Professional Documents
Culture Documents
Software Piracy - Sri Lanka
Uploaded by
Prasanga WdzCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Software Piracy - Sri Lanka
Uploaded by
Prasanga WdzCopyright:
Available Formats
University of Colombo
Faculty of Graduate Studies
Postgraduate Diploma in Information Systems Management
2015/2016
PgDISM 501 - Information Policy
Individual Assignment
Title: Software Piracy: Critical Analysis
Student Name
Primal Prasanga Wadanamby
Registration No.
2015/PgDISM/120
INFORMATION POLICY
ACKNOWLEDGEMENT
I would like to extend my sincere gratitude for our lecturer, Dr. Prathiba Mahanamahewa, for
his continuous advice and guidance given to me throughout this module. Without his
immense guidance and supervision, it would be hard for us to continue studies properly.
My heartfelt gratitude also goes to my friends for their continuous support guiding me in all
aspects throughout the module.
Finally I would like to express my sincere gratitude for all the people who gave their massive
support to make this project a success.
ii
INFORMATION POLICY
TABLE OF CONTENTS
ACKNOWLEDGEMENT .........................................................................................................ii
LIST OF FIGURES .................................................................................................................. iv
LIST OF ABBREVIATIONS .................................................................................................... v
INTRODUCTION ..................................................................................................................... 6
FACTORS BEHIND SOFTWARE PIRACY ........................................................................... 7
STATISTICAL ANALYSIS ..................................................................................................... 9
REGIONAL HIGHLIGHTS .................................................................................................. 9
COUNTRY HIGHLIGHTS SRI LANKA ........................................................................ 12
LEGAL ANALYSIS ................................................................................................................ 14
LEGAL FRAMEWORK - INTERNATIONAL .................................................................. 14
LEGAL FRAMEWORK - LOCAL ..................................................................................... 14
CASES REPORTED LOCAL .......................................................................................... 16
SOLUTIONS ........................................................................................................................... 17
TECHNICAL ....................................................................................................................... 17
LEGAL ................................................................................................................................ 17
REFERENCING AND BIBLIOGRAPHY.............................................................................. 19
iii
INFORMATION POLICY
LIST OF FIGURES
Figure 1 - Average Rates of Unlicensed Software Use ............................................................. 9
Figure 2 - Emerging Markets 2014 .......................................................................................... 10
Figure 3 - Global PC Shipments .............................................................................................. 10
Figure 4 - Commercial Value of Pirated Software .................................................................. 11
Figure 5 - Commercial value of unlicensed software by country ............................................ 12
Figure 6 - Hardware Penetration .............................................................................................. 13
iv
INFORMATION POLICY
LIST OF ABBREVIATIONS
BSA Business Solution Alliance
IT Information Technology
OEM Original Equipment Manufacturer
PC Personal Computer
GDP Gross Domestic Product
DMCA - Digital Millennium Copyright Act
PIPA - Preventing Real Online Threats to Economic Creativity and Theft of Intellectual
Property Act
SOPA - Stop Online Piracy Act
WIPO - World Intellectual Property Organization
IPA - Intellectual Property Act
CCA - Computer Crimes Act
IP Internet Protocol
3D 3 Dimensions
INFORMATION POLICY
INTRODUCTION
With the rise of the information technology era, significance for technology related products
and services increased rapidly among countries, companies and individuals. In particular, the
globalization all around the world has created the necessity of information. Copying and
distribution of related materials had become a liable solution to fulfill such necessity. Even
without authorization of its owners, people have been tending to duplicate books, music,
video and software. Then the term Digital Piracy was introduced to the digital world due to
rapid increase of these copyright violations.
SPA (1998: cited in Gopal et al 2004) defined Digital piracy as illegal duplication of digital
goods, software, documents, audio and video for any reason other than to backup without
explicit permission from and compensation to the copyright holder (SPA: 1998 cited in
Gopal et al. 2004, p-03). Such acts have become major concern for both product
manufacturer in various industries and the policy makers. Especially in software industry,
piracy has been the foremost threat which loosened revenues and violated copyrights of both
companies and individuals.
In todays world, software piracy can be seen in multiple forms. Aladdin (2008) has
mentioned 9 forms of software piracy as below.
CD-R Infringement
Soft-lifting
Uploading and Downloading
Unrestricted Client Access Infringement
Software Counterfeiting
OEM Unbundling
Hard Disk Loading
Renting
Commercial Use of Non-Commercial Software
INFORMATION POLICY
FACTORS BEHIND SOFTWARE PIRACY
Continuity of software piracy is caused by numerous motives. The degree of software piracy
varies in different countries and in different regions. Though there are legal protection for
software in some countries, some are do not or rarely enforced for software protection. In
recent decades, many studies and researches have been conducted on reasons behind software
piracy. Eining and Christensen (1991 cited in Limayem, Khalifa & Chin, 2004: p125) utilize
the Theory of Reasoned Action (TRA) to build a model of piracy behavior which addressed
the individuals intension towards software piracy. Then later Ajzen (1991 cited in Limayem,
Khalifa & Chin, 2004: p124) developed the Theory of Planned Behavior (TPB) which
addressed the psychological aspects towards software piracy.
By referring few relative studies, below factors are identified as major reasons of software
piracy.
High price of software
Countries with lower and emerging economies are often victims of software piracy
due to the unaffordable cost of software. BSA (2013) emphasis the correlation of
piracy rate and economy of a country is evidently a critical factor.
Legal enforcement
Copy right laws and policies are established in order to avoid infringements of rights
and to minimize software piracy. In European and North American region people are
aware of laws and policies on copyright infringement. With the legal enforcement in
their countries, they are obligated to respect copyrights and they have achieved lower
software piracy rate as a result of legal enforcement.
Social and cultural factors
Juniwasarakij (2013) indicates that social and cultural factors play a vital role in
decision making on software piracy. In regions, countries are divided according to
their social structure. Especially on collectivism and individualism. Often countries
with collectivism structure tends to share resources among their community.
Therefore piracy rate is known to be in higher levels in collectivistic countries than
individualistic.
Public awareness
Lack of awareness in software license, agreements and legal aspects related are
known to be one of the major threat in software industry.
7
INFORMATION POLICY
Availability of pirated software on internet
Availability of pirated software copies on internet is one major factor which tends
people to involve in software piracy. Easy access, portability and riskless method of
having a software worth hundreds or thousands of dollars, increases the piracy rate
severely.
INFORMATION POLICY
STATISTICAL ANALYSIS
Software piracy has created negativity in economic and social factors. Especially in global
economy, it has been the cause of cripple in software industry. To measure and prevent
software piracy, Business Software Alliance (BSA) conducts studies globally. Key findings
of their recent global software study can be given as below.
Global piracy rate for PC software at 43%
Commercial value of $62.7 billion in 2013 for the market of pirated software ($4.7
billion more than year 2010)
Emerging economies have taken 56% of new PC shipments in 2011 and account for
more than half of all PCs in use
Emerging economies holds the highest software piracy rate
(BSA, 2012)
REGIONAL HIGHLIGHTS
World economy has changed its direction drastically towards emerging markets. Over the
past decade, global economy managed to survive in crisis which created falls in every
industry. Although the crisis affected to the software industry, piracy rate has been increased
continuously. According to Khadka (2015) global software piracy rate in 2007 was 38% and
in 2013 was 43%.
The increment of global software piracy rate is caused by variation in software piracy by
regions.
Figure 1 - Average Rates of Unlicensed Software Use
Source: (BSA, 2013)
9
INFORMATION POLICY
Figure 1 illustrates how unlicensed software programs are in use regionally. According to
average rate given, it can be identified that Western Europe and North America holds the
lowest rates from all 6 regions. Asia-pacific region is in the prime location which holds 62%
in rate. According to Forbes (2014) Asia-pacific region is the native ground for worlds best
emerging economies. Especially countries as China and India (in Figure 2) placed well ahead
in the list.
Figure 2 - Emerging Markets 2014
Source: (Forbes, 2014)
Hence the demand for resources is comparably higher in such countries. Figure 3 illustrates
how PCs shipments made to fulfill requests of emerging economies.
Figure 3 - Global PC Shipments
Source: (BSA, 2012)
10
INFORMATION POLICY
PC shipments for emerging economies have been increasing rapidly. In 2010, the difference
was marginal between matured and emerging economies. But the gap continuously increased
and emerging economies have extended their lead by acquiring 56% of rate in 2011. And
even demand for software has increased along with development and tends to accomplish by
using illegal software copies. Figure 4 clearly indicates emerging countries such as China,
India, Thailand, and Indonesia etc. are in the regions with high unlicensed software use rates.
Figure 4 - Commercial Value of Pirated Software
Source: (BSA, 2013)
The total commercial value of unlicensed software used in Asia-Pacific regions in 2013 is
US$21 billion (Yu, 2014). In Asia, Bangladesh lead in the list having highest piracy rate of
87%, followed by Pakistan at 85%, Indonesia at 84%, Sri Lanka at 83%, and Vietnam at 81%
(BSA, 2013). It can be identified a drop in piracy rates in Asian region by considering the
data from 2007 (Figure 5).
11
INFORMATION POLICY
Figure 5 - Commercial value of unlicensed software by country
Source: (BSA, 2013)
However the commercial values has been increasing rapidly. Especially in Vietnam, Sri
Lanka, Pakistan, Bangladesh and Thailand the commercial values have multiplied in 2013
when compared it with 2007.
COUNTRY HIGHLIGHTS SRI LANKA
Over the past decade, Sri Lanka emerged as one of the best economies in the world and
fastest in Asian region. According to Trade Economics (2015) growth averaged 6.4 percent
between 2005 and 2014, with Gross Domestic Product (GDP) per capita rising from
US$1242.40 in 2005 to US$3,625 in 2014.
IT industry in the country has been growing at a steady rate along with its economy in past
few decades. According to SLASSCOM (2014) the size of Sri Lankas IT industry in 2007
was US$ 213 million and has gained significant growth up to US$ 386 million in 2011. Such
growth has widened the necessity of hardware and software around the country. With the
growing demand, computer hardware market dominated in IT spending. In 2007 70% of Sri
Lankas IT spending were on hardware. ICTA (2011 cited in ICRA, 2011: p11) expected that
nearly 2,559,000 PCs are in use while having PC stock growth rate of 25.2% in 2010. And
also they have predicted more than double in stock of PCs in 2015 (Figure 6).
12
INFORMATION POLICY
Figure 6 - Hardware Penetration
Source: (ICTA, 2011 cited in ICRA, 2011)
Though the predicted improvement of hardware market clarifies the growth in IT industry,
software market lags in severely. While Sri Lankas spending on software was US$ 47
million in 2011, commercial value of unlicensed software was US$ 86 million. Hence it is
believed that software requirements for PCs are majorly fulfilled by pirated software (ICRA,
2011).
According to BSA (2013) Sri Lanka is in 5th place with rate of 83% in the list of countries
with highest unlicensed software installation rate in Asia. With the development of the IT
industry, necessity has created the environment for software piracy. Though the requirements
increases day by day, country has been able to reduce the unlicensed software installation rate
by 7% within 2007 - 2013. But the commercial value has been doubled in 2013 when
compared it with 2007.
13
INFORMATION POLICY
LEGAL ANALYSIS
LEGAL FRAMEWORK - INTERNATIONAL
Software privacy prevention has been prioritized internationally since 1980s. Therefore
countries with matured IT industry addressed laws and policies to protect the intellectual
right by preventing piracy. United States as the narrator, established acts in searching legal
solution for piracy prevention. Below given are three significant acts which presented in
United States in recent years.
Digital Millennium Copyright Act (DMCA) was the first to be presented in 1998 which
criminalized illegal production and dissemination of technology, devices, or services. And
also it accompanied provisions to limit online copyright infringement. Apart from laws and
policies, the act has allowed to perform organizations to investigate and conduct actions on
such copy right violations.
(DMCA, 1998)
Preventing Real Online Threats to Economic Creativity and Theft of Intellectual
Property Act (PIPA) and Stop Online Piracy Act (SOPA) are two of the modern day
infringement addressing act presented in 2011. They facilitate the government and copyright
holders to take legal actions regarding infringements done by websites which are dedicated to
the sale of infringing or forged goods.
(Yeh, B.T. & Miller, J., 2011)
LEGAL FRAMEWORK - LOCAL
Business Software Association ranks Sri Lanka with worst nations for software piracy over
the past years. With economical and legal conditions available in the country, software piracy
has been a common practice all over the country. In order to strengthen the legal enforcement
and to overcome challenges caused, several laws (acts) have been established over the past
decade. Given below are the three acts introduced respectively.
Intellectual Property Act of 2003
Computer Crimes Act of 2007
Companies Act of 2007
14
INFORMATION POLICY
Intellectual Property Act of 2003 (IPA)
Intellectual Property Act accompanies features for the protection of software, trade secrets
and integrated circuits. To prevent infringement of intellectual property right, it has enabled
a framework which is validated by World Intellectual Property Organization (WIPO).
Copy right and related rights, Industrial Designs, Patents, Marks & Trade Marks, Collective
marks, Certification Marks, Trade Names and Layout Designs of Integrated Circuits are the
headings which stated under intellectual property by the act. Legal provision has been given
by operation of law to each above property from the act and addressed in different sections.
(IPA, 2003)
Computer Crimes Act of 2007 (CCA)
Computer Crimes Act primarily addresses crimes related to computer, hacking offences and
contents. In support of preventing software piracy, the act has addressed content related
cyber-crimes and included laws and regulations.
The Act comprises provisions which state that any person who is intentionally or without
lawful authority carries out a function, produces, sells, procures for use, imports and exports,
distributes or otherwise makes any computer or computer system or computer program shall
be guilty of an offence. And it has given the authorization to conduct thorough investigation
to prevent such practices in Sri Lanka.
(CCA, 2007)
Companies Act of 2007
Companies Act addresses the legislative factor of the commercial law in Sri Lanka. Though
importance of the act was to ease the process of formation of a company, it provides legal
body to get protection in today business world.
Legislation of the commercial law has enabled the companies to deals with issues of both
private law and public law. Especially act provides legal enforcement on company rights,
relations, and conduct of individuals and businesses which are engaged in commerce,
15
INFORMATION POLICY
merchandising, trade, and sales. Hence Companies Act also strengthen the legal frame work
of software piracy prevention.
(Nation.lk, 2007)
CASES REPORTED LOCAL
Case 1 - Microsoft Corporation and Media Center 2011
According to a complaint made by Microsoft Sri Lanka, Computer dealer/media center in
Unity Plaza, Colombo 4 found with unlicensed Microsoft software (Windows XP
Professional and Office Enterprise 2007) in DVDs which are used in pre-installing as bundle
with purchased PCs. Then a case was filed against the dealer at Supreme Court in 2010 by
Microsoft.
Computer dealer agrees to make a settlement after the court decision and signed affirming
that they will no longer distribute or sell any computers with pirated/unlicensed Microsoft
software in future.
(Microsoft Corporation, 2011)
Case 2 Tec Touch International 2008
According to a complaint filed by local music producers, Tec Touch International was raided
by police and found thousands of counterfeit copies of local music, movies, teledramas and
business software which are belongs to members of BSA.
After the prosecution, the court granted the accused bail of Rs. 25,000 for each case filed
against the owners and in addition, two surety bonds of Rs. 100,000 for each case had to be
signed by the accused with one of the sureties.
(ANCL, 2008)
16
INFORMATION POLICY
SOLUTIONS
TECHNICAL
Generate license at the server
o Without providing the software program and a key in bundle, registration and
validation of the software needs to be done at the server via internet. Autodesk
inc, software enterprise in 3D modeling uses network license for registration
of their product after purchase.
Partial installation via internet
o CD of the purchased software program only should contain partial file.
Software installation can be completed by allowing to download via internet.
Google has introduced this method even with their Chrome browser.
IP Tag
o Monitoring software programs location (at server) by installed PCs IP
address and making sure the serial number of the software doesnt appear on
multiple locations.
SecuROM
o It is a solution/file developed by SONY to prevent copying software/media
CD by home media duplication devices, professional duplicators, and even
resists reverse engineering of software.
QR Code and Mobile Gateway
o Providing serial number of a software in QR code and allowing user
authentication by using a mobile gateway. Whatsapp PC software allows to
validate user by its mobile number by using this technology.
LEGAL
Legal bind on Cloud data space providers
o Cloud technology is common data store solution in present era. It is used as
data storage for websites and blogs. Legal enforcement on such space
providers to monitor and address storing pirated software copies will prevent
use of internet as repository.
17
INFORMATION POLICY
Regulations on Banning Torrent Websites
o Torrent websites holds the main entry point for pirated software to the
country. Therefore legal actions required to perform regulations and sanctions
on torrent websites and clients through countrys internet service providers.
18
INFORMATION POLICY
REFERENCING AND BIBLIOGRAPHY
Aladdin. (2008). Software Piracy: Causes, Effects, and Prevention. [Online] Available From:
ftp://ftp.cisapp.com/pub/marketing/HASP/HASP_SRM/WhitePapers/WP_HASP_Software_Piracy.pdf
[Accessed: 17 April 2015]
ANCL, (2008). Another company charged with piracy. [Online] Available From:
http://www.sundayobserver.lk/2008/07/27/fin20.asp [Accessed: 28 April 2015]
BSA. (2009) Software Piracy on the Internet: A Threat to Your Security. [Online]. Available
From: http://portal.bsa.org/internetreport2009/2009internetpiracyreport.pdf. [Accessed: 16
April 2015]
BSA. (2012). Shadow Market 2011 BSA Global Software Piracy Study. [Online] Available
From:
http://globalstudy.bsa.org/2011/downloads/study_pdf/2011_BSA_Piracy_Study-
Standard.pdf [Accessed: 18 April 2015]
BSA. (2013). The Compliance Gap - BSA Global Software Survey. [Online]. Available
From:
http://globalstudy.bsa.org/2013/downloads/studies/2013GlobalSurvey_Study_en.pdf
[Accessed: 17 April 2015]
Computer
Crime
Act
of
2007.
Chapter
24.
Available
From:
http://www.slcert.gov.lk/Downloads/Acts/Computer_Crimes_Act_No_24_of_2007%28E%2
9.pdf [Accessed: 29 April 2015]
Forbes. (2014) Turkey and South Africa's Interest Rate Hikes Still Might Save Emerging
Markets
from
the
Federal Reserve.
[Online]
Available
From:
http://www.forbes.com/sites/cedricmuhammad/2014/01/29/turkey-and-south-africas-interestrate-hikes-might-save-emerging-markets-from-the-federal-reserve/ [Accessed: 21 April 2015]
Gopal, R.D. (2004). A Behavioral Model of Digital Music Piracy. Journal of Organizational
Computing and Electronic Commerce. p. 1-34
ICRA, (2011) IT and ITES Industry in Sri Lanka. [Online]. Available From:
http://www.icralanka.com/images/pdf/Sri%20Lanka%20IT%20ITES%20Sept%2015%20Final.pdf [Accessed: 21 April 2015]
19
INFORMATION POLICY
Intellectual
Property
Act
of
2003,
Chapter
36.
Available
From:
http://www.wipo.int/wipolex/en/text.jsp?file_id=184465 [Accessed: 29 April 2015]
Juntiwasarakij, S. (2013). Towards Socio-Economic Perspective of Software Piracy: The
Case of Thailand. Proceeding of WCECS. 2. p. 23-27.
Khadka, I. (2015). Software piracy: A study of causes, effects and preventive measures.
[Online]
Available
From:
http://www.theseus.fi/bitstream/handle/10024/87274/Khadka_Ishwor.pdf?sequence=1
[Accessed: 17 April 2015]
Limayem, M., Khalifa, M. & Chin, W.W. (2004). Factors motivating software piracy: a
longitudinal study. p. 124-131.
Luppicini, R & Adell, R. (2009) Handbook of Research on Technoethics. Information
Science Publishing.
Microsoft Corporation. (2011) Parties agree to settle in Microsoft Corporation vs. Media
Centre
case
in
the
Supreme
Court.
[Online]
Available
From:
http://www.microsoft.com/srilanka/PressRoomNew96.aspx [Accessed: 28 April 2015]
Nation.lk. (2007) Salient features of Companies Act No. 7 of 2007. [Online] Available From:
http://www.nation.lk/2007/04/29/busi6.htm [Accessed: 29 April 2015]
Sharari, A.S. (2006). Intellectual Property Rights Legislation and Computer Software Piracy
in Jordan. Journal of Social Sciences. 2(1). p. 7-13.
Sharma, V., Hussain, S.Z. & Rizvi, S.A.M. (2010). Distributed Co-ordinator Model for
Optimal Utilization of Software and Piracy Prevention. International Journal of Computer
Science and Security. p.550-558.
SLASSCOM. (2014) Sri Lankan IT/BPM Industry - 2014 Review. [Online]. Available From:
http://www.slasscom.lk/sites/default/files/Sri%20Lankan%20ITBPM%20Industry%20Review%202014.pdf [Accessed: 21 April 2015]
The
digital
millennium
copyright
act
of
1998,
Chapter
12.
Available
http://www.copyright.gov/legislation/hr2281.pdf [Accessed: 29 April 2015]
20
From:
INFORMATION POLICY
Trade Economics. (2015) Sri Lanka GDP Growth Rate. [Online] Available From:
http://www.tradingeconomics.com/sri-lanka/gdp-growth [Accessed: 22 April 2015]
Yeh, B.T. & Miller, J. (2011) A Legal Analysis of S. 968, the PROTECT IP Act. [Online]
Available From: http://fas.org/sgp/crs/misc/R41911.pdf [Accessed: 30 April 2015]
Yu, E. (2014) APAC software piracy rate climbs to 62 percent. [Online] Available From:
http://www.zdnet.com/article/apac-software-piracy-rate-climbs-to-62-percent/ [Accessed: 20
April 2015]
21
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Solucionario Econometría Jeffrey M. WooldridgeDocument4 pagesSolucionario Econometría Jeffrey M. WooldridgeHéctor F Bonilla3% (30)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Ccna MCQ 1 PDFDocument14 pagesCcna MCQ 1 PDFsreesree.b100% (1)
- University of Colombo Faculty of Graduate Studies: PGDBM 504 - Strategic ManagementDocument15 pagesUniversity of Colombo Faculty of Graduate Studies: PGDBM 504 - Strategic ManagementPrasanga WdzNo ratings yet
- Engineering Mathematics Stage 01Document4 pagesEngineering Mathematics Stage 01Prasanga WdzNo ratings yet
- MA1001Document3 pagesMA1001Prasanga WdzNo ratings yet
- C++ Programming Concepts Assignment ReportDocument33 pagesC++ Programming Concepts Assignment ReportPrasanga WdzNo ratings yet
- Index: Skiii I0OtDocument6 pagesIndex: Skiii I0OtPrasanga WdzNo ratings yet
- APLC - Individual AssignmentDocument29 pagesAPLC - Individual AssignmentPrasanga WdzNo ratings yet
- Tutorial 01 QuestionsDocument1 pageTutorial 01 QuestionsPrasanga WdzNo ratings yet
- Basic Elactrical Engineering Stage 01Document5 pagesBasic Elactrical Engineering Stage 01Prasanga WdzNo ratings yet
- GE1003Document3 pagesGE1003Prasanga WdzNo ratings yet
- Web Programming - Individual AssignmentDocument49 pagesWeb Programming - Individual AssignmentPrasanga WdzNo ratings yet
- EWAP - Individual AssignmentDocument34 pagesEWAP - Individual AssignmentPrasanga WdzNo ratings yet
- Ubiquitous ComputingDocument96 pagesUbiquitous ComputingPrasanga Wdz100% (1)
- Sri Lanka Company Act7 of 2007Document488 pagesSri Lanka Company Act7 of 2007Dammike KobbekaduweNo ratings yet
- Iesl Model Paper-EnglishDocument5 pagesIesl Model Paper-EnglishPrasanga WdzNo ratings yet
- Future Technologies, Today's ChoicesDocument72 pagesFuture Technologies, Today's Choicesisaac2008100% (31)
- Harvard Referencing Examples Tcm44-39847Document29 pagesHarvard Referencing Examples Tcm44-39847aangsetiawanNo ratings yet
- Financial Ratio AnalysisDocument14 pagesFinancial Ratio AnalysisPrasanga WdzNo ratings yet
- ADS DocumentDocument51 pagesADS DocumentPrasanga WdzNo ratings yet
- Elemetary Linear Algebra by MathewsDocument201 pagesElemetary Linear Algebra by MathewsPrasanga WdzNo ratings yet
- SPC LecturenotesDocument99 pagesSPC LecturenotesPrasanga WdzNo ratings yet
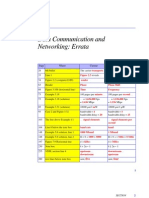
- Data Communication and Networking Errata CorrectionsDocument2 pagesData Communication and Networking Errata CorrectionsPrasanga WdzNo ratings yet
- Textile Mathematics Part 1Document63 pagesTextile Mathematics Part 1Anonymous PHCzwD8eAO100% (1)
- 053 Database ProgrammingDocument24 pages053 Database Programmingsyadshak05No ratings yet
- SEP Essay FinalDocument38 pagesSEP Essay FinalAlejandro RojasNo ratings yet
- VoIP FinalDocument12 pagesVoIP FinalPrasanga WdzNo ratings yet
- Build Cloud Applications Without Hand-CodingDocument22 pagesBuild Cloud Applications Without Hand-CodingPrasanga WdzNo ratings yet
- Fundamentals of Image ProcessingDocument72 pagesFundamentals of Image Processingkirthi83No ratings yet
- Stored ProcedureDocument16 pagesStored ProcedurePrasanga WdzNo ratings yet
- EC20 HMI Connection GuideDocument3 pagesEC20 HMI Connection GuideGabriel Villa HómezNo ratings yet
- Winsteps ManualDocument615 pagesWinsteps Manualandresote33100% (1)
- SPDIF WhitepaperDocument14 pagesSPDIF Whitepaperapi-3760834100% (1)
- MOAC Virtual Lab ExercisesDocument3 pagesMOAC Virtual Lab ExercisesJyoti PatelNo ratings yet
- Compressed SensingDocument14 pagesCompressed Sensingnigel989No ratings yet
- V Flower Vocaloid Wiki FandomDocument1 pageV Flower Vocaloid Wiki FandomFlower chanNo ratings yet
- Ericsson Ethernet Jumbo FramesDocument18 pagesEricsson Ethernet Jumbo Framesmbuh_meongNo ratings yet
- LM M530Document58 pagesLM M530Victor VilcapomaNo ratings yet
- Ict-Webpage 10 q1 w3 Mod3Document12 pagesIct-Webpage 10 q1 w3 Mod3Lemuel Ramos RempilloNo ratings yet
- V11 What's New and Changes PDFDocument98 pagesV11 What's New and Changes PDFGNo ratings yet
- Marrow E4 FMT 2Document151 pagesMarrow E4 FMT 2Cherry KolaNo ratings yet
- CVJuan David Ramírezdelos RíosDocument1 pageCVJuan David Ramírezdelos Ríositzel083No ratings yet
- Transportation Model Optimization With MODI MethodDocument2 pagesTransportation Model Optimization With MODI Methodhello_khayNo ratings yet
- Face RecogDocument26 pagesFace RecogFavasNo ratings yet
- ENGG103 Course Specifications Eng v202Document7 pagesENGG103 Course Specifications Eng v202Ibrahim MahamidNo ratings yet
- 21 Primavera Tips and ShortcutsDocument30 pages21 Primavera Tips and ShortcutsMarioNo ratings yet
- Transport Layer: Unit - IVDocument19 pagesTransport Layer: Unit - IVHarishmaNo ratings yet
- 2010 PAARL Standards For Academic LibrariesDocument6 pages2010 PAARL Standards For Academic LibrariesChristian Robert NalicaNo ratings yet
- ZXCTN 6500 V1.00.10R2 Benchmark Slides - 20141023Document32 pagesZXCTN 6500 V1.00.10R2 Benchmark Slides - 20141023محيي الدين الكميشىNo ratings yet
- UntitledDocument2 pagesUntitledmoch bagas setya rahmanNo ratings yet
- Foundations of Information Systems in BusinessDocument28 pagesFoundations of Information Systems in BusinessRaheel PunjwaniNo ratings yet
- Adobe Photoshop WorkshopDocument67 pagesAdobe Photoshop WorkshopInigo JosephNo ratings yet
- Write For Us Digital MarketingDocument6 pagesWrite For Us Digital MarketingSumit PrajapatiNo ratings yet
- College Events Dissemination System: Rishabh Kedia, Abhishek Pratap Singh & Varun GuptaDocument8 pagesCollege Events Dissemination System: Rishabh Kedia, Abhishek Pratap Singh & Varun GuptaTJPRC PublicationsNo ratings yet
- Chapter 14 SFCDocument48 pagesChapter 14 SFCSiswo Ponco RahardjoNo ratings yet
- Pervasive Healthcare Computing: EMR/EHR, Wireless and Health MonitoringDocument3 pagesPervasive Healthcare Computing: EMR/EHR, Wireless and Health MonitoringPajak RedikonNo ratings yet
- HR Practices and Organizational Strategies in Select: IT Companies in India "Document59 pagesHR Practices and Organizational Strategies in Select: IT Companies in India "Sneha MehtaNo ratings yet
- Ipv4 Address Classes PDFDocument2 pagesIpv4 Address Classes PDFAmol IngleNo ratings yet