 { member Node15:xe-0/0/3; member Node16:xe-0/0/3; ether-options { 802.3ad NW-NG-0:ae3; } } interface-range LAGR1-ae8 { member Node09:xe-0/0/[0-1]; member Node10:xe-0/0/[0-1]; ether-options { 802.3ad NW-NG-0:ae8; } } interface-range LAG2-ae0 { member Node17:xe-0/0/[0-1]; member Node18:xe-0/0/[0-1]; ether-options { 802.3ad RSNG-2:ae0; } } interface-range LAG2-ae4 { member Node17:xe-0/0/[8-9]; member Node18:xe-0/0/[8-9]; ether-options { 802.3ad RSNG-2:ae4; } } interface-range LAG1-ae20 {
30
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interface-range LAG1-ae21 { member Node01:ge-0/0/21; member Node02:ge-0/0/21; ether-options { 802.3ad RSNG-1:ae21; } } interface-range LAG1-ae22 { member Node01:ge-0/0/22; member Node02:ge-0/0/22; ether-options { 802.3ad RSNG-1:ae22; } } interface-range LAG1-ae23 { member Node01:ge-0/0/23; member Node02:ge-0/0/23; ether-options { 802.3ad RSNG-1:ae23; } } interface-range LAG1-ae24 { member Node01:ge-0/0/24; member Node02:ge-0/0/24; ether-options { 802.3ad RSNG-1:ae24; } } interface-range LAG1-ae25 { member Node01:ge-0/0/25; member Node02:ge-0/0/25; ether-options { 802.3ad RSNG-1:ae25; } } interface-range LAG2-ae5 { member Node17:xe-0/0/[10-11]; member Node18:xe-0/0/[10-11]; ether-options { 802.3ad RSNG-2:ae5; } } NW-NG-0:ae0 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 ]; } } } }
member Node01:ge-0/0/20; member Node02:ge-0/0/20; ether-options { 802.3ad RSNG-1:ae20; }
Copyright 2013, Juniper Networks, Inc.
31
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
NW-NG-0:ae1 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } NW-NG-0:ae2 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 211-213 } } } } NW-NG-0:ae3 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 211-213 } } } } NW-NG-0:ae8 { aggregated-ether-options { lacp { active; } } unit 0 { family ethernet-switching port-mode trunk; vlan { members 301-303; } } } } Node02:xe-0/0/1 { disable; } RSNG-1:ae0 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } }
{ 121-123 ];
{ 221-223 301-303 ];
{ 221-223 301-303 ];
{ 121-123 211-213 221-223 ];
32
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} RSNG-1:ae1 { description Server with VMs (srv131); unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae2 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae3 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae4 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae5 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae6 { unit 0 { family ethernet-switching { port-mode trunk; vlan {
221-223 301-303 ];
221-223 ];
221-223 ];
221-223 301-303 ];
221-223 ];
Copyright 2013, Juniper Networks, Inc.
33
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } RSNG-1:ae13 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae14 { unit 0 { family ethernet-switching port-mode trunk; vlan { members 301-303; } } } } RSNG-1:ae15 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae16 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 121; } } } RSNG-1:ae17 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae18 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 122; } }
{ 121-123 211-213 221-223 301-303 ];
{ 121-123 211-213 221-223 301-303 ];
{ 121-123 211-213 221-223 301-303 ];
34
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} RSNG-1:ae19 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae20 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 111; } } } RSNG-1:ae21 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae22 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 303; } } } RSNG-1:ae23 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae24 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 303; } } } RSNG-1:ae25 { unit 0 {
{ 121-123 211-213 221-223 301-303 ];
{ 121-123 211-213 221-223 ];
{ 121-123 211-213 221-223 ];
Copyright 2013, Juniper Networks, Inc.
35
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} protocols { lldp { interface all; } } fabric { resources { node-group NW-NG-0 { network-domain; node-device Node09; node-device Node10; node-device Node15; node-device Node16; } node-group RSNG-1 {
} } RSNG-2:ae0 { description EX4200 VC; unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 ]; } } } } RSNG-2:ae4 { description EX4200VC (ex056 & ex006); unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 ]; } } } } RSNG-2:ae5 { description STC; unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 301-303 ]; } } } }
family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 ]; } }
36
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} vlans { v111 { vlan-id } v112 { vlan-id } v113 { vlan-id } v121 { vlan-id } v122 { vlan-id } v123 { vlan-id } v211 { vlan-id }
} aliases { node-device Node01; } node-device Node02; } node-device Node09; } node-device Node10; } node-device Node15; } node-device Node16; } node-device Node17; } node-device Node18; } }
} node-group RSNG-2 { node-device Node17; node-device Node18; } BBAK3172 { BBAK3152 { P4560-C { P4585-C { P4336-C { P4649-C { P4303-C { P3333-C {
node-device Node01; node-device Node02;
111; 112; 113; 121; 122; 123; 211;
Copyright 2013, Juniper Networks, Inc.
37
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
v212 { vlan-id } v213 { vlan-id } v221 { vlan-id } v222 { vlan-id } v223 { vlan-id } v301 { vlan-id } v302 { vlan-id } v303 { vlan-id }
212; 213; 221; 222; 223; 301; 302; 303;
SRX ConfigurationActive Passive Cluster Mode (SRX-2PS.conf)
## Last changed: 2012-09-26 19:26:31 EDT version 12.1R2.9; groups { node0 { system { host-name srx001-0; backup-router 10.13.97.1 destination 0.0.0.0/0; } interfaces { fxp0 { unit 0 { family inet { address 10.13.97.62/24; } } } } } node1 { system { host-name srx001-1; backup-router 10.13.97.1 destination 0.0.0.0/0; } interfaces { fxp0 { unit 0 { family inet { address 10.13.97.42/24; }
38
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} apply-groups ${node}; system { time-zone America/New_York; authentication-order [ radius password ]; root-authentication { encrypted-password $1$ElUDAN5V$C/4LOvuGWfVnM1S4JHHyF.; ## SECRET-DATA } name-server { 172.28.113.111; 172.28.114.111; } services { ssh; xnm-clear-text; web-management { https { system-generated-certificate; } } } syslog { user * { any emergency; } file messages { any notice; authorization info; } file interactive-commands { interactive-commands any; } } license { autoupdate { url https://ae1.juniper.net/junos/key_retrieval; } } ntp { server 172.28.113.123; server 172.28.114.123; } } chassis { cluster { control-link-recovery; reth-count 3; control-ports { fpc 9 port 0; fpc 21 port 0; fpc 11 port 1; fpc 23 port 1; } redundancy-group 0 {
Copyright 2013, Juniper Networks, Inc.
39
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } interfaces { xe-4/0/0 { gigether-options { redundant-parent } } xe-4/0/1 { gigether-options { redundant-parent } } xe-4/0/2 { gigether-options { redundant-parent } } xe-4/0/3 { gigether-options { redundant-parent } } xe-16/0/0 { gigether-options { redundant-parent } } xe-16/0/1 { gigether-options { redundant-parent } } xe-16/0/2 { gigether-options { redundant-parent } } xe-16/0/3 { gigether-options {
} redundancy-group 1 { node 0 priority 100; node 1 priority 200; interface-monitor { xe-4/0/0 weight 255; xe-4/0/1 weight 255; xe-4/0/2 weight 255; xe-4/0/3 weight 255; xe-16/0/0 weight 255; xe-16/0/1 weight 255; xe-16/0/2 weight 255; xe-16/0/3 weight 255; } }
node 0 priority 100; node 1 priority 200;
reth1;
reth1;
reth2;
reth2;
reth1;
reth1;
reth2;
40
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} fab0 { fabric-options { member-interfaces { xe-0/2/0; xe-1/2/0; } } } fab1 { fabric-options { member-interfaces { xe-12/2/0; xe-13/2/0; } } } reth1 { vlan-tagging; redundant-ether-options { redundancy-group 1; } unit 111 { vlan-id 111; family inet { address 10.210.111.1/24; } } unit 112 { vlan-id 112; family inet { address 10.210.112.1/24; } } unit 113 { vlan-id 113; family inet { address 10.210.113.1/24; } } unit 121 { vlan-id 121; family inet { address 10.210.121.1/24; } } unit 122 { vlan-id 122; family inet { address 10.210.122.1/24; } } unit 123 { vlan-id 123; family inet {
redundant-parent reth2;
Copyright 2013, Juniper Networks, Inc.
41
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } reth2 { vlan-tagging; redundant-ether-options { redundancy-group 1; } unit 211 { vlan-id 211; family inet { address 10.210.211.1/24; } } unit 212 { vlan-id 212; family inet { address 10.210.212.1/24; } } unit 213 { vlan-id 213; family inet { address 10.210.213.1/24; } } unit 221 { vlan-id 221; family inet { address 10.210.221.1/24; } } unit 222 { vlan-id 222; family inet { address 10.210.222.1/24; } } unit 223 { vlan-id 223; family inet { address 10.210.223.1/24; } } unit 301 { vlan-id 301; family inet { address 10.210.1.1/24; } } unit 302 { vlan-id 302; family inet { address 10.210.2.1/24; } }
address 10.210.123.1/24;
42
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } snmp { community solutions; } routing-options { static { route 10.0.0.0/8 next-hop 10.13.97.1; route 172.16.0.0/12 next-hop 10.13.97.1; route 0.0.0.0/0 next-hop 10.13.97.1; } rib-groups { VRA-in { import-rib [ VRA.inet.0 VRC.inet.0 ]; } VRB-in { import-rib [ VRB.inet.0 VRC.inet.0 ]; } } } security { idp { idp-policy C1A1-ftp1 { rulebase-ips { rule 1 { match { from-zone C1; source-address any; to-zone A1; destination-address any; application default; attacks { custom-attacks ftp1; } } then { action { drop-connection; } notification { log-attacks; } } } } } active-policy C1A1-ftp1; custom-attack ftp1 { severity major; attack-type { signature {
unit 303 { vlan-id 303; family inet { address 10.210.3.1/24; } }
Copyright 2013, Juniper Networks, Inc.
43
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} application-firewall { rule-sets FileSync-deny { rule Dropbox { match { dynamic-application [ junos:DROPBOX junos:DROPBOX-LAN-SYNC ]; } then { deny; } } default-rule { permit; } } } screen { ids-option untrusted { icmp { ip-sweep threshold 1000000; fragment; large; flood threshold 10000; ping-death; } ip { bad-option; record-route-option; timestamp-option; security-option; stream-option; spoofing; source-route-option; loose-source-route-option; strict-source-route-option; unknown-protocol; tear-drop; } tcp { syn-fin; fin-no-ack; tcp-no-flag; syn-frag; port-scan threshold 1000000; syn-ack-ack-proxy threshold 10; syn-flood { attack-threshold 100; source-threshold 100;
} security-package { url https://services.netscreen.com/cgi-bin/index.cgi; }
context ftp-get-filename; pattern .*\.\[exe\]; direction any;
44
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } policies { from-zone A1 to-zone A1 { policy A1-deny1 { description Policy to specifically block HTTP traffic between two networks (test 111B); match { source-address net113; destination-address net111; application junos-http; } then { deny; count; } } policy A1-all-permit { description Default intrazone policy to allow all traffic (test 111A); match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone A2 to-zone A2 { policy A2-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count;
} udp { flood threshold 10000; udp-sweep threshold 1000; } limit-session { source-ip-based 100; destination-ip-based 100; }
} land; winnuke; tcp-sweep threshold 1000;
destination-threshold 100; timeout 15;
Copyright 2013, Juniper Networks, Inc.
45
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} from-zone A1 to-zone A2 { policy A1_to_A2-deny1 { description Policy to specifically block traffic from A1 to A2 for two networks (test 112B); match { source-address net113; destination-address net123; application junos-http; } then { deny; count; } } policy A1_to_A2-all-permit { description Policy to allow all traffic from A1 to A2 (test 112A); match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone A2 to-zone A1 { policy A2_to_A1-permit1 { description Policy to specifically permit some traffic from A2 to A1 for two networks (test 121A); match { source-address net122; destination-address net112; application junos-http; } then { permit; count; } } policy A2_to_A1-all-deny { description Policy to block all (not-specifically permitted) traffic from A2 to A1 (test 121B); match { source-address any; destination-address any; application any; } then { deny; count; }
46
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } from-zone B1 to-zone B1 { policy B1-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone B2 to-zone B2 { policy B2-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone B1 to-zone B2 { policy B1_to_B2 { match { source-address any; destination-address any; application any; } then { permit; } } } from-zone B2 to-zone B1 { policy B2_to_B1 { match { source-address any; destination-address any; application junos-http; } then { permit; count; } } } from-zone C1 to-zone C1 {
Copyright 2013, Juniper Networks, Inc.
47
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} from-zone C1 to-zone A1 { policy C1_to_A1-permit1 { description Policy to specifically permit some traffic from C1 to A1 for two networks (test 151A); match { source-address any; destination-address [ net111 net112 ]; application [ junos-http junos-ftp ]; } then { permit { application-services { idp; } } count; } } policy C1_to_A1-deny1 { description Policy to specifically deny some traffic from C1 to A1 for two networks (test 151B), general rule is to block anyway; match { source-address net301; destination-address net113; application junos-http; } then { deny; count; } } } from-zone A1 to-zone C1 { policy A1_to_C1-deny1 { description Policy to specifically deny some traffic from A1 to C1 for two networks (test 115B), general rule is to block anyway; match { source-address net111; destination-address net302; application junos-http; } then { deny; count;
policy C1-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } }
48
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } policy A1_to_C1-permit1 { description Policy to specifically permit some traffic from C1 for two networks (test 115A); match { source-address net111; destination-address net301; application junos-http; } then { permit; count; } } policy A1_to_C1-permit2 { description Policy to specifically permit some traffic from C1; match { source-address net111; destination-address net303; application [ junos-http junos-udp-any ]; } then { permit; count; } } policy A1_to_C1-permit3 { description Policy to specifically permit some traffic from C1 (including public Internet) and test app-services; match { source-address net111; destination-address any; application [ junos-http junos-https ]; } then { permit { application-services { application-firewall { rule-set FileSync-deny; } } } count; } } } from-zone B1 to-zone C1 { policy B1_to_C1-permit2 { description Policy to specifically permit some traffic from C1; match { source-address net211; destination-address net303; application [ junos-http junos-udp-any ]; }
A1 to
A1 to
A1 to
B1 to
Copyright 2013, Juniper Networks, Inc.
49
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} zones { security-zone A1 { address-book { address net111 10.210.111.0/24; address net112 10.210.112.0/24; address net113 10.210.113.0/24; } host-inbound-traffic { system-services { all; } } interfaces { reth1.111; reth1.112; reth1.113; } } security-zone A2 { address-book { address net121 10.210.121.0/24; address net122 10.210.122.0/24; address net123 10.210.123.0/24; } interfaces { reth1.121; reth1.122; reth1.123; } } security-zone B1 { address-book { address net211 10.210.211.0/24; address net212 10.210.212.0/24; address net213 10.210.213.0/24; } interfaces { reth2.211; reth2.212; reth2.213; } } security-zone B2 { address-book { address net221 10.210.221.0/24; address net222 10.210.222.0/24; address net223 10.210.223.0/24; } interfaces { reth2.221; reth2.222; reth2.223;
then { permit; count; }
50
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } routing-instances { VRA { instance-type virtual-router; interface reth1.111; interface reth1.112; interface reth1.113; interface reth1.121; interface reth1.122; interface reth1.123; routing-options { interface-routes { rib-group inet VRA-in; } static { rib-group VRA-in; route 0.0.0.0/0 next-table VRC.inet.0; } } } VRB { instance-type virtual-router; interface reth2.211; interface reth2.212; interface reth2.213; interface reth2.221; interface reth2.222; interface reth2.223; routing-options { interface-routes { rib-group inet VRB-in; } static { rib-group VRB-in; route 0.0.0.0/0 next-table VRC.inet.0; } } } VRC { instance-type virtual-router; interface reth2.301;
} } security-zone C1 { address-book { address net301 10.210.1.0/24; address net302 10.210.2.0/24; address net303 10.210.3.0/24; } screen untrusted; interfaces { reth2.301; reth2.302; reth2.303; } }
Copyright 2013, Juniper Networks, Inc.
51
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
interface reth2.302; interface reth2.303; routing-options { static { route 0.0.0.0/0 next-hop 10.210.3.21; } }
SRX Delta Configuration to Convert an Active/Passive Cluster to Active/Active
del del del del set set set set set set set chassis cluster redundancy-group 1 interface-monitor xe-4/0/2 weight 255 chassis cluster redundancy-group 1 interface-monitor xe-4/0/3 weight 255 chassis cluster redundancy-group 1 interface-monitor xe-16/0/2 weight 255 chassis cluster redundancy-group 1 interface-monitor xe-16/0/3 weight 255 chassis cluster redundancy-group 2 node 0 priority 200 chassis cluster redundancy-group 2 node 1 priority 100 chassis cluster redundancy-group 2 interface-monitor xe-4/0/2 weight 255 chassis cluster redundancy-group 2 interface-monitor xe-4/0/3 weight 255 chassis cluster redundancy-group 2 interface-monitor xe-16/0/2 weight 255 chassis cluster redundancy-group 2 interface-monitor xe-16/0/3 weight 255 interfaces reth2 redundant-ether-options redundancy-group 2
Use Case 2: QFabric in Layer 3 Mode, VR-based Traffic Steering to SRX As Needed
QFabric Configuration for Layer 3 Mode with Static Routing (QF-3PS-static.conf)
version 10.4I0 [daveu]; system { root-authentication { encrypted-password $1$pKp3TsxD$wKH8888alHlYz6SaSQEW9.; ## SECRET-DATA } } chassis { node-group NW-NG-0 { aggregated-devices { ethernet { device-count 48; } } } node-group RSNG-1 { aggregated-devices { ethernet { device-count 48; } } } node-group RSNG-2 { aggregated-devices { ethernet { device-count 48; } } }
52
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interfaces { interface-range LAG1-ae0 { member Node01:xe-0/0/0; member Node02:xe-0/0/0; ether-options { 802.3ad RSNG-1:ae0; } } interface-range LAG1-ae1 { member Node01:xe-0/0/1; member Node02:xe-0/0/1; ether-options { 802.3ad RSNG-1:ae1; } } interface-range LAG1-ae2 { member Node01:xe-0/0/2; member Node02:xe-0/0/2; ether-options { 802.3ad RSNG-1:ae2; } } interface-range LAG1-ae3 { member Node01:xe-0/0/3; member Node02:xe-0/0/3; ether-options { 802.3ad RSNG-1:ae3; } } interface-range LAG1-ae4 { member Node01:xe-0/0/4; member Node02:xe-0/0/4; ether-options { 802.3ad RSNG-1:ae4; } } interface-range LAG1-ae5 { member Node01:xe-0/0/5; member Node02:xe-0/0/5; ether-options { 802.3ad RSNG-1:ae5; } } interface-range LAG1-ae6 { member Node01:xe-0/0/6; member Node02:xe-0/0/6; ether-options { 802.3ad RSNG-1:ae6; } } interface-range LAG1-ae7 { member Node01:xe-0/0/7; member Node02:xe-0/0/7; ether-options { 802.3ad RSNG-1:ae7; } } interface-range LAG1-ae8 {
Copyright 2013, Juniper Networks, Inc.
53
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interface-range LAG1-ae9 { member Node01:ge-0/0/9; member Node02:ge-0/0/9; ether-options { 802.3ad RSNG-1:ae9; } } interface-range LAG1-ae10 { member Node01:ge-0/0/10; member Node02:ge-0/0/10; ether-options { 802.3ad RSNG-1:ae10; } } interface-range LAG1-ae11 { member Node01:ge-0/0/11; member Node02:ge-0/0/11; ether-options { 802.3ad RSNG-1:ae11; } } interface-range LAG1-ae12 { member Node01:ge-0/0/12; member Node02:ge-0/0/12; ether-options { 802.3ad RSNG-1:ae12; } } interface-range LAG1-ae13 { member Node01:ge-0/0/13; member Node02:ge-0/0/13; ether-options { 802.3ad RSNG-1:ae13; } } interface-range LAG1-ae14 { member Node01:ge-0/0/14; member Node02:ge-0/0/14; ether-options { 802.3ad RSNG-1:ae14; } } interface-range LAG1-ae15 { member Node01:ge-0/0/15; member Node02:ge-0/0/15; ether-options { 802.3ad RSNG-1:ae15; } } interface-range LAG1-ae16 {
member Node01:ge-0/0/8; member Node02:ge-0/0/8; ether-options { 802.3ad RSNG-1:ae8; }
54
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interface-range LAG1-ae17 { member Node01:ge-0/0/17; member Node02:ge-0/0/17; ether-options { 802.3ad RSNG-1:ae17; } } interface-range LAG1-ae18 { member Node01:ge-0/0/18; member Node02:ge-0/0/18; ether-options { 802.3ad RSNG-1:ae18; } } interface-range LAG1-ae19 { member Node01:ge-0/0/19; member Node02:ge-0/0/19; ether-options { 802.3ad RSNG-1:ae19; } } interface-range LAGR1-ae0 { member Node15:xe-0/0/0; member Node16:xe-0/0/0; ether-options { 802.3ad NW-NG-0:ae0; } } interface-range LAGR1-ae1 { member Node15:xe-0/0/1; member Node16:xe-0/0/1; ether-options { 802.3ad NW-NG-0:ae1; } } interface-range LAGR1-ae2 { member Node15:xe-0/0/2; member Node16:xe-0/0/2; ether-options { 802.3ad NW-NG-0:ae2; } } interface-range LAGR1-ae3 { member Node15:xe-0/0/3; member Node16:xe-0/0/3; ether-options { 802.3ad NW-NG-0:ae3; } } interface-range LAGR1-ae8 {
member Node01:ge-0/0/16; member Node02:ge-0/0/16; ether-options { 802.3ad RSNG-1:ae16; }
Copyright 2013, Juniper Networks, Inc.
55
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interface-range LAG2-ae0 { member Node17:xe-0/0/[0-1]; member Node18:xe-0/0/[0-1]; ether-options { 802.3ad RSNG-2:ae0; } } interface-range LAG2-ae4 { member Node17:xe-0/0/[8-9]; member Node18:xe-0/0/[8-9]; ether-options { 802.3ad RSNG-2:ae4; } } interface-range LAG1-ae20 { member Node01:ge-0/0/20; member Node02:ge-0/0/20; ether-options { 802.3ad RSNG-1:ae20; } } interface-range LAG1-ae21 { member Node01:ge-0/0/21; member Node02:ge-0/0/21; ether-options { 802.3ad RSNG-1:ae21; } } interface-range LAG1-ae22 { member Node01:ge-0/0/22; member Node02:ge-0/0/22; ether-options { 802.3ad RSNG-1:ae22; } } interface-range LAG1-ae23 { member Node01:ge-0/0/23; member Node02:ge-0/0/23; ether-options { 802.3ad RSNG-1:ae23; } } interface-range LAG1-ae24 { member Node01:ge-0/0/24; member Node02:ge-0/0/24; ether-options { 802.3ad RSNG-1:ae24; } } interface-range LAG1-ae25 {
member Node09:xe-0/0/[0-1]; member Node10:xe-0/0/[0-1]; ether-options { 802.3ad NW-NG-0:ae8; }
56
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} interface-range LAG2-ae5 { member Node17:xe-0/0/[10-11]; member Node18:xe-0/0/[10-11]; ether-options { 802.3ad RSNG-2:ae5; } } NW-NG-0:ae0 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 110 120 ]; } } } } NW-NG-0:ae1 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 110 120 ]; } } } } NW-NG-0:ae2 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 210 220 301-303 ]; } } } } NW-NG-0:ae3 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 210 220 301-303 ]; } } } } NW-NG-0:ae8 { aggregated-ether-options { lacp {
member Node01:ge-0/0/25; member Node02:ge-0/0/25; ether-options { 802.3ad RSNG-1:ae25; }
Copyright 2013, Juniper Networks, Inc.
57
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} RSNG-1:ae0 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae1 { description Server with VMs (srv131); unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae2 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae3 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae4 { unit 0 { family ethernet-switching {
} unit 0 { family ethernet-switching { port-mode trunk; vlan { members 301-303; } } }
active;
221-223 ];
221-223 301-303 ];
221-223 ];
221-223 ];
58
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} RSNG-1:ae5 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae6 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae7 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae8 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 111; } } } RSNG-1:ae9 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } }
port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 301-303 ]; }
{ 121-123 211-213 221-223 ];
{ 121-123 211-213 221-223 ];
{ 121-123 211-213 221-223 301-303 ];
{ 121-123 211-213 221-223 301-303 ];
Copyright 2013, Juniper Networks, Inc.
59
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
RSNG-1:ae10 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 112; } } } RSNG-1:ae11 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae12 { unit 0 { family ethernet-switching port-mode trunk; native-vlan-id 113; } } } RSNG-1:ae13 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae14 { unit 0 { family ethernet-switching port-mode trunk; vlan { members 301-303; } } } } RSNG-1:ae15 { unit 0 { family ethernet-switching port-mode trunk; vlan { members [ 111-113 } } } } RSNG-1:ae16 {
{ 121-123 211-213 221-223 301-303 ];
{ 121-123 211-213 221-223 301-303 ];
{ 121-123 211-213 221-223 301-303 ];
60
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} RSNG-1:ae17 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 301-303 ]; } } } } RSNG-1:ae18 { unit 0 { family ethernet-switching { port-mode trunk; native-vlan-id 122; } } } RSNG-1:ae19 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 301-303 ]; } } } } RSNG-1:ae20 { unit 0 { family ethernet-switching { port-mode trunk; native-vlan-id 111; } } } RSNG-1:ae21 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 ]; } } } } RSNG-1:ae22 { unit 0 { family ethernet-switching { port-mode trunk;
unit 0 { family ethernet-switching { port-mode trunk; native-vlan-id 121; } }
Copyright 2013, Juniper Networks, Inc.
61
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } RSNG-1:ae23 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-1:ae24 { unit 0 { family ethernet-switching { port-mode trunk; native-vlan-id 303; } } } RSNG-1:ae25 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-2:ae0 { description EX4200 VC; unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-2:ae4 { description EX4200VC (ex056 & ex006); unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 } } } } RSNG-2:ae5 { description STC; unit 0 {
native-vlan-id 303;
221-223 ];
221-223 ];
221-223 ];
221-223 ];
62
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } vlan { unit 110 { family inet { address 10.210.110.2/24; } } unit 111 { family inet { address 10.210.111.1/24; } } unit 112 { family inet { address 10.210.112.1/24; } } unit 113 { family inet { address 10.210.113.1/24; } } unit 120 { family inet { address 10.210.120.2/24; } } unit 121 { family inet { address 10.210.121.1/24; } } unit 122 { family inet { address 10.210.122.1/24; } } unit 123 { family inet { address 10.210.123.1/24; } } unit 210 { family inet { address 10.210.210.2/24; } } unit 211 { family inet { address 10.210.211.1/24;
family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 301-303 ]; } }
Copyright 2013, Juniper Networks, Inc.
63
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } protocols { lldp { interface all; } } routing-instances { A1 { instance-type virtual-router; interface vlan.110; interface vlan.111; interface vlan.112; interface vlan.113; routing-options { static { route 0.0.0.0/0 next-hop 10.210.110.1; } router-id 10.210.110.2; } } A2 { instance-type virtual-router; interface vlan.120; interface vlan.121;
} } unit 212 { family inet address } } unit 213 { family inet address } } unit 220 { family inet address } } unit 221 { family inet address } } unit 222 { family inet address } } unit 223 { family inet address } }
{ 10.210.212.1/24;
{ 10.210.213.1/24;
{ 10.210.220.2/24;
{ 10.210.221.1/24;
{ 10.210.222.1/24;
{ 10.210.223.1/24;
64
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} B1 {
interface vlan.122; interface vlan.123; routing-options { static { route 0.0.0.0/0 next-hop 10.210.120.1; } router-id 10.210.120.2; } instance-type virtual-router; interface vlan.210; interface vlan.211; interface vlan.212; interface vlan.213; routing-options { static { route 0.0.0.0/0 next-hop 10.210.210.1; } router-id 10.210.210.2; } instance-type virtual-router; interface vlan.220; interface vlan.221; interface vlan.222; interface vlan.223; routing-options { static { route 0.0.0.0/0 next-hop 10.210.220.1; } router-id 10.210.220.2; }
} B2 {
} } fabric { resources { node-group NW-NG-0 { network-domain; node-device Node09; node-device Node10; node-device Node15; node-device Node16; } node-group RSNG-1 { node-device Node01; node-device Node02; } node-group RSNG-2 { node-device Node17; node-device Node18; } } aliases { node-device BBAK3172 {
Copyright 2013, Juniper Networks, Inc.
65
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } vlans { v110 { vlan-id 110; l3-interface } v111 { vlan-id 111; l3-interface } v112 { vlan-id 112; l3-interface } v113 { vlan-id 113; l3-interface } v120 { vlan-id 120; l3-interface } v121 { vlan-id 121; l3-interface } v122 { vlan-id 122; l3-interface } v123 { vlan-id 123;
Node01; } node-device Node02; } node-device Node09; } node-device Node10; } node-device Node15; } node-device Node16; } node-device Node17; } node-device Node18; }
BBAK3152 { P4560-C { P4585-C { P4336-C { P4649-C { P4303-C { P3333-C {
vlan.110;
vlan.111;
vlan.112;
vlan.113;
vlan.120;
vlan.121;
vlan.122;
66
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
l3-interface } v210 { vlan-id 210; l3-interface } v211 { vlan-id 211; l3-interface } v212 { vlan-id 212; l3-interface } v213 { vlan-id 213; l3-interface } v220 { vlan-id 220; l3-interface } v221 { vlan-id 221; l3-interface } v222 { vlan-id 222; l3-interface } v223 { vlan-id 223; l3-interface } v301 { vlan-id 301; } v302 { vlan-id 302; } v303 { vlan-id 303; }
vlan.123;
vlan.210;
vlan.211;
vlan.212;
vlan.213;
vlan.220;
vlan.221;
vlan.222;
vlan.223;
Copyright 2013, Juniper Networks, Inc.
67
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Configuration for Enabling OSPF
set set set set set set set set set set set set set set set set set set set set protocols ospf area 0.0.0.0 interface NW-NG-0:ae5.0 protocols ospf area 0.0.0.0 interface NW-NG-0:ae8.0 routing-instances A1 protocols ospf domain-id 10.210.110.2 routing-instances A1 protocols ospf area 0.0.0.0 interface routing-instances A1 protocols ospf area 0.0.0.0 interface routing-instances A1 protocols ospf area 0.0.0.0 interface routing-instances A1 protocols ospf area 0.0.0.0 interface routing-instances A2 protocols ospf domain-id 10.210.120.2 routing-instances A2 protocols ospf area 0.0.0.0 interface routing-instances A2 protocols ospf area 0.0.0.0 interface routing-instances A2 protocols ospf area 0.0.0.0 interface routing-instances A2 protocols ospf area 0.0.0.0 interface routing-instances B1 protocols ospf area 0.0.0.0 interface routing-instances B1 protocols ospf area 0.0.0.0 interface routing-instances B1 protocols ospf area 0.0.0.0 interface routing-instances B1 protocols ospf area 0.0.0.0 interface routing-instances B2 protocols ospf area 0.0.0.0 interface routing-instances B2 protocols ospf area 0.0.0.0 interface routing-instances B2 protocols ospf area 0.0.0.0 interface routing-instances B2 protocols ospf area 0.0.0.0 interface
vlan.110 vlan.111 passive vlan.112 passive vlan.113 passive vlan.120 vlan.121 vlan.122 vlan.123 vlan.210 vlan.211 vlan.212 vlan.213 vlan.220 vlan.221 vlan.222 vlan.223 passive passive passive passive passive passive passive passive passive
SRX ConfigurationActive/Passive Cluster (SRX-3PS-static)
## Last changed: 2012-09-26 20:20:17 EDT version 12.1R2.9; groups { node0 { system { host-name srx001-0; backup-router 10.13.97.1 destination 0.0.0.0/0; } interfaces { fxp0 { unit 0 { family inet { address 10.13.97.62/24; } } } } } node1 { system { host-name srx001-1; backup-router 10.13.97.1 destination 0.0.0.0/0; } interfaces { fxp0 { unit 0 { family inet { address 10.13.97.42/24; } } }
68
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} apply-groups ${node}; system { time-zone America/New_York; authentication-order [ radius password ]; root-authentication { encrypted-password $1$ElUDAN5V$C/4LOvuGWfVnM1S4JHHyF.; ## SECRET-DATA } name-server { 172.28.113.111; 172.28.114.111; } services { ssh; xnm-clear-text; web-management { https { system-generated-certificate; } } } syslog { user * { any emergency; } file messages { any notice; authorization info; } file interactive-commands { interactive-commands any; } } license { autoupdate { url https://ae1.juniper.net/junos/key_retrieval; } } ntp { server 172.28.113.123; server 172.28.114.123; } } chassis { cluster { control-link-recovery; reth-count 3; control-ports { fpc 9 port 0; fpc 21 port 0; fpc 11 port 1; fpc 23 port 1; } redundancy-group 0 {
Copyright 2013, Juniper Networks, Inc.
69
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } interfaces { xe-4/0/0 { gigether-options { redundant-parent } } xe-4/0/1 { gigether-options { redundant-parent } } xe-4/0/2 { gigether-options { redundant-parent } } xe-4/0/3 { gigether-options { redundant-parent } } xe-16/0/0 { gigether-options { redundant-parent } } xe-16/0/1 { gigether-options { redundant-parent } } xe-16/0/2 { gigether-options { redundant-parent } } xe-16/0/3 {
} redundancy-group 1 { node 0 priority 100; node 1 priority 200; interface-monitor { xe-4/0/0 weight 255; xe-4/0/1 weight 255; xe-4/0/2 weight 255; xe-4/0/3 weight 255; xe-16/0/0 weight 255; xe-16/0/1 weight 255; xe-16/0/2 weight 255; xe-16/0/3 weight 255; } }
node 0 priority 100; node 1 priority 200;
reth1;
reth1;
reth2;
reth2;
reth1;
reth1;
reth2;
70
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} fab0 { fabric-options { member-interfaces { xe-0/2/0; xe-1/2/0; } } } fab1 { fabric-options { member-interfaces { xe-12/2/0; xe-13/2/0; } } } reth1 { vlan-tagging; redundant-ether-options { redundancy-group 1; } unit 110 { vlan-id 110; family inet { address 10.210.110.1/24; } } unit 120 { vlan-id 120; family inet { address 10.210.120.1/24; } } } reth2 { vlan-tagging; redundant-ether-options { redundancy-group 1; } unit 210 { vlan-id 210; family inet { address 10.210.210.1/24; } } unit 220 { vlan-id 220; family inet { address 10.210.220.1/24; } } unit 301 {
gigether-options { redundant-parent reth2; }
Copyright 2013, Juniper Networks, Inc.
71
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } snmp { community solutions; } routing-options { static { route 10.0.0.0/8 next-hop 10.13.97.1; route 172.16.0.0/12 next-hop 10.13.97.1; route 0.0.0.0/0 next-hop 10.13.97.1; } rib-groups { VRA-in { import-rib [ VRA.inet.0 VRC.inet.0 ]; } VRB-in { import-rib [ VRB.inet.0 VRC.inet.0 ]; } } } security { idp { idp-policy C1A1-ftp1 { rulebase-ips { rule 1 { match { from-zone C1; source-address any; to-zone A1; destination-address any; application default; attacks { custom-attacks ftp1; } } then { action { drop-connection; } notification {
} unit 302 { vlan-id 302; family inet { address 10.210.2.1/24; } } unit 303 { vlan-id 303; family inet { address 10.210.3.1/24; } }
vlan-id 301; family inet { address 10.210.1.1/24; }
72
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} application-firewall { rule-sets FileSync-deny { rule Dropbox { match { dynamic-application [ junos:DROPBOX junos:DROPBOX-LAN-SYNC ]; } then { deny; } } default-rule { permit; } } } screen { ids-option untrusted { icmp { ip-sweep threshold 1000000; fragment; large; flood threshold 10000; ping-death; } ip { bad-option; record-route-option; timestamp-option; security-option; stream-option; spoofing; source-route-option; loose-source-route-option; strict-source-route-option; unknown-protocol;
} } active-policy C1A1-ftp1; custom-attack ftp1 { severity major; attack-type { signature { context ftp-get-filename; pattern .*\.\[exe\]; direction any; } } } security-package { url https://services.netscreen.com/cgi-bin/index.cgi; }
log-attacks;
Copyright 2013, Juniper Networks, Inc.
73
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } policies { from-zone A1 to-zone A1 { policy A1-deny1 { description Policy to specifically block HTTP traffic between two networks (test 111B); match { source-address net113; destination-address net111; application junos-http; } then { deny; count; } } policy A1-all-permit { description Default intrazone policy to allow all traffic (test 111A); match { source-address any; destination-address any; application any; } then { permit; count; }
tear-drop; } tcp { syn-fin; fin-no-ack; tcp-no-flag; syn-frag; port-scan threshold 1000000; syn-ack-ack-proxy threshold 10; syn-flood { attack-threshold 100; source-threshold 100; destination-threshold 100; timeout 15; } land; winnuke; tcp-sweep threshold 1000; } udp { flood threshold 10000; udp-sweep threshold 1000; } limit-session { source-ip-based 100; destination-ip-based 100; }
74
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } from-zone A2 to-zone A2 { policy A2-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone A1 to-zone A2 { policy A1_to_A2-deny1 { description Policy to specifically block traffic from A1 to A2 for two networks (test 112B); match { source-address net113; destination-address net123; application junos-http; } then { deny; count; } } policy A1_to_A2-all-permit { description Policy to allow all traffic from A1 to A2 (test 112A); match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone A2 to-zone A1 { policy A2_to_A1-permit1 { description Policy to specifically permit some traffic from A2 to A1 for two networks (test 121A); match { source-address net122; destination-address net112; application junos-http; } then { permit; count; }
Copyright 2013, Juniper Networks, Inc.
75
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} policy A2_to_A1-all-deny { description Policy to block all (not-specifically perimtted) traffic from A2 to A1 (test 121B); match { source-address any; destination-address any; application any; } then { deny; count; } } } from-zone B1 to-zone B1 { policy B1-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone B2 to-zone B2 { policy B2-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone B1 to-zone B2 { policy B1_to_B2 { match { source-address any; destination-address any; application any; } then { permit; } } } from-zone B2 to-zone B1 {
76
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} from-zone C1 to-zone C1 { policy C1-all-permit { description Default intrazone policy to allow all traffic; match { source-address any; destination-address any; application any; } then { permit; count; } } } from-zone C1 to-zone A1 { policy C1_to_A1-permit1 { description Policy to specifically permit some traffic from C1 to A1 for two networks (test 151A); match { source-address any; destination-address [ net111 net112 ]; application [ junos-http junos-ftp ]; } then { permit { application-services { idp; } } count; } } policy C1_to_A1-deny1 { description Policy to specifically deny some traffic from C1 to A1 for two networks (test 151B), general rule is to block anyway; match { source-address net301; destination-address net113; application junos-http; } then { deny; count; }
policy B2_to_B1 { match { source-address any; destination-address any; application junos-http; } then { permit; count; } }
Copyright 2013, Juniper Networks, Inc.
77
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } from-zone A1 to-zone C1 { policy A1_to_C1-deny1 { description Policy to specifically deny some traffic from A1 to C1 for two networks (test 115B), general rule is to block anyway; match { source-address net111; destination-address net302; application junos-http; } then { deny; count; } } policy A1_to_C1-permit1 { description Policy to specifically permit some traffic from A1 to C1 for two networks (test 115A); match { source-address net111; destination-address net301; application junos-http; } then { permit; count; } } policy A1_to_C1-permit2 { description Policy to specifically permit some traffic from A1 to C1; match { source-address net111; destination-address net303; application [ junos-http junos-udp-any ]; } then { permit; count; } } policy A1_to_C1-permit3 { description Policy to specifically permit some traffic from A1 to C1 (including public Internet) and test app-services; match { source-address net111; destination-address any; application [ junos-http junos-https ]; } then { permit { application-services { application-firewall { rule-set FileSync-deny; }
78
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
C1;
} from-zone B1 to-zone C1 { policy B1_to_C1-permit2 { description Policy to specifically permit some traffic from B1 to match { source-address net211; destination-address net303; application [ junos-http junos-udp-any ]; } then { permit; count; }
} } count;
} zones { security-zone A1 { address-book { address net111 10.210.111.0/24; address net112 10.210.112.0/24; address net113 10.210.113.0/24; } host-inbound-traffic { system-services { all; } } interfaces { reth1.110; } } security-zone A2 { address-book { address net121 10.210.121.0/24; address net122 10.210.122.0/24; address net123 10.210.123.0/24; } interfaces { reth1.120; } } security-zone B1 { address-book { address net211 10.210.211.0/24; address net212 10.210.212.0/24; address net213 10.210.213.0/24; } interfaces { reth2.210;
Copyright 2013, Juniper Networks, Inc.
79
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} } routing-instances { VRA { instance-type virtual-router; interface reth1.110; interface reth1.120; routing-options { interface-routes { rib-group inet VRA-in; } static { rib-group VRA-in; route 0.0.0.0/0 next-table VRC.inet.0; route 10.210.111.0/24 next-hop 10.210.110.2; route 10.210.112.0/24 next-hop 10.210.110.2; route 10.210.113.0/24 next-hop 10.210.110.2; route 10.210.121.0/24 next-hop 10.210.120.2; route 10.210.122.0/24 next-hop 10.210.120.2; route 10.210.123.0/24 next-hop 10.210.120.2; } } } VRB { instance-type virtual-router; interface reth2.210; interface reth2.220; routing-options { interface-routes { rib-group inet VRB-in; } static {
} } security-zone B2 { address-book { address net221 address net222 address net223 } interfaces { reth2.220; } } security-zone C1 { address-book { address net301 address net302 address net303 } screen untrusted; interfaces { reth2.301; reth2.302; reth2.303; } }
10.210.221.0/24; 10.210.222.0/24; 10.210.223.0/24;
10.210.1.0/24; 10.210.2.0/24; 10.210.3.0/24;
80
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} VRC { instance-type virtual-router; interface reth2.301; interface reth2.302; interface reth2.303; routing-options { static { route 0.0.0.0/0 next-hop 10.210.3.21; } } }
rib-group VRB-in; route 0.0.0.0/0 next-table VRC.inet.0; route 10.210.211.0/24 next-hop 10.210.210.2; route 10.210.212.0/24 next-hop 10.210.210.2; route 10.210.213.0/24 next-hop 10.210.210.2; route 10.210.221.0/24 next-hop 10.210.220.2; route 10.210.222.0/24 next-hop 10.210.220.2; route 10.210.223.0/24 next-hop 10.210.220.2;
Delta Configuration to Enable OSPF Instead of Static Routing on the SRX
set protocols ospf area 0.0.0.0 interface ge-3/0/0.0 set security zones security-zone A1 host-inbound-traffic protocols ospf set security zones security-zone A2 host-inbound-traffic protocols ospf set security zones security-zone B1 host-inbound-traffic protocols ospf set security zones security-zone B2 host-inbound-traffic protocols ospf set security zones security-zone C1 host-inbound-traffic protocols ospf set routing-instances VRA protocols ospf rib-group VRA-in set routing-instances VRA protocols ospf area 0.0.0.0 interface reth1.110 set routing-instances VRA protocols ospf area 0.0.0.0 interface reth1.120 set routing-instances VRB protocols ospf rib-group VRB-in set routing-instances VRB protocols ospf area 0.0.0.0 interface reth2.210 set routing-instances VRB protocols ospf area 0.0.0.0 interface reth2.220 set routing-instances VRC protocols ospf area 0.0.0.0 interface reth2.301 set routing-instances VRC protocols ospf area 0.0.0.0 interface reth2.302 set routing-instances VRC protocols ospf area 0.0.0.0 interface reth2.303 del routing-instances VRA routing-options static route 10.210.111.0/24 next-hop 10.210.110.2 del routing-instances VRA routing-options static route 10.210.112.0/24 next-hop 10.210.110.2 del routing-instances VRA routing-options static route 10.210.113.0/24 next-hop 10.210.110.2 del routing-instances VRA routing-options static route 10.210.121.0/24 next-hop 10.210.120.2 del routing-instances VRA routing-options static route 10.210.122.0/24 next-hop 10.210.120.2 del routing-instances VRA routing-options static route 10.210.123.0/24 next-hop 10.210.120.2 del routing-instances VRB routing-options static route 10.210.211.0/24 next-hop 10.210.210.2
Copyright 2013, Juniper Networks, Inc.
81
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
del routing-instances 10.210.210.2 del routing-instances 10.210.210.2 del routing-instances 10.210.220.2 del routing-instances 10.210.220.2 del routing-instances 10.210.220.2
VRB routing-options static route 10.210.212.0/24 next-hop VRB routing-options static route 10.210.213.0/24 next-hop VRB routing-options static route 10.210.221.0/24 next-hop VRB routing-options static route 10.210.222.0/24 next-hop VRB routing-options static route 10.210.223.0/24 next-hop
Use Case 3: SRX with Services Offload
SRX Delta Configuration for Enabling Services Offload
set chassis node 0 fpc 4 pic 0 services-offload set chassis node 0 fpc 4 pic 1 services-offload set chassis node 0 fpc 9 pic 0 services-offload set chassis node 0 fpc 9 pic 1 services-offload set chassis node 0 fpc 11 pic 0 services-offload set chassis node 0 fpc 11 pic 1 services-offload set chassis node 1 fpc 4 pic 0 services-offload set chassis node 1 fpc 4 pic 1 services-offload set chassis node 1 fpc 9 pic 0 services-offload set chassis node 1 fpc 9 pic 1 services-offload set chassis node 1 fpc 11 pic 0 services-offload set chassis node 1 fpc 11 pic 1 services-offload set security policies from-zone A1 to-zone C1 policy Policy to specifically permit some traffic from A1 to Offload set security policies from-zone A1 to-zone C1 policy services-offload set security policies from-zone B1 to-zone C1 policy Policy to specifically permit some traffic from B1 to Offload set security policies from-zone B1 to-zone C1 policy services-offload
A1_to_C1-permit2 description C1 for testing Service A1_to_C1-permit2 then permit B1_to_C1-permit2 description C1 for testing Service B1_to_C1-permit2 then permit
82
Copyright 2013, Juniper Networks, Inc.
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
Appendix B: QFabric Interfaces for Servers
In our configuration, QFabric nodes are configured in pairs to provide rSNgs. Interfaces for servers (hosts) are configured as lag links with two members, one out of each node member for ha purposes. this configuration approach is well documented in the implementation guide Designing a Layer 2 Data Center Network with the QFabric Architecture. For server ports, it makes sense to enable and use link layer discovery protocol (lldp), which is globally enabled in our configuration. lldp can be used as a troubleshooting tool as well as provide service for data Center bridging Capability exchange (dCbX). Configuration snippet for server interfaces on the QFabric side:
interface-range LAG1-ae0 { member Node01:xe-0/0/0; member Node02:xe-0/0/0; ether-options { 802.3ad RSNG-1:ae0; } } RSNG-1:ae0 { unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 ]; } } } } Or alternative, shorter CLI syntax set interfaces set interfaces set interfaces set interfaces set interfaces 121-123 ] interface-range interface-range interface-range RSNG-1:ae0 unit RSNG-1:ae0 unit LAG1-ae0 LAG1-ae0 LAG1-ae0 0 family 0 family member Node01:xe-0/0/0 member Node02:xe-0/0/0 ether-options 802.3ad RSNG-1:ae0 ethernet-switching port-mode trunk ethernet-switching vlan members [ 111-113
QFabric Interfaces for EX Switches
to allow for higher density of 1g server connections in the data center, you can use the eX4200 line of switches. these switches are connected in the vC for ha setup. you can connect the switch to the QFabric side using 10g links, with each switch having one or two uplinks (a total of two or four per vC). this approach is documented in Designing a Layer 2 Data Center Network with the QFabric Architecture. bridge protocol data unit (bpdu) protect is enabled by default on the QFabric architecture. as soon as it sees the bpdu frame on the port, the port is flagged and disabled. If a timeout is not configured on the port for this type of error, the port remains disabled until administrator issues the clear command (clear ethernet-switching bpdu-error interface x). be sure to disable all spanning-tree protocols on the eX ports facing QFabric. Configuration Snippet for eX vC Interfaces on QFabric
interface-range LAG2-ae4 { member Node17:xe-0/0/[8-9]; member Node18:xe-0/0/[8-9]; ether-options { 802.3ad RSNG-2:ae4; }
Copyright 2013, Juniper Networks, Inc.
83
IMPLEMENTATION GUIDE - Integrating SRX Series Services Gateways into a QFabric Switch-based Data Center Implementation Guide
} RSNG-2:ae4 { description EX4200VC (ex056 & ex006); unit 0 { family ethernet-switching { port-mode trunk; vlan { members [ 111-113 121-123 211-213 221-223 ]; } } } } Or alternative, shorter CLI syntax set interfaces interface-range LAG2-ae4 member Node17:xe-0/0/[8-9] set interfaces interface-range LAG2-ae4 member Node18:xe-0/0/[8-9] set interfaces interface-range LAG2-ae4 ether-options 802.3ad RSNG-2:ae4 set interfaces RSNG-2:ae4 description EX4200VC (ex056 & ex006) set interfaces RSNG-2:ae4 unit 0 family ethernet-switching port-mode trunk set interfaces RSNG-2:ae4 unit 0 family ethernet-switching vlan members [ 111-113 121-123 ] set interfaces RSNG-2:ae4 unit 0 family ethernet-switching vlan members [ 121-123 221-223 ]
About Juniper Networks
Juniper Networks is in the business of network innovation. From devices to data centers, from consumers to cloud providers, Juniper Networks delivers the software, silicon and systems that transform the experience and economics of networking. the company serves customers and partners worldwide. additional information can be found at www.juniper.net.
Corporate and Sales Headquarters Juniper Networks, Inc. 1194 North mathilda avenue Sunnyvale, Ca 94089 uSa phone: 888.JuNIper (888.586.4737) or 408.745.2000 Fax: 408.745.2100 www.juniper.net
APAC and EMEA Headquarters Juniper Networks International b.v. boeing avenue 240 1119 pZ Schiphol-rijk amsterdam, the Netherlands phone: 31.0.207.125.700 Fax: 31.0.207.125.701
to purchase Juniper Networks solutions, please contact your Juniper Networks representative at 1-866-298-6428 or authorized reseller.
Copyright 2013 Juniper Networks, Inc. all rights reserved. Juniper Networks, the Juniper Networks logo, Junos, NetScreen, and ScreenoS are registered trademarks of Juniper Networks, Inc. in the united States and other countries. all other trademarks, service marks, registered marks, or registered service marks are the property of their respective owners. Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify, transfer, or otherwise revise this publication without notice.
8010090-001-eN
Jan 2013
printed on recycled paper
84
Copyright 2013, Juniper Networks, Inc.
You might also like
- Resin 4.0 AdminDocument427 pagesResin 4.0 AdminTeobaldo MaitaNo ratings yet
- Book Software SRX Series Volume 1 PDFDocument2,394 pagesBook Software SRX Series Volume 1 PDFSatyapriya PanigrahiNo ratings yet
- Getting Started Guide For Branch SRX SeriesDocument158 pagesGetting Started Guide For Branch SRX Seriessatya28No ratings yet
- VPC Best Practices Design GuideDocument117 pagesVPC Best Practices Design GuidetafitaNo ratings yet
- BASA 200 Brocade Associate SAN Administrator: Lab GuideDocument152 pagesBASA 200 Brocade Associate SAN Administrator: Lab Guidechandan_rhceNo ratings yet
- 317177-A Rel NotesDocument88 pages317177-A Rel NotesLuis RodriguesNo ratings yet
- Antg000 v2r3Document810 pagesAntg000 v2r3FXBessugesNo ratings yet
- Data Computing Appliance Version 3Document150 pagesData Computing Appliance Version 3Derek YuenNo ratings yet
- Virtual Chassis MX SeriesDocument230 pagesVirtual Chassis MX SeriesJosé Pablo MongeNo ratings yet
- Lab Guide CFA200 Rev0114 LG - LDocument114 pagesLab Guide CFA200 Rev0114 LG - LdipeshNo ratings yet
- VPC Best Practices Design Guide PDFDocument129 pagesVPC Best Practices Design Guide PDFNelsonbohrNo ratings yet
- Operation Manuel ClipX BM40Document498 pagesOperation Manuel ClipX BM40Fal GUARMACHNo ratings yet
- Juniper SRX Security Chassis ClusterDocument426 pagesJuniper SRX Security Chassis ClusterNOC AlbideyNetNo ratings yet
- Brocade Network OS Administrator S GuideDocument242 pagesBrocade Network OS Administrator S GuidepaulohrodriguesNo ratings yet
- $fieldbus Installations in A DeltaVT Digital Automation System PDFDocument112 pages$fieldbus Installations in A DeltaVT Digital Automation System PDFMichael ArteagaNo ratings yet
- ASP Virtual Implementation PDFDocument724 pagesASP Virtual Implementation PDFmulyadiNo ratings yet
- Sap Hana Eim Adapter SDK enDocument72 pagesSap Hana Eim Adapter SDK enravan_shindeNo ratings yet
- 990-9814C EN Rev 2.1.2.3Document32 pages990-9814C EN Rev 2.1.2.3ralphNo ratings yet
- WR VX Simulator Users Guide 6.1 PDFDocument114 pagesWR VX Simulator Users Guide 6.1 PDFprnchaNo ratings yet
- EMC Symmetrix Remote Data Facility (SRDF) : Connectivity GuideDocument150 pagesEMC Symmetrix Remote Data Facility (SRDF) : Connectivity GuidepeymanNo ratings yet
- AssuredSAN 3004 Series Setup Guide - G222 - 83-00006725-15-01-ADocument94 pagesAssuredSAN 3004 Series Setup Guide - G222 - 83-00006725-15-01-AKilly BlameNo ratings yet
- Junos Os Multipoint VPN Configuration With Next-Hop Tunnel BindingDocument29 pagesJunos Os Multipoint VPN Configuration With Next-Hop Tunnel Bindingab_laaroussiNo ratings yet
- 650i Ultra PDF 070403Document121 pages650i Ultra PDF 070403Slobodan Boba JovanovićNo ratings yet
- Avaya P333R 3.12 UG PDFDocument268 pagesAvaya P333R 3.12 UG PDFbratiloveanuNo ratings yet
- Fieldbus InstallationDocument112 pagesFieldbus InstallationSubhendu JanaNo ratings yet
- Assuredsan 3004 Series Setup Guide: For Firmware Release Gl210 or LaterDocument88 pagesAssuredsan 3004 Series Setup Guide: For Firmware Release Gl210 or LaterKilly BlameNo ratings yet
- Ns Vcs MXDocument92 pagesNs Vcs MXSalman SaluNo ratings yet
- IBM Proventia IPS and Check Point VPN-1 VSX NGX R65Document64 pagesIBM Proventia IPS and Check Point VPN-1 VSX NGX R65tpressleyNo ratings yet
- Foundation Fieldbus Manual (Allen Bradley)Document184 pagesFoundation Fieldbus Manual (Allen Bradley)Thia Dewi Ratnasari100% (1)
- REVELPROG-IS ManualDocument48 pagesREVELPROG-IS ManualJuan Carlos De Leon CoradoNo ratings yet
- Branch High Availability in The Distributed Enterprise: Implementation GuideDocument23 pagesBranch High Availability in The Distributed Enterprise: Implementation GuidePablo EzequielNo ratings yet
- Ug962 v7 Vc709 XT Connectivity TRD UgDocument98 pagesUg962 v7 Vc709 XT Connectivity TRD Ugteo2005No ratings yet
- Fastiron Ethernet Switch: Stacking Configuration GuideDocument172 pagesFastiron Ethernet Switch: Stacking Configuration GuideThanh Kieu TienNo ratings yet
- Solaris Host Utilities 62 Installation and SetupDocument128 pagesSolaris Host Utilities 62 Installation and SetupJehanzeb KayaniNo ratings yet
- HP Storageworks Msa San Switch 2/8: Installation GuideDocument72 pagesHP Storageworks Msa San Switch 2/8: Installation GuidenetfinityfrNo ratings yet
- Manual 5020MGC 01 04Document51 pagesManual 5020MGC 01 04consultachNo ratings yet
- Pelco DVR5100 Series Network Design Guide ManualDocument20 pagesPelco DVR5100 Series Network Design Guide ManualPedro Fernández HernándezNo ratings yet
- h15300 Vxrail Network GuideDocument135 pagesh15300 Vxrail Network GuideEL MELHANo ratings yet
- WCCP Reference Guide.8Document102 pagesWCCP Reference Guide.8ksudhakar09No ratings yet
- Tsunami8100 SoftwareMgmtGuide-V4.2 SWV2.4.3Document250 pagesTsunami8100 SoftwareMgmtGuide-V4.2 SWV2.4.3Анатолий ПетьковNo ratings yet
- TestDocument120 pagesTestRagee KaneshNo ratings yet
- Fos 741 AccessgatewayDocument100 pagesFos 741 AccessgatewayСергей ЛавренюкNo ratings yet
- MetroCluster Service and Expansion GuideDocument178 pagesMetroCluster Service and Expansion GuideabhisharNo ratings yet
- ZZ Ref Im-Webinterface (En) 1-1 1vta100180Document47 pagesZZ Ref Im-Webinterface (En) 1-1 1vta100180Derouich2019No ratings yet
- Vxworks Network Prog Guide (5 5)Document351 pagesVxworks Network Prog Guide (5 5)swjangNo ratings yet
- Alta Disponibilidad DataontapDocument220 pagesAlta Disponibilidad DataontapAngel Arturo Arrieta CastilloNo ratings yet
- ContrailDocument44 pagesContrailxixihahawo1No ratings yet
- Ex4200 Metro Ring With MX Series Head-End: Using Virtual Chassis Technology in The WanDocument23 pagesEx4200 Metro Ring With MX Series Head-End: Using Virtual Chassis Technology in The WanAram AvetisyanNo ratings yet
- Cisco Switch Substation Automation PDFDocument86 pagesCisco Switch Substation Automation PDFIndin HasanNo ratings yet
- Check Point Security Gateway R70 Installation and Configuration Guide For Crossbeam X-Series PlatformsDocument62 pagesCheck Point Security Gateway R70 Installation and Configuration Guide For Crossbeam X-Series PlatformsDinesh PalNo ratings yet
- Access Gateway - Admin GuideDocument94 pagesAccess Gateway - Admin GuideVijay DharmarajNo ratings yet
- Working With OOTB MACH Simulation ExamplesDocument44 pagesWorking With OOTB MACH Simulation ExamplesEMERSONNo ratings yet
- VSX5000-InstlGuide N450000590r001Document230 pagesVSX5000-InstlGuide N450000590r001Georgi VodenitcharovNo ratings yet
- Hypersocket Implementation GuideDocument132 pagesHypersocket Implementation GuideWarawut NakakeatNo ratings yet
- Platform General Vxworks Migration Guide 3.6Document124 pagesPlatform General Vxworks Migration Guide 3.6Ding YueNo ratings yet
- Pan Os Networking AdminDocument544 pagesPan Os Networking AdminAnkita SinghNo ratings yet
- Deploying QoS for Cisco IP and Next Generation Networks: The Definitive GuideFrom EverandDeploying QoS for Cisco IP and Next Generation Networks: The Definitive GuideRating: 5 out of 5 stars5/5 (2)
- CAN and FPGA Communication Engineering: Implementation of a CAN Bus based Measurement System on an FPGA Development KitFrom EverandCAN and FPGA Communication Engineering: Implementation of a CAN Bus based Measurement System on an FPGA Development KitNo ratings yet
- What Is An Application Delivery ControllerDocument7 pagesWhat Is An Application Delivery ControllerMichael LeonardNo ratings yet
- Value of The Hyperscale CloudDocument12 pagesValue of The Hyperscale CloudMichael LeonardNo ratings yet
- Using ADC Services To Build Openstack CloudsDocument13 pagesUsing ADC Services To Build Openstack CloudsMichael LeonardNo ratings yet
- Implementing Cisco ACI With Citrix NetscalerDocument36 pagesImplementing Cisco ACI With Citrix NetscalerMichael LeonardNo ratings yet
- Opening The Way To Data Center AgilityDocument14 pagesOpening The Way To Data Center AgilityMichael LeonardNo ratings yet
- Practial Path To Automating NetworksDocument4 pagesPractial Path To Automating NetworksMichael LeonardNo ratings yet
- OpenStack and NetScalerDocument7 pagesOpenStack and NetScalerMichael LeonardNo ratings yet
- Integrating Citrix NetScaler With Cisco ACIDocument10 pagesIntegrating Citrix NetScaler With Cisco ACIMichael LeonardNo ratings yet
- NetScaler Cisco ACE Nexus and ACI IntegrationDocument4 pagesNetScaler Cisco ACE Nexus and ACI IntegrationMichael LeonardNo ratings yet
- SDN 101 An Introduction To Software Defined NetworkingDocument9 pagesSDN 101 An Introduction To Software Defined NetworkingXaed HazhmeNo ratings yet
- Cisco ACI Citrix NetScaler SharepointDocument148 pagesCisco ACI Citrix NetScaler SharepointMichael LeonardNo ratings yet
- Cisco APIC Citrix NetScaler Solution GuideDocument8 pagesCisco APIC Citrix NetScaler Solution GuideMichael LeonardNo ratings yet
- Monetizing The Business Edge With Hosted Private Cloud ServicesDocument19 pagesMonetizing The Business Edge With Hosted Private Cloud ServicesMichael LeonardNo ratings yet
- Vertical Campus Implementation GuideDocument144 pagesVertical Campus Implementation GuideMichael LeonardNo ratings yet
- Building Application Centric ADC Enabled Data CentersDocument6 pagesBuilding Application Centric ADC Enabled Data CentersMichael LeonardNo ratings yet
- Architecting Your Network To Survive A DisasterDocument10 pagesArchitecting Your Network To Survive A DisasterMichael LeonardNo ratings yet
- Integrating SDN in To The Data CenterDocument11 pagesIntegrating SDN in To The Data CenterMichael LeonardNo ratings yet
- VMware Vmotion Inter Data Center Workload MobilityDocument35 pagesVMware Vmotion Inter Data Center Workload MobilityMichael LeonardNo ratings yet
- Introduction To Big Data: Infrastructure and Networking ConsiderationsDocument11 pagesIntroduction To Big Data: Infrastructure and Networking ConsiderationsMichael LeonardNo ratings yet
- Securing Virtualization in The Cloud-Ready Data CenterDocument15 pagesSecuring Virtualization in The Cloud-Ready Data CenterMichael LeonardNo ratings yet
- Getting On The Path To SDNDocument12 pagesGetting On The Path To SDNMichael LeonardNo ratings yet
- Juniper Junos Node Unifier For The MX SeriesDocument7 pagesJuniper Junos Node Unifier For The MX SeriesMichael LeonardNo ratings yet
- Horizontal Campus Validated Design GuideDocument174 pagesHorizontal Campus Validated Design GuideMichael LeonardNo ratings yet
- Understanding Big Data and The QFabric SystemDocument12 pagesUnderstanding Big Data and The QFabric SystemMichael LeonardNo ratings yet
- Internet Edge Implementation GuideDocument63 pagesInternet Edge Implementation GuideMichael LeonardNo ratings yet
- The Evolution of Virtualized Desktops and Converged InfrastructureDocument7 pagesThe Evolution of Virtualized Desktops and Converged InfrastructureMichael LeonardNo ratings yet
- Decoding Software Defined NetworkingDocument8 pagesDecoding Software Defined NetworkingMichael LeonardNo ratings yet
- The Role of Layer 4-7 Services in Scaling ApplicationsDocument20 pagesThe Role of Layer 4-7 Services in Scaling ApplicationsMichael LeonardNo ratings yet
- Platform As A Service: The Next Big Opportunity For Communications Service ProvidersDocument10 pagesPlatform As A Service: The Next Big Opportunity For Communications Service ProvidersMichael LeonardNo ratings yet
- Support Wiki - Cable Pin-OutsDocument6 pagesSupport Wiki - Cable Pin-OutsfrancportNo ratings yet
- 1600924722788Document205 pages1600924722788Ivan Ally Ramadhan 2020No ratings yet
- Chimney Sizing Calculation-R1Document3 pagesChimney Sizing Calculation-R1Arun Kumar67% (3)
- ITP For Construction of CurbsDocument4 pagesITP For Construction of CurbsYay B. GicoNo ratings yet
- Vertical Split Case Pump: Key Features and BenefitsDocument2 pagesVertical Split Case Pump: Key Features and BenefitsTimNo ratings yet
- Nvs 810 DatasheetDocument2 pagesNvs 810 DatasheetFran PojeNo ratings yet
- 3.1method Statment For Installation of Fire Protection System FinalDocument31 pages3.1method Statment For Installation of Fire Protection System Finalمقاول تكييف كهرباء وصحيNo ratings yet
- Dynamics AX 2012 Shortcuts (GL)Document1 pageDynamics AX 2012 Shortcuts (GL)ramu278No ratings yet
- Precast Concrete Pipe Rack DesignDocument43 pagesPrecast Concrete Pipe Rack DesignAmanpreet Singh67% (3)
- An Overview of Cell-Level ATM Network SimulationDocument13 pagesAn Overview of Cell-Level ATM Network SimulationSandeep Singh TomarNo ratings yet
- TSM ProcedureDocument77 pagesTSM ProcedureAnton SoNo ratings yet
- Manhole Detail.-Proposal-1Document1 pageManhole Detail.-Proposal-1Mohammed BasheeruddinNo ratings yet
- Pages From 610-Hands-On Software Architecture - Jyotiswarup RaiturkarDocument10 pagesPages From 610-Hands-On Software Architecture - Jyotiswarup RaiturkarKaisar OnoNo ratings yet
- Drawing Templates - FreeCAD DocumentationDocument17 pagesDrawing Templates - FreeCAD Documentationwdany100% (1)
- QTs EcoSeriesDocument22 pagesQTs EcoSeriesasrihamidNo ratings yet
- Thesis College PDFDocument104 pagesThesis College PDFVaralakshmi SundarrajanNo ratings yet
- IPTVDocument20 pagesIPTVKaungMinnChainNo ratings yet
- Data Communication ProtocolsDocument8 pagesData Communication Protocolssubramanyam62No ratings yet
- Digital Electronics NotesDocument29 pagesDigital Electronics NotesHimanshu KhanduriNo ratings yet
- Get the most from your premium HD office suiteDocument8 pagesGet the most from your premium HD office suiteArun_Kumar_2397No ratings yet
- 22-105 Ritmik CatalogDocument80 pages22-105 Ritmik CatalogALİNo ratings yet
- Appendix B: Technical InformationDocument11 pagesAppendix B: Technical InformationOnTa OnTa60% (5)
- Basic Methodology: Design Philosophies AS/NZS 7000:2010 - Section 2Document10 pagesBasic Methodology: Design Philosophies AS/NZS 7000:2010 - Section 2Victor JimenezNo ratings yet
- Instruction SetDocument5 pagesInstruction SetSaad SaeedNo ratings yet
- IC v8.1 Cookbook PDFDocument121 pagesIC v8.1 Cookbook PDFFelipe FerreiraNo ratings yet
- 06 08 07Document7 pages06 08 07Hutanu GabrielNo ratings yet
- Concrete Made by Volumetric Batching and Continuous Mixing: Standard Specification ForDocument3 pagesConcrete Made by Volumetric Batching and Continuous Mixing: Standard Specification ForHuaman Chavez Jesus AngelNo ratings yet
- Low Yat Plaza & Digital Mall C-Zone Price ListDocument2 pagesLow Yat Plaza & Digital Mall C-Zone Price ListLee Wai LeongNo ratings yet
- Mini Project "DESIGN OF BLAST RESISTANT STRUCTURES"Document35 pagesMini Project "DESIGN OF BLAST RESISTANT STRUCTURES"Chetan ChavanNo ratings yet