Professional Documents
Culture Documents
Mepco Schlenk Engg College Autonomous PG CURRICULUM Web Curriculum MTECH IT
Uploaded by
Vishnu Prasaad0 ratings0% found this document useful (0 votes)
109 views45 pagesM.Tech IT Syllabus 1-2 Semester
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentM.Tech IT Syllabus 1-2 Semester
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
109 views45 pagesMepco Schlenk Engg College Autonomous PG CURRICULUM Web Curriculum MTECH IT
Uploaded by
Vishnu PrasaadM.Tech IT Syllabus 1-2 Semester
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 45
23
MEPCO SCHLENK ENGINEERING COLLEGE, SIVAKASI (AUTONOMOUS)
AFFILIATED TO ANNA UNIVERSITY, CHENNAI 600 025
REGULATIONS: MEPCO - R2013 (FULL TIME)
M.TECH INFORMATION TECHNOLOGY
Department Vision Department Mission
To emerge as Realm of Preeminence that
empowers the students to reach the zenith,
as assertive IT professionals by offering
quality technical education and research
environment to best serve the nation.
To develop dynamic IT
professionals with globally
competitive learning experience by
providing high class education.
Programme Educational Objectives
After 3 Years of Graduation, our graduates will
1. Flourish as eminent researchers, academicians or IT practitioners.
2. Create, apply and disseminate cognitive ideas related to IT field and advance in
their profession.
3. Nurture continuous self learning to update the latest developments in IT
industries.
Programme Outcomes
The graduates will be able to
1. Conceptualize and apply the basic engineering techniques studied in their
under graduation.
2. Identify and formulate current research problems related to IT industry.
3. Design system, service or component to meet desired economic, social and
ethical needs with in realistic IT constraints.
4. Interpret, analyze and synthesize complex data to provide valid conclusions.
5. Employ modern tools and techniques to solve research issues related to
Information and Communication Technology.
6. Comprehend and evaluate existing research avenues on their own.
7. Orally communicate ideas clearly in an organized manner.
8. Write concise system documentation, user manual and research articles.
9. Apply IT principles in the construction of software systems of varying
complexity.
10. Engage in lifelong learning to adapt in their professional work or graduate
studies.
24
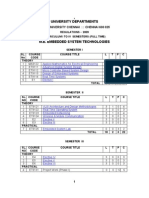
CURRICULUM (I TO IV SEMESTER)
I SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MA177 Optimization Techniques 3 1 0 4
2. 13MC101 Advanced Data Structures and Algorithms
(Common to M.E CSE and M.Tech IT)
3 0 0 3
3. 13MI101 Modern Computer Architecture 3 0 0 3
4. 13MI102 Advanced Database Technology 3 0 0 3
5. 13MI103 Network Programming and Management 3 0 0 3
6. 13MI104 Soft Computing Techniques 3 1 0 4
PRACTICAL
7. 13MC151 Advanced Data Structures Laboratory
(Common to M.E CSE and M.Tech IT)
0 0 3 2
8. 13MI151 Network Programming Laboratory 0 0 3 2
9 13MI152 Comprehension 0 0 2 1
TOTAL 18 2 8 25
II SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
1. 13MI201 Web Mining and Information Retrieval 3 0 0 3
2. 13MI202 Cloud Computing Technologies
(Common to M.E CSE and M.Tech IT)
3 0 0 3
3. 13MI203 Cyber Security 3 0 0 3
4. 13MI204 Big Data Analytics
(Common to M.E CSE and M.Tech IT)
3 0 0 3
5. Elective I 3 0 0 3
6. Elective II 3 0 0 3
PRACTICAL
7. 13MI251 Big Data Analytics Laboratory 0 0 3 2
8. 13MI252 Cloud Computing Laboratory
(Common to M.E CSE & M.Tech IT)
0 0 3 2
9. 13MC252 Technical Seminar * 0 0 2 1
TOTAL 18 0 6 22
* Internal Assessment only
25
III SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. Elective III 3 0 0 3
2. Elective IV 3 0 0 3
3. Elective V 3 0 0 3
PRACTICAL
1. 13MI351 Project Work (Phase I) 0 0 12 6
TOTAL 9 0 12 15
IV SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
PRACTICAL
1. 13MI451 Project Work (Phase II)
0 0 24 12
TOTAL 0 0 24 12
Total No. of Credits : 74
LIST OF ELECTIVES
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
1. 13MI401 X- Informatics 3 0 0 3
2. 13MI402 XML and Web Services 3 0 0 3
3. 13MC407 Energy Aware Computing
(Common to M.E CSE &M.Tech IT)
3 0 0 3
4. 13MI403 Internet of Things
(Common to M.E CSE &M.Tech IT)
3 0 0 3
5. 13MI404 Performance Evaluation and Reliability of
Information Systems
3 0 0 3
26
6. 13MI405 Next Generation Wireless Networks 3 0 0 3
7. 13MI406 Pervasive Computing 3 0 0 3
8. 13MI407 Multimedia Technologies 3 0 0 3
9. 13MI408 Video Analytics
(Common to M.E CSE &M.Tech IT)
3 0 0 3
10. 13MI409 Wireless Sensor Networks
(Common to M.E CSE &M.Tech IT)
3 0 0 3
11. 13MI410 Image Processing and Pattern Analysis 3 0 0 3
12. 13MI411 Machine Learning 3 0 0 3
13. 13MI412 Web Mining 3 0 0 3
14. 13MI413 Software Agents 3 0 0 3
15. 13MI414 Automata Theory and Compiler Design 3 0 0 3
16. 13MI415 Social Network Analysis 3 0 0 3
17. 13MI416 Human Computer Interaction and Human factor 3 0 0 3
18. 13MI417 GPU Architecture and Programming 3 0 0 3
19. 13MI418 Knowledge Engineering 3 0 0 3
20. 13MI419 Parallel Computing 3 0 0 3
21. 13MI420 Ontology and Semantic Web 3 0 0 3
22. 13MI421 Logic Programming 3 0 0 3
23. 13MI422 VLSI Design 3 0 0 3
TOTAL NO. OF CREDITS: 74
27
REGULATIONS MEPCO R2013 (PART TIME)
M.TECH INFORMATION TECHNOLOGY
CURRICULUM (I TO VI SEMESTER)
I SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MA177 Optimization Techniques 3 1 0 4
2.
13MC101
Advanced Data Structures and Algorithms
(Common to M.E CSE & M.Tech IT)
3 0 0 3
3. 13MI101 Modern Computer Architecture 3 0 0 3
PRACTICAL
4. 13MC151 Advanced Data Structures Laboratory
(Common to ME CSE & MTech IT)
0 0 3 2
5 13MI152 Comprehension 0 0 2 1
TOTAL 9 1 5 13
II SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1.
13MI202 Cloud Computing Technologies
(Common to M.E CSE & M.Tech IT)
3 0 0 3
2.
13MI203 Cyber Security 3 0 0 3
3.
Elective I 3 0 0 3
PRACTICAL
4.
13MI252 Cloud Computing Laboratory
(Common to M.E CSE & M.Tech IT)
0 0 3 2
TOTAL 9 0 3 11
III SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MI102 Advanced Database Technology 3 0 0 3
2. 13MI103 Network Programming and Management 3 0 0 3
3. 13MI104 Soft Computing Techniques 3 1 0 4
PRACTICAL
4. 13MI151 Network Programming Laboratory 0 0 3 2
TOTAL 9 1 3 12
28
IV SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1.
13MI201 Web Mining and Information Retrieval
3 0 0 3
2.
13MI204 Big Data Analytics
(Common to ME CSE & MTech IT)
3 0 0 3
3. Elective II 3 0 0 3
PRACTICAL
4.
13MI251
Big Data Analytics Laboratory 0 0 3 2
TOTAL 9 0 5 11
V SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. Elective III 3 0 0 3
2. Elective IV 3 0 0 3
3. Elective V 3 0 0 3
PRACTICAL
4. 13MI351 Project Work (Phase I) 0 0 12 6
TOTAL 9 0 12 15
VI SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
PRACTICAL
1. 13MI451 Project Work ( Phase II) 0 0 24 12
TOTAL 0 0 24 12
Total No. of Credits : 74
LIST OF ELECTIVES
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
1. 13MI401
X- Informatics
3 0 0 3
2. 13MI402
XML and Web Services
3 0 0 3
3. 13MC407
Energy Aware Computing
(Common to M.E CSE &M.Tech IT)
3 0 0 3
4. 13MI403
Internet of Things
(Common to M.E CSE &M.Tech IT)
3 0 0 3
29
SYLLABUS FOR I YEAR M.TECH INFORMAION TECHNOLOGY
I SEMESTER
13MA177 : OPTIMIZATION TECHNIQUES L T P C
3 1 0 4
Course Objectives:
To give the idea about mathematical models related to Engineering problems
To understand the various methods of solving linear programming problems
To provide information about optimization techniques related to constrained and
unconstrained non linear programming
Course Outcomes:
Upon completion of the course the students will be able
To formulate mathematical models in engineering applications
To determine the solution of LPP including transportation and assignment problems
5. 13MI404
Performance Evaluation and Reliability of
Information Systems
3 0 0 3
6. 13MI405
Next Generation Wireless Networks
3 0 0 3
7. 13MI406
Pervasive Computing
3 0 0 3
8. 13MI407
Multimedia Technologies
3 0 0 3
9. 13MI408
Video Analytics
(Common to M.E CSE &M.Tech IT)
3 0 0 3
10. 13MI409
Wireless Sensor Networks
(Common to M.E CSE &M.Tech IT)
3 0 0 3
11. 13MI410
Image Processing and Pattern Analysis
3 0 0 3
12. 13MI411 Machine Learning 3 0 0 3
13. 13MI412 Web Mining 3 0 0 3
14. 13MI413 Software Agents 3 0 0 3
15. 13MI414 Automata Theory and Compiler Design 3 0 0 3
16. 13MI415 Social Network Analysis 3 0 0 3
17. 13MI416 Human Computer Interaction and Human factor 3 0 0 3
18. 13MI417 GPU Architecture and Programming 3 0 0 3
19. 13MI418 Knowledge Engineering 3 0 0 3
20. 13MI419 Parallel Computing 3 0 0 3
21. 13MI420 Ontology and Semantic Web 3 0 0 3
22. 13MI421 Logic Programming 3 0 0 3
23. 13MI422 VLSI Design 3 0 0 3
TOTAL CREDITS: 74
30
To apply various search methods to identify the optimum solution for NLPP
To identify the unconstrained and constrained problems in optimization and their
solution
UNIT I LINEAR PROGRAMMING 9
Introduction Formulation - Graphical solutions standard and canonical forms Simplex
method Revised simplex method duality in linear programming Post optimal analysis.
UNIT II TRANSPORTATION AND ASSIGNMENT PROBLEM 9
Transportation Problem North-West corner rule lowest cost minimum method Vogels
approximation method Modi method for optimization Degeneracy in transportation problem
Assignment problem Hungarian algorithm Unbalanced assignment problem Maximization
problem Travelling Salesmen Problem.
UNIT III NON-LINEAR PROGRAMMING 9
Introduction elimination methods : Unrestricted and Exhaustive search methods, Fibonacci
method , golden section method Interpolation method: Quadratic and cubic interpolation
methods, Direct root methods Kuhn-Tucker conditions.
UNIT IV UNCONSTRAINED OPTIMIZATION TECNIQUES 9
Introduction Standard form of the problem and basic terminology Direct search method:
Simplex method, Random search method, Univariate and pattern search method Indirect
search method: Steepest Descent (Cauchy) method, Conjugate gradient method, Newton's
method Application to engineering problems.
UNIT V CONSTRAINED OPTIMIZATION TECNIQUES 9
Introduction Standard form of the problem and basic terminology Direct method:
Sequential Linear Programming, Generalised Reduced gradient method, Methods of feasible
direction Indirect method: Penalty function method, Interior and exterior penalty function
method, Convex programming problem Check for convergence Application to engineering
problems
TUTORIAL :15 PERIODS
TOTAL: 45+15=60 PERIODS
REFERENCE BOOKS:
1. Roa, S.S., Engineering Optimization Theory and Practice, New Age international
Publications, 2010.
2. Deb K., 'Optimisation for Engineering Design-Algorithms and Example', Prentice Hall
3. Taha, H.A. Operations Research: An Introduction, Pearson Education Inc., (Prentice-Hall
of India Pvt. Ltd.), New Delhi, 8th Edition, 2008.
4. Sinha S.M., Mathematical Programming: Theory and Methods, Elsevier India, 1st Edition,
2006.
5. Gupta P.K. and Hira , D.S., Operations Research, S. Chand and Co. Ltd.,
6. New Delhi, 2001.
7. Manmohan P.K. and Gupta, S.C. , Operations Research, Sultan Chand and Co., New
Delhi, 9th Edition, 2001.
8. Ravindran A., Phillips D.T. and Solberg, J.JOperations Research - Principles and Practice,
Wiley India Edition, 2007.
31
13MC101: ADVANCED DATA STRUCTURES AND ALGORITHMS L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To recall elementary data structures and the significance of writing efficient algorithms
To study data structures for concurrency
To study advanced data structures such as search trees, hash tables, heaps and operations
on them
To expose various distributed data structures
To understand the principles of efficient algorithm design and learn various advanced
algorithms
Course Outcomes:
Implement and apply concurrent linked lists, stacks, and queues
Perform operations on search trees and hash tables
Perform operations on different types of heap
Implement and apply data structures for strings
Implement advanced concurrent structures
Explain design techniques for algorithms and advanced algorithm
UNIT I DATA STRUCTURES AND CONCURRENCY 9
Review of algorithm design and analysis review of elementary data structures data structures
and concurrency locking linked lists coarse-grained synchronization fine-grained
synchronization lazy synchronization non-blocking synchronization concurrent queues
bounded partial queues unbounded lock-free queues dual data structures concurrent stacks
elimination backoff stack
UNIT II SEARCH TREES, HASH TABLES AND STRINGS 9
Search Trees Weight Balanced trees Red Black trees Finger Trees and level linking Skip
lists joining and splitting balanced search trees Hash trees extendible hashing- Strings
tries and compressed tries dictionaries suffix trees suffix arrays.
UNIT III HEAPS 9
Heaps - Array-Based Heaps - Heap-Ordered Trees and Half-Ordered Trees - Leftist Heaps Skew
Heaps - Binomial Heaps - Changing Keys in Heaps - Fibonacci Heaps - Double-Ended Heap
structures multidimensional heaps
UNIT IV ADVANCED CONCURRENT STRUCTURES 9
Concurrent hashing closed-address hash sets lock-free hash sets open-addressed hash sets
lock-based concurrent skip lists lock-free concurrent skip lists concurrent priority queues
bounded priority queue unbounded priority queue concurrent heap skip list based
unbounded priority queues.
UNIT V ADVANCED ALGORITHMS 9
Introduction to Approximation algorithms job scheduling on a single machine knapsack
problem minimizing weighted sum of completion time on a single machine MAX SAT and MAX
CUT. Introduction to Randomized algorithms min cut. Introduction to Parallel algorithms
parallel sorting algorithms.
TOTAL: 45 PERIODS
32
REFERENCE BOOKS:
1. M. Herlihy and N. Shavit, The Art of Multiprocessor Programming, Morgan Kaufmann,
2012.
2. Peter Brass, Advanced Data Structures, Cambridge University Press, 2008.
3. A. V. Aho, J. E. Hopcroft, and J. D. Ullman, The Design and Analysis of Computer
Algorithms, Addison-Wesley, 1975.
4. Gavpai, Data Structures and Algorithms Concepts, techniques and Applications, First
Edition, Tata McGraw-Hill, 2008.
5. Edited by S.K. Chang, Data Structures and Algorithms Series of Software Engineering
and Knowledge Engineering, Vol. 13, World Scientific Publishing, 2003.
6. Jon Kleinberg, "Algorithm Design", Addison-Wesley, 2013.
7. David P. Williamson, David B. Shmoys, The Design of Approximation Algorithms,
Cambridge University Press, 2011.
8. Rajeev Motwani and Prabhakar Raghavan, Randomized Algorithms, Cambridge University
Press, 1995.
9. Michael J. Quinn, Parallel Computing: Theory & Practice, Tata McGraw Hill Edition, 2003.
10. Ananth Grama, Anshul Gupta, et al., Introduction to Parallel Computing, Second Edition,
Pearson Education, 2003.
Web References:
1. http://www.geeksforgeeks.org/pattern-searching-set-8-suffix-tree-introduction/
2. http://iamwww.unibe.ch/~wenger/DA/SkipList/
3. http://www.cs.au.dk/~gerth/slides/soda98.pdf
4. http://www.cs.sunysb.edu/~algorith/files/suffix-trees.shtml
5. http://pages.cs.wisc.edu/~shuchi/courses/880-S07/scribe-notes/lecture20.pdf
13MI101: MODERN COMPUTER ARCHITECTURE L T P C
3 0 0 3
Course Objectives:
To understand the recent trends in the field of Computer Architecture and identify
performance related parameters.
To appreciate the need for parallel processing.
To expose the students to the problems related to multiprocessing.
To understand the different types of multicore architectures.
To analyze and use techniques that guarantee cache coherence and correct sequential
memory access across multiprocessor systems.
Course Outcomes:
Compare and evaluate the performance of various architectures.
Develop a framework for evaluating design decisions in terms of application requirements
and performance measurements.
Identify the limitations of ILP and the need for multicore architectures.
33
Address the issues related to multiprocessing and suggest solutions.
Utilize the complex architecture involved in multicore processors for parallel computing.
Analyze design of computer systems, including modern architectures and suggest the
suitable architecture according to the application.
UNIT I FUNDAMENTALS OF COMPUTER DESIGN AND ANALYSIS 9
Fundamentals of Computer Design Classes of Computers Trends in Technology, Power, Energy
and Cost Dependability - Measuring and reporting performance Quantitative principles of
computer design- Classes of Parallelism - ILP, DLP, TLP and RLP - Instruction set principles and
Examples - Pipelining :Basic & Intermediate concepts
UNIT II INSTRUCTION LEVEL PARALLELISM WITH DYNAMIC APPROACHES 9
Concepts Dynamic Scheduling Dynamic hardware prediction Multiple issue Hardware based
speculation Limitations of ILP Case studies.
UNIT III INSTRUCTION LEVEL PARALLELISM WITH SOFTWARE APPROACHES 9
Compiler techniques for exposing ILP Static branch prediction VLIW Advanced compiler
support Hardware support for exposing more parallelism Hardware versus software speculation
mechanisms Case studies.
UNIT IV MULTIPROCESSORS AND MULTICORE ARCHITECTURES 9
Symmetric and distributed shared memory architectures Performance issues Synchronisation
issues Models of memory consistency Software and hardware multithreading SMT and CMP
architectures Design issues Case studies CPU Accounting for Multicore Processors.
UNIT V MEMORY AND I/O 9
Cache performance Reducing cache miss penalty and miss rate Reducing hit time Main
memory and performance Memory technology. Types of storage devices Buses RAID
Reliability, availability and dependability I/O performance measures Designing an I/O system
Design, Performance, and Energy Consumption of eDRAM/SRAM Macrocells for L1 Data Caches.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. John L. Hennessey and David A. Patterson, Computer Architecture A quantitative
approach, Morgan Kaufmann / Elsevier, 4th. edition, 2007.
2. David E. Culler, Jaswinder Pal Singh, Parallel Computing Architecture : A hardware/
software approach , Morgan Kaufmann / Elsevier, 1997.
3. William Stallings, Computer Organization and Architecture Designing for Performance,
Pearson Education, Seventh Edition, 2006.
4. Behrooz Parhami, Computer Architecture, Oxford University Press, 2006.
5. Carlos Luque, Miquel Moreto, Francisco J. Cazorla, Roberto Gioiosa, Alper Buyuktosunoglu,
and Mateo Valero, CPU Accounting for Multicore Processors, IEEE Transactions On
Computers, Vol. 61, No. 2, February 2012.
6. Alejandro Valero, Salvador Petit, Julio Sahuquillo, Pedro Lpez, Jos Duato, Design,
Performance, and Energy Consumption of eDRAM/SRAM Macrocells for L1 Data Caches IEEE
Transactions On Computers, Vol. 61, No. 9, September 2012.
34
13MI102 : ADVANCED DATABASE TECHNOLOGY L T P C
3 0 0 3
Course Objectives:
To learn the modeling and design of emerging databases.
To acquire knowledge on parallel and distributed databases and its applications.
To study the usage and applications of Object Oriented and Intelligent databases.
To understand the usage of advanced data models.
To acquire inquisitive attitude towards research topics in databases.
Course Outcomes:
Design and implement parallel databases using inter and intra query parallelism concepts
Analyze and apply suitable query and transaction processing techniques for distributed
databases
Develop object oriented and object relational database real time applications using suitable
tools
Expertise and implement intelligent databases using DB2/SQL
Build advanced data models for web, multimedia and mobile computing services.
UNIT I PARALLEL AND DISTRIBUTED DATABASES 9
Database System Architectures: Centralized and Client-Server Architectures Server System
Architectures Parallel Systems- Distributed Systems Parallel Databases: I/O Parallelism Inter
and Intra Query Parallelism Inter and Intra operation Parallelism Design of Parallel Systems-
Distributed Database Concepts - Distributed Data Storage Distributed Transactions Commit
Protocols Concurrency Control Distributed Query Processing Case Studies
UNIT II OBJECT AND OBJECT RELATIONAL DATABASES 9
Concepts for Object Databases: Object Identity Object structure Type Constructors
Encapsulation of Operations Methods Persistence Type and Class Hierarchies Inheritance
Complex Objects Object Database Standards, Languages and Design: ODMG Model ODL OQL
Object Relational and Extended Relational Systems: Object Relational features in SQL/Oracle
Case Studies.
UNIT III INTELLIGENT DATABASES 9
Active Databases: Syntax and Semantics (Starburst, Oracle, DB2)- Taxonomy- Applications-Design
Principles for Active Rules- Temporal Databases: Overview of Temporal Databases- TSQL2-
Deductive Databases: Logic of Query Languages Datalog- Recursive Rules-Syntax and Semantics
of Datalog Languages- Implementation of Rules and Recursion- Recursive Queries in SQL, Data
Mining Concepts, Overview of Data Warehousing and OLAP.
UNIT IV
ADVANCED DATA MODELS
9
XML & Internet Databases: XML Data, XML Data Model, XML DTD, XML Schema, XML Databases,
XML Querying, Mobile Databases: Mobile Computing Architecture, Location and Handoff
Management, Mobile Data Management Issues, Data processing and mobility, Mobile Data Query
Processing, Transaction Management in Mobile databases, Issues in Information Broadcast-
Multimedia Databases Image databases, Video databases
35
UNIT V EMERGING TECHNOLOGIES 9
eographic Information System, Design and Representation of Geographic Data, Spatial Databases-
Spatial Data Types- Spatial Indexes - Spatial Relationships- Spatial Data Structures- R-Trees,
Spatial Queries, Genome Databases, Introduction to Big Data, Twig Pattern Queries, Handling
Partial Information in Relational Databases, Domain Specific Querying. Entity Mining High Utility
Dataset Mining.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. R. Elmasri, S.B. Navathe, Fundamentals of Database Systems, Fifth Edition, Pearson
Education/Addison Wesley, 2007.
2. Thomas Cannolly and Carolyn Begg, Database Systems, A Practical Approach to
Design, Implementation and Management, Third Edition, Pearson Education, 2007.
3. Henry F Korth, Abraham Silberschatz, S. Sudharshan, Database System Concepts, Fifth
Edition, McGraw Hill, 2006.
4. C.J.Date, A.Kannan and S.Swamynathan, An Introduction to Database Systems, Eighth
Edition, Pearson Education, 2006.
5. Raghu Ramakrishnan, Johannes Gehrke, Database Management Systems, McGraw Hill,
Third Edition 2004.
6. Jun Pyo Park, Chang-Sup Park, and Yon Dohn Chung, Lineage Encoding: An Efficient
Wireless XML Streaming Supporting Twig Pattern Queries, IEEE Transactions On
Knowledge And Data Engineering, Vol. 25, No. 7, July 2013
7. Maria Vanina Martinez, Cristian Molinaro, John Grant, and V.S. Subrahmanian,
Customized Policies for Handling Partial Information in Relational Databases, IEEE
Transactions on Knowledge and Data Engineering, Vol. 25, No. 6, June 2013
8. Shasha Li, Chin-Yew Lin, Young-In Song, and Zhoujun Li, Comparable Entity Mining from
Comparative Questions, IEEE Transactions on Knowledge and Data Engineering, Vol. 25,
No. 7, July 2013
13MI103: NETWORK PROGRAMMING AND MANAGEMENT L T P C
3 0 0 3
Course Objectives:
To study the design and implementation of a socket based application using either TCP, UDP
and SCTP.
To understand SCTP sockets and its options.
To study the security features in socket programming.
To explore the usage of sockets options and the system calls needed to support unicast,
broadcast and multicast applications.
To explore the emerging technologies in network management.
Course Outcomes:
Design and develop network applications using sockets system calls.
Explore the features of Stream Control Transmission Protocol (SCTP)
Incorporate the security features in the socket programming
36
Work with various networking tools such as ping, traceroute to investigate a traffic flow in the
network.
Extend network applications for broadcasting and multicasting
Create innovative network design by applying advanced socket concepts.
Analyze the network management protocols and practical issues involved in it.
UNIT I APPLICATION DEVELOPMENT 9
Introduction to Socket Programming Overview of TCP/IP Protocols Introduction to Sockets
Iterative TCP programming Iterative UDP programming Concurrent programming fork and
exec - I/O multiplexing I/O Models select function shutdown function TCP echo Server
(with multiplexing) poll function TCP echoClient (with Multiplexing) Multiplexing TCP and UDP
sockets- Threaded servers thread creation and termination TCP echo server using threads
Mutexes condition variables Ipv6 Socket Programming.
UNIT II ELEMENTARY SCTP SOCKETS AND SOCKET OPTIONS 9
Introduction to SCTP- Interface Modules SCTP functions- sctp_bindx, sctp_connectx,
sctp_getpaddrs, sctp_freepaddrs, sctp_getladdrs, sctp_freeladdrs, sctp_sendmsg,
sctp_recvmsg, sctp_opt_info, sctp_peeloff, shutdown Notifications - Socket options
getsockopt and setsockopt functions- Socket states generic socket options IP socket options
ICMP socket options TCP socket options - SCTP socket options fcntl functions.
UNIT III ADVANCED SOCKETS I 9
Routing sockets Datalink socket address structure Reading and writing sysctl operations
get_ifi_info function Interface name and index functions- Key Management sockets Reading
and writing Dumping Security Association Database Creating static Security Association
Dynamically maintaining SAs Broadcasting Broadcast addresses Unicast versus Broadcast
(Client) Application development for broadcasting Race conditions Multicasting Multicast
addresses- Multicasting versus Broadcasting on a LAN Multicasting on a WAN Source specific
Multicast Multicast socket options mcast_join, (Client) Application development for
multicasting Receiving IP multicast infrastructure session announcements Sending and
receiving.
UNIT IV ADVANCED SOCKETS II 9
Advanced UDP sockets Receiving flags, Destination IP address and Interface index Datagram
truncation Using UDP instead of TCP Adding reliability to UDP Binding interface addresses
Concurrent UDP servers SCTP Congestion control performance -Advanced SCTP sockets
Partial delivery - Notifications Unordered data Binding a subset of addresses Determining
peer and local address information Finding an association Id given an IP address
Heartbeating and Address failure Peeling off an association Controlling timing Using SCTP
instead of TCP Out of band data Signal driven I/O Design & Implementation of secure
socket SCTP.
UNIT V NETWORK MANAGEMENT 9
Network Management fundamentals Issues in SNMP Basic concepts in RMON RMON MIB
statistics group- history group - alarm group - host group- hostTopN group- matrix group- filter
group - capture group- event group- token Ring group- Issues in RMON1 RMON2 Overview
Protocol Directory group Protocol Distribution group Address Map group RMON2 host group
37
RMON2 matrix group User History Collection group Probe Configuration group Extensions
and practical issues.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. W. Richard Stevens, Unix Network Programming Vol-I, Second Edition, Pearson
Education, 1998.
2. D.E. Comer, Internetworking with TCP/IP Vol- III, (BSD Sockets Version), Second
Edition, Pearson Education, 2003.
3. Michael Donahoo, Kenneth Calvert, TCP/IP Sockets in C, A practical guide for
programmers, Second Edition, Elsevier, 2009.
4. Forouzan, TCP/IP Protocol Suite Second Edition, Tata MC Graw Hill, 2003.
5. Stefan Lindskog, Anna Brunstrom, Design & Implementation of secure socket SCTP,
Transactions on Computer Science VI, Springer, LNCS5730, 2009.
6. Jun-ichiro itojun Hagino, IPv6 Network Programming, Elsevier India Private Limited,
NewDelhi, 2006.
7. William Stallings, SNMP, SNMPv2, SNMPv3 and RMON 1 and 2,Third Edition, Addison
Wesley, 1999.
8. Mani Subramaniam, Network Management: Principles and Practice, Addison Wesley,
First Edition, 2001.
WEB REFERENCES:
1. Guanhua Ye, Tarek Saadawi, Myung Lee, SCTP Congestion Control Performance In
Wireless Multi-Hop Networks, Communications and Networks Consortium , January 2011,
http://www.geocities.ws/yegh98/publications/753.pdf
2. Paul Stalvig, Introduction to the Stream Control Transmission Protocol (SCTP): The next
generation of the Transmission Control Protocol (TCP), F5- Networks Inc, Oct 2007,
www.f5.com/pdf/white-papers/sctp-introduction-wp.pdf
13MI104 : SOFT COMPUTING TECHNIQUES L T P C
3 1 0 4
Course Objectives:
To give students knowledge of soft computing theories fundamentals, i.e. fundamentals of
non-traditional technologies and approaches to solving hard real-world problems, namely
fundamentals of artificial neural networks, fuzzy sets and fuzzy logic and genetic
algorithms.
To introduce the ideas of fuzzy sets, fuzzy logic and use of heuristics based on human
experience
To become familiar with neural networks that can learn from available examples and
generalize to form appropriate rules for inference systems
To provide the mathematical background for carrying out the optimization associated with
neural network learning
38
To familiarize with genetic algorithms and other random search procedures useful while
seeking global optimum in self-learning situations
To introduce case studies utilizing the above and illustrate the intelligent behavior of
programs based on soft computing
Course Outcomes:
Apply the tolerance of imprecision and uncertainty for design of robust and low-cost
intelligent machines.
Acquire knowledge of soft computing theories fundamentals and so to design program
systems using approaches of these theories for solving various real-world problems.
Implement soft computing techniques in building intelligent machines
Apply a soft computing methodology for a particular problem
Apply fuzzy logic and reasoning to handle uncertainty and solve engineering problems
Apply genetic algorithms to combinatorial optimization problems and apply neural
networks to pattern classification and regression problems
Evaluate and compare solutions by various soft computing approaches for a given
problem.
UNIT I NEURAL NETWORKS 9
Introduction: Soft Computing Constituents Soft Computing Vs Hard Computing Applications -
Artificial Neural Network (ANN): Fundamental Concept Basic Terminologies Neural Network
Architecture Learning Process Fundamental Models of ANN: McCulloch-Pitts Model Hebb
Network Linear Separability. Supervised Learning Networks: Perceptron Network Adaline and
Madaline Networks Back Propagation Network Radial Basis Function Network
UNIT II UNSUPERVISED LEARNING 9
Unsupervised Learning Networks: Kohonen Self Organizing Network Counter Propagation
Network ART Network Hopfield Network - Special Network Support Vector Machine- Kernel
methods for Pattern classification- Kernel methods for function optimization.
UNIT III FUZZY LOGIC 9
Introduction- Classic Sets- Fuzzy Sets crisp relations- Fuzzy Relations- Fuzzy Equivalence and
Tolerance Relation Value assignments- Fuzzy Composition- Membership FunctionsFuzzification-
Defuzzification. Fuzzy Arithmetic Extension Principle Fuzzy Measures Fuzzy Classification
UNIT IV FUZZY MODELLIGN & APPLICATRION 9
Fuzzy Rules and Fuzzy Reasoning: Fuzzy Propositions Formation of Rules Decomposition of
Rules Aggregation of Rules Approximate Reasoning Fuzzy Inference and Expert Systems
Fuzzy Decision Making Fuzzy Logic Control Systems. Case Studies : Hybrid system- Neuro Fuzzy
system for various applications- Knowledge Leverage Based TSK Fuzzy System Modeling - Fuzzy
C-Means algorithms for very large Data
UNIT V GENETIC ALGORITHM & APPLICATIONS 9
Genetic Algorithm: Fundamental Concept Basic Terminologies Traditional Vs Genetic Algorithm
- Elements of GA - Encoding - Fitness Function Genetic Operators: Reproduction Cross Over -
Inversion and Deletion - Mutation Simple and General GA - The Schema Theorem- difference
between GA and GP- Applications of GA. Multiobjective Optimization- Hybrid GA for Feature
39
Selection- Multiobjective Genetic Fuzzy Clustering for pixel classification- Clustering Wireless
Sensor Network Using Fuzzy Logic and Genetic Algorithm
TUTORIAL :15 PERIODS
TOTAL: 45+15=60 PERIODS
REFERENCE BOOKS:
1. J.S.R. Jang, C.T. Sun, E. Mizutani, Neuro-Fuzzy and Soft Computing, Prentice Hall India,
2004
2. S.N. Sivanandam, S.N. Deepa, Principles of Soft Computing, Wiley India, 2007.
3. Timoty J. Ross, Fuzzy Logic with Engineering Applications, McGraw Hill, 1997.
4. Davis E.Goldberg, Genetic Algorithms: Search, Optimization and Machine Learning,
Addison Wesley, N.Y., 1989.
5. S. Rajasekaran, G.A.V. Pai, Neural Networks, Fuzzy Logic, Genetic Algorithms, Prentice
Hall, India, 2004.
6. Elaine Rich & Kevin Knight, Artificial Intelligence, Second Edition, Tata Mcgraw Hill
Publishing Comp., 2006, New Delhi.
7. Il-Seok Oh, Jin-Seon Lee and Byung-Ro Moon, Hybrid Genetic Algorithms for Feature
Selection, IEEE Transactions On Pattern Analysis And Machine Intelligence, Vol. 26, No.
11, PP: 1424-1437, 2004.
8. Deng. Z et al, Knowledge-Leverage-Based TSK Fuzzy System Modeling IEEE Transaction
on Neural networks and learning system, Vol.24. Issue:8, PP.1200-1212,2013
9. Sanghamitra Bandyopadhyay,, Ujjwal Maulik, and Anirban Mukhopadhyay, Multiobjective
Genetic Clustering for pixel Classification in Remote Sensing Imagery, IEEE Transactions
on Geoscience and remote sensing, Vol. 51, No. 6, June 2013
10.Havens, T.C et al, Fuzzy C-Means algorithms for very large Data, IEEE Transaction on
Fuzzy system, Vol.20, No.6, PP: 1130-1146, 2012
11. Saeedian, E. et al, CFGA: Clustering Wireless Sensor Network Using Fuzzy Logic and
Genetic Algorithm, IEEE International Conference on Wireless Communications,
Networking and Mobile Computing(WiCOM), PP: 1:5 2011
13MC151: ADVANCED DATA STRUCTURES LABORATORY L T P C
(Common to M.E CSE / M.Tech IT) 0 0 3 2
Course Objectives:
To learn implementation of data structures for concurrency
To learn implementation of advanced data structures such as search trees, hash tables,
heaps and operations on them
To learn to implement advanced concurrent data structures
To learn to apply principles of efficient algorithm design and learn various advanced
algorithms
40
Course Outcomes:
Implement and apply concurrent linked lists, stacks, and queues
Perform operations on search trees and hash tables
Perform operations on different types of heaps
Implement and apply data structures for strings
Implement advanced concurrent structures
Apply design techniques for algorithms and advanced algorithms
SYLLABUS FOR THE LAB:
Each student has to work individually on assigned lab exercises. Lab sessions could be scheduled
as one contiguous three-hour session per week. The students have to complete a minimum of 12
exercises. It is recommended that all implementations are carried out in Java. If C or C++ has to
be used, then the threads library will be required for concurrency.
Implementation and applications of classic linear data structures, namely, linked lists,
queues, and stacks.
Implementation of various locking and synchronization mechanisms for concurrent linked
lists, concurrent queues, and concurrent stacks.
Implementation of weight balanced search trees and skip lists.
Implantation of suffix trees and pattern matching
Implementation of various heap structures.
Implementation of concurrent hashing, concurrent skip lists, and concurrent priority
queues.
Implementation of approximation and randomized algorithms.
Implementation of parallel sorting algorithms.
Developing an application involving concurrency and data structures.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. M. Herlihy and N. Shavit, The Art of Multiprocessor Programming, Morgan Kaufmann,
2012.
2. Peter Brass, Advanced Data Structures, Cambridge University Press, 2008.
3. A. V. Aho, J. E. Hopcroft, and J. D. Ullman, The Design and Analysis of Computer
Algorithms, Addison-Wesley, 1975.
4. Gavpai, Data Structures and Algorithms Concepts, techniques and Applications, First
Edition, Tata McGraw-Hill, 2008.
5. Edited by S.K. Chang, Data Structures and Algorithms Series of Software Engineering
and Knowledge Engineering, Vol. 13, World Scientific Publishing, 2003.
6. Jon Kleinberg, "Algorithm Design", Addison-Wesley, 2013.
7. David P. Williamson, David B. Shmoys, The Design of Approximation Algorithms,
Cambridge University Press, 2011.
8. Rajeev Motwani and PrabhakarRaghavan, Randomized Algorithms, Cambridge University
Press, 1995.
9. Michael J. Quinn, Parallel Computing: Theory & Practice, Tata McGraw Hill Edition, 2003.
10. AnanthGrama, Anshul Gupta, et al., Introduction to Parallel Computing, Second Edition,
Pearson Education, 2003.
41
WEB REFERENCES:
1. http://www.w3schools.in/c-programming-language
2. http://www.geeksforgeeks.org/pattern-searching-set-8-suffix-tree-introduction/
3. http://iamwww.unibe.ch/~wenger/DA/SkipList/
4. http://www.cs.au.dk/~gerth/slides/soda98.pdf
5. http://www.cs.sunysb.edu/~algorith/files/suffix-trees.shtml
6. http://pages.cs.wisc.edu/~shuchi/courses/880-S07/scribe-notes/lecture20.pdf
List of Sample Exercises
1. A file consists of a list of CD titles with information such as category(in alphanumeric
form maximum of 25 characters)and title(in alphanumeric form maximum of 25
characters characters).Duplicatesentriesare allowed. Example Categories are: Education,
Entertainment, Examinations, Soft skill, Games etc.
Design a system to get new entries to add, search for an entry, delete the existing
entries and view the titles. The system does not know the number of titles in advance.
The system may keep the information either in order or unordered. Compare the
efficiency of the above two approaches.
2. An electronics goods dealer has 50 different types of item and for each item he has a
maximum of 5 branded company products for sale. Read and store the monthly sales
(day wise) of the shop in a multi list and produce the following reports.
List the day wise total sales amount of all goods
List the weekly sale details of refrigerator.
List the monthly sale details of all LG brand electronic good
Make the list as empty at the end of seventh day of the week after taking
appropriate back up.
3. Construct concurrent bi-stack in a single array and perform the following operation for
string manipulation such as:
i) Search for a character and Replace it by a new one if available
ii) Reverse a String
iii) Test for palindrome
iv) Count the occurrences of the given character
4. A deque is a data structure consisting of a list of items, on which the following
operations are possible:
Push(X,D): Insert item X on the front end of the deque D.
Pop(D): Remove the front item from the deque D and return it
Inject(X,D): Insert an item X on the rear end of the deque D.
Eject(D): Remove the rear item from the deque D and return it.
Implement the above concurrent double ended queue.
5. Suppose that an advertising company maintain a database and needs to generate mailing
labels for certain constituencies. A typical request might require sending out a mailing to
people who are between the ages of 34 and 49and whose annual income is between
$100000 and $200000.This problem is known as a two dimensional range query. To solve
such range queries a two dimensional search tree namely 2-D tree can be used which has
42
the simple property that branching on odd levels is done with respect to the first key and
branching on even levels is done with respect to the second key. Implement a 2-D tree
with company database consist of the following fields such mail-ID, Age, Gender, Annual
Income and Occupation.
6. Using weight balanced search tree construct a Telephone directory with the
Information such as: Phone Number, Name and address then perform the following
a)Search for a phone number and print the customer name and address
b) Remove a Phone number from the directory
c) Change the address of the customer whose phone number is given.
d) Print the content of the directory
7. Construct a Red-Black tree with the database containing Book detail such access Number,
Title, Author name, Department and price. Perform the following operations
i) Search for a book based on Book title
ii) Add a new book entry into the database
iii)Remove the lost book entry from the database
Note: Arrange the list of records based an book title to improve the performance of the
frequent search operations.
8. The details of employees (Emp.Id, Name, Department and Total Years of experience) of a
company are to be maintained. The list indicates both alphabetical ordering of names,
ascending order of Emp.Id Number and alphabetical ordering of department names.
Perform the following by using Skip List structure:
Insert a new employee detail in the appropriate position
Remove an employee detail where Emp.Id is given
Find an employee detail whose ID is given.
Find employee information whose name in a particular department is
given.
List all employee detail in order of their name.
9. Construct a Suffix Tree data structure to construct a Telephone directory Telephone
directory with the Information such as: Phone Number, Name and address then perform
the following operation
a. Insert a new customer information into the directory
b. Disable a connection and Delete that phone number from the
directory
c. Print all customer addresses that starts with name AN*.
d. Print all customer addresses and phone numbers whose name starts
with alphabets A-E.
10. Construct double ended priority queue using Min-Max heaps and perform the following
a) Find 3
rd
minimum
b) Delete an item(with random priority)
c) Delete maximum element
d) Heap sort in descending order
e) Modify the priority of an item
43
11. Online dictionary implementation using Hashing
Implement a dictionary which contains the meaning of different words. Both the word and
the meaning can be in the same language. Your program should read a word and should
give the meaning. If the word is a new one (not available in the dictionary) then include
the word into its correct position with its meaning.
Implement the same problem using concurrent Hashing technique.
12. Implementation of Approximation algorithm : Solve the 0-1 Knapsack problem
Given a knapsack with maximum weight capacity C and a set S consisting of n items,
each item i with weight w
i
and profit p
i
(all w
i
, p
i
and W are integer values). The problem
is to pack the knapsack to achieve maximum total profit of packed items with items total
weight less than or equal to C.
13. Implementation of randomized algorithm: Find the solution for the Project selection
problem.
In the project selection problem, there are n projects and m equipments. Each project pi
yields revenue r(pi)and each equipment qi costs c(qi) to purchase. Each project requires
a number of equipments and each equipment can be shared by several projects. The
problem is to determine which projects and equipments should be selected and
purchased respectively, so that the profit is maximized.
14. Implement the following parallel sorting and compare the performance of those
algorithms.
i) parallel Quick sort
ii) Parallel merge sort
iii) Batchers Bitonic sort
Note:
Batchers Bitonic sort is a parallel sorting algorithm whose main operation is a technique
for merging two bitonic sequences. A bitonic sequence is the concatenation of an
ascending and a descending sequence. For example 2, 4, 6, 8, 23, 8, 5, 3, 0 is a bitonic
sequences.
13MI151: NETWORK PROGRAMMING LABORATORY L T P C
0 0 3 2
Course Outcomes:
Design network applications using TCP and UDP
Demonstrate the usage of various networking tools.
Analyze network traffic
Analyze packets transmitted over the network.
Simulate the given scenario and analyze the happenings.
List of Exercises
1. Write a socket program to implement the following for desired application.
a. Iterative and Reliable client Servers
b. Iterative and Unreliable Client Servers
c. Concurrent and Reliable Client Servers using fork and thread
44
d. Concurrent and Unreliable Client Servers using select and poll.
e. Add reliability to UDP protocol.
f. Multiplexing both TCP and UDP.
g. SCTP protocol
2. Use the software like wireshark in a LAN to capture the packet and do a statistical analysis
such as: the number of packets (bits) flowing in/out of a designated system, a pair wise
packet flow among the given IP addresses
3. Use the packet capturing tool and measure the traffic from each node in a application wise,
and pair wise traffic application
4. Repeat exercise 8 for protocol wise traffic analysis.
5. Simulate the transmission of ping messages over a network topology and do the following.
a. Find the number of packets dropped due to congestion.
b. Analyze the performance of the different congestion control algorithms (Old Tahoe,
Tahoe, and Reno).
6. Simulate a network using n nodes and set multiple traffic nodes and do the following.
a. Plot congestion window for different source / destination.
13MI201 Web Mining and Information Retrieval L T P C
3 0 0 3
Course Objectives:
To understand the different knowledge discovery issues in data mining from the world wide
web.
To analyze the different algorithms commonly used by Web application.
To apply the role played by Web mining in Information retrieval and extraction
To analyze the use of probabilistic models for web mining
To analyze the current trends in Web mining
To understand the various applications of Information Retrieval giving emphasis to Multimedia
IR, Web Search
Course Outcomes:
Upon Completion of the course, the students will be able to
1. Identify and differentiate between application areas for web content mining, web structure mining
and web usage mining.
2. Analyze various key concepts such as deep web, surface web, semantic web, web log, hypertext,
social network, information synthesis, corpora and evaluation measures such as precision and
recall.
3. Use different methods and techniques such as word frequency and co-occurrence statistics,
normalization of data, machine learning, clustering, vector space models and lexical semantics.
4. Analyze various algorithms commonly used by web mining applications.
5. Apply different approaches and techniques of web mining for e.g. sentiment analysis, targeted
marketing, linguistic forensics, topic/trend-detection-tracking and multi-document summarization
(information aggregation).
6. Design an efficient search engine.
45
UNIT I INTRODUCTION 9
Overview of Data mining Data mining from a Business Perspective Data types, Input and output
of data mining algorithms- Decision Tree- Classification and Regression Trees Preprocessing and
Post processing in Data mining
UNIT II WEB SEARCH 9
Client Side Design: HTML5 Syntax and Semantics Markups Forms Audio Video - Microdata
and Custom Data - Canvas.Server Side Scripting: PHP Introduction Creating PHP Pages PHP with
MySQL Tables to display data Form elements.
UNIT III REPRESENTING WEB DATA 9
XML Basics XML Namespaces - XML Schema - DOM SAX XPath - XSL: Extensible Stylesheet
Language Extensible Stylesheet Language Transformations (XSLT) - JAXP
UNIT IV LEARNING 9
Similarity and Clustering Formulations and approaches- Bottom up and Top down Partitioning
Paradigms Clustering and Visualization via Embeddings Probabilistic Approaches to clustering
Collaborative Filtering Supervised Learning Semi Supervised Learning
UNIT V INFORMATION RETRIEVAL 9
Information Retrieval and Text Mining - Keyword Search - Nearest-Neighbor Methods - Measuring
Similarity - Web-Based Document Search - DocumentMatching - Inverted Lists - Evaluation of
Performance - Structure in a Document Collection - Clustering Documents by Similarity- Evaluation of
Performance - Information Extraction - Patterns and Entities from Text- Coreference and Relationship
Extraction - Template Filling and Database Construction-Survey on web mining-Personalized Concept-
Based Clustering of Search Engine Queries-Searching the Web Using Composed Pages-A Collaborative
Decentralized Approach to Web Search.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Sholom Weiss, Text Mining: Predictive Methods for Analyzing Unstructured Information,
Springer, 2005
2. Hercules Antonio do Prado, Edilson Fernada, Emerging Technologies of Text Mining:
Techniques and Applications, Information Science Reference (IGI), 2008
3. Min Song, Yi-fang Brrok Wu, Handbook of Research on Text and Web Mining
Technologies, Vol I & II, Information Science Reference (IGI),2009
4. Soumen Chakrabarti Mining the Web : Discovery Knowledge from Hypertext Data
Elsevier Science 2003
5. K.P.Soman,Shyam Diwakar, V.Ajay Insight into Data Mining Theory and Practice
Prentice Hall of India Private Ltd 2006
6. Deitel & Deitel, Neito, Lin, Sadhu, XML How to Program, Pearson Education,2008
7. Christopher D. Manning, Prabhakar Raghavan and Hinrich Schtze, Introduction to
Information Retrieval, Cambridge University Press, 2008
8. Web Mining Research: A Survey- SIGKDD Explorations ACM SIGKDD ,July 2000
9. IEEE TRANSACTIONS ON KNOWLEDGE AND DATA ENGINEERING, VOL. 20, NO. 11,
NOVEMBER 2008
10. SIGIR06, August 611, 2006, Seattle, Washington, USA. ACM 1-59593-369-7/06/0008
11. IEEE TRANSACTIONS ON SYSTEMS, MAN, AND CYBERNETICSPART A: SYSTEMS AND
HUMANS, VOL. 42, NO. 5, SEPTEMBER 2012
46
13MI202 CLOUD COMPUTING TECHNOLOGIES L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To understand the concept of cloud and utility computing.
To understand the various issues in cloud computing.
To familiarize themselves with the types of virtualization.
To familiarize themselves with the lead players in cloud.
To appreciate the emergence of cloud as the next generation computing paradigm.
To be able to set up a private cloud.
Course Outcomes:
Recognize the strengths and limitations of cloud computing
Discuss on various virtual machine products
Identify the architecture, infrastructure and delivery models of cloud computing Applications.
Suggest solutions for the core issues of cloud computing such as security, privacy and
interoperability
Decide the appropriate technologies, algorithms and approaches for the related issues
UNIT I OVERVIEW OF VIRTUALIZATION 8
Basics of Virtualization - Virtualization Types Desktop Virtualization Network Virtualization
Server and Machine Virtualization Storage Virtualization System-level of Operating
Virtualization Application Virtualization- Virtualization Advantages - Virtual Machine Basics
Taxonomy of Virtual Machines - Process Virtual Machines - System Virtual Machines Hypervisor
Interpretation and Binary translation.
UNIT II VIRTUALIZATION STRUCTURES 8
Implementation Levels of Virtualization - Virtualization Structures - Tools and Mechanisms -
Virtualization of CPU, Memory, I/O Devices - Virtual Clusters and Resource Management
Virtualization for Data-Center Automation.
UNIT III CLOUD INFRASTRUCTURE 9
Scalable Computing over the Internet Technologies for Network based Systems - System Models
for Distributed and Cloud Computing Service Oriented Architecture NIST Cloud Computing
Reference Architecture. Cloud Computing and Services Model Public, Private and Hybrid Clouds
Cloud Eco System - IaaS - PaaS SaaS. Architectural Design of Compute and Storage Clouds
Layered Cloud Architecture Development Design Challenges - Inter Cloud Resource Management
Resource Provisioning and Platform Deployment Global Exchange of Cloud Resources.
Case Study : Amazon Web Service reference , GoGrid, Rackspace.
UNIT IV PROGRAMMING MODEL 10
Parallel and Distributed Programming Paradigms MapReduce , Twister and Iterative MapReduce
Hadoop Library from Apache Mapping Applications - Programming Support - Google App
Engine, Amazon AWS - Cloud Software Environments -Eucalyptus, Open Nebula, OpenStack.
CloudSim Architecture - Cloudlets VM creation Broker VM allocation Hosts Data
Center.
UNIT V SECURITY IN THE CLOUD AND RESOURCE MANAGEMENT AND RESOURCE MANAGEMENT 10
Cloud Computing Risk Issues Cloud Computing Security Challenges Cloud Computing Security
47
Architecture Trusted cloud Computing Identity Management and Access Control Autonomic
Security. Dynamic Resource Allocation Using Virtual Machines for Cloud Computing Environment -
Optimization of Resource Provisioning Cost in Cloud Computing
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Kai Hwang, Geoffrey C Fox, Jack G Dongarra, Distributed and Cloud Computing, From
Parallel Processing to the Internet of Things, Morgan Kaufmann Publishers, 2012.
2. Ronald L. Krutz, Russell Dean Vines, Cloud Security A comprehensive Guide to Secure
Cloud Computing, Wiley India, 2010.
3. John W.Rittinghouse and James F.Ransome, Cloud Computing: Implementation,
Management, and Security, CRC Press, 2010.
4. George Reese, Cloud Application Architectures: Building Applications and Infrastructure
in the Cloud O'Reilly
5. Sivadon Chaisiri, Bu-Sung Lee, and Dusit Niyato, Optimization Of Resource Provisioning
Cost In Cloud Computing, IEEE TRANSACTIONS ON SERVICES COMPUTING, VOL. 5, NO.
2, APRIL-JUNE 2012.
6. Zhen Xiao, Weijia Song, And Qi Chen, Dynamic Resource Allocation Using Virtual
Machines For Cloud Computing Environment, IEEE TRANSACTIONS ON PARALLEL AND
DISTRIBUTED SYSTEMS, VOL. 24, NO. 6, JUNE 2013.
7. Rajkumar Buyya, Christian Vecchiola, S.Tamarai Selvi, Mastering Cloud Computing,
TMGH,2013.
8. James E. Smith, Ravi Nair, Virtual Machines: Versatile Platforms for Systems and
Processes, Elsevier/Morgan Kaufmann, 2005.
9. William von Hagen, Professional Xen Virtualization, Wrox Publications, January, 2008.
10. Dimitrios Zissis, Dimitrios Lekkas, Addressing Cloud Computing Security Issues, Future
Generation Computer Systems 28 (2012) 583592,ELSEVIER
11. Rodrigo N.Calheiros, Rajiv Ranjan, Anton Beloglazov, Csar A. F. De Rose, and Rajkumar
Buyya, CloudSim: A Toolkit for Modeling and Simulation of Cloud Computing
Environments and Evaluation of Resource Provisioning Algorithms , Cloud Computing
and Distributed Systems (CLOUDS) Laboratory.
http://www.buyya.com/papers/CloudSim2010.pdf
13MI203 CYBER SECURITY L T P C
3 0 0 3
Course Objectives:
To know the concepts of Cyber security and create awareness about this field
in the society.
To familiarize with the fundamental concepts Cyber security and Hacking
To understand the concept of Forensic science, Ethical Hacking, Mobile
hacking and Cryptography
48
Course Outcomes:
Able to use tools for preserving the privacy of confidential data
Analyze security threats, vulnerabilities, and attacks
Demonstrate exploits of systems and networks
Select proper risk analysis methods for protecting infrastructure.
Explain major advantages and disadvantages of different security methods
Design small and large-scale protection mechanisms
UNIT I Cyber Security Fundamentals 8
Network and Security Concepts - Information Assurance Fundamentals- Basic Cryptography-
Symmetric Encryption- Public Key Encryption-The Domain Name System (DNS) Firewalls-
Virtualization- Radio-Frequency Identification-Microsoft Windows Security Principles-Windows
Tokens- Window Messaging- Windows Program Execution- The Windows Firewall
UNIT II Attacker Techniques and Motivations 8
How Hackers Cover Their Tracks (Anti-forensics) - How and Why Attackers Use Proxies -Tunneling
Techniques-Fraud Techniques- Phishing, Smishing, Vishing and Mobile Malicious Code- Rogue Anti-
Virus- Click Fraud -Threat Infrastructure - Botnets - Fast-Flux -Advanced Fast-Flux
UNIT III Exploitation 9
Techniques to Gain a Foothold - Shellcode - Integer Overflow Vulnerabilities - Stack-Based Buffer
Overflows - Format-String Vulnerabilities- SQL Injection - Malicious PDF Files - Race Conditions -
Web Exploit Tools -DoS Conditions - Brute-Force and Dictionary Attacks -Misdirection,
Reconnaissance and Disruption Methods - Cross-Site Scripting (XSS) - Social Engineering -
WarXing - DNS Amplification Attacks-Fault Injection Attacks on Cryptographic Devices
UNIT IV Malicious Code 10
Self-Replicating Malicious Code - Worms - Viruses - Evading Detection and Elevating Privileges -
Obfuscation - Virtual Machine Obfuscation - Persistent Software Techniques -Rootkits - Spyware -
Attacks against Privileged User Accounts and Escalation of Privileges
Token Kidnapping - Virtual Machine Detection -Stealing Information and Exploitation
Form Grabbing - Man-in-the-Middle Attacks - DLL Injection - Browser Helper Objects, Automatic
Malicious Code Analysis System
UNIT V Defense and Analysis Techniques AND RESOURCE MANAGEMENT 10
Memory Forensics - Why Memory Forensics Is Important - Capabilities of Memory Forensics -
Memory Analysis Frameworks - Dumping Physical Memory - Installing and Using Volatility -
Finding Hidden Processes -Volatility Analyst Pack - Honeypots -Malicious Code Naming -Automated
Malicious Code Analysis Systems - Passive Analysis - Active Analysis - Physical or Virtual Machines-
Intrusion Detection Systems Wireless Intrusion detection system.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Cyber Security Essentials, James Graham, Ryan Olson, Rick Howard Auerbach Publications
2. Computer Security Handbook, Seymour Bosworth, M. E. Kabay, Eric Whyne, John Wiley &
Sons, 2009
3. Cybersecurity: The Essential Body of Knowledge , Dan Shoemaker, Cengage Learning 2011
49
4. Security in Computing, Charles B. Pfleeger, Shari Lawrence Pfleeger, Third Edition, Pearson
Education, 2003
5. AMCAS: An Automatic Malicious Code Analysis System , Jia Zhang ; Yuntao Guan ; Xiaoxin
Jiang ; Haixin Duan , WAIM '08. The Ninth International Conference on Web-Age Information
Management, 2008.
6. Fault Injection Attacks on Cryptographic Devices: Theory, Practice, and Countermeasures ,
Barenghi, A. ; Politec. di Milano, Milan, Italy ; Breveglieri, L. ; Koren, I. ; Naccache, D.
Proceedings of the IEEE,Nov. 2012
7. Wireless Intrusion Detection System Using a Lightweight Agent , Haddadi, F. ; Sarram, M.A.
Second International Conference on Computer and Network Technology (ICCNT), 2010
13MI204: BIG DATA ANALYTICS L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To Explore the fundamental concepts of big data and analytics
To apply various techniques for mining data stream.
To analyze the big data using intelligent techniques.
To apply search methods and Visualization.
To design applications using Map Reduce Concepts.
Course Outcomes:
Work with big data platform and its analysis techniques.
Design efficient algorithms for mining the data from large volumes.
Model a framework for Human Activity Recognition.
Analyze the big data for useful business applications.
Implement search methods and Visualization
UNIT I INTRODUCTION TO BIG DATA 9
Introduction to Big Data Platform Challenges of Conventional Systems - Intelligent data analysis
Nature of Data - Analytic Processes and Tools - Analysis Vs Reporting - Modern Data Analytic
Tools - Statistical Concepts: Sampling Distributions - Re-Sampling - Statistical Inference -
Prediction Error.
UNIT II DATA ANALYSIS 9
Regression Modeling - Multivariate Analysis Bayesian Methods Bayesian Paradigm - Bayesian
Modeling - Inference and Bayesian Networks - Support Vector and Kernel Methods - Analysis of
Time Series: Linear Systems Analysis - Nonlinear Dynamics - Rule Induction - Fuzzy Logic:
Extracting Fuzzy Models from Data - Fuzzy Decision Trees
UNIT III SEARCH METHODS AND VISUALIZATION 9
Search by simulated Annealing Stochastic, Adaptive search by Evaluation Evalution Strategies
Genetic Algorithm Genetic Programming Visualization Classification of Visual Data Analysis
Techniques Data Types Visualization Techniques Interaction techniques Specific Visual data
analysis Techniques.
50
UNIT IV MINING DATA STREAMS 9
Introduction To Streams Concepts Stream Data Model and Architecture - Stream Computing -
Sampling Data in a Stream Filtering Streams Counting Distinct Elements in a Stream
Estimating Moments Counting Oneness in a Window Decaying Window - Real time Analytics
Platform(RTAP) Applications - Case Studies - Real Time Sentiment Analysis, Stock Market
Predictions.
UNIT V FRAMEWORKS 9
MapReduce Hadoop, Hive, MapR Sharding NoSQL Databases - S3 - Hadoop Distributed File
Systems Case Study- Preventing Private Information Inference Attacks on Social Networks-
Grand Challenge: Applying Regulatory Science and Big Data to Improve Medical Device Innovation
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Michael Berthold, David J. Hand, Intelligent Data Analysis, Springer, 2007.
2. Anand Rajaraman and Jeffrey David Ullman, Mining of Massive Datasets, Cambridge
University Press, 2012.
3. Bill Franks, Taming the Big Data Tidal Wave: Finding Opportunities in Huge Data Streams
with Advanced Analytics, John Wiley & sons, 2012.
4. Glenn J. Myatt, Making Sense of Data, John Wiley & Sons, 2007
5. Pete Warden, Big Data Glossary, OReilly, 2011.
6. Jiawei Han, Micheline Kamber Data Mining Concepts and Techniques, Second Edition,
Elsevier, Reprinted 2008.
7. Raymond Heatherly , Murat Kantarcioglu and Bhavani Thuraisingham Preventing Private
Information Inference Attacks on Social Networks IEEE Transaction on Knowledge and
Data Engineering,Vol 25, No.8 ,August 2013.
8. Arthur G. Erdman , Daniel F. Keefe , Senior Member, IEEE, and Randall Schiest Grand
Challenge: Applying Regulatory Science and Big Data to Improve Medical Device
Innovation IEEE TRANSACTIONS ON BIOMEDICAL ENGINEERING, VOL. 60, NO. 3, MARCH
2013
13MI251: BIG DATA ANALYTICS LABORATORY L T P C
0 0 3 2
Course Objectives:
To Explore the fundamental concepts of big data and analytics
To apply various programming techniques for mining data stream.
To apply search methods and Visualization.
To design applications using Map Reduce Concepts
To apply various data mining concepts in Weka tool.
51
Course Outcomes
Work with big data platform and its analysis techniques.
Design efficient algorithms for mining the data from large volumes.
Analyze the big data for useful business applications.
Implement search methods and Visualization.
Implement various application using Map Reduce concepts.
Implement various data mining concepts in Weka tool.
List of Exercises
1. Creating an interactive Hadoop MapReduce job flow.
2. Querying Hadoop MapReduce jobs using Hive.
3. Loading unstructured data into Hadoop Distributed File System (HDFS).
4. Simplifying Big Data processing and communicating with Pig Latin.
5. Creating and customizing applications to analyze data.
6. Implementing a targeted Big Data strategy.
7. Using weka tool to exploring the data.
8. Preprocess the given data using weka tool.
9. Apply different classification techniques to classify the given data set.
10. Apply various clustering techniques to cluster the data.
11. Apply various association rule mining algorithms.
13MI252: CLOUD COMPUTING LABORATORY L T P C
(Common to M.E CSE & M.Tech IT) 0 0 3 2
Course Objectives:
To learn how to use Cloud Services.
To implement Virtualization
To implement Task Scheduling algorithms.
To implement Energy-conscious model.
To build Private Cloud.
Course Outcomes:
Analyze the use of Cloud Applications
Apply resource allocation, scheduling algorithms.
Implement Energy-conscious model.
Create virtual machines from available physical resources.
Setup a private cloud.
Familiarize with Open Source Cloud computing Software.
SYLLABUS FOR THE LAB:
List Of Exercises:
1. Study and Usage of Google Apps.
2. Implement Virtual OS using virtual box.
3. Simulate VM allocation algorithm using cloudSim.
4. Simulate Task Scheduling algorithm using CloudSim.
52
5. Simulate Energy-conscious mode006C using CloudSim.
6. Setup a Private Cloud Using Open Stack or Eucalyptus.
7. Install and configure Open Stack Object Storage - Swift in Ubuntu.
8. Implement Open Stack Nova-Compute.
9. Implement Open Stack Image services Glance.
ELECTIVE I
13MI401: X INFORMATICS L T P C
3 0 0 3
Course Objectives:
To present the state-of-the art developments in medical informatics, public health
informatics and bioinformatics.
To demonstrate a thorough understanding of creation, interpretation, storage and usage of
medical information.
To understand the case study of computerized patient record.
To study and use different tools for clinical information system.
To apply the knowledge of bio informatics for systems.
Course Outcomes:
Design and develop clinical and hospital management system on his own.
Design computerized information systems for use in health care.
Assure confidentiality of protected patient health information when using health
information system.
Conceive and design effective user-centered systems to support medical work and
decision-making.
Work with different medical imaging techniques.
Apply the knowledge of bio informatics for biological databases
Evaluate outcomes of the use of information in clinical practice.
UNIT I MEDICAL INFORMATICS 9
Introduction - Structure of Medical Informatics Internet and Medicine -Security Issues Computer
based Medical Information Retrieval, Hospital Management and Information System - Functional
Capabilities of a Computerized HIS - E-Health Services - Health Informatics Medical Informatics
Bioinformatics.
UNIT II HEALTHCARE INFORMATICS 9
Strategic Planning - Selecting a Health Care Information System - Systems Integration and
Maintenance - Systems Integration - Regulatory and Accreditation Issues - Contingency Planning
and Disaster Recovery.
UNIT III COMPUTERISED PATIENT RECORD 9
Introduction - History taking by Computer, Dialogue with the Computer - Components and
Functionality of CPR - Development Tools Intranet - CPR in Radiology - Application Server
Provider - Clinical Information System - Computerized Prescriptions for Patients.
53
UNIT IV COMPUTERS IN CLINICAL LABORATORY AND MEDICAL IMAGING 9
Automated Clinical Laboratories - Automated Methods in Hematology - Cytology and Histology -
Intelligent Laboratory Information System - Computerized ECG, EEG And EMG - Computer Assisted
Medical Imaging - Nuclear Medicine - Ultrasound Imaging Ultrasonography -Computed X-Ray
Tomography - Radiation Therapy and Planning, Nuclear Magnetic Resonance.
UNIT V BIO-INFORMATICS 9
Pair wise Sequence Alignment Local Versus Global Alignment Multiple Sequence Alignment
Computational Methods Dot Matrix Analysis Substitution Matrices Dynamic Programming
Word Methods Bayesian Methods Multiple Sequence Alignment Dynamic Programming
Progressive Strategies Iterative Strategies Tools Nucleotide Pattern Matching Polypeptide
Pattern Matching Utilities Sequence Databases -Improved Algorithms for Matching r-Separated
Sets with Applications to Protein Structure Alignment - DALIX: Optimal DALI Protein Structure
Alignment.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. R.D.Lele, Computers in Medicine Progress in Medical Informatics, Tata Mcgraw Hill
Publishing Computers, 2005.
2. Mohan Bansal, Medical informatics, Tata Mcgraw Hill Publishing, 2003.
3. Burke, Lillian; Well, Barbara, Information Technology for the Health Professions,
Prentice Hall, 2006.
4. Bryan Bergeron, Bio Informatics Computing, Second Edition, Pearson Education,
2003.
5. Karen Wager, Frances Lee and John Glaser, Managing Health Care Information
Systems, Second Edition, Josey-Bass Publishers, 2009.
6. Aleksandar Poleksic, Improved Algorithms for Matching r-Separated Sets with
Applications to Protein Structure Alignment, IEEE/ACM Transactions On Computational
Biology And Bioinformatics, Vol. 10, No. 1, January/February 2013.
7. Inken Wohlers, Rumen Andonov, and Gunnar W. Klau, DALIX: Optimal DALI Protein
Structure Alignment, IEEE/ACM Transactions On Computational Biology And
Bioinformatics, Vol. 10, No. 1, January/February 2013.
13MI402: XML AND WEB SERVICES L T P C
3 0 0 3
Course Objectives:
To explore the basics of XML technology
To analyze the background of distributed information system
To analyze and design a web service based application
To apply the security features of web services and service composition
Course Outcomes:
Create, validate, parse, and transform XML documents
Design a middleware solution based application
Develop web services using different technologies
54
Design secured web data transmission
Compose set of web services using BPEL
UNIT I XML FUNDAMENTALS 9
XML structuring with schema DTD XML Schema XML Processing DOM SAX Presental XSL
Transformation XSLT XPath XQuery
UNIT II DISTRIBUTED INFORMATION SYSTEM 9
Distributed information system Design of IB Architecture of IB Communication in an IS
Middleware RPC TP monitors Object brokers Message oriented middleware EAI EAI
Middleware Workflow Management benefits and limitations Web technologies for Application
Integration.
UNIT III WEB SERVICES 9
Web Services Definition Web Services and EAI Web Services Technologies web services
Architecture SOAP WSDL UDDI WS Addressing WS Routing WS- Security WS Policy
Web Service invocation framework web services using java WS using .NET mobile web service.
UNIT IV XML SECURITY 9
XML Security and meta framework - XML signature XML Encryption SAML XKMS WS
Security RDF semantic Web service.
UNIT V SERVICE COMPOSITION 9
Service Coordination and Composition coordination protocols WS Coordination WS
transaction RosttaNet ebXML WSCI Service Composition Service Composition Models
Dependencies between coordination and composition BPEL Current trends - QoS-Aware Web
Service Recommendation by Collaborative Filtering
Case Study : Service-Centric Framework for a Digital Government Application.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
R1. Gystavo Alonso, Fabio casasi, Hareemi kuno, vijay machiraju, web Services concepts,
Architecture and Applications, Springer, 2004.
R2. Ron Schmelzer etal XML and Web Services, Pearson Education, 2002.
R3. Sandeep chatterjee and james webber, Developing Enterprise web services: An
Architects and Guide, Practice Hall, 2004.
R4. Freunk p.coyle, XML, web Services and the Data Revolution, Pearson, 2002.
R5. Zibin Zheng, Hao Ma, Michael R. Lyu, and Irwin King, QoS-Aware Web Service
Recommendation by Collaborative Filtering, IEEE TRANSACTIONS ON SERVICES
COMPUTING, VOL. 4, NO. 2, APRIL-JUNE 2011
R6. Athman Bouguettaya, Qi Yu, Xumin Liu and Zaki Malik, Service-Centric Framework for a
Digital Government Application, IEEE TRANSACTIONS ON SERVICES COMPUTING, VOL. 4,
NO. 1, JANUARY-MARCH 2011.
55
13MC407:ENERGY-AWARE COMPUTING L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To know the fundamental principles energy efficient devices
To study the concepts of Energy efficient storage
To introduce energy efficient algorithms
To enable the students to know energy efficient techniques involved to support real-time
systems.
To study Energy aware applications
Course Outcomes:
Design Power efficient architecture Hardware and Software.
Analyze power and performance trade off between various energy aware storage devices.
Implement various energy aware algorithms.
Restructure the software and Hardware for Energy aware applications.
Explore the Energy aware applications
UNIT I INTRODUCTION 9
Energy efficient network on chip architecture for multi core system-Energy efficient MIPS CPU core
with fine grained run time power gating Low power design of Emerging memory technologies.
UNIT II ENERGY EFFICIENT STORAGE 9
Disk Energy Management-Power efficient strategies for storage system-Dynamic thermal
management for high performance storage systems-Energy saving technique for Disk storage
systems
UNIT III ENERGY EFFICIENT ALGORITHMS 9
Scheduling of Parallel Tasks Task level Dynamic voltage scaling Speed Scaling Processor
optimization- Memetic Algorithms Online job scheduling Algorithms
UNIT IV REAL TIME SYSTEMS 9
Multi processor system Real Time tasks- Energy Minimization Energy aware scheduling-
Dynamic Reconfiguration- Adaptive power management-Energy Harvesting Embedded system
UNIT V ENERGY AWARE APPLICATIONS 9
On chip network Video codec Design Surveillance camera- Low power mobile storage.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Ishfaq Ah mad, Sanjay Ranka, Handbook of Energy Aware and Green Computing, Chapman and
Hall/CRC, 2012
2. Chong-Min Kyung, Sungioo yoo, Energy Aware system design Algorithms and Architecture,
Springer, 2011.
3. Bob steiger wald ,Chris:Luero, Energy Aware computing, Intel Press,2012.
4. Ramesh Karri, David Goodman Eds, System Level Power Optimization for Wireless Multimedia
Communication Power Aware Computing , Kluwer Academic Publishers, 2002
WEB REFERENCES:
1. http://www.inf.ed.ac.uk/teaching/courses/eac/
56
13MI403 : INTERNET OF THINGS L T P C
(Common to M.E CSE & M.Tech IT) 3 0 0 3
Course Objectives:
To learn the basic issues, policy and challenges in the Internet
To understand the components and the protocols in Internet
To build a small low cost embedded system with the internet
To understand the various modes of communications with internet
To learn to manage the resources in the Internet
To deploy the resources into business
To understand the cloud and internet environment.
Course Outcomes:
At the end of this course the students will be able to:
Identify the components of IOT
Design a portable IOT using appropriate boards
Program the sensors and controller as part of IOT
Develop schemes for the applications of IOT in real time scenarios
Establish the communication to the cloud through wifi/ Bluetooth
Manage the internet resources
Model the Internet of things to business
UNIT I INTRODUCTION 9
Definition phases Foundations Policy Challenges and Issues - identification - security
privacy. Components in internet of things: Control Units Sensors Communication modules
Power Sources Communication Technologies RFID Bluetooth Zigbee Wifi Rflinks
Mobile Internet Wired Communication
UNIT II PROGRAMMING THE MICROCONTROLLER FOR IOT 9
Basics of Sensors and actuators examples and working principles of sensors and actuators
Cloud computing and IOT Arduino/Equivalent Microcontroller platform Setting up the board -
Programming for IOT Reading from Sensors
Communication: Connecting microcontroller with mobile devices communication through
bluetooth and USB connection with the internet using wifi / ethernet
UNIT III RESOURCE MANAGEMENT IN THE INTERNET OF THINGS 9
Clustering - Software Agents - Data Synchronization - Clustering Principles in an Internet of Things
Architecture - The Role of Context - Design Guidelines -Software Agents for Object - Data
Synchronization- Types of Network Architectures - Fundamental Concepts of Agility and
Autonomy-Enabling Autonomy and Agility by the Internet of Things-Technical Requirements for
Satisfying the New Demands in Production - The Evolution from the RFID-based EPC Network to an
Agent based Internet of Things- Agents for the Behaviour of Objects
57
UNIT IV BUSINESS MODELS FOR THE INTERNET OF THINGS 9
The Meaning of DiY in the Network Society- Sensor-actuator Technologies and Middleware as a
Basis for a DiY Service Creation Framework - Device Integration - Middleware Technologies
Needed for a DiY Internet of Things Semantic Interoperability as a Requirement for DiY Creation -
Ontology- Value Creation in the Internet of Things-Application of Ontology Engineering in the
Internet of Things-Semantic Web-Ontology - The Internet of Things in Context of EURIDICE -
Business Impact
UNIT V FROM THE INTERNET OF THINGS TO THE WEB OF THINGS: 9
Resource-oriented Architecture and Best Practices- Designing RESTful Smart Things - Web-
enabling Constrained Devices - The Future Web of Things - Set up cloud environment send data
from microcontroller to cloud Case study CAM:cloud Assisted Privacy Other recent projects.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Charalampos Doukas , Building Internet of Things with the Arduino, Create space, April
2002
2. Dieter Uckelmann et.al, Architecting the Internet of Things, Springer, 2011
3. Luigi Atzor et.al, The Internet of Things: A survey, , Journal on Networks, Elsevier
Publications, October, 2010
4. Huang Lin ; Dept. of Electr. & Comput. Eng., Univ. of Florida, Gainesville, FL, USA ; Jun
Shao ; Chi Zhang ; Yuguang Fang,CAM: Cloud-Assisted Privacy Preserving Mobile Health
Monitoring IEEE Transactions on Information Forensics and Security, 2013
5. Pengwei Hu; Fangxia Hu An optimized strategy for cloud computing architecture, 3rd IEEE
Transactions on Computer Science and Information Technology (ICCSIT), 2010
WEB REFERENCES:
1. http://postscapes.com/
2. http://www.theinternetofthings.eu/what-is-the-internet-of-things
13MI404: PERFORMANCE EVALUATION AND RELIABILITY OF
INFORMATION SYSTEMS
L T P C
3 0 0 3
Course Objectives:
Gain a basic understanding of probability theory and its applications to networks
Gain an understanding of Markov chains, including Multi-dimensional chains and their
applications in the analysis of computer networks.
Gain an understanding of queuing system models such as M/M/1, M/M/m/m and M/G/1 and
their applications in the analysis of computer networks.
Gain an appreciation for the challenges in the analysis of network of queues and some of the
fundamental results in the field including Burkes theorem, Jacksons theorem etc.
Gain an understanding of the reliability basics, modeling and analysis
58
Course Outcomes:
Apply the probability concepts the Networks.
Demonstrate the usage of Markov Chains for the analysis of networks
Able to select opt Queuing discipline for the real time network applications
Appreciate the importance of Reliability concepts for Network modeling
Solve research problems related to Computer networks and evaluate its performance
Design of network of queues and analyze using Burkes theorem, Jacksons theorem
UNIT I 9
Performance Characteristics Requirement Analysis: Concepts User, Device, Network
Requirements Process Developing RMA ,Delay, Capacity Requirements Flow Analysis
Identifying and Developing Flows Flow Models Flow Prioritization Specification.
UNIT II 9
Random variables - Stochastic process Link Delay components Queuing Models Littles
Theorem Birth & Death process Queuing Disciplines.
UNIT III 9
Markovian FIFO Queuing Systems M/M/1 M/M/a M/M/ - M/G/1 M/M/m/m and other
Markov-Non-Markovian and self-similar models Network of Queues Burkes Theorem
Jacksons Theorem.
UNIT IV 9
Reliability and Availability concepts-failure Containment and redundancy-Robust Design principles-
Error detection-Analyzing and modeling reliability and robustness
UNIT V 9
Intelligent Packet Dropping for Optimal Energy-Delay Tradeoffs in Wireless Downlinks- An
Interacting Stochastic Models Approach for the Performance Evaluation of DSRC
Vehicular Safety Communication- Performance modeling of epidemic routing
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Eric Bauer, Design for Reliability: Information and Computer-Based Systems ,Wiley-IEEE
Press, 2011
2. James D.McCabe , Network Analysis ,Architecture and Design , 2
nd
dition,Elsevier,2003
3. Raj Jain,"The Art of Computer Systems Performance Analysis: Techniques for Experimental
Design, Measurement, Simulation, and Modeling",Wiley - Interscience, 1991
4. Bertsekas & Gallager , Data Networks , second edition ,Pearson Education,2003
5. Introduction to Probability Models by Sheldon Ross (8th edition) Academic Press, New York ,
2003
6. Nader F.Mir Computer and Communication Networks,Pearson Education.2007
7. Paul J.Fortier, Howard E.Michel, Computer Systems Performance Evaluation and Prediction,
Elsevier,2003
8. Intelligent Packet Dropping for Optimal Energy-Delay Tradeoffs in Wireless Downlinks, Neely,
M.J, IEEE Transactions On Automatic Control, VOL. 54, NO. 3, March 2009
59
9. An Interacting Stochastic Models Approach for the Performance Evaluation of DSRC Vehicular
Safety Communication, Xiaoyan Yin, Xiaomin Ma, and Kishor S. Trivedi, IEEE Transactions On
Computers, VOL. 62, NO. 5, May 2013
10. Performance modeling of epidemic routing with Heterogeneous Node Types, Yin-Ki Ip ; Wing-
Cheong Lau ; On-Ching Yue IEEE International Conference on Communications, 2008.
13MI405: NEXT GENERATION WIRELESS NETWORKS L T P C
3 0 0 3
Course Objectives:
To learn various generations of wireless and cellular networks
To study about fundamentals of 3G Services, its protocols and applications
To study about evolution of 4G Networks, its architecture and applications
To study about WiMAX networks, protocol stack and standards
To Study about Spectrum characteristics & Performance evaluation
Course Outcomes:
Acquaint with the latest 3G/4G and WiMAX networks and its architecture.
Illustrate the implications of various layers in Wireless networks.
Able to design and implement wireless network environment for any application using
latest wireless protocols and standards
Analyze the performance of networks.
Exploit various diversity schemes in LTE
UNIT I Introduction 9
Introduction: History of mobile cellular systems, First Generation, Second Generation, Generation
2.5, Overview of 3G & 4G, 3GPP and 3GPP2 standards
UNIT II 3G Networks 9
3G Networks: Evolution from GSM, 3G Services & Applications, UMTS network structure, Core
network, UMTS Radio access, HSPA HSUPA, HSDPA, CDMA 1X , EVDO Rev -0, Rev-A, Rev-B,
Rev-C Architecture, protocol stack.
UNIT III 4G LTE Networks 9
LTE: Introduction, Radio interface architecture, Physical layer, Access procedures, System
Architecture Evolution (SAE), Algorithms for Enhanced Inter-Cell Interference Coordination
UNIT IV WiMAX Networks 9
WiMax: Introduction IEEE 802.16, OFDM, MIMO, IEEE 802.20, Burst Construction Algorithm for
IEEE 802.16
UNIT V Spectrum & Performance 9
Spectrum for LTE-Flexibility-Carrier Aggregation-Multi standard Radio base stations-RF
requirements for LTE-Power level requirements-Emission requirements-Sensitivity and Dynamic
range-Receiver susceptibility. Performance Assessment-Performance Evaluation, Resource
Scheduling scheme for Career aggregation
TOTAL: 45 PERIODS
60
REFERENCE BOOKS:
1. Introduction to 3G Mobile Communication, Juha Korhonen, Artech House,
(www.artechhouse.com), Jan 2003, ISBN-10: 1580535070
2. 4G LTE/LTE Advanced for Mobile Broadband, Erik Dahlman, Stefan Parkvall, Johan Skold,
Academic Press 2011.
3. 3G Evolution HSPA and LTE for Mobile Broadband, Erik Dahlman, Stefan Parkvall, Johan
Skold and Per Beming, Academic Press, Oct 2008, ISBN-10: 0123745381
4. UMTS Mobile Communication for the Future, Flavio Muratore, John Wiley & Sons Ltd, Jan
2001, ISBN-10: 0471498297 HSDPA/HSUPA for UMTS, Harri Holma and Antti Toskala,
Johan Wiley & Sons Ltd, May 2006, ISBN-10: 0470018844
5. Heuristic Burst Construction Algorithm for Improving Downlink Capacity in IEEE 802.16
OFDMA Systems, Joo-Young Baek ; Young-Joo Suh,IEEE Transactions on Mobile
Computing 2012 ,Volume: 11 , Issue: 1.
6. Algorithms for Enhanced Inter-Cell Interference Coordination (eICIC) in LTE HetNets,Deb,
S. ; Wireless Chief Technology Office, Alcatel-Lucent, USA ; Monogioudis, P. ; Miernik, J. ;
Seymour, J.P. , IEEE/ACM Transactions on Networking, (Volume:PP , Issue: 99 ) March
2013
7. A multi-user MIMO resource scheduling scheme for carrier aggregation scenario, Na Lei;
Caili Guo ; Chunyan Feng ; Yu Chen, International Conference on Wireless
Communications and Signal Processing (WCSP), 2011
13MI406 PERVASIVE COMPUTING
L T P C
3 0 0 3
COURSE OBJECTIVES :
To understand the basics of Pervasive Computing
To learn the role of Sensor & Mesh networks in Pervasive Computing
To realize the Scope of Context Aware & Wearable Computing
To Address the Security issues in Pervasive networks
To develop Mobile applications using Programming
COURSE OUTCOMES:
At the end of the course the student should be able to
Exploit the usage of Pervasive Computing in real time applications
Analyze the implications of various layers in Sensor & Mesh networks
Develop Pervasive computing environment using sensor and mesh networks
Develop applications based on the paradigm of context aware computing & wearable
computing
Master the security violations and issues in Pervasive Networks
Design applications using android & iOS
61
UNIT I PERVASIVE COMPUTING AND SYSTEMS 9
Introduction- Tools and Techniques for Dynamic Reconguration and Interoperability of Pervasive
Systems-Models for Service and Resource Discovery-Pervasive Learning Tools and Technologies-
Service Management in Pervasive Computing Environments
UNIT II SENSOR AND MESH NETWORKS 9
Sensor Networks Role in Pervasive Computing In Network Processing and Data Dissemination
Sensor Databases Data Management in Wireless Mobile Environments Wireless Mesh
Networks Architecture Mesh Routers Mesh Clients Routing Cross Layer Approach
Security Aspects of Various Layers in WMN Applications of Sensor and Mesh networks
UNIT III CONTEXT AWARE COMPUTING & WEARABLE COMPUTING 9
Adaptability Mechanisms for Adaptation - Functionality and Data Transcoding Location
Aware Computing Location Representation Localization Techniques Triangulation and Scene
Analysis Delaunay Triangulation and Voronoi graphs Types of Context Role of Mobile
Middleware Adaptation and Agents Service Discovery Middleware
Health BAN- Medical and Technological Requirements-Wearable Sensors-Intra-BAN
communications, Body area network for wireless patient monitoring
UNIT IV PERVASIVE NETWORKING SECURITY 9
Security and Privacy in Pervasive Networks Wormhole attacks in Pervasive Networks- Defense
strategies for Network security Smart Devices, Systems and Intelligent Environments.
Autonomic and Pervasive Networking Adaptive architecture of Service Component Probabilistic
k-Coverage in Pervasive Wireless Sensor Networks-Performance Evaluation of Pervasive Networks
Based on WiMAX Networks-lmplementation Framework for Mobile and Pervasive Frameworks
UNIT V APPLICATION DEVELOPMENT 9
Three tier architecture - Model View Controller Architecture - Memory Management Information
Access Devices PDAs and Smart Phones Smart Cards and Embedded Controls J2ME
Programming for CLDC GUI in MIDP Application Development on Android and iPhone
TOTAL-45 PERIODS
REFERENCES:
1. Asoke K Talukder, Hasan Ahmed, Roopa R Yavagal, Mobile Computing: Technology,
Applications and Service Creation, 2nd ed, Tata McGraw Hill, 2010.
2. Mohammad s. Obaidat et al, Pervasive Computing and Networking, John wiley 2011
3. Reto Meier, Professional Android 2 Application Development, Wrox Wiley,2010.
4. Pei Zheng and Lionel M Li, Smart Phone & Next Generation Mobile Computing, Morgan
Kaufmann Publishers, 2006.
5. Frank Adelstein, Fundamentals of Mobile and Pervasive Computing, TMH, 2005
6. Jochen Burthardt et al, Pervasive Computing: Technology and Architecture of Mobile Internet
Applications, Pearson Education, 2003
7. Feng Zhao and Leonidas Guibas, Wireless Sensor Networks, Morgan Kaufmann Publishers,
2004
8. Reto Meier, Professional Android 2 Application Development, Wrox Wiley,2010.
62
9. Stefan Poslad, Ubiquitous Computing: Smart Devices, Environments and Interactions, Wiley,
2009.
10. Body area network for wireless patient monitoring,Monton, E. ; Hernandez, J.F. ; Blasco, J.M. ;
Herve, T. ; Micallef, J. ; Grech, I. ; Brincat, A. ; Traver, V. IET Communications, Volume: 2 ,
Issue: 2 ,2008
13MI407: MULTIMEDIA TECHNOLOGIES L T P C
3 0 0 3
Course Objectives:
To familiarize with various elements of multimedia
To analyse various multimedia systems
To use various tools for developing multimedia
To develop a multimedia application
Course Outcomes:
Apply MPEG and CD standards in multimedia creation
Use various authoring and editing tools
Develop animation, images, Sound using Multimedia Tools.
Develop a multimedia application
UNIT I INTRODUCTION 7
Introduction to Multimedia Characteristics Utilities Creation -Uses Promotion Digital
Representation Media and Data streams Multimedia Architecture Multimedia Documents
UNIT II ELEMENTS OF MULTIMEDIA 11
Multimedia Building Blocks: Text ,Graphics , Video Capturing, Sound Capturing, and Editing Intro
to 2D & 3D Graphics -surface characteristics and texture - lights Animation: key frames &
Tweening, techniques, principles of animation, 3Danimation, file formats.
UNIT III MULTIMEDIA SYSTEMS 9
Visual Display Systems CRT - video adapter card - video adapter cable LCD PDP - optical
storage media - CD technology - DVD Technology - Compression Types and Techniques CODEC -
GIF coding standards lossy and lossless JPEG - MPEG-1 - MPEG-2 - MP3 - Fractals MMDBS
UNIT IV MULTIMEDIA TOOLS 9
Authoring tools features and types - card and page based tools - icon and object based tools -
time based tools - cross platform authoring tools Editing tools - text editing and word processing
tools - OCR software - painting and drawing tools - 3D modeling and animation tools - image
editing tools sound editing tools - digital movie tools plug -ins and delivery vehicles for www
UNIT V MULTIMEDIA APPLICATION DEVELOPMENT 9
Software life cycle ADDIE Model conceptualization content collection and processing story
flowline script - storyboard - implementation - multiplatform issues authoring Sketch-Based
Annotation and Visualization in Video Authoring - metaphors testing report writing -
documentation - case study: -Web Application Console Application Distributed Application
Mobile Application - games consoles iTV kiosks education
TOTAL: 45PERIODS
63
REFERENCE BOOKS:
1. Parekh R Principles Of Multimedia Tata McGraw-Hill, 2006.
2. Ralf Steinmetz, Klara Nahrstedt, Multimedia: Computing, Communications and Applications
Prentice Hall, 1995.
3. Multimedia ; An Introduction by John Villamil and Louis Molina, Prentice Hall, New Delhi1998.
3. Tay Vaughan, Multimedia: Making It Work McGraw-Hill Professional, 2006
4. Deitel & Deitel Internet & World Wide Web How to Program, Fourth Edition Prentice Hall,
2008.
5. David Pizzi, Jean-Luc Lugrin, Alex Whittaker, and Marc Cavazza ,Automatic Generation of Game
Level Solutions as Storyboards IEEE Transactions on Computational Intelligence and AI in Games,
Vol. 2, No. 3, September 2010
6. Bo-Wei Chen, Jia-Ching Wang, and Jhing-Fa Wang, Fellow, IEEEA Novel Video Summarization
Based on Mining the Story-Structure and Semantic Relations Among Concept Entities IEEE
Transactions on Multimedia, Vol. 11, NO. 2, February 2009
7. Cui-Xia Ma, Yong-Jin Liu, Hong-An Wang, Dong-Xing Teng, and Guo-Zhong Dai Sketch-Based
Annotation and Visualization in Video Authoring IEEE Transactions on Multimedia, Vol. 14, No. 4,
August 2012
13MI408: VIDEO ANALYTICS
(Common to M.E CSE / M.Tech IT)
L T P C
3 0 0 3
Course Objectives:
To know the fundamental concepts of big data and analytics
To learn various techniques for mining data streams
To acquire the knowledge of extracting information from surveillance videos.
To learn Event Modelling for different applications.
To understand the models used for recognition of objects in videos.
Course Outcomes:
1. Work with big data platform and its analysis techniques.
2. Design efficient algorithms for mining the data from large volumes.
3. Work with surveillance videos for analytics.
4. Design optimization algorithms for better analysis and recognition of objects in a scene.
5. Model a framework for Human Activity Recognition.
UNIT I INTRODUCTION TO BIG DATA & DATA ANALYSIS 9
Introduction to Big Data Platform Challenges of Conventional systems Web data- Evolution of
Analytic scalability- analytic processes and tools- Analysis Vs Reporting- Modern data analytic tools-
Data Analysis: Regression Modeling- Bayesian Modeling- Rule induction.
UNIT II MINING DATA STREAMS 9
Introduction to Stream concepts- Stream data model and architecture Stream Computing-
Sampling data in a Stream- Filtering Streams- Counting distinct elements in a Stream- Estimating
64
moments- Counting oneness in a window- Decaying window- Real time Analytics platform(RTAP)
applications- case studies.
UNIT III VIDEO ANALYTICS 9
Introduction- Video Basics - Fundamentals for Video Surveillance- Scene Artifacts- Object Detection
and Tracking: Adaptive Background Modelling and Subtraction- Pedestrian Detection and Tracking-
Vehicle Detection and Tracking- Articulated Human Motion Tracking in Low-Dimensional Latent
Spaces.
UNIT IV BEHAVIOURAL ANALYSIS & ACTIVITY RECOGNITION 9
Event Modelling- Behavioural Analysis- Human Activity Recognition-Complex Activity Recognition-
Activity modelling using 3D shape, Video summarization, shape based activity models- Suspicious
Activity Detection.
UNIT V HUMAN FACE RECOGNITION & GAIT ANALYSIS 9
Introduction: Overview of Recognition algorithms Human Recognition using Face: Face Recognition
from still images, Face Recognition from video, Evaluation of Face Recognition Technologies- Human
Recognition using gait: HMM Framework for Gait Recognition, View Invariant Gait Recognition, Role of
Shape and Dynamics in Gait Recognition - Factorial HMM and Parallel HMM for Gait Recognition- Face
Recognition Performance: Role of Demographic Information.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Michael Berthold, David J.Hand, Intelligent Data Analysis, Springer, 2007.
2. Anand Rajaraman and Jeffrey David Ullman, Mining of Massive Datasets, Cambridge
University Press, 2012.
3. Yunqian Ma, Gang Qian, Intelligent Video Surveillance: Systems and Technology, CRC Press
(Taylor and Francis Group), 2009.
4. Rama Chellappa, Amit K.Roy-Chowdhury, Kevin Zhou.S, Recognition of Humans and their
Activities using Video, Morgan&Claypool Publishers, 2005.
5. YiHuang,DongXu and Tat-Jen Cham, Face and Human Gait Recognition Using Image-to-Class
Distance IEEE Transactions On Circuits And Systems For Video Technology, Vol. 20, No. 3,
March 2010.
6. Changhong Chen, Jimin Liang, Heng Zhao, Haihong Hu, and Jie Tian, Factorial HMM and
Parallel HMM for Gait Recognition, IEEE Transactions On Systems, Man, And Cybernetics
Part C: Applications And Reviews, Vol. 39, No. 1, January 2009.
7. Changhong Chen, Jimin Liang, Haihong Hu, Licheng Jiao, Xin Yang, Factorial Hidden
Markov Models for Gait Recognition, Advances in Biometrics Lecture Notes in Computer
Science Volume 4642, 2007, pp 124-133.
8. Brendan F. Klare, Mark J. Burge, Joshua C. Klontz, Richard W. Vorder Bruegge, and Anil K.
Jain, Face Recognition Performance: Role of Demographic Information IEEE Transactions On
Information Forensics And Security, Vol. 7, No. 6, December 2012.
65
13MI409 : WIRELESS SENSOR NETWORKS
(Common to M.E CSE / M.Tech IT)
L T P C
3 0 0 3
Course Objectives:
To understand the basics of Sensor Networks
To learn various fundamental and emerging protocols of all layers
To study about the issues pertaining to major obstacles in establishment and efficient
management of sensor networks
To understand the nature and applications of sensor networks
To understand various security practices and protocols of Sensor Networks
Course Outcomes:
Analyze various protocols and its issues
Implement various routing protocols for Sensor networks
Use various security techniques in WSN
Create a Sensor network environment for different type of applications.
UNIT I SENSOR NETWORKS FUNDAMENTALS AND ARCHITECTURE 9
Introduction and Overview of WSNs, Application of WSNs, Challenges for Wireless Sensor
Networks, Enabling Technologies For Wireless Sensor Networks. Node Architecture- Sensing
Subsystem, Processing Subsystem, Communication Interfaces - Prototypes.
UNIT II Networking Sensors 9
Fundamentals of (Wireless) MAC Protocols, Low duty cycle protocols and wakeup concepts ,
Contention based Protocols Naming and Addressing- Fundamentals, Address and Name
Management in WSN, Assignment of MAC Addresses-Content based and geographic addressing
UNIT III SENSOR NETWORK MANAGEMENT AND PROGRAMMING 9
Sensor Management - Topology Control Protocols and Sensing Mode Selection Protocols - Time
Synchronization-Sender/sender synchronization, Sender/receiver synchronization - Localization
and Positioning Operating Systems and Sensor Network Programming Sensor Network
Simulators - A Lightweight and Energy-Efficient Architecture for WSNs
UNIT IV SENSOR NETWORK DATABASES, PLATFORMS AND TOOLS 9
Sensor Database Challenges, Querying- Aggregation. Sensor Node Hardware Berkeley Motes,
Programming Challenges, Node-level software platforms, Node-level Simulators, State-centric
programming.
UNIT V SENSOR NETWORK SECURITY 9
Security in Sensor Networks Challenges of Security in WSNs-Security Attacks in sensor
networks- Detecting and Localizing Identity-Based Attacks in WSN, Protocols and Mechanisms for
security-Symmetric and Public keyCryptograpy, Key Management-Low-Energy Symmetric Key
Distribution in Wireless Sensor Networks, Defenses against attacks, Secure Protocols,TinySec,
SPINS ,Localized Encryption and Authentication Protocol,IEEE 802.15.4 and Zigbee security
TOTAL: 45 PERIODS
66
REFERENCE BOOKS:
1. Kazem Sohraby, Daniel Minoli,Taieb Znati Wireless Sensor Networks: Technology, Protocols,
and Applications John Wiley & Sons, Inc .2007
2. Holger Karl, Andreas willig, Protocols and Architectures for Wireless Sensor Networks, John
Wiley & Sons, Inc .2005.
3. Erdal ayrc , Chunming Rong, Security in Wireless Ad Hoc and Sensor Networks, John Wiley
and Sons, 2009
4. Waltenegus Dargie, Christian Poellabauer, Fundamentals of Wireless Sensor Networks Theory
and Practice, John Wiley and Sons, 2010
5. Miguel A. Lopez-Gomez, Member, IEEE, and Juan C. Tejero-Calado, Nonmember A
Lightweight and Energy-Efficient Architecture for Wireless Sensor Networks IEEE Transactions
on Consumer Electronics, Vol. 55, No. 3, AUGUST 2009
6. Yingying Chen, Member, IEEE, Jie Yang, Student Member, IEEE, Wade Trappe, Member, IEEE,
and Richard P. Martin, Member, IEEE Detecting and Localizing Identity-Based Attacks in
Wireless and Sensor Networks , IEEE transactions on vehicular technology, Vol. 59, No.
5,June 2010
7. Kealan McCusker, Member, IEEE, and Noel E. OConnor, Member, IEEE ,Low-Energy
Symmetric Key Distribution in Wireless Sensor Networks , IEEE Transactions On Dependable
and Secure Computing, Vol. 8, No. 3, May/June 2011
13MI410: IMAGE PROCESSING AND PATTERN ANALYSIS
L T P C
3 0 0 3
Course Objectives:
To introduce the student to various Image processing and Pattern recognition techniques.
To study the Image fundamentals.
To study the mathematical morphology necessary for Image processing and Image
segmentation.
To study the Image Representation and description and feature extraction.
To study the principles of Pattern Recognition.
To know the various applications of Image processing.
Course Outcomes:
Enhance the image for better appearance
Segment the image using different techniques
Represent the images in different forms
Develop algorithms for Pattern Recognition
Extract and deploy the features in various Image processing applications
UNIT I INTRODUCTION 9
Elements of an Image Processing System- Mathematical Preliminaries- Image Enhancement-Grayscale
Transformation- Piecewise Linear Transformation-Bit Plane Slicing- Histogram Equalization--Histogram
Specification- Enhancement by Arithmetic Operations- Smoothing Filter- Sharpening Filter- Image Blur
Types and Quality Measures.
UNIT II MATHEMATICAL MORPHOLOGY and IMAGE SEGMENTATION 9
Binary Morphology-Opening and Closing- Hit-or-Miss Transform- Grayscale Morphology- Basic
67
morphological Algorithms- Morphological Filters-Thresholding-Object (Component) Labeling-
Locating Object Contours by the Snake Model- Edge Operators-Edge Linking by Adaptive
Mathematical morphology- Automatic Seeded Region Growing- A Top-Down Region Dividing
Approach.
UNIT III IMAGE REPRESENTATION AND DESCRIPTION and FEATURE
EXTRACTION
9
Run-Length Coding- Binary Tree and Quadtree- Contour Representation-Skeletonization by
Thinning- Medial Axis Transformation-Object Representation and Tolerance- Fourier Descriptor and
Moment Invariants-Shape Number and Hierarchical Features-Corner Detection- Hough Transform-
Principal Component Analysis-Linear Discriminate Analysis- Feature Reduction in Input and Feature
Spaces.
UNIT IV PATTERN RECOGNITION 9
The Unsupervised Clustering Algorithm-Bayes Classifier- Support Vector Machine- Neural
Networks-The Adaptive Resonance Theory Network-Fuzzy Sets in Image Analysis-Document image
processing and classification-Block Segmentation and Classification- Rule-Based Character
Recognition system- Logo Identification-Fuzzy Typographical Analysis for Character Pre
classification-Fuzzy Model for Character Classification.
UNIT V APPLICATIONS 9
Face and Facial Feature Extraction-Extraction of Head and Face Boundaries and Facial Features-
Recognizing Facial Action Units-Facial Expression Recognition in JAFFE Database-Image
Steganography- Types of Steganography- Applications of Steganography- Embedding Security and
Imperceptibility- Examples of Steganography Software-Genetic Algorithm Based Steganography-
Robust Face Recognition for Uncontrolled Pose and Illumination Changes.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Image Processing and Pattern Recognition: Fundamentals and Techniques- Frank Y Shih,
Willey IEEE Press, April 2010
2. Rafael C. Gonzalez, Richard E. Woods, Steven Eddins, Digital Image Processing using
MATLAB, Pearson Education, Inc., 2004.
3. D.E. Dudgeon and R.M. Mersereau, Multidimensional Digital Signal Processing, Prentice
Hall Professional Technical Reference, 1990.
4. William K. Pratt, Digital Image Processing, John Wiley, New York, 2002.
5. Milan Sonka et al, Image Processing, Analysis and Machine Vision, Brookes/Cole, Vikas
Publishing House, 2nd edition, 1999;
6. Sid Ahmed, M.A., Image Processing Theory, Algorithms and Architectures, McGrawHill,
1995
7. Maria De Marsico, Michele Nappi, Daniel Riccio, and Harry Wechsler Robust Face
Recognition for Uncontrolled Pose and Illumination Changes IEEE transactions on
Systems, Man, and Cybernetics: Systems, Vol. 43, no. 1, January 2013
You might also like
- Interfacing PIC Microcontrollers: Embedded Design by Interactive SimulationFrom EverandInterfacing PIC Microcontrollers: Embedded Design by Interactive SimulationNo ratings yet
- Mca2013 PDFDocument61 pagesMca2013 PDFselvam_mca100% (1)
- M.E. Software Engineering SyallabusDocument34 pagesM.E. Software Engineering SyallabusDarwin V TomyNo ratings yet
- Anna University, Chennai Affiliated Institutions: Semester IiDocument17 pagesAnna University, Chennai Affiliated Institutions: Semester Iianitha_eswaranNo ratings yet
- Es R19Document41 pagesEs R19Sundar ShodavaramNo ratings yet
- University Updates Semester Course SchedulesDocument11 pagesUniversity Updates Semester Course SchedulesAlphones DamonNo ratings yet
- Programme Outcomes (Pos) Po1: Po2: Po3:: Gandipet, Hyderabad - 500 075Document33 pagesProgramme Outcomes (Pos) Po1: Po2: Po3:: Gandipet, Hyderabad - 500 075lokeshjoelNo ratings yet
- Regulations - 2008Document82 pagesRegulations - 2008BubbyOshinNo ratings yet
- Master of Computer Applications Curriculum and SyllabiDocument73 pagesMaster of Computer Applications Curriculum and SyllabiStanly JonesNo ratings yet
- Vssut MCA-2yr-SyllabusDocument106 pagesVssut MCA-2yr-Syllabusbiswajit biswalNo ratings yet
- M.E.embedded System TechnologiesDocument32 pagesM.E.embedded System TechnologiesSri RamNo ratings yet
- MCA 2013 Regulation SubjectsDocument61 pagesMCA 2013 Regulation SubjectsJami BurnettNo ratings yet
- M.E. Embedded System TechnologiesDocument31 pagesM.E. Embedded System TechnologiespradeepreddygNo ratings yet
- SYLLABUSDocument108 pagesSYLLABUSrharshad93No ratings yet
- 58.CSE_1.1.3.Document45 pages58.CSE_1.1.3.sirishaksnlpNo ratings yet
- M Tech DSCE R15 SyllabusDocument41 pagesM Tech DSCE R15 SyllabusNikhil KumarNo ratings yet
- M.E. (Embedded System Technologies)Document37 pagesM.E. (Embedded System Technologies)Priya DarshiniNo ratings yet
- Anna University, Chennai Affiliated Institutions Regulations - 2013 Curriculum and Syllabus I To Vi Semesters (Full Time) Master of Computer Application Programme Educational ObjectivesDocument61 pagesAnna University, Chennai Affiliated Institutions Regulations - 2013 Curriculum and Syllabus I To Vi Semesters (Full Time) Master of Computer Application Programme Educational ObjectiveskksNo ratings yet
- Emb Sys TecDocument39 pagesEmb Sys TecYuvaperiyasamy MayilsamyNo ratings yet
- MCA ChennaiDocument50 pagesMCA ChennaicsisajurajNo ratings yet
- Embedded System TechnologiesDocument37 pagesEmbedded System TechnologiesjayaprahasNo ratings yet
- R18 B.Tech ECE III Year Course Structure and SyllabusDocument36 pagesR18 B.Tech ECE III Year Course Structure and SyllabusShivNo ratings yet
- ITSylabus 2004Document38 pagesITSylabus 2004api-3748394100% (2)
- Computer & Communication CourseDocument36 pagesComputer & Communication CourseanuragkrNo ratings yet
- M. SC - IT - 5 YrDocument67 pagesM. SC - IT - 5 YrMouli JeeNo ratings yet
- Autonomous Academic UG Civil UG Curriculum and SyllabusDocument209 pagesAutonomous Academic UG Civil UG Curriculum and SyllabusGaurav PawarNo ratings yet
- R18 B.TECH CSE II Year Syllabus PDFDocument33 pagesR18 B.TECH CSE II Year Syllabus PDFHemima RachelNo ratings yet
- CSE Anna University Chennai SyllabusDocument108 pagesCSE Anna University Chennai SyllabusAnu SelviNo ratings yet
- 3-2 ECE R16 Syllabus PDFDocument22 pages3-2 ECE R16 Syllabus PDFmushahedNo ratings yet
- M.Tech. (Full Time) - Robotics Curriculum & Syllabus 2015 – 2016Document54 pagesM.Tech. (Full Time) - Robotics Curriculum & Syllabus 2015 – 2016Vignesh SaminathanNo ratings yet
- SyllabusDocument80 pagesSyllabusAlbert John VargheseNo ratings yet
- M.E Cse PDFDocument51 pagesM.E Cse PDFLatha MugunthanNo ratings yet
- Final Datesheet Course Wise - 13 - MarchDocument67 pagesFinal Datesheet Course Wise - 13 - MarchRam KushwahNo ratings yet
- Final Updated New Syllabus MCA BPUT 2008-10Document16 pagesFinal Updated New Syllabus MCA BPUT 2008-10dilipbiswakarmaNo ratings yet
- UG 3-2 R19 CSE SyllabusDocument16 pagesUG 3-2 R19 CSE SyllabusSravaniNo ratings yet
- TE Computer 2019 Course Revised Draft 7june2021Document104 pagesTE Computer 2019 Course Revised Draft 7june2021sun foruNo ratings yet
- DNT-7th & 8th ALLDocument31 pagesDNT-7th & 8th ALLMd. Abdur RoufNo ratings yet
- JNTUK MCA R19 SyllabusDocument87 pagesJNTUK MCA R19 SyllabusHidayathulla SkNo ratings yet
- Catalog ICTDocument4 pagesCatalog ICTkhaamohNo ratings yet
- TE Computer Engg 2019 Course Syllabus Draft 23may2021Document100 pagesTE Computer Engg 2019 Course Syllabus Draft 23may2021Mayur SarodeNo ratings yet
- R18 B.Tech It Iii YearDocument61 pagesR18 B.Tech It Iii YearheelobgeNo ratings yet
- CSEDocument35 pagesCSEsai creativesNo ratings yet
- BEC Curriculum Syllabus 2017-18 2018-19 24-06-2020 NewDocument169 pagesBEC Curriculum Syllabus 2017-18 2018-19 24-06-2020 NewswethaNo ratings yet
- Software For Embedded SystemDocument39 pagesSoftware For Embedded Systemjani28cseNo ratings yet
- M.E. Computer Science and Engineering Curriculum and SyllabusDocument58 pagesM.E. Computer Science and Engineering Curriculum and SyllabuspajadhavNo ratings yet
- UG 4-1 R19 CSE SyllabusDocument33 pagesUG 4-1 R19 CSE SyllabusBrahmaiah ThanniruNo ratings yet
- R19 Cse (Iot)Document368 pagesR19 Cse (Iot)pushpa lathaNo ratings yet
- A Comprehensive Guide to 5G SecurityFrom EverandA Comprehensive Guide to 5G SecurityMadhusanka LiyanageNo ratings yet
- Enterprise Interoperability: Smart Services and Business Impact of Enterprise InteroperabilityFrom EverandEnterprise Interoperability: Smart Services and Business Impact of Enterprise InteroperabilityMartin ZelmNo ratings yet
- Introduction to Quantum Computing & Machine Learning Technologies: 1, #1From EverandIntroduction to Quantum Computing & Machine Learning Technologies: 1, #1No ratings yet
- ESP32 Programming for the Internet of Things: JavaScript, AJAX, MQTT and WebSockets SolutionsFrom EverandESP32 Programming for the Internet of Things: JavaScript, AJAX, MQTT and WebSockets SolutionsRating: 5 out of 5 stars5/5 (2)
- Material-Integrated Intelligent Systems: Technology and ApplicationsFrom EverandMaterial-Integrated Intelligent Systems: Technology and ApplicationsStefan BosseNo ratings yet
- Industrial Sensors and Controls in Communication Networks: From Wired Technologies to Cloud Computing and the Internet of ThingsFrom EverandIndustrial Sensors and Controls in Communication Networks: From Wired Technologies to Cloud Computing and the Internet of ThingsNo ratings yet
- Designing Embedded Systems with PIC Microcontrollers: Principles and ApplicationsFrom EverandDesigning Embedded Systems with PIC Microcontrollers: Principles and ApplicationsRating: 2 out of 5 stars2/5 (1)
- Cyber Security in Parallel and Distributed Computing: Concepts, Techniques, Applications and Case StudiesFrom EverandCyber Security in Parallel and Distributed Computing: Concepts, Techniques, Applications and Case StudiesNo ratings yet
- The Fifth Generation Computer Project: State of the Art Report 11:1From EverandThe Fifth Generation Computer Project: State of the Art Report 11:1Rating: 5 out of 5 stars5/5 (1)
- Nanoelectronics: Materials, Devices, Applications, 2 VolumesFrom EverandNanoelectronics: Materials, Devices, Applications, 2 VolumesRobert PuersNo ratings yet
- Force Restore On Windows Media ServerDocument2 pagesForce Restore On Windows Media ServerAbhishek PondicherryNo ratings yet
- ASTRA DatasheetDocument4 pagesASTRA DatasheetJohn E. MosqueraNo ratings yet
- Operating Systems Lecture Notes-2Document15 pagesOperating Systems Lecture Notes-2Arun SasidharanNo ratings yet
- 27030422-ACOMT2A04 DatasheetDocument3 pages27030422-ACOMT2A04 DatasheetJorge VieiraNo ratings yet
- TestYantra CapabilitiesDocument27 pagesTestYantra CapabilitiesChris Majestic IT ServicesNo ratings yet
- Embedded Systems Road MapDocument9 pagesEmbedded Systems Road MapbajehagNo ratings yet
- Code - MSG Pervasiv PDFDocument252 pagesCode - MSG Pervasiv PDFdarkopuNo ratings yet
- Hart Chapter 9 SolutionsDocument23 pagesHart Chapter 9 SolutionsCassio SchefferNo ratings yet
- Disaster Recovery For SAP HANADocument2 pagesDisaster Recovery For SAP HANAHasan ShahriarNo ratings yet
- SSD For AnsysDocument32 pagesSSD For AnsysludovicgenoletNo ratings yet
- HDD-SSD Compatible List Stardom 20151119Document1 pageHDD-SSD Compatible List Stardom 20151119Vincent FollézouNo ratings yet
- Transport Layer: Computer Networking: A Top Down ApproachDocument111 pagesTransport Layer: Computer Networking: A Top Down ApproachShanta PhaniNo ratings yet
- Ecall Vs NG EcallDocument6 pagesEcall Vs NG EcallTrần Văn DũngNo ratings yet
- VLSI Routing InformationDocument23 pagesVLSI Routing InformationSwathi KambleNo ratings yet
- Angel StoyanovDocument4 pagesAngel StoyanovmikeshiiNo ratings yet
- Iphone Se 820-00282 SchematicDocument60 pagesIphone Se 820-00282 SchematicHec MercadoNo ratings yet
- Using The Circuitmaster 4000M Precision Active Oscilloscope For Circuit AnalysisDocument8 pagesUsing The Circuitmaster 4000M Precision Active Oscilloscope For Circuit AnalysisAnonymous LJTck8PNo ratings yet
- Mini Hi-Fi System Service ManualDocument95 pagesMini Hi-Fi System Service ManualyoyneerNo ratings yet
- Api MetaDocument416 pagesApi MetaBhaskar Kumar UppuluriNo ratings yet
- Service Manual: Model: MIX260FXDocument34 pagesService Manual: Model: MIX260FXericNo ratings yet
- Computer Basics ElementsDocument413 pagesComputer Basics ElementsFaquir Sanoar SanyNo ratings yet
- Power Quality Detection Using FACTSDocument4 pagesPower Quality Detection Using FACTSSaravanan T YNo ratings yet
- React Redux Saga Example App. - Ron LavitDocument8 pagesReact Redux Saga Example App. - Ron LavitCristhian CruzNo ratings yet
- NShield Hardware InstallationDocument60 pagesNShield Hardware InstallationARMAGEDDON87No ratings yet
- I2c Driver ArchitectureDocument12 pagesI2c Driver ArchitectureAkhilesh ChaudhryNo ratings yet
- Pinball Cabinet BulidDocument41 pagesPinball Cabinet Bulidbocadillodebordillo100% (2)
- Extreme Routing Student Guide v2.0 (Ebook)Document319 pagesExtreme Routing Student Guide v2.0 (Ebook)Hrvoje SilovNo ratings yet
- Lesson6 Storage HDD FDD CDDocument40 pagesLesson6 Storage HDD FDD CDLorraine I. JameroNo ratings yet
- Kontakt 2 English ManualDocument213 pagesKontakt 2 English Manualalq10No ratings yet
- Cobos V3.0 QuickstartDocument42 pagesCobos V3.0 QuickstartWellington MarquesNo ratings yet