Professional Documents
Culture Documents
GSTV 2015-16 CPNI Procedures PDF
Uploaded by
Federal Communications Commission (FCC)0 ratings0% found this document useful (0 votes)
166 views1 pageFCC CPNI Submission
Original Title
GSTV 2015-16 CPNI Procedures.pdf
Copyright
© © All Rights Reserved
Available Formats
PDF or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentFCC CPNI Submission
Copyright:
© All Rights Reserved
Available Formats
Download as PDF or read online from Scribd
0 ratings0% found this document useful (0 votes)
166 views1 pageGSTV 2015-16 CPNI Procedures PDF
Uploaded by
Federal Communications Commission (FCC)FCC CPNI Submission
Copyright:
© All Rights Reserved
Available Formats
Download as PDF or read online from Scribd
You are on page 1of 1
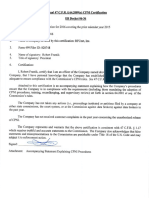
47 C.F.R. 64.
2009(e) ACCOMPANYING STATEMENT:
POLICIES AND OPERATING PROCEDURES USED TO ENSURE COMPLIANCE
WITH FCC RULES CONCERNING CPNI
1. GS Texas Ventures, LLC (GSTX), as a matter of policy, does not make available to
any third party Customer Proprietary Network Information (CPNI) except as necessary
to provide service and comply with applicable interconnection agreements, intercarrier
requirements, and as routinely disclosed at the signaling layer.
2. Since CPNI is not made available to third parties, except as necessary to provide
service, GSTX is not required to allow the Customer to opt out of the use of their CPNI
by third parties. Any changes to this policy will require the adoption of a notice and optout mechanism, and status reporting that complies with FCC rules.
3. CPNI is used by GSTX internally as needed for the provisioning, billing, and
maintenance of the services provided. CPNI is also used internally for directed sales
efforts for service offerings among the categories of service to which the customer
already subscribes (e.g. contract renewals), but this information is only provided to
GSTX sales staff on a case by case basis and records are maintained of these efforts.
GSTXs sales staff do not have access to systems where CPNI is stored and
maintained. CPNI is not currently used for general sales and marketing campaigns. Any
changes to this policy will require proper record keeping as required by FCC rules.
4. All GSTX staff have been informed that CPNI may only be used for allowed purposes
(as narrowly defined herein) and are aware that the unauthorized use of CPNI will be
grounds for dismissal.
5. CPNI is protected from unauthorized access and use. Systems that are used to store
and maintain CPNI are firewalled from the public internet. Only information associated
with individual login sessions is stored on workstations and all data repositories are
centralized on servers. Data is segregated at the server level (e.g., staff that do not have
access to CPNI do not have accounts on servers where CPNI is stored). Backups are
encrypted with password protection. Login credentials are controlled and are changed
periodically. Hardcopy is not produced except in a directed manner (e.g. for a particular
customer for an authorized use). Hardcopy produced for temporary use (e.g., installation
and maintenance activities) is destroyed after use.
6. Supervisory review at the highest level exists to ensure the foregoing policies and
procedures are followed.
7. GSTX does not use, disclose or permit access to CPNI to identify or track customers
that call competing service providers.
You might also like
- Incident Management Process Guide For Information TechnologyFrom EverandIncident Management Process Guide For Information TechnologyNo ratings yet
- KHT - CPNI - 2015-16 Procedures PDFDocument1 pageKHT - CPNI - 2015-16 Procedures PDFFederal Communications Commission (FCC)No ratings yet
- Computer-Managed Maintenance Systems: A Step-by-Step Guide to Effective Management of Maintenance, Labor, and InventoryFrom EverandComputer-Managed Maintenance Systems: A Step-by-Step Guide to Effective Management of Maintenance, Labor, and InventoryRating: 3 out of 5 stars3/5 (1)
- Product Terms & Conditions (PTC)Document17 pagesProduct Terms & Conditions (PTC)KarthikNo ratings yet
- Is Policy JEL Observations 10 April 07Document5 pagesIs Policy JEL Observations 10 April 07sksinghkgnNo ratings yet
- Remote Access PolicyDocument4 pagesRemote Access PolicydaviedNo ratings yet
- Overview: Server Security PolicyDocument3 pagesOverview: Server Security PolicyInformation TechnologyNo ratings yet
- Internet DMZ Equipment Policy: 1. OverviewDocument4 pagesInternet DMZ Equipment Policy: 1. OverviewAreefNo ratings yet
- Wi-27 CpniDocument2 pagesWi-27 CpniFederal Communications Commission (FCC)No ratings yet
- Overview: Server Security PolicyDocument3 pagesOverview: Server Security PolicySanda NechiforNo ratings yet
- CPNILetter PDFDocument4 pagesCPNILetter PDFFederal Communications Commission (FCC)No ratings yet
- EZ Network Systems 2012 CPNI AttachmentDocument2 pagesEZ Network Systems 2012 CPNI AttachmentFederal Communications Commission (FCC)No ratings yet
- POLICY FirewallAdministrationDocument8 pagesPOLICY FirewallAdministrationAbhishek BahiratNo ratings yet
- Attachment To 2012 Annual CPNI CertificationDocument2 pagesAttachment To 2012 Annual CPNI CertificationFederal Communications Commission (FCC)No ratings yet
- 2011 CPNI ATTACHMENT-Aspireworks1Document2 pages2011 CPNI ATTACHMENT-Aspireworks1Federal Communications Commission (FCC)No ratings yet
- Commonwealth Virtualization Policy SummaryDocument4 pagesCommonwealth Virtualization Policy Summaryalan dumsNo ratings yet
- IT 17.04.1 Firewall Management ProceduresDocument5 pagesIT 17.04.1 Firewall Management ProceduresAzeemNo ratings yet
- BTI - CPNI Statement of PolicyDocument1 pageBTI - CPNI Statement of PolicyFederal Communications Commission (FCC)No ratings yet
- T-Systems CPNI Policy Statement - Final 022717 PDFDocument2 pagesT-Systems CPNI Policy Statement - Final 022717 PDFFederal Communications Commission (FCC)No ratings yet
- Server Security PolicyDocument2 pagesServer Security PolicyPaul DamesNo ratings yet
- Overview: Server Security PolicyDocument3 pagesOverview: Server Security PolicySpit FireNo ratings yet
- InsuranceDocument142 pagesInsuranceஸ்ரீதர் ரெட்டிNo ratings yet
- Coi Cpni Accomp Statement 022811Document3 pagesCoi Cpni Accomp Statement 022811Federal Communications Commission (FCC)No ratings yet
- 15 Acceptable Usage PolicyDocument4 pages15 Acceptable Usage PolicyAliAlmutawaaNo ratings yet
- NexG - 2017 - CPNI Compliance - 02.17.17 PDFDocument3 pagesNexG - 2017 - CPNI Compliance - 02.17.17 PDFFederal Communications Commission (FCC)No ratings yet
- CommPartners 2011 CPNIDocument2 pagesCommPartners 2011 CPNIFederal Communications Commission (FCC)No ratings yet
- PTCL RFI for Revenue Assurance and Fraud Management SolutionDocument12 pagesPTCL RFI for Revenue Assurance and Fraud Management SolutionpaalhtcNo ratings yet
- PingTone CPNI Attachment - 2015Document3 pagesPingTone CPNI Attachment - 2015Federal Communications Commission (FCC)No ratings yet
- Pilgrim CPNI Policy 20132Document3 pagesPilgrim CPNI Policy 20132Federal Communications Commission (FCC)No ratings yet
- IMG2Document2 pagesIMG2Federal Communications Commission (FCC)No ratings yet
- Virtual Private Network (VPN) Policy: 1. Overview 2. PurposeDocument3 pagesVirtual Private Network (VPN) Policy: 1. Overview 2. PurposeWanaarbatNo ratings yet
- CCTV Guidance Data ControllerDocument18 pagesCCTV Guidance Data ControllerMihai PreotescuNo ratings yet
- 2012 Annual Statement of CPNI ComplianceDocument3 pages2012 Annual Statement of CPNI ComplianceFederal Communications Commission (FCC)No ratings yet
- Semester Project COSC 578: Best Video Rental Libraries Database Management Software SystemDocument35 pagesSemester Project COSC 578: Best Video Rental Libraries Database Management Software Systemkhara1234567890No ratings yet
- 3GPP TS 22.031Document12 pages3GPP TS 22.031santanameroNo ratings yet
- Img 0004Document4 pagesImg 0004Federal Communications Commission (FCC)No ratings yet
- Tele1net Cpni 2016 PDFDocument2 pagesTele1net Cpni 2016 PDFFederal Communications Commission (FCC)No ratings yet
- CPNIcert2016 PDFDocument4 pagesCPNIcert2016 PDFFederal Communications Commission (FCC)No ratings yet
- Mca2017agr Na Eng Sep20172 CRDocument9 pagesMca2017agr Na Eng Sep20172 CRbuzzoffscribd.comNo ratings yet
- 120 Maintenance CCTV Surveillance Systems CopDocument16 pages120 Maintenance CCTV Surveillance Systems CopAdrian Dalida AgawinNo ratings yet
- CCTV GuidanceDocument19 pagesCCTV GuidanceDigambar S TatkareNo ratings yet
- Service Unit PolicyDocument2 pagesService Unit PolicyAldwin Roy H. EsperNo ratings yet
- Republic of The PhilippinesDocument3 pagesRepublic of The PhilippinesLara Mae Alfonso AndresNo ratings yet
- Microsoft Cloud Agreement: 1. Grants, Rights and TermsDocument9 pagesMicrosoft Cloud Agreement: 1. Grants, Rights and TermsIndika P8No ratings yet
- MNP Porting Process Guidelines: SeparationDocument25 pagesMNP Porting Process Guidelines: SeparationbachmannNo ratings yet
- National Bank of Ethiopia VPN Policy: V P N (VPN) PDocument42 pagesNational Bank of Ethiopia VPN Policy: V P N (VPN) PBirhanNo ratings yet
- 3GPP TS 22.031Document12 pages3GPP TS 22.031santanameroNo ratings yet
- B - CPNI Documentation - 800-2017Document1 pageB - CPNI Documentation - 800-2017Federal Communications Commission (FCC)No ratings yet
- ATC Internship Letter - AnshDocument53 pagesATC Internship Letter - AnshAyush srivastavaNo ratings yet
- ACSI CPNI Cert 2016Document3 pagesACSI CPNI Cert 2016Federal Communications Commission (FCC)No ratings yet
- DPC - CCTV Guidance For Data ControllersDocument27 pagesDPC - CCTV Guidance For Data ControllersDave IdNo ratings yet
- SFD TrueCall Common-GSM 63Document24 pagesSFD TrueCall Common-GSM 63James WangNo ratings yet
- Accompanying Statement Explaining CPNI Procedures - Creative Interconnect Communications, LLCDocument2 pagesAccompanying Statement Explaining CPNI Procedures - Creative Interconnect Communications, LLCFederal Communications Commission (FCC)No ratings yet
- DMZ Lab Security Policy-2Document4 pagesDMZ Lab Security Policy-2SilverNo ratings yet
- C C CC C: of The Commission's RulesDocument5 pagesC C CC C: of The Commission's Rulessbrister6142No ratings yet
- CPNI Certification 2013 - RFCnetDocument4 pagesCPNI Certification 2013 - RFCnetFederal Communications Commission (FCC)No ratings yet
- 3GPP TS 22.032Document8 pages3GPP TS 22.032santanameroNo ratings yet
- Nov 2018 AnsDocument17 pagesNov 2018 AnsparasNo ratings yet
- IT Purchasing, Maintenance & Disposal Policy: Responsible Officer: Last Updated: Date of Review: Audience/ApplicationDocument3 pagesIT Purchasing, Maintenance & Disposal Policy: Responsible Officer: Last Updated: Date of Review: Audience/Applicationደስታ ጌታውNo ratings yet
- Terms of Reference (TOR) For Selection of Consulting Audit Firm For Conducting Information Systems Audit of Banglalink Digital Communications LTD PDFDocument5 pagesTerms of Reference (TOR) For Selection of Consulting Audit Firm For Conducting Information Systems Audit of Banglalink Digital Communications LTD PDFফয়সাল হোসেনNo ratings yet
- Paradigm Signed 2017 CPNI PDFDocument6 pagesParadigm Signed 2017 CPNI PDFFederal Communications Commission (FCC)No ratings yet
- 2017 Cpni Certification RTC PDFDocument2 pages2017 Cpni Certification RTC PDFFederal Communications Commission (FCC)No ratings yet
- CPNI Certification1Document2 pagesCPNI Certification1Federal Communications Commission (FCC)No ratings yet
- CPNI Operating ProceduresDocument2 pagesCPNI Operating ProceduresFederal Communications Commission (FCC)No ratings yet
- 2017 Cpni Certification Lucre PDFDocument2 pages2017 Cpni Certification Lucre PDFFederal Communications Commission (FCC)No ratings yet
- SKM C22717040608540 PDFDocument3 pagesSKM C22717040608540 PDFFederal Communications Commission (FCC)No ratings yet
- FCC Cpni LTR 2017 PDFDocument1 pageFCC Cpni LTR 2017 PDFFederal Communications Commission (FCC)No ratings yet
- Le Futur CPNI2017 StatementDocument1 pageLe Futur CPNI2017 StatementFederal Communications Commission (FCC)No ratings yet
- FCC Cpni Statement4 PDFDocument1 pageFCC Cpni Statement4 PDFFederal Communications Commission (FCC)No ratings yet
- 2016 Annual Certification Filed 2017 PDFDocument1 page2016 Annual Certification Filed 2017 PDFFederal Communications Commission (FCC)No ratings yet
- Signed CPNI Due March 20171 PDFDocument6 pagesSigned CPNI Due March 20171 PDFFederal Communications Commission (FCC)No ratings yet
- 2017-Accompanying Statement Explaining CPNI Procedures PDFDocument2 pages2017-Accompanying Statement Explaining CPNI Procedures PDFFederal Communications Commission (FCC)No ratings yet
- Hinson Signed 2017 CPNI PDFDocument6 pagesHinson Signed 2017 CPNI PDFFederal Communications Commission (FCC)No ratings yet
- Signed CPNI Due March 2017 PDFDocument6 pagesSigned CPNI Due March 2017 PDFFederal Communications Commission (FCC)No ratings yet
- Hello Pager Company CPNI Compliance Procedures February 20161Document1 pageHello Pager Company CPNI Compliance Procedures February 20161Federal Communications Commission (FCC)No ratings yet
- Celtic Communications Accompanying STMT CPNI 2016 Filing PDFDocument3 pagesCeltic Communications Accompanying STMT CPNI 2016 Filing PDFFederal Communications Commission (FCC)No ratings yet
- 2017 Annual CPNI Certification (Ops Procedures Attachement)Document2 pages2017 Annual CPNI Certification (Ops Procedures Attachement)Federal Communications Commission (FCC)No ratings yet
- 2017 Cpni Certification STC PDFDocument2 pages2017 Cpni Certification STC PDFFederal Communications Commission (FCC)No ratings yet
- CPNI Certification 20161 PDFDocument3 pagesCPNI Certification 20161 PDFFederal Communications Commission (FCC)No ratings yet
- To Who It May ConcernDocument1 pageTo Who It May ConcernFederal Communications Commission (FCC)No ratings yet
- STMT of Cpni Procedures & Compliance1 PDFDocument4 pagesSTMT of Cpni Procedures & Compliance1 PDFFederal Communications Commission (FCC)No ratings yet
- STMT of Cpni Procedures & Compliance1 PDFDocument4 pagesSTMT of Cpni Procedures & Compliance1 PDFFederal Communications Commission (FCC)No ratings yet
- 2016 CPNI Compliance Certificate PDFDocument2 pages2016 CPNI Compliance Certificate PDFFederal Communications Commission (FCC)No ratings yet
- Vista Latina CPNI 2017 Signed PDFDocument6 pagesVista Latina CPNI 2017 Signed PDFFederal Communications Commission (FCC)No ratings yet
- CPNI Statement 17Document6 pagesCPNI Statement 17Federal Communications Commission (FCC)No ratings yet
- CPNI Statement 171Document6 pagesCPNI Statement 171Federal Communications Commission (FCC)No ratings yet
- Summary of CPNI Compliance Process Requirements For LPC1Document2 pagesSummary of CPNI Compliance Process Requirements For LPC1Federal Communications Commission (FCC)No ratings yet
- Comunicaciones Rey CPNI 2017 Signed1 PDFDocument6 pagesComunicaciones Rey CPNI 2017 Signed1 PDFFederal Communications Commission (FCC)No ratings yet
- Favorite Comm. Signed FCC CPNI 2017 PDFDocument6 pagesFavorite Comm. Signed FCC CPNI 2017 PDFFederal Communications Commission (FCC)No ratings yet
- VVN CPNI 2017 Signed PDFDocument6 pagesVVN CPNI 2017 Signed PDFFederal Communications Commission (FCC)No ratings yet
- Terms of Use and Privacy PolicyDocument13 pagesTerms of Use and Privacy PolicyFarveen FarookNo ratings yet
- 2019 Version 70-741 Dumps With VCE and PDFDocument91 pages2019 Version 70-741 Dumps With VCE and PDFwilvarelNo ratings yet
- Work Order LetterDocument1 pageWork Order LetterAbdulfatah AliNo ratings yet
- Training and Certification Guide For Partners - 01-02-2019Document32 pagesTraining and Certification Guide For Partners - 01-02-2019Claudia Vargas Rosas67% (3)
- Automated job scheduling with AutoSysDocument30 pagesAutomated job scheduling with AutoSysamy_750% (2)
- Foundation: Larry L. Peterson and Bruce S. DavieDocument70 pagesFoundation: Larry L. Peterson and Bruce S. DavieJanhavi VishwanathNo ratings yet
- Network Theory & Java Overview: By: Mr. Asyran Zarizi Bin AbdullahDocument45 pagesNetwork Theory & Java Overview: By: Mr. Asyran Zarizi Bin AbdullahSTAR BOY100% (1)
- UNIT 1: Database SystemsDocument25 pagesUNIT 1: Database SystemsAnonymous FKWVgNnSjoNo ratings yet
- Hi! We Are Valtech - Absolunet: Ecommerce IntelligenceDocument21 pagesHi! We Are Valtech - Absolunet: Ecommerce IntelligenceJuan David PerafánNo ratings yet
- IFMIS IT Supervisor Training ManualDocument14 pagesIFMIS IT Supervisor Training ManualAnimaw Abebe TarikuNo ratings yet
- Question Bank - (Unit-2,3,4) PDFDocument27 pagesQuestion Bank - (Unit-2,3,4) PDFAnurag KumarNo ratings yet
- Click and Play Intuitively, Make Your Media Alive: NSA221 NSA221Document4 pagesClick and Play Intuitively, Make Your Media Alive: NSA221 NSA221FranzzNo ratings yet
- Prodly Moover User GuideDocument81 pagesProdly Moover User GuideDiderNo ratings yet
- CHP 12Document48 pagesCHP 12Aqsa NoumanNo ratings yet
- Windev 24 HFSQL PDFDocument24 pagesWindev 24 HFSQL PDFw_mahmudNo ratings yet
- PolyWorksPlug-in (Ai) Leica Absolute ScannerDocument9 pagesPolyWorksPlug-in (Ai) Leica Absolute ScannertiborNo ratings yet
- Two-step picking process in SAP-WMDocument15 pagesTwo-step picking process in SAP-WMSubhojit BanerjeeNo ratings yet
- 20537B - Configuring and Operating A Hybrid Cloud With Microsoft Azure Stack - Skillpipe PDFDocument40 pages20537B - Configuring and Operating A Hybrid Cloud With Microsoft Azure Stack - Skillpipe PDFaruna_hNo ratings yet
- PassLeader AWS Certified DevOps Engineer - Professional Exam Dumps (1-20)Document6 pagesPassLeader AWS Certified DevOps Engineer - Professional Exam Dumps (1-20)abhiNo ratings yet
- E Waste Guidelines Partnership 2015Document52 pagesE Waste Guidelines Partnership 2015Razvan MicanNo ratings yet
- Learning ObjectivesDocument8 pagesLearning Objectivess11032944No ratings yet
- Alice Francis RichardDocument3 pagesAlice Francis Richardapi-3807268No ratings yet
- Configure Yard Management in SAP WMDocument4 pagesConfigure Yard Management in SAP WMAnil KumarNo ratings yet
- Career Path to Chief Information Security OfficerDocument1 pageCareer Path to Chief Information Security OfficeradyanganefiNo ratings yet
- Blood Bank and Donor Management System-Documentation-3Document83 pagesBlood Bank and Donor Management System-Documentation-3CSE-040-Priyanka.MNo ratings yet
- Migration Audit ICAI ReportDocument67 pagesMigration Audit ICAI ReportRavikiran Dhuraji100% (1)
- Ab Initio EME ConceptsDocument66 pagesAb Initio EME ConceptsPindiganti100% (3)
- Install Guide Open Stack UbuntuDocument153 pagesInstall Guide Open Stack UbuntuSurfer1978No ratings yet
- Privacy PolicyDocument5 pagesPrivacy Policyartespastelesfacilencasa artespastelesfacilencasaNo ratings yet
- Ebay PDFDocument21 pagesEbay PDFKOUSHIK DEYNo ratings yet
- Summary of The Subtle Art of Not Giving A F*ck: A Counterintuitive Approach to Living a Good Life by Mark Manson: Key Takeaways, Summary & Analysis IncludedFrom EverandSummary of The Subtle Art of Not Giving A F*ck: A Counterintuitive Approach to Living a Good Life by Mark Manson: Key Takeaways, Summary & Analysis IncludedRating: 4.5 out of 5 stars4.5/5 (38)
- Crushing It!: How Great Entrepreneurs Build Their Business and Influence-and How You Can, TooFrom EverandCrushing It!: How Great Entrepreneurs Build Their Business and Influence-and How You Can, TooRating: 5 out of 5 stars5/5 (887)
- The Millionaire Fastlane, 10th Anniversary Edition: Crack the Code to Wealth and Live Rich for a LifetimeFrom EverandThe Millionaire Fastlane, 10th Anniversary Edition: Crack the Code to Wealth and Live Rich for a LifetimeRating: 4.5 out of 5 stars4.5/5 (85)
- 12 Months to $1 Million: How to Pick a Winning Product, Build a Real Business, and Become a Seven-Figure EntrepreneurFrom Everand12 Months to $1 Million: How to Pick a Winning Product, Build a Real Business, and Become a Seven-Figure EntrepreneurRating: 4 out of 5 stars4/5 (2)
- Creative Personal Branding: The Strategy To Answer What's Next?From EverandCreative Personal Branding: The Strategy To Answer What's Next?Rating: 4.5 out of 5 stars4.5/5 (3)
- Without a Doubt: How to Go from Underrated to UnbeatableFrom EverandWithout a Doubt: How to Go from Underrated to UnbeatableRating: 4 out of 5 stars4/5 (23)
- Creating Competitive Advantage: How to be Strategically Ahead in Changing MarketsFrom EverandCreating Competitive Advantage: How to be Strategically Ahead in Changing MarketsRating: 5 out of 5 stars5/5 (2)
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Anything You Want: 40 lessons for a new kind of entrepreneurFrom EverandAnything You Want: 40 lessons for a new kind of entrepreneurRating: 5 out of 5 stars5/5 (46)
- The Science of Positive Focus: Live Seminar: Master Keys for Reaching Your Next LevelFrom EverandThe Science of Positive Focus: Live Seminar: Master Keys for Reaching Your Next LevelRating: 5 out of 5 stars5/5 (51)
- Summary: Who Not How: The Formula to Achieve Bigger Goals Through Accelerating Teamwork by Dan Sullivan & Dr. Benjamin Hardy:From EverandSummary: Who Not How: The Formula to Achieve Bigger Goals Through Accelerating Teamwork by Dan Sullivan & Dr. Benjamin Hardy:Rating: 5 out of 5 stars5/5 (2)
- What Self-Made Millionaires Do That Most People Don't: 52 Ways to Create Your Own SuccessFrom EverandWhat Self-Made Millionaires Do That Most People Don't: 52 Ways to Create Your Own SuccessRating: 4.5 out of 5 stars4.5/5 (24)
- Summary of Zero to One: Notes on Startups, or How to Build the FutureFrom EverandSummary of Zero to One: Notes on Startups, or How to Build the FutureRating: 4.5 out of 5 stars4.5/5 (100)
- Transformed: Moving to the Product Operating ModelFrom EverandTransformed: Moving to the Product Operating ModelRating: 4 out of 5 stars4/5 (1)
- 24 Assets: Create a digital, scalable, valuable and fun business that will thrive in a fast changing worldFrom Everand24 Assets: Create a digital, scalable, valuable and fun business that will thrive in a fast changing worldRating: 5 out of 5 stars5/5 (19)
- Summary: Choose Your Enemies Wisely: Business Planning for the Audacious Few: Key Takeaways, Summary and AnalysisFrom EverandSummary: Choose Your Enemies Wisely: Business Planning for the Audacious Few: Key Takeaways, Summary and AnalysisRating: 4.5 out of 5 stars4.5/5 (3)
- Built to Serve: Find Your Purpose and Become the Leader You Were Born to BeFrom EverandBuilt to Serve: Find Your Purpose and Become the Leader You Were Born to BeRating: 5 out of 5 stars5/5 (23)
- Your Next Five Moves: Master the Art of Business StrategyFrom EverandYour Next Five Moves: Master the Art of Business StrategyRating: 5 out of 5 stars5/5 (794)
- AI Money Machine: Unlock the Secrets to Making Money Online with AIFrom EverandAI Money Machine: Unlock the Secrets to Making Money Online with AINo ratings yet
- How to Prospect, Sell and Build Your Network Marketing Business with StoriesFrom EverandHow to Prospect, Sell and Build Your Network Marketing Business with StoriesRating: 5 out of 5 stars5/5 (21)
- Don't Start a Side Hustle!: Work Less, Earn More, and Live FreeFrom EverandDon't Start a Side Hustle!: Work Less, Earn More, and Live FreeRating: 4.5 out of 5 stars4.5/5 (30)
- The Corporate Startup: How established companies can develop successful innovation ecosystemsFrom EverandThe Corporate Startup: How established companies can develop successful innovation ecosystemsRating: 4 out of 5 stars4/5 (6)
- SYSTEMology: Create time, reduce errors and scale your profits with proven business systemsFrom EverandSYSTEMology: Create time, reduce errors and scale your profits with proven business systemsRating: 5 out of 5 stars5/5 (48)
- Summary of The 33 Strategies of War by Robert GreeneFrom EverandSummary of The 33 Strategies of War by Robert GreeneRating: 3.5 out of 5 stars3.5/5 (20)
- Rich Dad's Before You Quit Your Job: 10 Real-Life Lessons Every Entrepreneur Should Know About Building a Multimillion-Dollar BusinessFrom EverandRich Dad's Before You Quit Your Job: 10 Real-Life Lessons Every Entrepreneur Should Know About Building a Multimillion-Dollar BusinessRating: 4.5 out of 5 stars4.5/5 (407)
- Summary of The Lean Startup: How Today's Entrepreneurs Use Continuous Innovation to Create Radically Successful Businesses by Eric RiesFrom EverandSummary of The Lean Startup: How Today's Entrepreneurs Use Continuous Innovation to Create Radically Successful Businesses by Eric RiesRating: 4.5 out of 5 stars4.5/5 (99)
- Level Up: How to Get Focused, Stop Procrastinating, and Upgrade Your LifeFrom EverandLevel Up: How to Get Focused, Stop Procrastinating, and Upgrade Your LifeRating: 5 out of 5 stars5/5 (22)
- Expert Secrets: The Underground Playbook for Creating a Mass Movement of People Who Will Pay for Your AdviceFrom EverandExpert Secrets: The Underground Playbook for Creating a Mass Movement of People Who Will Pay for Your AdviceRating: 5 out of 5 stars5/5 (363)
- Company Of One: Why Staying Small Is the Next Big Thing for BusinessFrom EverandCompany Of One: Why Staying Small Is the Next Big Thing for BusinessRating: 3.5 out of 5 stars3.5/5 (14)
- Invention: A Life of Learning Through FailureFrom EverandInvention: A Life of Learning Through FailureRating: 4.5 out of 5 stars4.5/5 (28)