Professional Documents
Culture Documents
Biometrics Iris Technology
Uploaded by
Toaster97Original Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Biometrics Iris Technology
Uploaded by
Toaster97Copyright:
Available Formats
ZEIT GEIST-2009
NAME: L.MIHIRA COLLEGE:K.I.E.T. TOPIC:BIOMETRICS {IRIS TECHNOLOGY}
Biometrics (ancient Greek: bios life, metron measure) refers to two very different fields of study and application. The first, which is the older and is used in biological studies, is the collection, synthesis, analysis and management of data in biology. Biometrics in reference to biological sciences, or biostatistics, has been studied since the early twentieth century.[1] Biometrics is the science and technology of measuring and analyzing biological data. In information technology, biometrics refers to technologies that measure and analyze human body characteristics, such as fingerprints, eye retinas and irises, voice patterns, facial patterns and hand measurements, for authentication purposes. Biometric characteristics can be divided in two main classes, as represented in figure on the right:
Physiological are related to the shape of the body. Examples include, but are not limited to fingerprint, face recognition, hand and palm geometry and iris recognition. Behavioral are related to the behavior of a person. Characteristic implemented by using biometrics are signature verification, keystroke dynamics, and voice.
Physiological
Fingerprints: The patterns of friction ridges and valleys on an individual's fingertips are unique to that individual. For decades, law enforcement has been classifying and determining identity by matching key points of ridge endings and bifurcations. Fingerprints are unique for each finger of a person including identical twins.
Face Recognition: The identification of a person by their facial image can be done in a number of different ways such as by capturing an image of the face in the visible spectrum using an optical camera or by using the infrared patterns of facial heat emission. Facial recognition in visible light typically model key features from the central portion of a facial image. Using a wide assortment of cameras, the visible light systems extract features from the captured image(s) that do not change over time while avoiding superficial features such as facial expressions or hair. Several approaches to modeling facial images in the visible spectrum are Principal Component Analysis, Local Feature Analysis, neural networks, elastic graph theory, and multi-resolution analysis Hand and Finger Geometry: These methods of personal authentication are well established. Hand recognition has been available for over twenty years. To achieve
personal authentication, a system may measure either physical characteristics of the fingers or the hands. These include length, width, thickness and surface area of the hand. One interesting characteristic is that some systems require a small biometric sample (a few bytes). Hand geometry has gained acceptance in a range of applications
Odor and Scent Cognitive Biometric Systems
Odor evaluation is important in criminal prosecution and defense. Blood hounds and other dogs have been used to identify individuals by their scent trails. Dogs are first offered a reference article, such as a handkerchief, hat, or an article of clothing.[8] This scent evidence is usually admissible in court. It's employed similarly to finger print identification. [9] The latter is premised on the alleged factuality of the "individual odor theory," which hold that each person has a unique scent that can be identified by the dog and related back to a specific individual. High courts have accepted the performance of canine scent identification, even when it is claimed that they are detecting the scent of a specific individual at the scene of a crime nearly 2 years after the crime was committed as discussed in the case State v. Eugene Wiley Case No. 8001659, 18th Judicial Circuit, Brevard County Fla. Among all these identifications,iris technology is the most reliable technology. Among all our sense organs,eyes play a major role inside which lies the iris. It surrounds the pupil & protects it. Another interesting aspect is that, no two persons in the world can have a similar iris. It is unique for each & every individual. The science also says that, iris has been a challenge against the fingerprint technology which is not as unique as iris is. This concept is used in the IRIS TECHNOLOGY Lets know some thin about it.
WHAT ACTUALLY IS IRIS TECHNOLOGY?
Iris technology is the biometric authentication of high resolution images of the iris of the individuals eye. It was developed by JOHN DOGHMAN in 20th centuary. It is being usede in many govt. organisations for the issue of sugar cards, election cards, etc.
It is also used for capturing criminals in the very prestigious CENTRAL BUREAU OF INVESTIGATION, INTELLIGENCE BUREAU, etc. Unlike another less prevalent ocular based technology called iris scanning, Iris recognition uses latest camera technology, with harmless infra red illumination which is passed into the eye for a second .then it is converted into a digital template. PROCEDURE: 1.At first the eye is kept at the base of the iris recognition machine and a digital photograph of the iris is taken.
IRIS RECOGNITION ALGORITHM
2.The Pixels of iris are converted into bit wise manner so as to make easy for the conversion. 3.Now this is inturn converted into a phase sequence of 512 bytes of iris code. 4. The obtained digital template value is there by used for verification with another stored digital template value &hence verified. ADVANTAGES: 1.Biggest advantage is its reliability& the process gets over in just a fraction of two seconds. 2. Iris being well protected inside the eye & doesnt get damaged easily. But if a person is upto some manual labour, the finger prints get ruptured & it becomes difficult to take them. So, iris can be betterly used. 3.Iris is unique for any person in the world where as the finger prints are not unique for more than 5.0% of human population due to mono zygotic twin. 4.. Verification of finger prints is very difficult & time taking because they are too complex. But in case of iris recognition more than 5000 templates can be verirfied just in a minute.. 5. Any kind of surgical operation cannot damage the iris. This has been proven successful since 30 years & it is a great contributon in the field of medicine. After a few years of its it wasnt recognized due to some problems like LIVE TISSUE VERIFICATION. But in the past 10 years, it has been turned into an advanced technology, with its wide range of improvement.
Technology Comparison
Method
Coded Pattern
Misidentification rate 1/1,200,000 1/1,000 1/700
Security
Applications High-security facilities Universal Low-security facilities Low-security facilities Low-security facilities Telephone service
Iris Recognition Fingerprinting Hand Shape Facial Recognition Signature Voiceprinting
Iris pattern Fingerprints Size, length and thickness of hands Outline, shape and distribution of eyes and nose Shape of letters, writing order, pen pressure Voice characteristics
High Medium Low
1/100
Low
1/100 1/30
Low Low
Iris-Scan Issues
Iris-scan technology requires reasonably controlled and cooperative user interaction - the enrollee must hold still in a certain spot, even if only momentarily. Many users struggle to interact with the system until they become accustomed to its operations. In applications whose user interaction is frequent (e.g. employee physical access), the technology grows easier to use; however, applications in which user interaction is infrequent (e.g. national ID) may encounter ease-of-use issues. Over time, with improved acquisition devices, this issue should grow less problematic.
The accuracy claims associated with iris-scan technology may overstate the real-world efficacy of the technology. Because the claimed equal error rates are derived from assessment and matching of ideal iris images (unlike those acquired in the field), actual results may not live up to the astronomical projections provided by leading suppliers of the technology. Lastly, since iris technology is designed to be an identification technology, fallback procedures may not be as fully developed as in a verification deployment (users accustomed to identification may not carry necessary ID, for example). Though these issues do not reduce the effectiveness of iris recognition technology, they must be kept in mind should a company decide to implement on iris-based solution.
The following table shows a comparison of existing biometric systems in terms of those parameters: Comparison of various biometric technologies, modified from Jain et al., 2004[21] (H=High, M=Medium, L=Low) Biometrics Universalit Uniquenes Permanenc Collectabilit Performanc Acceptabilit Circumventio : y s e y e y n* Face H L M H L H L Fingerprint M H H M H M H Hand M M M H M M M geometry Keystrokes L L L M L M M Hand veins M M M M M M H Iris H H H M H L H Retinal scan H H M L H L H Signature L L L H L H L Voice M L L M L H L Facial thermograp H H L H M H H h Odor H H H L L M L DNA H H H L H L L Gait M L L H L H M Ear Canal M M H M M H M
*If we start encouraging new technologies in different fields, the world
surely becomes a great global leader
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Exponent Properties DiscoveryDocument3 pagesExponent Properties DiscoveryToaster97No ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- 100 Functional Equations Problems-OlympiadDocument15 pages100 Functional Equations Problems-Olympiadsanits591No ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Creative Science & Research - Screen Printing Press (2004)Document21 pagesCreative Science & Research - Screen Printing Press (2004)amrandconan100% (2)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- 4TB Hard Drives Bring RAID 6 To Its Limits - SNS EuropeDocument4 pages4TB Hard Drives Bring RAID 6 To Its Limits - SNS EuropeToaster97No ratings yet
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Trigonometry and Complex Numbers GuideDocument5 pagesTrigonometry and Complex Numbers GuideToaster97No ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- 50 Diophantine Equations Problems With SolutionsDocument6 pages50 Diophantine Equations Problems With Solutionsbvarici100% (2)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Ricks On MaudDocument12 pagesRicks On MaudToaster97No ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- STEP 2004 SolutionsDocument36 pagesSTEP 2004 SolutionsToaster97No ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- 1998 Paper IDocument5 pages1998 Paper IToaster97No ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Last Tree Burning and Other Poems by Spiro Constantine MarkouDocument36 pagesThe Last Tree Burning and Other Poems by Spiro Constantine MarkouToaster97No ratings yet
- Research in India Happens in A Few Elite Institutions' - The HinduDocument4 pagesResearch in India Happens in A Few Elite Institutions' - The HinduToaster97No ratings yet
- Spice - Gallery Photos in PDFDocument1 pageSpice - Gallery Photos in PDFkeval_kanakharaNo ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Legacy of Vladimir Andreevich Steklov: Mathematician and Leader of Russian ScienceDocument14 pagesThe Legacy of Vladimir Andreevich Steklov: Mathematician and Leader of Russian ScienceToaster97No ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- 40 Functional EquationsDocument2 pages40 Functional EquationsToaster97No ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- How Do I Low-Level Format A SATA or ATA (IDE) Hard DriveDocument2 pagesHow Do I Low-Level Format A SATA or ATA (IDE) Hard DriveToaster97No ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- BibliographyDocument2 pagesBibliographyToaster97No ratings yet
- Research in India Happens in A Few Elite Institutions' - The HinduDocument4 pagesResearch in India Happens in A Few Elite Institutions' - The HinduToaster97No ratings yet
- Differential Equations NotesDocument100 pagesDifferential Equations NotesVasu KodagantiNo ratings yet
- DNA RepairDocument14 pagesDNA RepairToaster97No ratings yet
- Computer Network No.11 (IEEE 802.4, 802.5) From APCOMSDocument6 pagesComputer Network No.11 (IEEE 802.4, 802.5) From APCOMSNaveedNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Communication NotesDocument16 pagesCommunication NotesLuke Irlam100% (1)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- Computer Network No9 Cont Mediam Access Control From APCOMSDocument4 pagesComputer Network No9 Cont Mediam Access Control From APCOMSToaster97No ratings yet
- Car Speed Control Using BluetoothDocument8 pagesCar Speed Control Using BluetoothToaster97No ratings yet
- C and Data Structures Unit Wise Important QuestionsDocument15 pagesC and Data Structures Unit Wise Important QuestionsToaster97100% (1)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Artificial Photo Synthesi w8Document5 pagesArtificial Photo Synthesi w8Toaster97No ratings yet
- Artificial IntelligenceDocument13 pagesArtificial IntelligenceLarry WilliamsonNo ratings yet
- Business CommunicationDocument35 pagesBusiness CommunicationToaster97No ratings yet
- DmaDocument16 pagesDmaavireddy1No ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Dbms Lab ManualDocument99 pagesDbms Lab ManualToaster97No ratings yet
- Cellphones N Calls - Sreevidhya@StudentsDocument21 pagesCellphones N Calls - Sreevidhya@StudentsSumith KumarNo ratings yet
- Membership Savings Remittance Form (MSRF) : HQP-PFF-053Document1 pageMembership Savings Remittance Form (MSRF) : HQP-PFF-053Irene RomeroNo ratings yet
- Canine Courier November 2018Document68 pagesCanine Courier November 2018Eugene UglachNo ratings yet
- Cara Mereset DVR Dan NVR Hikvision CCTV PDFDocument9 pagesCara Mereset DVR Dan NVR Hikvision CCTV PDFTotok TriswantoNo ratings yet
- Cyber Crime NotesDocument110 pagesCyber Crime NotesTushar RanaNo ratings yet
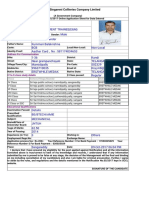
- The Singareni Collieries Company Limited: Address For CommunicationDocument1 pageThe Singareni Collieries Company Limited: Address For Communicationvizay237_430788222No ratings yet
- Exploit Vs PayloadDocument4 pagesExploit Vs PayloadFJRojkinNo ratings yet
- CS 373: Theory of Computation: Manoj Prabhakaran Mahesh Viswanathan Fall 2008Document64 pagesCS 373: Theory of Computation: Manoj Prabhakaran Mahesh Viswanathan Fall 2008Vinay Bangalore NagarajNo ratings yet
- Digital Forensic Tool KitDocument351 pagesDigital Forensic Tool Kitdonkalonk100% (1)
- Anti-Virus Comparative: Performance TestDocument12 pagesAnti-Virus Comparative: Performance Testsanjay sahNo ratings yet
- Import Export Code or IE Code Is Required For Every Person or Firm or Company or Entity Engaged in Export Business in IndiaDocument7 pagesImport Export Code or IE Code Is Required For Every Person or Firm or Company or Entity Engaged in Export Business in IndiamanishaNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Catalog Important SoftwareDocument77 pagesCatalog Important SoftwareSaurabh KoranglekarNo ratings yet
- Comptia Security+ 501: Implementing Compliance and Operational SecurityDocument38 pagesComptia Security+ 501: Implementing Compliance and Operational SecurityArthur KhongNo ratings yet
- Hacking Portable AppsDocument19 pagesHacking Portable AppslgonzalezaNo ratings yet
- 111010Document36 pages111010Yogi54No ratings yet
- Rethinking Borders Beyond The StateDocument19 pagesRethinking Borders Beyond The StateLuiz Felipe CandidoNo ratings yet
- HPXS302 1 Jan Jun2022 T&L W.2 RM V.1 16022022Document2 pagesHPXS302 1 Jan Jun2022 T&L W.2 RM V.1 16022022BonginkosiNo ratings yet
- Call MATLAB Functions - MATLAB & SimulinkDocument5 pagesCall MATLAB Functions - MATLAB & SimulinkLuis Enrique Carmona GutierrezNo ratings yet
- Exercises and answers for programming language class semanticsDocument7 pagesExercises and answers for programming language class semanticsVivo Vivoo VINo ratings yet
- Proper Arrival Times: Calica, Jannah Mae B. 11/14/16 Bsee V-Eb1 Web Exercises Activity 7Document9 pagesProper Arrival Times: Calica, Jannah Mae B. 11/14/16 Bsee V-Eb1 Web Exercises Activity 7Lorenz BanadaNo ratings yet
- Mis 8th Edition Bidgoli Test BankDocument35 pagesMis 8th Edition Bidgoli Test Bankepulotictomaleyrakqbs100% (28)
- Intro To Oracle Nosql DB Hol 1937059Document20 pagesIntro To Oracle Nosql DB Hol 1937059SUN8No ratings yet
- Dep33 Aof With IntroDocument2 pagesDep33 Aof With IntroDesikanNo ratings yet
- RohitDocument75 pagesRohitRobin PalanNo ratings yet
- eCOPS Police Record Management SystemDocument4 pageseCOPS Police Record Management SystemAmirul AsyrafNo ratings yet
- Ryanair vs. Expedia, Cease & Desist LetterDocument5 pagesRyanair vs. Expedia, Cease & Desist LetterGeekWireNo ratings yet
- Gat CheatDocument4 pagesGat Cheatfordbro12No ratings yet
- XSS CheatDocument9 pagesXSS CheatjosephNo ratings yet
- Sam & Max Season One ManualDocument27 pagesSam & Max Season One ManualRoccoGranataNo ratings yet
- Priority Queues: 1 N 1 N 1 N 1 NDocument22 pagesPriority Queues: 1 N 1 N 1 N 1 NjruanNo ratings yet
- RR (Repeatable Read)Document13 pagesRR (Repeatable Read)abjanuaryNo ratings yet
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Scary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldFrom EverandScary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldRating: 4.5 out of 5 stars4.5/5 (54)
- AI and Machine Learning for Coders: A Programmer's Guide to Artificial IntelligenceFrom EverandAI and Machine Learning for Coders: A Programmer's Guide to Artificial IntelligenceRating: 4 out of 5 stars4/5 (2)
- Artificial Intelligence: The Insights You Need from Harvard Business ReviewFrom EverandArtificial Intelligence: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (104)
- Make Money with ChatGPT: Your Guide to Making Passive Income Online with Ease using AI: AI Wealth MasteryFrom EverandMake Money with ChatGPT: Your Guide to Making Passive Income Online with Ease using AI: AI Wealth MasteryNo ratings yet
- Generative AI: The Insights You Need from Harvard Business ReviewFrom EverandGenerative AI: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (2)
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessFrom EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessNo ratings yet