Professional Documents
Culture Documents
CNDC Lab File (Pankaj)
Uploaded by
Pankaj BishtOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CNDC Lab File (Pankaj)
Uploaded by
Pankaj BishtCopyright:
Available Formats
1
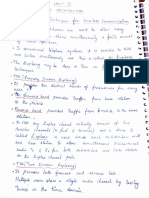
PRACTICAL NO. 1
AIM: To study different types of transmission media types. THEORY: TRANSMISSION MEDIA TYPE: The first layer (physical layer) of Communication Networks the OSI Seven layer model is dedicated to the transmission media. Due to the variety of transmission media and network wiring methods, selecting the most appropriate media can be confusing - what is the optimal cost-effective solution.
Classes of transmission media:
1.GUIDED(WIRED): The transmission capacity, in terms of either data rate or bandwidth, depends critically on the distance and on whether the medium is point-to-point or multipoint. 1.1 Twisted pair 1.2 Coaxial cable 1.3 Fiber optics cable
PANKAJ BISHT
CSE 7th SEM
45380
1.1 TWISTED PAIR: The least expensive and most widely used guided transmission medium is twisted pair. Twisted-pair cable is a type of cabling that is used for telephone communications and most modern Ethernet networks. A pair of wires forms a circuit that can transmit data. The pairs are twisted to provide protection against crosstalk, the noise generated by adjacent pairs. When electrical current flows through a wire, it creates a small, circular magnetic field around the wire. When two wires in an electrical circuit are placed close together, their magnetic fields are the exact opposite of each other. Thus, the two magnetic fields cancel each other out. They also cancel out any outside magnetic fields. Twisting the wires can enhance this cancellation effect. Using cancellation together with twisting the wires, cable designers can effectively provide self-shielding for wire pairs within the network media.
TWISTED PAIR CABLE
PANKAJ BISHT
CSE 7th SEM
45380
TYPES OF TWISTED PAIR: 1. UTP (unshielded twisted pair):This cable is a medium that is composed of pairs of wires . UTP cable is used in a variety of networks. Each of the eight individual copper wires in UTP cable is covered by an insulating material. In addition, the wires in each pair are twisted around each other. 2.Shielded Twisted-Pair Cable: Shielded twisted-pair (STP) cable combines the techniques of shielding, cancellation, and wire twisting. Each pair of wires is wrapped in a metallic foil . The four pairs of wires then are wrapped in an overall metallic braid or foil, usually 150-ohm cable. As specified for use in Ethernet network installations, STP reduces electrical noise both within the cable (pair-to-pair coupling, or crosstalk) and from outside the cable (EMI and RFI). STP usually is installed with STP data connector, which is created especially for the STP cable. However, STP cabling also can use the same RJ connectors that UTP uses.
1.2. COAXIAL CABLE 1. Physical Description: Coaxial cable, like twisted pair, consists of two conductors, but is constructed differently to permit it to operate over a wider range of frequencies. It consists of a hollow outer cylindrical conductor that surrounds a single inner wire conductor . The inner conductor is held in place by either regularly spaced insulating rings or a solid dielectric material. The outer conductor is covered with a jacket or shield. A single coaxial cable has a diameter of from 1 to 2.5 cm. Coaxial cable can be used over longer distances and support more stations on a shared line than twisted pair. 2. Applications: Coaxial cable is perhaps the most versatile transmission medium and is enjoying Wide spread use in a wide variety of applications. The most important of these are Television distribution Long-distance telephone transmission Short-run computer system links Local area networks
PANKAJ BISHT
CSE 7th SEM
45380
3.Transmission Characteristics: Coaxial cable is used to transmit both analog and digital signals. As can be seen from coaxial cable has frequency characteristics that are superior to those of twisted pair, and can hence be used effectively at higher frequencies and data rates. Because of its shielded, concentric construction, coaxial cable is much less susceptible to interference and crosstalk than twisted pair. The principal constraints on performance are attenuation, thermal noise, and intermodulation noise.
PANKAJ BISHT
CSE 7th SEM
45380
1.3. OPTICAL FIBER:
1. Physical Description: An optical fiber is a thin , flexible medium capable of guiding an optical ray. Various glasses and plastics can be used to make optical fibers. The lowest losses have difficult to manufacture; higher-loss multi component glass fibers are more economical and still provide good performance. Plastic fiber is even less costly and can be used for short-haul links, for which moderately high losses are acceptable. An optical fiber cable has a cylindrical shape and consists of three concentric sections: the core, the cladding, and the jacket . The core is the innermost section and consists of one or more very thin strands, or fibers, made of glass or plastic; the core has a diameter in the range of 8 to Each fiber is surrounded by its own cladding, a glass or plastic coating that has optical properties different from those of the core. The interface between the core and cladding acts as a reflector to confine light that would otherwise escape the core. The outermost layer, surrounding one or a bundle of cladded fibers, is the jacket. The jacket is composed of plastic and other material layered to protect against moisture, abrasion, crushing, and other environmental dangers. 2. Applications: One of the most significant technological breakthroughs in data transmission has been the development of practical fiber optic communications systems. Optical fiber already enjoys considerable use in long-distance telecommunications, and its use in military applications is growing. The continuing improvements in performance and decline in prices, together with the inherent advantages of optical fiber, have made it increasingly attractive for local area networking. 2. UNGUIDED MEDIA (WIRELESS): Unguided media transport electromagnetic waves without using a physical conductor. This type of communication is often referred to as wireless communication.
PANKAJ BISHT
CSE 7th SEM
45380
1.Radio Waves 2.Microwaves 3.Infrared
1. RADIO WAVES: Radio waves are used for multicast communications, such as radio and Television and paging systems. 2. MICROWAVE: Microwaves are used for unicast communication such as cellular telephones, satellite networks, and wireless LANs. 3. INFRARED: Infrared signals can be used for short range communication in a closed area using line-of-sight propagation.
PANKAJ BISHT
CSE 7th SEM
45380
PRACTICAL NO. -2
AIM: To study different types of topologies. THEORY: Computer network topology is the way various components of a network (like nodes, links, peripherals, etc.) are arranged. Network topologies define the layout, virtual shape or structure of network, not only physically but also logically. The way in which different systems and nodes are connected and communicate with each other is determined by topology of the network. Topology can be physical or logical. Physical Topology is the physical layout of nodes, workstations and cables in the network; while logical topology is the way information flows between different components. Types of Physical Network Topologies 1) 2) 3) 4) 5) 6) Bus Topology Star Topology Ring Topology Mesh Topology Tree Topology Hybrid Topology
1)BUS TOPOLOGY: Bus Topology is the simplest of network topologies. In this type of topology, all the nodes (computers as well as servers) are connected to the single cable (called bus), by the help of interface connectors. This central cable is the backbone of the network and is known as Bus . Every workstation communicates with the other device through this Bus.
PANKAJ BISHT
CSE 7th SEM
45380
Advantages of Linear Bus Topology 1) It is easy to set-up and extend bus network. 2) Cable length required for this topology is the least compared to other networks. 3) Bus topology costs very less. 4) Linear Bus network is mostly used in small networks. Good for LAN. Disadvantages of Linear Bus Topology 1) There is a limit on central cable length and number of nodes that can be connected. 2) Dependency on central cable in this topology has its disadvantages. If the main cable (i.e. bus ) encounters some problem, whole network breaks down. 3) Proper termination is required to dump signals. Use of terminators is must.
2) STAR TOPOLOGY: In Star topology, all the components of network are connected to the central device called hub which may be a hub, a router or a switch. Unlike Bus topology, where nodes were connected to central cable, here all the workstations are connected to central device with a point-to-point connection. So it can be said that every computer is indirectly connected to every other node by the help of hub. All the data on the star topology passes through the central device before reaching the intended destination. Hub acts as a junction to connect different nodes present in Star Network, and at the same time it manages and controls whole of the network. Depending on which central device is used, hub can act as repeater or signal booster. Central device can also communicate with other hubs of different network. Unshielded Twisted Pair (UTP) Ethernet cable is used to connect workstations to central node.
Advantages of Star Topology 1) Easy to connect new nodes or devices. In star topology new nodes can be added easily without affecting rest of the network. Similarly components can also be removed easily. 2) Centralized management. It helps in monitoring the network. 3) Failure of one node or link doesnt affect the rest of network. At the same time its easy to detect the failure and troubleshoot it.
PANKAJ BISHT CSE 7th SEM 45380
Disadvantages of Star Topology 1) Too much dependency on central device has its own drawbacks. If it fails whole network goes down. 2) The use of hub, a router or a switch as central device increases the overall cost of the network. 3) Performance and as well number of nodes which can be added in such topology is depended on capacity of central device.
3)RING TOPOLOGY: In Ring Topology, all the nodes are connected to each-other in such a way that they make a closed loop. Each workstation is connected to two other components on either side, and it communicates with these two adjacent neighbors. Data travels around the network, in one direction. Sending and receiving of data takes place by the help of TOKEN. Token Passing : Token contains a piece of information which along with data is sent by the source computer. This token then passes to next node, which checks if the signal is intended to it. If yes, it receives it and passes the empty to into the network, otherwise passes token along with the data to next node. This process continues until the signal reaches its intended destination. The nodes with token are the ones only allowed to send data. Other nodes have to wait for an empty token to reach them. This network is usually found in offices, schools and small buildings.
Advantages of Ring Topology 1) This type of network topology is very organized. Each node gets to send the data when it receives an empty token. This helps to reduces chances of collision. Also in ring topology all the traffic flows in only one direction at very high speed. 2) Even when the load on the network increases, its performance is better than that of Bus topology.
PANKAJ BISHT
CSE 7th SEM
45380
10
3) There is no need for network server to control the connectivity between workstations. 4) Additional components do not affect the performance of network. 5) Each computer has equal access to resources. Disadvantages of Ring Topology 1) Each packet of data must pass through all the computers between source and destination. This makes it slower than Star topology. 2) If one workstation or port goes down, the entire network gets affected. 3) Network is highly dependent on the wire which connects different components. 4) MAUs and network cards are expensive as compared to Ethernet cards and hubs.
4) MESH TOPOLOGY: In a mesh network topology, each of the network node, computer and other devices, are interconnected with one another. Every node not only sends its own signals but also relays data from other nodes. In fact a true mesh topology is the one where every node is connected to every other node in the network. This type of topology is very expensive as there are many redundant connections, thus it is not mostly used in computer networks. It is commonly used in wireless networks. Flooding or routing technique is used in mesh topology.
Types of Mesh Network topologies:1) Full Mesh Topology:In this, like a true mesh, each component is connected to every other component. Even after considering the redundancy factor and cost of this network, its main advantage is that the network traffic can be redirected to other nodes if one of the nodes goes down. Full mesh topology is used only for backbone networks. 2) Partial Mesh Topology:This is far more practical as compared to full mesh topology. Here, some of the systems are connected in similar fashion as in mesh topology while rests of the systems are only connected to 1 or 2 devices. It can be said that in partial mesh, the workstations are indirectly connected to other devices. This one is less costly and also reduces redundancy.
PANKAJ BISHT
CSE 7th SEM
45380
11
Advantages of Mesh topology 1) Data can be transmitted from different devices simultaneously. This topology can withstand high traffic. 2) Even if one of the components fails there is always an alternative present. So data transfer doesnt get affected. 3) Expansion and modification in topology can be done without disrupting other nodes. Disadvantages of Mesh topology 1) There are high chances of redundancy in many of the network connections. 2) Overall cost of this network is way too high as compared to other network topologies. 3) Set-up and maintenance of this topology is very difficult. Even administration of the network is tough.
5 ) TREE TOPOLOGY: Tree Topology integrates the characteristics of Star and Bus Topology. Earlier we saw how in Physical Star network Topology, computers (nodes) are connected by each other through central hub. And we also saw in Bus Topology, work station devices are connected by the common cable called Bus. After understanding these two network configurations, we can understand tree topology better.
PANKAJ BISHT
CSE 7th SEM
45380
12
Advantages of Tree Topology 1. It is an extension of Star and bus Topologies, so in networks where these topologies can't be implemented individually for reasons related to scalability, tree topology is the best alternative. 2. Expansion of Network is possible and easy. 3. Here, we divide the whole network into segments (star networks), which can be easily managed and maintained. Disadvantages of Tree Topology 1.Because of its basic structure, tree topology, relies heavily on the main bus cable, if it breaks whole network is crippled. 2. As more and more nodes and segments are added, the maintenance becomes difficult. 3. Scalability of the network depends on the type of cable used.
6) HYBRID TOPOLOGY: A network topology is a connection of various links and nodes, communicating with each other for transfer of data. We also saw various advantages and disadvantages of Star, Bus, Ring, Mesh and Tree topologies. Hybrid, as the name suggests, is mixture of two different things. Similarly in this type of topology we integrate two or more different topologies to form a resultant topology which has good points(as well as weaknesses) of all the constituent basic topologies rather than having characteristics of one specific topology. This combination of topologies is done according to the requirements of the organization. .
Advantages of Hybrid Network Topology 1) Reliable : Unlike other networks, fault detection and troubleshooting is easy in this type of topology. The part in which fault is detected can be isolated from the rest of network and required corrective measures can be taken, WITHOUT affecting the functioning of rest of the network.
PANKAJ BISHT CSE 7th SEM 45380
13
2) Scalable: Its easy to increase the size of network by adding new components, without disturbing existing architecture. 3) Flexible: Hybrid Network can be designed according to the requirements of the organization and by optimizing the available resources. Special care can be given to nodes where traffic is high as well as where chances of fault are high. 4) Effective: Hybrid topology is the combination of two or more topologies, so we can design it in such a way that strengths of constituent topologies are maximized while there weaknesses are neutralized. Disadvantages of Hybrid Topology 1) Complexity of Design: One of the biggest drawback of hybrid topology is its design. Its not easy to design this type of architecture and its a tough job for designers. Configuration and installation process needs to be very efficient. 2) Costly Hub: The hubs used to connect two distinct networks, are very expensive. These hubs are different from usual hubs as they need to be intelligent enough to work with different architectures and should be function even if a part of network is down. 3) Costly Infrastructure: As hybrid architectures are usually larger in scale, they require a lot of cables, cooling systems, sophisticate network devices, etc.
PANKAJ BISHT
CSE 7th SEM
45380
14
PRACTICAL NO. 3 AIM: To study Router Configuration using Packet Tracer Simulator. THEORY & COMMANDS: Packet Tracer is a powerful emulator that provides all the tools for setting up an efficient computer network. It works on CLI (Command Line Interface) configuration. As far as its working modes are concerned then it works in three modes: User Mode Privilege Mode Global Mode
As the name suggests, User Mode is the mode where all the users can work freely (without need of any password or something like). It deals with initial level settings. On the other side, Privilege Mode is a high end PT mode which deals with entry level settings of network. It includes commands for the terminal mode, clock, interface etc. Global Mode has the highest degree as customization. It is a protected mode which deals with highest level of network configuration. It allows users to set passwords, interfacing two devices etc.
PANKAJ BISHT
CSE 7th SEM
45380
15
Main Commands used are: 1. En or Enable: This command is used to get switched from User Mode to Privilege Mode. 2. Show flash: It shows system flash directory.
3. Show version: It shows Cisco Packet Tracer version. We are working on Version 12.4 iteration.
PANKAJ BISHT
CSE 7th SEM
45380
16
4. Show interface: This command shows the connection status with system addressing details.
5. Show ip interface: It deals with Internet Protocol Processing. It provides detail about status of working connection ports of device. 6. Show clock: It displays the clock.
7. Clock set: this command is used to edit and set clock for new time. Syntax: clock set HH:MM:SS & DD:MM:YY 8. Show history: This command shows the history of recently used commands in CLI terminal. 9. Config t or Config terminal: This command is used to enter to global mode.
10. Hostname: it changes the host name. Syntax: hostname new host name
PANKAJ BISHT
CSE 7th SEM
45380
17
11. No hostname: This command is used when no host name is required. It vanishes all the changes that are made to host name.
12. Enable password: It is used to enable the password to enter to privilege or global mode. Its syntax is written as: enable password password.
13. Enable secret password: This command is used in combination with enable password and helps to execute the password properly. Its syntax is: enable password password. 14.Service password encryption: This commands shows the password in aster sticks. 15.No enable password: Used to remove the password. Syntax is: no enable password password
PANKAJ BISHT
CSE 7th SEM
45380
18
PRACTICAL NO.4
AIM-: To study router to router configuration.
STEPS:1. Take two routers.
2. 3. 4. 5.
Double click on first router. Now a window is displayed. After that turn off the switch. Drag the WIC-2T module and turn on the switch. Click on CLI command after that enter these commands as shown in fig. below:
PANKAJ BISHT
CSE 7th SEM
45380
19
6.
Perform the same steps for second router except the clock rate.Then the router will be
connected successfully and node will blink green.
7.
Now use the ping command for success rate.
PANKAJ BISHT
CSE 7th SEM
45380
20
PRACTICAL NO.5 AIM:- To study interfacing of 10 PCs with one switch and two routers. STEPS:1. Take two router , one switch and 10 PCs. 2. Do connection between two routers by using commands and also connect switch.
3. 4. 5.
Now connect the 10 PCs with the switch. After that assign the IP to each PC. Now check the success rate
by
using
the
ping
command.
PANKAJ BISHT
CSE 7th SEM
45380
21
PANKAJ BISHT
CSE 7th SEM
45380
22
PRACTICAL NO.-6 AIM: To study the various protocols in OSI model. THEORY: OSI protocols are a family of standards for information exchange. These were developed and designed by the International Organization of Standardization (ISO). In 1977 the ISO model was introduced, which consisted of seven different layers. Each layer of the ISO model has its own protocols and functions. The OSI protocol stack was later adapted into the TCP/IP stack. In some networks, protocols are still popular using only the data link and network layers of the OSI model. The OSI protocol stack works on a hierarchical form, from the hardware physical layer to the software application layer. There are a total of seven layers. Data and information are received by each layer from an upper layer. After the required processing, this layer then passes the information on to the next lower layer. A header is added to the forwarded message for the convenience of the next layer. Each header consists of information such as source and destination addresses, protocol used, sequence number and other flow-control related data. The following are the OSI protocols used in the seven layers of the OSI Model: 7 Layers of OSI THE 7 LAYERS OF OSI Sender Transmit Application Presentation Session Transport Network Data link Physical LAYER 7 LAYER 6 LAYER 5 LAYER 4 LAYER 3 LAYER 2 LAYER 1 Receiver Application Presentation Session Transport Network Data link Physical Receive
PANKAJ BISHT
CSE 7th SEM
45380
23
The ISO (International Organization for Standardization) decided to construct a framework of standards in which different vendors would be able to use in order to communicate over a network consisting of diverse equipment and applications. This framework is now considered the standard for communication of networks. The OSI is divided into 7 layers, which divides the task into smaller more manageable task groups. Each task or group of tasks assigned to each layer can also be implemented independently. This limits complications between layers because the solutions offered by one layer do not adversely affect the other layers. LAYER 7 - APPLICATION LAYER The application level provides services that directly support the user applications, such as user interface, e-mail, file transfer, database access, etc. There are many protocols at this layer that are commonly needed such as HTTP, WWW, FTP, TELNET, SMTP. It gives applications access to the network through the layers below. Another important function is file transfer between computers. Some computers store file names or represent text lines differently. The application layer takes care of the incompatibilities and allows a smooth transfer between systems. Protocols: FTP, HTTP, SMTP, DNS, TFTP, NFS, TELNET. 1 .FTP (File Transfer Protocol) - Used to transfer files over the internet using TCP/IP. 2. HTTP (Hypertext Transfer Protocol) - Underlining protocol used by the World Wide Web. Allows Web servers and browsers to communicate with each other. 3. SMTP (Simple Mail Transfer Protocol) - Protocol used to send email messages between servers. 4. DNS (Domain Name Service) - An internet service that translates domain names, such as www.yahoo.com, into IP addresses. 5. TFTP (Trivial File Transfer Protocol) - Simplified version of the FTP protocol which has no security features. 6. NFS (Network File System) - Client/Server application designed by SUN MICROSYSTEMS to allow all network users to access files stored on different computer types. 7. Telnet - terminal emulation program that allows you to connect to a server and enter information and commands similar to if you were actually on the server terminal. LAYER 6 - PRESENTATION LAYER The presentation level is translator between the application and network format. Unlike the lower layers, its concern is with the syntax and semantics of the information transmitted. Most user programs do not exchange random binary bit strings. They exchange data such as names, addresses, dates, etc. Different computers store the data in a different way. In order to allow these computers to transmit the data to each other the presentation layer translates the data into a standard form to be used on the network. Another function is data compression which can be used to reduce the number of bits needed to send the packet of information. Security is also
PANKAJ BISHT
CSE 7th SEM
45380
24
added at this layer by using data encryption and decryption. This prevents others from intercepting the data and being able to decipher the meaning of the bits. Protocols: ASCII, EBCDIC, MIDI, MPEG, JPEG 1. ASCII - a code for representing English characters as numbers. 2. EBCDIC (Extended Binary-Coded Decimal Interchange Code) - IBM code for representing characters as numbers. 3. MIDI (Musical Instrument Device Interface) - adopted by the electronic music industry for controlling devices, such as synthesizers and sound cards, that emit music. 4. MPEG (Moving Pictures Experts Group) - the family of digital video compression standards and file formats developed by the ISO group. 5. JPEG (Joint Photographic Experts Group) - a lossy compression format for color images that reduces file size by 5% while losing some image detail. LAYER 5 SESSION LAYER This layer allows applications on connecting systems to communicate using a session. It opens, uses, and closes this communication link. It also acts as a dialog control mechanism controlling who is able to transmit. Sessions can allow data to be sent in both directions at the same time or only one direction. The session layer determines who has the ability to transfer at the current time. Another valuable ability is to insert checkpoints during data transfers. During a large file transmission if the system crashes the checkpoints allow the system to start downloading at the last known checkpoint. An example of this is during either a interactive login or file transfer connection, the session would recognize names in the session and register them into a history. It could then connect and reconnect in case of a system crash at either of the systems. Protocols: SQL, RPC. 1.SQL (Structured Query Language) - a standardized query language for requesting information from a database. 2. RPC (Remote Procedure Call) - allows a program on one computer execute a program on a server. LAYER 4 TRANSPORT LAYER The basic function of the transport layer is to accept data from the session layer, break up the data into smaller units if need be, and send these manageable data packets to the network layer. At the destination this layer is responsible for combining the packets into their original state. This layer also checks to see if the layers are in the right order when received and not in duplicated form. If there is an error in one of the packets there is a request for that packet's retransmission. There are two protocols that sit at this layer. First, the TCP protocol connects the sender and the receiver using a socket which is determined by the IP address and port number. TCP keeps track of the packet delivery order and which ones need to be resent. UDP on the other hand is a connectionless communication and does not guarantee packet delivery between sender
PANKAJ BISHT CSE 7th SEM 45380
25
and receiver. Because it is connectionless the sender sends the data into the network with an IP address of the receiver and hopes it makes it to its destination. Since there is not a way of asking the sender to retransmit because of an error there is little error protection if any. Protocols: TCP or UDP. 1. TCP (Transmission Control Protocol) - enables two to establish a connection and exchange streams of data. 2. UDP (User Datagram Protocol) - offering a direct way to send and receive datagrams over an IP network with very few error recovery services. LAYER 3 - NETWORK LAYER The network layer basically handles all of the addressing issues. This layer addresses packets, determines the best path or route, and manages network problems such as data congestion. There are three ways in which the packets are routed to their destinations. First, there could be a static route through the entire network that will never be changed. Second, there could be a static line only used during a particular session between the sender and receiver. Finally, the packets could be dynamically sent through the network using changing paths in order to prevent bottlenecks. The bottlenecks are formed when there are too many packets present in one subnet causing them to get in each other's way. The network level is also responsible for converting the network address and names to the MAC addresses of the machines. One of the most important functions of this layer is the ability to allow two different networks using conflicting addressing schemes to be able to send data to each other. The network layer allows the different protocols to "talk" to each other and understand where the packet's destination is. Routers work at this level by sending the packets along the network. Protocols: IP, ICMP, ARP, PING, Traceroute. 1.IP (Internet Protocol) - specifies the format of packets and the addressing schemes. 2.ICMP (Internet Control Message Protocol) - an extension of IP which supports packets containing error, control, and informational messages. 3. ARP (Address Resolution Protocol) - used to convert an IP address to a physical address. 4. PING - a utility to check if an IP address is accessible. 5. Traceroute - utility that tracks a packet from your computer to an internet host showing how many hops and how long it took.
LAYER 2 - DATA LINK LAYER: The data link layer defines the format of data on the network. All of the data sent through the network are made into a frame which is performed at this level. The frame is a uniform way of sending the data along with address information and error checking capabilities. CRC is used for the error detection at this level. If at the receiving end the CRC fails at this level there is a
PANKAJ BISHT
CSE 7th SEM
45380
26
request back to the sender Protocols: IEEE 802.2, 802.3, 802.5.
for
retransmission
of
this
packet.
1. IEEE 802.2 - divides the data link layer into two sublayers -- the logical link control (LLC) layer and the media access control (MAC) layer. 2.802.3 - Defines the MAC layer for bus networks that use CSMA/CD. This is the basis of the Ethernet standard. 3.802.5 - Defines the MAC layer for token-ring networks. LAYER 1 PHYSICAL LAYER The physical layer is responsible for establishing, maintaining and ending physical connections (point to point) between computers. This layer is concerned with the actual interpretation of the bit stream into an electrical signal that can be carried across a physical medium. The protocols at this layer deal with the binary transmission, voltage levels, and data rates. This layer would also specify physical medium properties such as cables and network cards. Protocols: IEEE 802.3, 802.5.
PANKAJ BISHT
CSE 7th SEM
45380
You might also like
- Ethernet Quick Guide SecuredDocument4 pagesEthernet Quick Guide SecuredDương Ngọc Sơn100% (1)
- IEEE Standards GuideDocument11 pagesIEEE Standards GuideHector Ledesma IIINo ratings yet
- Data Link LayerDocument43 pagesData Link LayerVenkatakrishnan SubramaniyanNo ratings yet
- LTE L2 Introduction: Bearers, Channels, MAC & RLCDocument116 pagesLTE L2 Introduction: Bearers, Channels, MAC & RLCJawad AL-noaimi100% (3)
- CCNA Certification and Network TypesDocument64 pagesCCNA Certification and Network TypesNikhil ThavamNo ratings yet
- IT131P-Networking Basics SyllabusDocument5 pagesIT131P-Networking Basics SyllabusJess Doria100% (1)
- Advances in Analog and RF IC Design for Wireless Communication SystemsFrom EverandAdvances in Analog and RF IC Design for Wireless Communication SystemsGabriele ManganaroRating: 1 out of 5 stars1/5 (1)
- Network Routing Basics Understanding IP Routing in Cisco SystemsDocument436 pagesNetwork Routing Basics Understanding IP Routing in Cisco Systemsellybeauty100% (1)
- Lab Manual Computer NetworkDocument46 pagesLab Manual Computer Networkmeghana09No ratings yet
- CISA Exam - Testing Concept-Network Physical Media (Fiber Optic/ UTP/STP/Co-axial) (Domain-4)From EverandCISA Exam - Testing Concept-Network Physical Media (Fiber Optic/ UTP/STP/Co-axial) (Domain-4)No ratings yet
- Volte Kpi CountersDocument2 pagesVolte Kpi CountersRuchikaNo ratings yet
- Types of Network Cables and TopologiesDocument30 pagesTypes of Network Cables and TopologiesanonymousNo ratings yet
- Mesh Topology: Greater Privacy and Security As Message Travels Along A Dedicated LineDocument18 pagesMesh Topology: Greater Privacy and Security As Message Travels Along A Dedicated Linedaniel tuernerNo ratings yet
- CN PracticalsDocument31 pagesCN Practicalskumarjass5251No ratings yet
- Medi-Caps University Indore: Computer Network Lab File Department of Computer Science Engineering Session: 2019-23Document46 pagesMedi-Caps University Indore: Computer Network Lab File Department of Computer Science Engineering Session: 2019-23Harsh JoshiNo ratings yet
- Networking Report For StudentDocument8 pagesNetworking Report For StudentAbhishek DwivediNo ratings yet
- Engineering College Tuwa: Name: Subject: Branch: Computer Engineering Enrollment NoDocument39 pagesEngineering College Tuwa: Name: Subject: Branch: Computer Engineering Enrollment NoREEYANo ratings yet
- Network CableDocument14 pagesNetwork Cablesyukz0% (1)
- CN LAB FILE SAnyamDocument56 pagesCN LAB FILE SAnyamPrathamesh PandeyNo ratings yet
- UNIT 8 - NetworksDocument15 pagesUNIT 8 - NetworksChrispin MachilikaNo ratings yet
- Types of CablesDocument3 pagesTypes of CablesshahmukteshNo ratings yet
- Network Lab ManualDocument7 pagesNetwork Lab ManualANKIT67% (3)
- CCNA Routing and Switching Guide: IP Addressing, Routing, Switching, ACLs and MoreDocument122 pagesCCNA Routing and Switching Guide: IP Addressing, Routing, Switching, ACLs and Moredhileep sNo ratings yet
- Aditi CN FileDocument51 pagesAditi CN FileKunalNo ratings yet
- httpsz-p3-cdn.fbsbx.comvt59.2708-21316348873_5815810248475238_4852308856062457441_n.pdfTLE-CSS_Grade-9_QRT-2_ModuLE-2-forDocument21 pageshttpsz-p3-cdn.fbsbx.comvt59.2708-21316348873_5815810248475238_4852308856062457441_n.pdfTLE-CSS_Grade-9_QRT-2_ModuLE-2-forkaye14davidNo ratings yet
- Lesson 3 Transmission MediaDocument9 pagesLesson 3 Transmission MediaKevin SambuNo ratings yet
- Chapter 2 - Networking HardwareDocument6 pagesChapter 2 - Networking HardwareBonsa MesganawNo ratings yet
- CN Pract-2Document13 pagesCN Pract-2Ur MnNo ratings yet
- 3 Transmission MediaDocument22 pages3 Transmission MediaRashad MahmoodNo ratings yet
- CN Chapter2Document10 pagesCN Chapter2nishitha.eeeNo ratings yet
- Mcse PracticalsDocument29 pagesMcse Practicalsarzoo105100% (1)
- Computer Is A Programmable Machine. This Means It Can Execute A Programmed List of Instructions and Respond To New Instructions That It Is GivenDocument5 pagesComputer Is A Programmable Machine. This Means It Can Execute A Programmed List of Instructions and Respond To New Instructions That It Is GivenArlone AlbezaNo ratings yet
- Network MediaDocument11 pagesNetwork MediaSajal GhoshNo ratings yet
- Types of Transmission Media: Twisted Pair, Coaxial, Fiber OpticDocument9 pagesTypes of Transmission Media: Twisted Pair, Coaxial, Fiber Opticpratyay dhondNo ratings yet
- Document 3Document17 pagesDocument 3Night FuryNo ratings yet
- Q3W5Recognize Network Fundamentals and The Benefits and RiskDocument28 pagesQ3W5Recognize Network Fundamentals and The Benefits and RiskabdulkikieNo ratings yet
- Lesson 3 Transmission MediaDocument9 pagesLesson 3 Transmission MediateddykigiaNo ratings yet
- Task: 1: To Study The Different Types of Network Cables and Network TopologiesDocument12 pagesTask: 1: To Study The Different Types of Network Cables and Network Topologiesabhishek kumar100% (1)
- Handout 2 - Networking HardwareDocument6 pagesHandout 2 - Networking HardwareHirut GetachewNo ratings yet
- Information Sheet 3.1Document10 pagesInformation Sheet 3.1Danica De GuzmanNo ratings yet
- Idresss sir#6OKDocument17 pagesIdresss sir#6OKDil NawazNo ratings yet
- Cabling and InfrastructureDocument5 pagesCabling and Infrastructureanu balakrishnanNo ratings yet
- Networking Concepts and Telecommunications: Figure 8-1Document23 pagesNetworking Concepts and Telecommunications: Figure 8-1Ngonidzashe ZanamweNo ratings yet
- Chapter 8 and 9Document15 pagesChapter 8 and 9Nandhini PNo ratings yet
- Experiment 1 ACADocument5 pagesExperiment 1 ACAaakash dabasNo ratings yet
- Network Intercables RacewayDocument5 pagesNetwork Intercables RacewayLeonardo Noran JrNo ratings yet
- Assignment 1-LAN SETUPDocument79 pagesAssignment 1-LAN SETUPshweta bhavsarNo ratings yet
- Networking BasicsDocument11 pagesNetworking BasicsSyeda Zoya Hassan RizviNo ratings yet
- Physical Layer: Twisted-Pair CableDocument6 pagesPhysical Layer: Twisted-Pair CableNeenu PrasannanNo ratings yet
- L1 Networking BasicsDocument11 pagesL1 Networking BasicsRola HashimNo ratings yet
- ThinktankIP XiiDocument81 pagesThinktankIP XiiGuruKPONo ratings yet
- Star Topology Network GuideDocument14 pagesStar Topology Network GuideKuldeep AttriNo ratings yet
- chapter 4 11TH CLASS unit 1Document9 pageschapter 4 11TH CLASS unit 1rajindertelecomnsqfNo ratings yet
- Lab Manual (CN)Document33 pagesLab Manual (CN)alkahaf mukadamNo ratings yet
- Lab 1Document14 pagesLab 1nawal 109No ratings yet
- TLE Grade8 ICT-CSS Module13Document8 pagesTLE Grade8 ICT-CSS Module13Hazel Mae EbaritaNo ratings yet
- CN FileDocument26 pagesCN FileShaktiNo ratings yet
- Notes-Transmission MediaDocument22 pagesNotes-Transmission MediaRaj VermaNo ratings yet
- Chapter 1Document7 pagesChapter 1Edouard Mvogo BilegueNo ratings yet
- Fiber Optic Cable: Glass Threads Transmit Light SignalsDocument6 pagesFiber Optic Cable: Glass Threads Transmit Light SignalsAaaNo ratings yet
- Types of Network MediaDocument7 pagesTypes of Network MediaIANNo ratings yet
- PHY LAYER FUNCS & MEDIADocument26 pagesPHY LAYER FUNCS & MEDIAalish shrsethaNo ratings yet
- Networking 1.5Document13 pagesNetworking 1.5Echo greenNo ratings yet
- Different Types of Wired NetworkDocument10 pagesDifferent Types of Wired NetworkGagan DeepNo ratings yet
- Q3 Module2 G11 CSS NCII Sison Central is BlueDocument8 pagesQ3 Module2 G11 CSS NCII Sison Central is BluexzainahanielmartinezNo ratings yet
- Chapter 3 - Transmission MediaDocument24 pagesChapter 3 - Transmission MediaTawanda MukuteNo ratings yet
- Transmission MediumDocument12 pagesTransmission MediumSuryanshuNo ratings yet
- Designing Embedded Communications SoftwareDocument239 pagesDesigning Embedded Communications SoftwareAmrRassemNo ratings yet
- MAC Sub Layer Functions and ProtocolsDocument24 pagesMAC Sub Layer Functions and ProtocolssanthipriyasunkaraNo ratings yet
- 12 MultipleAccessDocument48 pages12 MultipleAccessdharshan dharshiNo ratings yet
- 14 Performance Analysis of Wired and Wireless LANDocument5 pages14 Performance Analysis of Wired and Wireless LANSigula Galuh0% (1)
- 1Q 2010 Cdma Subscribers: by The CDMA Development GroupDocument19 pages1Q 2010 Cdma Subscribers: by The CDMA Development GroupHamza SaleemNo ratings yet
- LTE Physical, Logical and Transport ChannelsDocument2 pagesLTE Physical, Logical and Transport ChannelsMkathuriNo ratings yet
- Wifi DirectDocument32 pagesWifi DirectRast GNo ratings yet
- Question BankDocument996 pagesQuestion BankJohann NeethlingNo ratings yet
- Concept of SRBDocument17 pagesConcept of SRBfahmi1987No ratings yet
- TDMA, FDMA AND CDMA QuestionsDocument7 pagesTDMA, FDMA AND CDMA QuestionsAbdul Basit MughalNo ratings yet
- JNTUH Syllabus 2013 M.tech Communication SysDocument26 pagesJNTUH Syllabus 2013 M.tech Communication SysSRINIVASA RAO GANTANo ratings yet
- TDMA and FDMADocument17 pagesTDMA and FDMAtony starkNo ratings yet
- Internetworking Concepts Overview: © 1999, Cisco Systems, IncDocument50 pagesInternetworking Concepts Overview: © 1999, Cisco Systems, IncShashi Kant RaviNo ratings yet
- TEL280 Ingeniería Inalámbrica: Sessions 8-10: Multiple AccessDocument9 pagesTEL280 Ingeniería Inalámbrica: Sessions 8-10: Multiple AccessRuth Nadiezhda AraujoNo ratings yet
- Ccna CCNPDocument36 pagesCcna CCNPHimanshu PatariaNo ratings yet
- Understanding CSMA/CD ProtocolDocument10 pagesUnderstanding CSMA/CD ProtocolKrishna BhikadiyaNo ratings yet
- Computer Networks and SecurityDocument26 pagesComputer Networks and SecurityKamal ThelagaNo ratings yet
- WiMAX Project Presentation on IEEE 802.16 StandardDocument18 pagesWiMAX Project Presentation on IEEE 802.16 StandardNpt DcNo ratings yet
- LTE Protocol Stack LayersDocument7 pagesLTE Protocol Stack Layersmd1234_1984No ratings yet
- Multiple Access ProtocolsDocument43 pagesMultiple Access ProtocolsSahilPrabhakarNo ratings yet
- IEEE Networking StandardsDocument3 pagesIEEE Networking StandardsZainab TariqNo ratings yet
- Principles of Computer Communication NetworksDocument8 pagesPrinciples of Computer Communication Networksomic1100% (2)
- Chapter 9 - Ethernet: CCNA Exploration 4.0Document90 pagesChapter 9 - Ethernet: CCNA Exploration 4.0kiennaNo ratings yet