Professional Documents
Culture Documents
Rotational Attack of PSNR Value Using SVD-DCT On Digital Image Watermarking
Uploaded by
seventhsensegroupOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Rotational Attack of PSNR Value Using SVD-DCT On Digital Image Watermarking
Uploaded by
seventhsensegroupCopyright:
Available Formats
International Journal of Computer Trends and Technology (IJCTT) volume 4 Issue 9 Sep 2013
ISSN: 2231-2803 http://www.ijcttjournal.org Page 2986
Rotational Attack Of Psnr Value Using SvdDct
On Digital Image Watermarking
Vikas Chaubey
#1
,Chetan Kumar
#2
, Prashant Kumar
#3
#1MTech. Scholar, Dept of Computer Science & Engineering, kautilya institute of technology,jaipur,rajasthan,india
#2 Associate Professor, Dept of Computer Science & Engineering, kautilya institute of technology,jaipur,rajasthan,india
#3Assistant Professor, Dept of Computer Science & Engineering, MVN University, Palwal, Haryana, India
Abstract: Various signals have a very extensive dynamic
range, peak signal noise ratio is generally communicated in
relations of the logarithmic decibel scale. Every geometric
attack is defined by a set of parameters that determines the
operation performed over the target image. The Discrete
Cosine Transformation coefficients are modified to embed the
watermark data. Because of the conflict between robustness
and transparency, the modification is usually made in middle
frequencies, avoiding the lowest and highest bands. Singular
Value Decomposition-based watermarking is that the largest
of the modified singular values change very little for most
types of attacks.
Keywords:- Watermarking, Peak Signal Noise Ratio,
Discrete Cosine Transform, Singular Value Decomposition,
Attack.
I .INTRODUCTION
Now a day quick-tempered progression of the Internet
or Network not only needed new possibilities but also
publicly presented appearance to information manage
databases around the world, circulated project work across
different countries, or fast and consistent means of
electronic communication - emerged, but the comfort with
which digital media can be reproduced and modified, or the
point that regulation is seemingly unable to cope with its
rapid level of modification makes it also very noticeable to
people with dis-honorable motives. With these drawbacks
of the digital age in mind, creators of multimedia content
may wish for a digital analogy to the watermarks that have
been used in bookmaking since the 13th Century.
This type of attitudes and tools to protect ones
intellectual property rights started the reasonably new
research field of digital watermarks. Someone familiar
with encryption techniques might be tempted to ask why
there is such an quantity of apprehension in the research
civic to grow robust watermarking techniques, if numerous
secure encryption systems are freely available because
encryption on your own frequently is insufficient to guard
digital content, since unthinking and erroneous usage by
human hands often decreases it useless.
1.1Spread Spectrum Watermarking:
Several of the current watermarking techniques addition
one bit of information over many pixels or transform
factors and use classical detection systems to recover the
watermarking information. These types of watermarking
techniques are usually mentioned to as spread-spectrum
approaches, due to their similarity to spread-spectrum
communication systems. When used in digital image
watermarking, this translates to inserting the watermarking
bits at more than one location in the image [5]. Thus, even
if subsequent image operations may remove the watermark
in some parts of the image, it is very likely that the
embedded copyright is still detectable.
1.2Embedding:
The starting step is to assign +1 and -1 to the
watermarking bits 1 and 0 respectively. The resultant bit
streamis then settled either in columns, rows or tiles across
the whole image (Fig 1, key2: logical 1: black areas,
logical 0: white areas; every tile relates to one bit in the
watermark). To get done the band spread, key2 is then
multiplied by the output of a pseudo-noise generator like a
linear feedback shift register (LFSR) or other random
generators. Lastly, the values of the watermark are adjusted
by multiplying them with a rescaling factor and
additional to the original image in a pixel wise manner. The
rescale factor determines the strong point with which the
watermark is embedded (usually depending on the
characteristics of different portions of the image, e.g. some
parts of the image might allow for a rescale factor of 5 or
more, while others undergo a visible degradation in image
quality even if the rescale cause is reduced to 1)
addition
Rescale
factor
Original image
Watermarked image
Watermark key2
Watermark pass key1
watermark
Modulatio
n
International Journal of Computer Trends and Technology (IJCTT) volume 4 Issue 9 Sep 2013
ISSN: 2231-2803 http://www.ijcttjournal.org Page 2987
Fig:1
1.3 Detection:
The recognizable problemin the watermark detection
step is how to recover the embedded watermark froma
(possibly) watermarked image. There are several methods
to this problem:
Private or non-blind watermarking: The embedded
watermark is recovered by deducting the original image.
Semi-blind watermarking: The finder requires access to
the published or unchanged watermarked image.
Public or blind watermarking: The embedded
watermark can be identified without the original image.
The described watermark is an example for a public or
blind watermarking scheme, because the embedded
copyright can be retrieved without the original image by
taking advantage. Since the watermark is added as a
pseudo-noise sequence having a high spatial frequency, it
can be recovered by applying a high-pass filter such as the
following complication mask:
High-pass filter
To calculate the filtered image, the convolution mask is
shifted over the whole image. In every step the pixel below
the -8 is replaced by the
inner product of the
convol
ution
mask
and
the
underl
ying
pixel values. The resulting image
is then multiplied by password-
dependent pseudo-noise sequence key1 to get the
correlation image. After summing the values of the
correlation image for every copyright bit, the actual bit
values (key2) are finally recovered using the following
formula (see Fig 2):
Output Bit (corrSquare[i][j]) =
{ 0avg (corrSquare [i][j] =-detection threshold }
{ 1avg (corrSquare [i][j] =+detection threshold }
Detection failed else
Fig:2 (HF-High pass Filter, DM-Demodulation)
II. DCT-SVD DIGITAL IMAGE WATERMARKING
The process of separating the image into bands using
the Discrete Wavelet Transformation is well-defined. In
two-dimensional Discrete Wavelet Transformation, each
level of decomposition produces four bands of data denoted
by LL, HL, LH, and HH. The LL sub-band can further be
decomposed to obtain another level of decomposition. In
two-dimensional Discrete Cosine Transformation, we apply
the transformation to the whole image but need to map the
frequency coefficients fromthe lowest to the highest in a
zig-zag order to 4 quadrants in order to apply SVD to each
block. All the quadrants will have the same number of
DCT coefficients. For example, if the cover image is
256x256, the number of DCT coefficients[8] in each block
will be 65,536. To differentiate these blocks fromthe DCT
bands, we will label themB1, B2, B3, B4. This process is
depicted in Fig shown below.
Fig: 3
In pure DCT-based watermarking, the DCT coefficients
are modified to embed the watermark data. Because of the
conflict between robustness and transparency [2], the
modification is usually made in middle frequencies,
avoiding the lowest and highest bands. In SVD-based
watermarking, several approaches are possible. A common
approach is to apply SVD to the whole cover image, and
modify all the singular values to embed the watermark
data. An important property of SVD-based watermarking is
B1
B2
B3
B4
Pseudo noise sequence
Watermarked Image
H
F
Pseudo noise
Watermark password key1
D
M
Correlation
image
Summation
Recovered
watermark
bit key2
International Journal of Computer Trends and Technology (IJCTT) volume 4 Issue 9 Sep 2013
ISSN: 2231-2803 http://www.ijcttjournal.org Page 2988
that the largest of the modified singular values change very
little for most types of attacks. We will combine DCT and
SVD to develop a new hybrid non-blind image
watermarking scheme [8] that is resistant to a variety of
attacks. The proposed scheme is given by the following
algorithm. Assume the size of visual watermark is nxn, and
the size of the cover image is 2nx2n.
2.1 Watermark Embedding:
1. Apply the Discrete Cosine Transformation to the
whole cover image A.
2. Using the zig-zag sequence, map the Discrete Cosine
Transformation quantities into 4 quadrants: B1, B2, B3,
and B4.
3. Apply Singular Value Decomposition to every
quadrant: A
k
=u
A
k
A
k
I
A
k1
, k =1,2,3,4, where k denotes
B1,B2,B3 and B4
4. Apply Discrete Cosine Transformation to the whole
visual watermark W.
5. Apply Singular Value Decomposition to the Discrete
Cosine Transformation-transformed visual watermark W:
w =u
w
w
I
w
1
.
6. Modify the singular values in each quadrant B
k
, k =
1,2,3,4, with the singular values of the Discrete Cosine
Transformation-transformed visual watermark:
z
k
=z
k
+o
k
z
w
i =1n where z
k
i =
1n are the singular values of
A
k
, andz
w
i =1n
are the singular values of
v
.
7. Obtain the 4 sets of modified DCT coefficients:
A
k
=u
A
k
X
A
k
I
A
k1
, k =1,2,3,4.
8. Map the modified Discrete Cosine Transformation
coefficients back to their original positions.
9. Apply the inverse Discrete Cosine Transformation to
produce the watermarked cover image.
2.2 Watermark Extraction:
1. Apply the Discrete Cosine Transformations to the
whole watermarked (and possibly attacked) cover image
A
.
2. Using the zig-zag sequence, map the Discrete Cosine
Transformations coefficients into 4 quadrants: B1, B2, B3,
and B4.
3. Apply Singular Value decomposition to each
quadrant: A
k
=u
A
k
X
A
k
I
A
k1
, k =1,2,3,4. where k denotes
the attacked quadrants.
4. Extract the singular values from each
quadrant Bk,k =1,2,3,4: z
w
k
=
x
i
k
-x
i
k
u
k
,i =1,..n
5. Construct the Discrete Cosine Transformation
coefficients of the four visual watermarks using the
singular vectors:
w
k
=u
w
k
w
k
I
w
k
,k =1,2,3,4.
6. Apply the inverse Discrete Cosine Transformation to
each set to construct the four visual watermarks
The Discrete Cosine Transformation factors with the
highest magnitudes [1] are found in quadrant B1, and those
with the lowest magnitudes are found in quadrant B4.
Correspondingly, the singular values with the highest
values are in quadrant B1, and the singular values with the
lowest values are in quadrant B4.
The largest singular values in quadrants B2, B3, and B4
have the same order of magnitude. So, instead of assigning
a different scaling factor for each quadrant, we used only
two values: One value for B1, and a smaller value for the
other three quadrants.
III. GEOMETRICAL ACTION
Let us now discuss the geometrical operation used in
image processing. There are various ways to classify image
operations. The reason for categorizing the operation is to
gain an insight into the nature of the operations, the
expected results and the kind of computational liability.
3.1 Translation:
Translation is the movement of an image to a new
position. Let us assume that the point at the coordinate
position X=(x, y) of the matrix F is motivated to the new
position X whose coordinate location is(x, y).
Mathematically, this can be stated as a translation of point
X to new position X. The translation is represented as
x= x + x
y= y + y.
3.2 Scaling:
Depending on the requirement, the object can be scaled.
Scaling means expanding and shrinking. In the similar
coordinate system, the scaling of the point(x, y) to the new
point(x, y) of the image F is designated as
x=x * Sx
y=y * Sy.
3.3 Zooming:
This image can be Zoomed using a process called pixel
replication of interpolation [6]. Replication is called a zero-
order hold process, where each pixel along the scan line is
repetitive once. Then the scan line repeated. The aim is to
increase the number of pixels, thereby increasing the
dimension of the image.
3.4 Rotation:
This has been the true battle horse of digital
watermarking, especially because of its success with still
images. Correlation based detection and extraction fail
when rotations are performed on the watermarked image
because the embedded watermark and the locally generated
form do not share the same spatial pattern anymore.
Obviously, it would be possible to do exhaustive search
on different rotation angles factors until a correlation peak
International Journal of Computer Trends and Technology (IJCTT) volume 4 Issue 9 Sep 2013
ISSN: 2231-2803 http://www.ijcttjournal.org Page 2989
is found, but this is prohibitively complex. The two
parameters become simple when the original image is
present, but we have augmented against this possibility in
previous sections[5]. Some authors have recently proposed
the use of rotation transforms (such as the Fourier-Mellin
[4]) but this dramatically decreases the capacity for
message hiding.
IV. RESULT AND DISCUSSION OF ROTATIONAL
ATTACK:
Correlation based detection and extraction fail when
rotation or scaling are performed on the watermarked
image because the embedded watermark and the locally
generated version do not share the same spatial pattern
anymore.
The above figure shows the rotated watermarked image
by 2 degree in counter clockwise direction .The rotating
attack is done at step size of 15.
Normalized cross correlation coefficient calculation in
case of rotating attack on watermarked image:
Rotating attack is performed on watermarked image by
rotating the watermarked image to 2 degree in
anticlockwise direction. The similarity between the
watermarked image and attacked watermarked image is
found by calculating the correlation over entire dimension
of the attacked image. The same procedure is applied as
above.
Taking x =x +(w * W_h_r)
y =y +(w * w)
P =(x/y)
Where x =0; initially
y =0; initially
P =correlation coefficient
w =original watermark
W_h_r = watermark extracted from
rotated image
The value of correlation coefficient found in this case is
extraction is done P1 =0.6781and P2=0.6799 for step size
of 15 and PSNR value=13.5805. The correlation value is
less which shows that the watermarking scheme is not
more robust for rotating attack also.
PSNR- Peak Signal Noise Ratio.
Fig 5 : Rotational back(2 degree rotation)
The above figure shows the rotated back watermarked
image. The rotating attack is done at step size of 15.The
value of correlation coefficient found in this case of
rotational back after extraction is done P1 =0.6378and
P2=0.7044 for step size of 15 and PSNR value=11.9180.
V. CONCLUSION
In my paper I have applied rotation attacks domain
Digital Watermarking. As wavelet has hierarchical nature
so its multi resolution analysis helps to surround the
watermark in n no. of levels. Watermark Encryption before
embedding gives added security to the algorithmand hence
chaotic scrambling has proved to be a deserved answer to
it. Embedding Watermark in Integer Wavelet Domain
assures more reversibility of data than any other domain.
As it maps integers to integers so adding binary watermark
to Integer Wavelet Transformation decomposed image
comes in good compatibility. We have seen that increasing
the step size increases the depth of watermark embedding
and so its energy to withstand regular signal processing
attacks.
VI. FUTURE WORK
I have implemented a watermarking scheme to embed
the watermark. If due to any region possible a dither and
wiener attack on your digital image water marking. Find
the peak signal noise ratio value after the attack of
extraction done. Also recover fromwatermarking attack by
the using of Singular Value Decomposition and Discrete
Cosine Transformation algorithm. In my work the
procedure I used in embedding watermark in second level
found to be very less robust to most of the common signal
processing attacks , as against when used in single gave
appreciable results. The causes could be so many from
chosen wavelet to block size selection. A good research in
this regard may chief to a very nice and effective
methodology to the area of Digital Watermarking.
Fig-4 : Rotational attack(-2 degree rotation)
International Journal of Computer Trends and Technology (IJCTT) volume 4 Issue 9 Sep 2013
ISSN: 2231-2803 http://www.ijcttjournal.org Page 2990
REFERENCES
[1] Chih-Chin Lai, Member, IEEE, and Cheng-Chih Tsai Digital Image
Watermarking Using Discrete Wavelet Transform and Singular Value
Decomposition IEEE Transactions on Instrumentation and Measurement,
VOL. 59, NO. 11, NOVEMBER 2010.
[2] K. Bhagyashri and J oshi M.Y.,Robust Image Watermarking based on
Singular Value Decomposition and Discrete Wavelet Transform,
Nanded 2010 IEEE.
[3]- F. Petitcolas, R. Anderson, and M. Kuhn,Attacks on copyright
marking systems, in Information Hiding (D. Aucsmith, ed.), vol. 1525 of
Lecture Notes in Computer Science, (Berlin), pp. 218238, Springer-
Verlag, 1998.
[4]- A. Herrigel, J. ORuanaidh, H. Petersen, S. Pererira, and T. Pun,
Secure copyright protection techniques for digital images, in
Information Hiding (D. Aucsmith, ed.), vol. 1525 of Lecture Notes in
Computer Science, (Berlin), pp. 169190, Springer- Verlag, 1998.
[5]- Digital Watermarking.pdf Michael Stumpfl Dept. of Electronics and
Computer Science University of Southampton e-mail:
ms601@soton.ac.uk.
[6]- J . R. Hernandez, F. Perez-Gonzalez, and J. M. Rodrguez, Coding
and synchronization: A boost and a bottleneck for the development of
image watermarking, in Proc. of the COST #254 workshop on Intelligent
Communications, (LAquila, Italia), pp. 7782, SSGRR, J une 1998.
[7] K. Bhagyashri and J oshi M.Y.,Robust Image Watermarking based on
Singular Value Decomposition and Discrete Wavelet Transform,
Nanded 2010 IEEE.
[8]- Robust DCT-SVD Domain Image Watermarking for Copyright
Protection: embedding data in all frequencies Alexander Sverdlov, Scott
Dexter, Ahmet M. Eskicioglu.
You might also like
- Fabrication of High Speed Indication and Automatic Pneumatic Braking SystemDocument7 pagesFabrication of High Speed Indication and Automatic Pneumatic Braking Systemseventhsensegroup0% (1)
- Implementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationDocument6 pagesImplementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationseventhsensegroupNo ratings yet
- Design, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)Document7 pagesDesign, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)seventhsensegroupNo ratings yet
- Ijett V5N1P103Document4 pagesIjett V5N1P103Yosy NanaNo ratings yet
- FPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorDocument4 pagesFPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorseventhsensegroupNo ratings yet
- An Efficient and Empirical Model of Distributed ClusteringDocument5 pagesAn Efficient and Empirical Model of Distributed ClusteringseventhsensegroupNo ratings yet
- Non-Linear Static Analysis of Multi-Storied BuildingDocument5 pagesNon-Linear Static Analysis of Multi-Storied Buildingseventhsensegroup100% (1)
- Analysis of The Fixed Window Functions in The Fractional Fourier DomainDocument7 pagesAnalysis of The Fixed Window Functions in The Fractional Fourier DomainseventhsensegroupNo ratings yet
- Ijett V4i10p158Document6 pagesIjett V4i10p158pradeepjoshi007No ratings yet
- Design and Implementation of Multiple Output Switch Mode Power SupplyDocument6 pagesDesign and Implementation of Multiple Output Switch Mode Power SupplyseventhsensegroupNo ratings yet
- Experimental Analysis of Tobacco Seed Oil Blends With Diesel in Single Cylinder Ci-EngineDocument5 pagesExperimental Analysis of Tobacco Seed Oil Blends With Diesel in Single Cylinder Ci-EngineseventhsensegroupNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- UnLock Root Pro 4.1.1Document9 pagesUnLock Root Pro 4.1.1jackcarver11No ratings yet
- CS300.1 CS60.4 CS60.2: The Official Brand of Live MusicDocument8 pagesCS300.1 CS60.4 CS60.2: The Official Brand of Live MusicLuis RodriguezNo ratings yet
- Block Diagram: PowerDocument96 pagesBlock Diagram: PowerBrennan GriffinNo ratings yet
- OpenSAP Byd4 Week 5 Unit 5 Additional ExerciseDocument2 pagesOpenSAP Byd4 Week 5 Unit 5 Additional ExerciseHong YangNo ratings yet
- Adnan PDFDocument3 pagesAdnan PDFmudassarhussainNo ratings yet
- Domus Ventilation Guide 2019Document96 pagesDomus Ventilation Guide 2019Regie CayasNo ratings yet
- IntroductionCorporate Social Responsibility To Gati by PrashantDocument9 pagesIntroductionCorporate Social Responsibility To Gati by PrashantvarshaNo ratings yet
- Mike and KeyDocument25 pagesMike and KeyddscribeNo ratings yet
- Types of CameraDocument18 pagesTypes of CameraVijay Ravi100% (1)
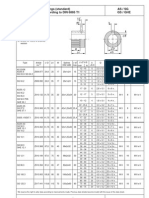
- As / SG Gs / Ghe Dimensions For Couplings (Standard) Bore With Keyway According To DIN 6885 T1Document1 pageAs / SG Gs / Ghe Dimensions For Couplings (Standard) Bore With Keyway According To DIN 6885 T1hadeNo ratings yet
- IRGC (2021) - Spotlight - Risk Governance and The Rise of DeepfakesDocument4 pagesIRGC (2021) - Spotlight - Risk Governance and The Rise of DeepfakessaidNo ratings yet
- BS en 00480-6-2005 PDFDocument8 pagesBS en 00480-6-2005 PDFShan Sandaruwan AbeywardeneNo ratings yet
- Advance Java Sem 5Document18 pagesAdvance Java Sem 5Gunjan Pratim JadhavNo ratings yet
- Click and Learn How To Get Free TikTok FansDocument4 pagesClick and Learn How To Get Free TikTok FansFreedmanMcFadden9No ratings yet
- Guidelines For Layout and Format of The Proposal: 1. Page Margins (For All Pages) - Use A4 Size PaperDocument3 pagesGuidelines For Layout and Format of The Proposal: 1. Page Margins (For All Pages) - Use A4 Size PaperAummy CreationNo ratings yet
- 22KW Hydraulic Power Unit GADocument1 page22KW Hydraulic Power Unit GAGabi GabrielNo ratings yet
- Microsoft Word - CHALLAN DHSK - 5th - Sem - Challan - 22-23Document1 pageMicrosoft Word - CHALLAN DHSK - 5th - Sem - Challan - 22-23YoUnG PrINCeNo ratings yet
- Geothermal Project TimelinesDocument10 pagesGeothermal Project TimelinesAldwin EncarnacionNo ratings yet
- Helukabel F-Cy-JzDocument2 pagesHelukabel F-Cy-JzMikko MagtibayNo ratings yet
- Laboratorio de Microondas - Medicion en Lineas de TX Usando Lineas RanuradasDocument5 pagesLaboratorio de Microondas - Medicion en Lineas de TX Usando Lineas RanuradasacajahuaringaNo ratings yet
- Abstract Superstructure Conc - Frame WestgateDocument2 pagesAbstract Superstructure Conc - Frame WestgateTashamiswa MajachaniNo ratings yet
- Faqs: Instant Credit Card Approval and IssuanceDocument1 pageFaqs: Instant Credit Card Approval and Issuancedaong_84No ratings yet
- Society and Culture With Family PlanningDocument7 pagesSociety and Culture With Family PlanningHope Earl Ropia BoronganNo ratings yet
- Colphenebswh 1816Document2 pagesColphenebswh 1816vinoth kumar SanthanamNo ratings yet
- Ms500se PDFDocument5 pagesMs500se PDFEduardo NazarioNo ratings yet
- SAP MM Module OverviewDocument15 pagesSAP MM Module OverviewAmit Kumar100% (1)
- ASME B16.47 Series A FlangeDocument5 pagesASME B16.47 Series A FlangePhạm Trung HiếuNo ratings yet
- DC and AC InterferenceDocument40 pagesDC and AC InterferenceREJI JOY ThoppilNo ratings yet
- 25 Powerful Business English Presentation Phrases To Impress Your AudienceDocument3 pages25 Powerful Business English Presentation Phrases To Impress Your AudienceMutia ChimoetNo ratings yet
- Corrective MaintenanceDocument12 pagesCorrective MaintenanceMohammed Nerissa100% (1)