Professional Documents
Culture Documents
Cyber Law and Information Security
Uploaded by
Dreamtech PressCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cyber Law and Information Security
Uploaded by
Dreamtech PressCopyright:
Available Formats
Cyber Law and Information Security
` 299/-
The Cyber Law and Information Security book touches almost every important aspect of cyber law and need of information
security, such as what is cyber law and how is it used to deal with cyber crimes, fundamental concepts of e-commerce (including models and generations of e-commerce, advantages of e-commerce, e-governance and EDI, e-cash, e-payment, and security threats), ethical issues in data and software privacy, Internet security threats, digital signatures, information security, cryptography, VPN, and
Key Features:
Need of cyber law, objective and scope of the IT Act 2000, Indian Cyber Law, Uncitral Model Law u Intellectual property issues and cyber space, overview of intellectual property related to legislation in India, patents, copyrights, u trademarks, law related to semiconductor layout and design Fundamentals of e-commerce, security threats to e-commerce, virtual organization, business transactions on Web, e-governance u and EDI, concepts in electronic payment systems, e-cash, credit/debit cards, e-agreement, legal recognition of electronic and digital records, e-commerce, and issues of privacy Physical security and its need, disaster management and control, basic tenets of physical security, and physical entry controls u statements Access control, biometrics, factors in biometric system, criteria for selection of biometric, design issues in the biometric system, u interoperability issues, economic and social aspects, legal challenges Digital signatures and technical issues, legal issues, electronic records, digital contracts, requirements of the digital signature u system Cyber crime, cyber jurisdiction, cyber crime and evidence act, treatment of cyber crime in different countries, ethical issues in u data and software privacy, plagiarism, pornography, tampering computer documents Internet security threats such as hacking, cracking, viruses, trojan horse, malicious code, and logic bombs u Certifying authorities and their need, appointment, function of controller, generation, suspension, and revocation u Information systems and its importance, role of security in Internet and Web services, principles of information security, u classification of threats and attacks, security challenges, security implication for organizations Introduction to cryptography, issues in documents security, public key, private key, firewalls u Basic concepts of network security, perimeters of network protection and network attack, need of intrusion monitoring, and u detection VPN, tunneling VPN, types of VPN and their usage, security concerns in VPN u Concept of networking, IP addressing and subnetting, DNS, DHCP , bootp, active directory, IIS, NAT, WSUS, exchange server, ISA, u wireless network, and Mobile IP
ISBN: 978-93-5119-200-8 | Price: ` 299 | Pages: 252 | Authors: Faiyaz Ahamad, KLSI
This Book Covers:
t Fundamentals of Cyber Law E-Commerce t Digital Signatures t Investigation of Cyber Crime t Internet Security Threats t t Certifying Authorities Information Security t Cryptography t Basic Concepts of Network Security t Virtual Private Network (VPN) t Concept of Networking t
Table of Contents:
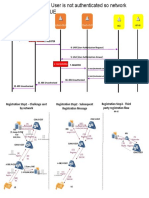
Fundamentals of Cyber Law:History of Internet | Introduction to Indian Cyber Law | Objective and Scope of the IT Act 2000 | Uncitral Model Law | ISP Guideline | Intellectual property issues | Overview of Intellectual property related legislation in India | Patent | Copyright | Trademark law | Law related to semiconductor layout and design | E Commerce: E-Commerce and its Models | Generations of E-commerce | Advantages of E-commerce | EDI | E-Cash and E-Payment Scheme | Business T r a n s a c t i o n s o n We b o r E - T r a n s a c t i o n | Credit/Debit/Smart Cards | E-Commerce in India | Recent Trends in Shopping | Mobile Commerce | EMarketplace Technology | E-Agreement | Legal Recognition of Electronic and Digital Records | Virtual Organisation | Security in E-Commerce: E-Commerce Issues of privacy | Security Threats to E Commerce | Physical Security | Spyware Technology | Access Control | Digital Signatures | Certificate Issuance | Investigation and Ethics: Cybercrime | Cyber/Resource Theft | Types of cyber crimes/frauds | Cyber frauds in India | Cyber jurisdiction | Dealing with cybercrime in various countries | Ethical issues in data and software privacy | Issues in ethical hacking | Internet security threats | Certifying authorities | Cyber crime forensic |
Information Security:Information Systems | Developing Information System | Principles of Information Security | An Overview of Information Security Management System (ISMS) |Classification of Threats and Attacks | Security Implication for Organisations | Information Classification and their Roles | Some other terms in Information Security | Stages of Vulnerability Management | Cr yptography: Understanding Cryptography and Encryption | Understanding Cryptographic Algorithms | Understanding Cryptanalysis | Describing Code Breaking Methodologies | Describing Cryptographic Attacks | Firewalls | Issues in Documents Security | Basic concepts of Network Security | Perimeters of Network protection and Network attack | Common Attacks | Need of Intrusion Monitoring and Detection | Honeypot | VPN | Networking: Concept of Networking | IP Addressing and Subnetting | Domain Name System(DNS) | Protocol | Services | Network Address Translation (NAT) | Server | Internet Security and Acceleration (ISA) | Wireless network | Ethernet | Fiber Distributed Data Interface(FDDI) | Client Server Model | Concurrency | Byte ordering | Network Socket | Zigbee | RAN | MANET |
About the Authors:
Faiyaz Ahamad is currently working as the Assistant Professor at the Department of Computer Science and Information Technology, Integral University, Lucknow (U.P.), India. Prof. Ahamad holds a Masters degree in Information Technology, and is also pursuing his Doctorate from the BBD University, Lucknow. His areas of interest include software engineering, software testing, software architecture, databases, data warehousing and mining, computer simulation and modeling, management information system, and SOA. He has more than 10 years of teaching experience and has also worked as a compliance officer. He did his training for two months in NTPC, Shakti Nagar, Sonebhadra, U.P. and has co-authored six publicationsAn Efficient and Scalable Design of Service Discovery Scheme for Wireless Mesh Network, A Language Independent Approach to Develop Urdu Stemmer, Secure Key Pre Distribution in Wireless Sensor Networks Using Combinatorial Design and Traversal Design Based Key Distribution, Scalable Design of Service Discovery Mechanism for Ad-hoc Network Using Wireless Mesh Network, Encrypting Data Using the Features of Mimetic Algorithm and Cryptography, and Service Discovery Mechanism for WLAN. The proficient teams at Kogent Learning Solutions Inc. and Dreamtech Press have seized the market of engineering textbooks, bringing excellent content in engineering and technical education to the fore. These teams are committed to providing excellence in the quality of content by judiciously analyzing the needs of their readers and ensuring dedication of their authors and editors in catering to these needs.
Published by:
DREAMTECH PRESS
19-A, Ansari Road, Daryaganj New Delhi-110 002, INDIA Tel: +91-11-2324 3463-73, Fax: +91-11-2324 3078 Email: feedback@dreamtechpress.com Website: www.dreamtechpress.com
WILEY INDIA PVT. LTD.
4435-36/7, Ansari Road, Daryaganj New Delhi-110 002, INDIA Tel: +91-11-4363 0000, Fax: +91-11-2327 5895 Email: csupport@wiley.com Website: www.wileyindia.com
Exclusively Distributed by:
Regional Offices: Bangalore: Tel: +91-80-2313 2383, Fax: +91-80-2312 4319, Email: blrsales@wiley.com Mumbai: Tel: +91-22-2788 9263, 2788 9272, Telefax: +91-22-2788 9263, Email: mumsales@wiley.com Contact Persons: Raju Joseph: +91-9845065992 | Sandeep Rao: +91-9620215542 | Arun Kumar: +91-9611231170
/dtechpress
/dtechpress
/dreamtechpress
/company/dreamtech-press
You might also like
- Introduction To Cyber Law.Document25 pagesIntroduction To Cyber Law.Guru PrasadNo ratings yet
- Information Technology ActDocument53 pagesInformation Technology ActKaustubh Barve100% (1)
- Syracuse Media ListDocument4 pagesSyracuse Media Listapi-356565018No ratings yet
- Learning With PythonDocument2 pagesLearning With PythonDreamtech PressNo ratings yet
- Introduction To Information Security and Cyber LawsDocument2 pagesIntroduction To Information Security and Cyber LawsDreamtech Press80% (5)
- Intermediate Written Chinese - Read and Write Mandarin Chinese As The Chinese Do (PDFDrive)Document380 pagesIntermediate Written Chinese - Read and Write Mandarin Chinese As The Chinese Do (PDFDrive)Sally100% (1)
- Legal Issues of Electronic SignatureDocument13 pagesLegal Issues of Electronic SignatureParvathy KarthaNo ratings yet
- Mergers & Acquisitions and Corporate ValuationDocument2 pagesMergers & Acquisitions and Corporate ValuationDreamtech Press0% (1)
- Digital SignatureDocument13 pagesDigital Signaturevart1992No ratings yet
- Digital Signature Seminar ReportDocument20 pagesDigital Signature Seminar ReportMukesh Chetwani0% (1)
- PRO/Engineer PTC Creo Parametric 3.0Document2 pagesPRO/Engineer PTC Creo Parametric 3.0Dreamtech Press33% (9)
- Learning Bentley STAAD Pro V8i For Structural AnalysisDocument2 pagesLearning Bentley STAAD Pro V8i For Structural AnalysisDreamtech Press42% (12)
- Electronic and Digital SignatureDocument16 pagesElectronic and Digital SignatureParthNo ratings yet
- The Principles of Teaching SpeakingDocument35 pagesThe Principles of Teaching SpeakingLJ Jamin CentinoNo ratings yet
- Electronic Evidence AND Judicial Approach: Rajasthan State Judicial AcademyDocument13 pagesElectronic Evidence AND Judicial Approach: Rajasthan State Judicial AcademyharshNo ratings yet
- Social Media Analytics Unit-1Document43 pagesSocial Media Analytics Unit-1karunakar yadavNo ratings yet
- R in Action, Second EditionDocument2 pagesR in Action, Second EditionDreamtech Press0% (1)
- Information Technology Act 2000-AL PDFDocument77 pagesInformation Technology Act 2000-AL PDFRicha Rajpal100% (2)
- Legal Regulation of Cyber Crimes in IndiaDocument9 pagesLegal Regulation of Cyber Crimes in IndiaSwarnaprava DashNo ratings yet
- Big Data Black BookDocument2 pagesBig Data Black BookDreamtech Press17% (24)
- Cyber Arbitration 17decDocument8 pagesCyber Arbitration 17decApala ChaturvediNo ratings yet
- Digital Signature Project ReportDocument27 pagesDigital Signature Project ReportSurabhi Agrawal50% (14)
- Ruby ProgrammingDocument2 pagesRuby ProgrammingDreamtech PressNo ratings yet
- Tender Management System - DZDocument14 pagesTender Management System - DZAjie Ekpere100% (1)
- Digital Signature Vs Electronic SignatureDocument2 pagesDigital Signature Vs Electronic SignatureAjay KumarNo ratings yet
- Spring in Action Fourth EditionDocument2 pagesSpring in Action Fourth EditionDreamtech Press0% (4)
- Sap ABAPDocument1 pageSap ABAPDreamtech PressNo ratings yet
- Digital Technology and Media LiteracyDocument31 pagesDigital Technology and Media LiteracyE-dlord M-alabanan0% (1)
- Iot Lecture Notes Modified 0Document87 pagesIot Lecture Notes Modified 0VINOD DNo ratings yet
- Introducing Data ScienceDocument2 pagesIntroducing Data ScienceDreamtech Press0% (1)
- Cyber Law (Optional)Document4 pagesCyber Law (Optional)Kshitij Nawarang0% (1)
- Digital Signature Standard and DSA AlgorithmDocument4 pagesDigital Signature Standard and DSA AlgorithmSajendra KumarNo ratings yet
- A Computational Introduction To Number Theory and Algebra - Version 2 - Errata - Victor ShoupDocument1 pageA Computational Introduction To Number Theory and Algebra - Version 2 - Errata - Victor ShouphexramNo ratings yet
- Digital Signature Seminar ReportDocument15 pagesDigital Signature Seminar ReportAshish RajNo ratings yet
- Digital SignatureDocument26 pagesDigital SignatureNeha Dabhi100% (1)
- Project Report (Digital Signatures)Document33 pagesProject Report (Digital Signatures)Uzair Shakeel0% (1)
- E-Mail Related CrimesDocument5 pagesE-Mail Related Crimesvarunendra pandey50% (2)
- Cyber Law Sections With CasesDocument34 pagesCyber Law Sections With CasesnandynanduNo ratings yet
- Introduction To Cyber WorldDocument24 pagesIntroduction To Cyber WorldSufyan TariqNo ratings yet
- Electronic Evidence in Civil Proceedings in IndiaDocument11 pagesElectronic Evidence in Civil Proceedings in IndiaNordsci ConferenceNo ratings yet
- 3.security Issues in E-Procurement (PKI)Document50 pages3.security Issues in E-Procurement (PKI)Rohit BediNo ratings yet
- Digital Signature ProjectDocument87 pagesDigital Signature ProjectSuresh Neharkar100% (1)
- Electronic Signature From Your Scanned Digital SignatureDocument29 pagesElectronic Signature From Your Scanned Digital SignatureVamsi VelagalaNo ratings yet
- Electronic SignatureDocument21 pagesElectronic SignatureAniruddha ShindeNo ratings yet
- TASK - SCHEDULING MCDM PDFDocument17 pagesTASK - SCHEDULING MCDM PDFMunmun SahaNo ratings yet
- Cyber LawDocument11 pagesCyber LawTAJ AHAMED100% (1)
- Awt Difference Between Genericservlet and Httpservlet: GenericservletDocument6 pagesAwt Difference Between Genericservlet and Httpservlet: GenericservletAniket RaneNo ratings yet
- Cloud Seminar ReportDocument14 pagesCloud Seminar ReportSketNo ratings yet
- 8th Sem 1stDocument15 pages8th Sem 1stpuneet kumar verma100% (2)
- Srs Project Visually ImpairedDocument2 pagesSrs Project Visually ImpairedShivam Mittal67% (3)
- A Flight Fare Prediction Using Machine LearningDocument8 pagesA Flight Fare Prediction Using Machine LearningIJRASETPublicationsNo ratings yet
- Public Policy Principles For Electronic Commerce and InsuranceDocument8 pagesPublic Policy Principles For Electronic Commerce and Insuranceb_1980b2148No ratings yet
- What Is Electronic EvidenceDocument11 pagesWhat Is Electronic Evidenceyashc09100% (1)
- The Simple Guide To Electronic Signature WorkflowsDocument6 pagesThe Simple Guide To Electronic Signature WorkflowsAkicaNo ratings yet
- Case Study Digital SignatureDocument7 pagesCase Study Digital Signaturedaveharshil31100% (2)
- Detection of Url Based Phishing Attacks Using Machine Learning IJERTV8IS110269Document8 pagesDetection of Url Based Phishing Attacks Using Machine Learning IJERTV8IS110269ITWorldNo ratings yet
- Digital SignatureDocument19 pagesDigital SignatureGaurav Kumar100% (1)
- Career Objective: Key Strength: Communication/Co-operation & Co-ordination/PromptnessDocument4 pagesCareer Objective: Key Strength: Communication/Co-operation & Co-ordination/PromptnessAbhishek MalepatiNo ratings yet
- Introduction To Project: State Bank of IndiaDocument79 pagesIntroduction To Project: State Bank of IndiaAru.SNo ratings yet
- 8 Rules: For E-Signature SecurityDocument48 pages8 Rules: For E-Signature SecurityKaye Reyes-RoldanNo ratings yet
- Seminar Digital SignatureDocument11 pagesSeminar Digital Signaturegarima_gaur27No ratings yet
- Cyber Law Unit 1Document60 pagesCyber Law Unit 1ShreyaNo ratings yet
- Indian Army C++ ProjectDocument34 pagesIndian Army C++ ProjectAbhinav KushwahNo ratings yet
- Unit-Iv Cyber-Crime and The Legal Landscape Around The WorldDocument20 pagesUnit-Iv Cyber-Crime and The Legal Landscape Around The WorldayushNo ratings yet
- IT Project LLMDocument23 pagesIT Project LLMsoumilNo ratings yet
- Client Server Software EngineeringDocument9 pagesClient Server Software EngineeringShagufta Raza0% (1)
- Cyber Defamation in IndiaDocument5 pagesCyber Defamation in IndiaHitesh BansalNo ratings yet
- Project Currency Converter JavaDocument16 pagesProject Currency Converter JavaHARESH.SNo ratings yet
- KPMG Flash News CBDT Notifies Revised Safe Harbour Rules 2Document6 pagesKPMG Flash News CBDT Notifies Revised Safe Harbour Rules 2Piyush AggarwalNo ratings yet
- Digital SignatureDocument19 pagesDigital SignatureRanu Sharma100% (1)
- Mca Degree SubjectsDocument2 pagesMca Degree SubjectsVarun UpadhyayNo ratings yet
- ManagementDocument16 pagesManagementAbhishek KhandekarNo ratings yet
- Digital Awareness Cyber SecurityDocument110 pagesDigital Awareness Cyber SecurityAjay PatelNo ratings yet
- Key Features of The Book:: ISBN: 978-93-5119-208-4 - PriceDocument2 pagesKey Features of The Book:: ISBN: 978-93-5119-208-4 - PriceDreamtech Press0% (1)
- J2EE 1.7 Projects Black BookDocument2 pagesJ2EE 1.7 Projects Black BookDreamtech Press0% (3)
- Building The Web of ThingsDocument2 pagesBuilding The Web of ThingsDreamtech PressNo ratings yet
- MongoDB in ActionDocument2 pagesMongoDB in ActionDreamtech PressNo ratings yet
- Wireless Technology (Includes Practicals)Document2 pagesWireless Technology (Includes Practicals)Dreamtech Press0% (1)
- Getting Mean With Mongo, Express, Angular, and NodeDocument2 pagesGetting Mean With Mongo, Express, Angular, and NodeDreamtech PressNo ratings yet
- Pro Spring, 4th EditionDocument1 pagePro Spring, 4th EditionDreamtech PressNo ratings yet
- Financial DerivativesDocument2 pagesFinancial DerivativesDreamtech PressNo ratings yet
- Object Oriented Programming Using JavaDocument2 pagesObject Oriented Programming Using JavaDreamtech Press0% (1)
- Cloud ComputingDocument2 pagesCloud ComputingDreamtech PressNo ratings yet
- Software Project Management (Includes Practicals)Document2 pagesSoftware Project Management (Includes Practicals)Dreamtech PressNo ratings yet
- System ProgrammingDocument2 pagesSystem ProgrammingDreamtech Press25% (4)
- Pro Angular JS (Apress)Document1 pagePro Angular JS (Apress)Dreamtech PressNo ratings yet
- Practical Business Analytics Using SAS A Hands-On GuideDocument1 pagePractical Business Analytics Using SAS A Hands-On GuideDreamtech PressNo ratings yet
- Pro Apache Hadoop 2nd EditionDocument1 pagePro Apache Hadoop 2nd EditionDreamtech Press100% (1)
- Research AnalyticsDocument2 pagesResearch AnalyticsDreamtech Press25% (4)
- Java 8 Programming Black BookDocument2 pagesJava 8 Programming Black BookDreamtech Press31% (36)
- Groovy in Action, Second EditionDocument2 pagesGroovy in Action, Second EditionDreamtech PressNo ratings yet
- Big DataDocument2 pagesBig DataDreamtech Press0% (1)
- Storm AppliedDocument2 pagesStorm AppliedDreamtech PressNo ratings yet
- Company Profile TheConversionDocument31 pagesCompany Profile TheConversionAfter MathNo ratings yet
- Gpon An5506 02BDocument8 pagesGpon An5506 02Bivan andres aguirre arrietaNo ratings yet
- Lesson Plan Template Flag 10Document3 pagesLesson Plan Template Flag 10api-317303624No ratings yet
- Komunikasi Antarbudaya Mahasiswa Malaysia Dan Indonesia Fakultas Dakwah Dan Komunikasi Universitas Islam Negeri (Uin) Sumatera UtaraDocument21 pagesKomunikasi Antarbudaya Mahasiswa Malaysia Dan Indonesia Fakultas Dakwah Dan Komunikasi Universitas Islam Negeri (Uin) Sumatera UtaraLilian Arifka JulyNo ratings yet
- Network Layer Architecture and Types of ProtocolDocument3 pagesNetwork Layer Architecture and Types of ProtocolSuryanshNo ratings yet
- Pass Res B1plus CST 2BDocument1 pagePass Res B1plus CST 2BLusi LoveNo ratings yet
- Instructional StrategiesDocument2 pagesInstructional StrategiesEllie BrownNo ratings yet
- 4 THE PARTNERSHIP APPROACH TO COMMUNITY HEALTH PRACTICE Mam ThaiDocument14 pages4 THE PARTNERSHIP APPROACH TO COMMUNITY HEALTH PRACTICE Mam ThaiKasandra Dawn Moquia BerisoNo ratings yet
- A-Sbc/P-Cscf Slrm/I-Cscf CSM/S-CSCF: 1. RegisterDocument2 pagesA-Sbc/P-Cscf Slrm/I-Cscf CSM/S-CSCF: 1. RegisterClaudiu CiobanuNo ratings yet
- EssayDocument10 pagesEssayapi-245632465No ratings yet
- Interaction Design Lab - Week 03Document4 pagesInteraction Design Lab - Week 03Kim Long67% (3)
- Self-Evaluation Lesson Plan 1Document2 pagesSelf-Evaluation Lesson Plan 1api-350083105No ratings yet
- 2scaffolding As A Teaching StrategyDocument15 pages2scaffolding As A Teaching StrategyTriharyatiNo ratings yet
- Ca 12 Module 2Document4 pagesCa 12 Module 2Patricia TorrecampoNo ratings yet
- English: Sources of Media and InformationDocument14 pagesEnglish: Sources of Media and InformationRei GúnNo ratings yet
- Review TestDocument12 pagesReview Test2003camtuNo ratings yet
- Name Rediet FantuDocument2 pagesName Rediet FanturedietNo ratings yet
- 300 S 20 Syllabus (2) 4Document13 pages300 S 20 Syllabus (2) 4jesseNo ratings yet
- 3GPP TR 23.871Document27 pages3GPP TR 23.871santanameroNo ratings yet
- BSS 1030 - TEST ONE - June 2023 - FULLTIMEDocument5 pagesBSS 1030 - TEST ONE - June 2023 - FULLTIMEMulenga NkoleNo ratings yet
- English Language Learners: Developing Literacy in Second-Language Learners-Report of The National Literacy Panel On Language-Minority Children and YouthDocument21 pagesEnglish Language Learners: Developing Literacy in Second-Language Learners-Report of The National Literacy Panel On Language-Minority Children and YouthLedi Wakha WakhaNo ratings yet
- Impact of Social Media On SocietyDocument2 pagesImpact of Social Media On SocietytinaantonyNo ratings yet
- Pointers For Writing A ConclusionDocument4 pagesPointers For Writing A Conclusioncoolest51100% (1)
- Integrated Unit LessonDocument3 pagesIntegrated Unit Lessonapi-609086308No ratings yet
- Pip ProposalDocument2 pagesPip Proposalapi-288700696No ratings yet
- Word & Image: A Journal of Verbal/Visual EnquiryDocument9 pagesWord & Image: A Journal of Verbal/Visual EnquirySáraÍriszPappNo ratings yet