Professional Documents
Culture Documents
Dukes 2013
Uploaded by
Sajid Mohy Ul DinCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Dukes 2013
Uploaded by
Sajid Mohy Ul DinCopyright:
Available Formats
A Case Study on Web Application Security Testing
with Tools and Manual Testing
LaShanda Dukes, Xiaohong Yuan, Francis Akowuah
Department of Computer Science
North Carolina Agricultural & Technical State University
Greensboro, United States
ldukes@aggies.ncat.edu, xhyuan@ncat.edu, fakowua@aggies.ncat.edu
AbstractWeb application security has become a big issue
because of common vulnerabilities found in web applications.
This paper illustrates a case study on conducting security testing
on an example application, Tunestore. The example application
was tested using a number of tools such as Paros, WebScarab,
JBroFuzz, Acunetix, and Fortify. Manual testing was also
conducted. The testing results of different tools and manual
testing are compared and discussed. Our case study shows
manual testing is very important since some vulnerability types
can only be found through manual testing and testers
observations, and it is important to utilize a variety of tools as
well as conduct careful manual testing in order to find the most
number of vulnerabilities in a web application. Based on this case
study, hands-on labs can be developed for teaching web security,
software security testing, and other topics.
I. INTRODUCTION
Web applications today are highly functional, and rely
upon a two-way flow of information between the server and
browser. Security becomes a big issue because no one wants to
use a web application if they believe their information will be
disclosed to unauthorized parties [1]. Vulnerabilities
commonly found in web applications include injection, crosssite scripting, cross-site request forgery, security
misconfiguration, broken authentication and session
management, and more.
Penetration testing and static code analysis may be used to
assess the vulnerabilities of web applications. Penetration
testing is a method of security testing through the simulation of
an attack. Static code analysis, also known as source code
analysis is a code review process that examines the softwares
source code for common coding errors and defects without
execution [3].
This case study uses an example web application,
Tunestore to conduct security testing. It illustrates web
application security testing using tools and manual testing. The
tools used to conduct testing on Tunestore are Paros,
WebScarab, JBroFuzz, Fortify, and Acunetix. Our case study
shows manual testing is very important since some
vulnerability types can only be found through manual testing
and testers observations, and it is important to utilize a variety
of tools as well as conduct careful manual testing in order to
find the most number of vulnerabilities in a web application.
Based on this case study, hands-on labs can be developed to
This work is partially supported by Department of Education under grant
P120A090049 and NSF under grant HRD-1137516. Any opinions, findings,
and conclusions or recommendations expressed in this material are those of
the author(s) and do not necessarily reflect the views of the National Science
Foundation and Department of Education.
978-1-4799-0053-4/13/$31.00 2013 IEEE
teach about web application vulnerabilities, software security
testing, and other topics.
This paper is organized as follows: Section II discusses
some common web application vulnerabilities. Section III
describes the tools we used for web application security
testing, Section IV gives a description of the example
application used to conduct security testing, and Section V and
VI discuss the results from testing the example application
using tools as well as through manual testing. Section VII
provides further discussion on the testing results and Section
VIII concludes the paper.
II.
COMMON WEB APPLICATION VULNERABILITIES
This section discusses common vulnerabilities of web
applications. They include SQL injection, cross-site scripting,
cross-site request forgery, broken authentication and session
management. These vulnerabilities were listed in OWASPs
Top 10 Project as among the Top 10 critical web application
security risks [4]. They also appear significantly in the Web
Hacking Incident Database (WHID) [5]. A brief discussion is
provided here. A more detailed discussion can be found in [6].
SQL injection is a vulnerability type where an application
accepts malicious scripts that are later parsed and executed.
The fundamental way of attack involves the direct insertion of
code into user-input variables that are concatenated with SQL
commands and executed. A rare and indirect way of attack is
where the malicious code is injected into strings that are
destined for storage in a table or as metadata. Subsequently
when the stored string is concatenated into a dynamic SQL
command the malicious code is executed. An attacker can
anonymously read and modify data contained in a database as
well as take full control of the server by exploiting the SQL
vulnerability.
An application is vulnerable to cross-site scripting (XSS)
vulnerabilities when it takes untrusted data and sends it to a
web browser without proper validation and escaping. This
allows attackers to embed malicious JavaScript, VBScript,
ActiveX, HTML or Flash into a dynamic page to trick the user,
executing the script on his machine in order to gather data,
hijack sessions, redirect users to a malicious site or deface the
website. Furthermore, a successful attack may result in the
compromising of private information, manipulation or theft of
cookies, creation of requests that can be mistaken for those of a
valid user. It might also cause the execution of malicious code
on the end user systems. Three types of XSS exist. The first
one is Reflected XSS, in which dynamic web pages take text
submitted by a client or user and simply renders this text back
to user within its response. The second type is Stored XSS. It
occurs where some malicious user-submitted data is stored in a
database to be used in the creation of pages that will be served
to other users later. Thus, visitors of the web page fall victim
for this attack. Lastly, Local XSS exploit targets vulnerabilities
that exist within the webpage code itself. Usually, this happens
when Document Object Model (DOM) is wrongly used in
JavaScript. As a result, opening another web page with
malicious JavaScript code in it at the same time might actually
alter the code in the first page on the local system.
Broken authentication and session management is the
vulnerability whereby the application does not implement its
authentication and session management functions correctly.
The attacker uses leaks or flaws such as exposed accounts,
session IDs and passwords in the authentication or session
management function to impersonate users. When successful,
an attacker is able to do anything the victim could do. The
situation worsens when the administrator is the victim.
Cross-site request forgery usually occurs where HTTP
cookies are primarily used to transmit session tokens. Where
precaution is not taken against the misuse of the token, an
attacker can trick an authenticated user to perform actions of
his (attacker) choosing. Victims are forced to change data and
perform functions they are allowed or authorized to do
Insecure direct object reference is a common web
application vulnerability regarding access control. This occurs
when an application wrongfully exposes a reference to an
internal implementation object. An attacker, usually an
authorized user, exploits this vulnerability by simply changing
a parameter value that references a system object. This enables
him to access unauthorized objects.
III.
TOOLS USED IN THE CASE STUDY
This section briefly describes the tools used in this case study
which are: Paros, WebScarab, JBroFuzz, Acunetix and
Fortify.
A. Paros
Paros [7] is a free web application vulnerability assessment
tool written in Java by ProofSecure.com. It can be used as a
web spider, vulnerability scanner, proxy, and a fuzzer. The web
spider function is used to discover the content of a website by
parsing a webpage for links to other content, requesting these
pages, and continuing this process recursively. The scanner
function scans the web application to identify common
vulnerabilities such as cross-site scripting, SQL injection,
forms with autocomplete enabled, old versions of files, etc.
Paros can also trap HTTP and HTTPS requests and responses
so they can be modified manually [1, 8].
B. WebScarab
WebScarab [9] is an open-source web application security
testing tool written in Java. The tool is a part of the Open Web
Application Security Project (OWASP) [10]. It can be used for
analyzing applications that communicate with HTTP and
HTTPS protocols. WebScarab operates as an intercepting
proxy, in which the user is allowed to review and modify
intercepted requests that are created by the browser and
responses from the server. Similar to Paros, it can be used as a
web spider to discover the content of a website. The fuzzer
feature of WebScarab allows a user to test a web page by
taking a list of test strings and trying them in the input fields
automatically [11].
C. JBroFuzz
JBroFuzz is a web application fuzzer written in Java and is
a part of the OWASP Project. The fuzzer is for requests made
over HTTP and HTTPS protocols [12]. The fuzzing feature is
used to create a HTTP request to send to the web application.
A fuzzer can be added to a parameter field to add attack
payloads. The payload feature has attack strings of several
vulnerability categories such as Injection, XSS, Integer
Overflow, XPATH Injection, SQL Injection, and more. HTTP
responses are displayed in an output window showing the
payload and the HTTP response status code. The responses of
the web application to the attack strings are also shown. The
graphing feature can generate different types of graphs to
visualize the fuzzing results. There are six types of
graphs/charts: Status Code Pie Chart, Response Time Bar
Chart, Response Size Bar Chart, Jaccard Index, Hamming
Distance, and Response Header.
D. Acunetix
Acunetix is a product of the Acunetix Company [13]. It is a
web vulnerability scanner created to replicate hackers
methodologies to find vulnerabilities in web applications.
Acunetix crawls through the websites to analyze the content
including flash content, SOAP and AJAX. The scanner
includes features such as advanced and in-depth SQL injection
and cross-site scripting testing, penetration tools which
include HTTP Editor and HTTP Fuzzer, and others. The cost
of the tool ranges from $1,000 - $12,995. It has a free trial
version that can only scan for cross-site scripting
vulnerabilities in a web application. In this case study, the free
trial version was used to test the example web application.
E. Fortify
Fortify is a static analysis tool used to find root causes of
security vulnerabilities in source code. Fortify supports a
range of languages, platforms, build environments and
software component APIs. Fortify can detect more than 480
types of software security vulnerabilities among 20 different
languages. The tool displays results sorted by severity of risk
and guidance on how to mitigate the risks [14]. The
demonstration version of the software that comes with the
book Software Security: Building Security In [3] only scans
for SQL injection, buffer overflow, system information leak,
and HTTP response splitting vulnerabilities. In this case study,
the demonstration version of Fortify was used to test the
example web application.
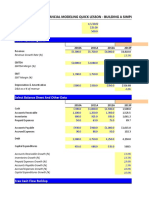
Table 1 summarizes the automated tools used for the case
study.
IV.
THE EXAMPLE APPLICATION
The application used to conduct security testing is the
Tunestore web application developed by Dr. Bei-Tseng Bill
Chus project team from the University of North Carolina at
Charlotte. The Tunestore web application is a .war file installed
on a server on an Ubuntu Virtual Machine to conduct security
testing. Tunestore is an online retail store of songs. A user has
to create an account to gain access to the store and its database
of songs, although users may view the list of songs without
being a registered user. Registered users are able to select
several options within the store: add balance, friends,
profile, CDs, and log out. The add balance option
allows the user to add money to their account by using a credit
card to purchase songs. The friends option allows the user to
add and view friends, as well as accept friend requests. The
profile option provides the user with their username and their
current account balance. The user may also change their
password under the profile option. The CDs option
displays a list of songs the user can buy, send as a gift, or make
a comment under the CD. This option also shows the users
purchased CDs. The log out option logs the user out of their
profile and redirects them to the homepage of the store.
V.
SECURITY TESTING WITH TOOLS
Obsolete File (7): It indicates that miscellaneous
items including files, backup, unused, or obsolete
files exist. If these files contain program source,
information such as server logic or ODBC/JDBC
user IDs and passwords may be revealed since these
file extensions may not be processed by the web
server.
Obsolete File Extended Check (7): It also indicates
that miscellaneous items including files, backup,
unused, or obsolete files exist.
Password Autocomplete in Browser (7): This
vulnerability means the AUTOCOMPLETE attribute
is not disabled in the HTML FORM/INPUT element
containing password type input. Passwords may be
stored in browsers and retrieved.
Session ID in URL rewrite (7): URL rewrite is used
to track user session IDs. The session ID may be
disclosed in the referer header. Besides, the session
ID can be stored in the browsers history or server
logs.
SQL Injection (4): SQL injection is possible. User
parameters submitted will be formulated into a SQL
query for database processing. If the query is built by
simple string concatenation, it is possible to modify
the meaning of the query by carefully crafting the
parameter.
SQL Injection Fingerprinting (4): SQL injection may
be possible.
The Tunestore web application was tested using the five
tools described in Section III. This section describes the
testing results of using these tools.
A. Testing Results with Paros
Using the scanner feature of Paros, 37 potential
vulnerabilities were discovered in the Tunestore web
application. These vulnerabilities are listed below. The
number following the vulnerability refers to the number of
occurrences of the vulnerability.
Table 1. Automated Tools used in the Case Study
Tool
Paros [7]
WebScarab [8]
JBroFuzz [11]
Acunetix [12]
Fortify [13]
Functionalities
Web proxy
Web spider
Automated vulnerability scanner
Manual request with proxy, fuzzer
Web proxy
Web spider
Manual fuzzer
Manual vulnerability scanner
Manual request with web proxy, spider,
fuzzer, history
Automated fuzzing
Graphing
Built-in attack payloads
Automatic client script analyzer
SQL Injection and Cross-site scripting
testing
Fast scanner crawls
Port scans on web servers
Automated vulnerability scanner
Source code analyzer
Cost
Free
Operating System
Linux, Apple Mac OS X, Microsoft Windows
Free
Linux, Apple Mac OS X, Microsoft Windows
Free
Linux, Apple Mac OS X, Microsoft Windows
Commercial
$1,000 $12,995
Microsoft Windows, Microsoft Windows
Server, Microsoft Windows 2008 Server
Commercial
Linux, Microsoft Windows, Mac OS, Oracle
Solaris, HP-UX
Cross-Site Scripting (1): Malicious scripts may be
injected into the browser which can appear to be
genuine content from the original site. These scripts
can be used to execute arbitrary code or steal
customers sensitive information such as user
passwords or cookies.
B. Testing Results with WebScarab
Using the fuzzer and the proxy features of WebScarab, we
discovered potential SQL injection and cross-site scripting
vulnerabilities:
SQL Injection: An input attack file was created
which included SQL injection attack strings. This
attack file was submitted to the WebScarab fuzzer
to test the login page of the Tunestore web
application. Some of the attacks were successful.
Reflected
Cross-Site
Scripting:
Using
WebScarabs fuzzer feature, an input attack file
was created which included cross-site scripting
attack strings to test the login page of the
Tunestore web application. The scripts were
executed showing that the login page has XSS
vulnerabilities.
Stored Cross-Site Scripting: Using WebScarabs
proxy feature, comments submitted by the user
was intercepted and changed to malicious scripts.
The malicious scripts were then saved on the
server, and would be activated when someone
views the comment on the CD.
Other input fields such as those related to the registration,
friend, and add balance options could also be tested using
WebScarab. However, in this case study, those fields were
tested using the manual approach instead of WebScarabs
fuzzer feature.
C. Testing Results with Fortify (the Demonstration Version)
Using Fortify Source Code Analyzer, 30 potential
vulnerabilities were discovered. These vulnerabilities are
listed below. The number following the vulnerability refers to
the number of occurrences of the vulnerability.
SQL Injection (27).
System Information Leak (2): It means system
data or debugging information is revealed, which
can help attackers learn about the system and plan
attacks.
HTTP Response Splitting (1): It means
unvalidated data in HTTP response headers can
enable cache-poisoning, cross-site scripting,
cross-user defacement or hijacking attacks.
D. Testing Results with JBroFuzz and Acunetix
JBroFuzz was first used to test for SQL injection and XSS
vulnerabilities. However, a bug in the tool was discovered. For
some valid SQL injection attack strings, JBroFuzz generated
invalid requests to the web application, and thus could not
identify the SQL injection vulnerability. Because of this bug,
JBroFuzz was no longer used to test for other vulnerabilities in
the Tunestore web application. However, the payloads
embedded in JBroFuzz were used in manual testing to
discover some of the vulnerabilities in Tunestore.
Using Acunetix (free edition), cross-site scripting
vulnerabilities were discovered.
VI.
MANUAL TESTING
Using manual testing, authentication, access control,
injection, cross-site scripting, cross-site request forgery, and
integer overflow vulnerabilities were discovered. Some of the
vulnerabilities confirm those found through automated tools.
Others were not reported by the tools.
The vulnerabilities found through manual testing which
confirm those reported by the automated tools are the
following:
SQL Injection This allows illegitimate users to
login as a legitimate user.
Reflected Cross-Site Scripting Malicious scripts
may be injected into input fields of the login page
and be executed.
Stored Cross-Site Scripting Using WebScarabs
proxy feature, a malicious script can be stored in
the comment field.
Using manual testing, we were able to confirm some of the
vulnerabilities reported by some of the tool. Acunetix indicated
cross-site scripting vulnerabilities in the login page of the
Tunestore web application. Although, the tool reported true
positives, manual testing also revealed cross-site scripting
vulnerabilities on the comment page. Malicious scripts were
stored into the comment field and stored in the database. This
indicates a typical case of stored cross-site scripting (XSS)
vulnerability.
The vulnerabilities found through manual testing which are
not reported by the automated tools are the following:
The application allows users to register with weak
passwords. It does not have a minimum or
maximum length for passwords. It does not give
users feedback on password strength. This
vulnerability can cause an attacker to carry out
brute force attacks and enumerate existing users
on the system.
The application does not have a lockout policy for
failed login attempts. This makes the application
have a high risk of brute force attacks.
Unencrypted credentials are transmitted over
HTTP protocol.
Forgot password feature was not implemented.
Registered users will not be able to access the
system if they do not remember their passwords.
The application implements a stay logged in
feature. This makes the application have a high
risk of session hijacking.
Insecure storage of credentials. Username and
passwords stored in the database are not
encrypted. As a result, an attacker can eavesdrop
on the network and gain access users
unauthorized information. Thus, an attacker is
able to gain access to the database to view users
data.
Horizontal privilege escalation The application
allows users to view friends CDs and view
comments on CDs without logging into the
application.
Cross-Site Request Forgery Malicious scripts
may be injected into the comment field of
Tunestore which includes a crafted link. When a
victim clicks on the link, it causes some actions to
occur, such as logging the victim out, etc.
Integer Overflow The submission of large
numbered values will overflow the balance field
on the account. The add balance option will no
longer operate correctly.
An attacker can add an amount to the add
balance feature in their profile by using SQL
injection techniques. Hence, an attacker can
successfully create a new user account with a
substantial amount of money added to their
account without providing valid credit card
information. As a result, the attacker is able to
purchase CDs for free. This vulnerability was
discovered through examining the source code.
Insecure Direct Object Reference. Requests for
protected resources, in this case the music files,
are made directly to the static resources, which
are located within the web root of the server. The
music filenames are predictable. The last names
of the artists are used. Changing the values in the
download link permits a user to download any
song from Tunestore without purchasing them.
VII. DISCUSSION
Our case study shows that Tunestore is a good example
application for teaching students about web security. It can be
used to demonstrate various web application vulnerabilities to
the students. Limited by our academic environment, we do not
have the full versions of Fortify and Acunetix. Therefore the
testing results from the demonstration or the trial version of
the tools are very limited in this study. Universities can apply
for the Hewlett-Packard Company Educational Software
License Agreement to receive the full version of Fortify for
free for educational purposes. However, we could not get the
full version of Fortify because our university did not agree
with the user agreement for the license for the Fortify
software.
The web spidering and proxy features of Paros and
WebScarab are very useful for web application testing. The
web spidering functions allow testers to understand the
content and structure of the web application. The proxy allows
testers to intercept and modify requests and responses
transmitted between the client and server to conduct attacks.
The scanner feature of Paros is quite limited. It does report
some main vulnerabilities such as SQL injection, cross-site
scripting, and session ID in URL rewrite, etc. WebScarabs
fuzzer feature can be very useful because a large number of
attack strings can be submitted to test the application
automatically. Some of the manual testing conducted in this
case study, such as testing for buffer overflow, integer
overflow vulnerabilities, could have been done using
WebScarabs fuzzer feature. JBroFuzz does not have good
documentation on how to use the tool. From our use of the
tool, we discovered a bug in the tool, and did not think the tool
worked properly as it is supposed to. However, the attack
types and payloads embedded in the tool can be useful. The
payloads can be used for manual testing, or testing with
WebScarabs fuzzer feature.
Manual testing discovered most of the vulnerabilities
especially the design flaws. Some of them are the same as
those found using Paros, Fortify, Acunetix, for example, SQL
injection, and cross-site scripting vulnerabilities. Most of the
authentication and access control vulnerabilities can only be
found through manual testing based on testers observations.
Therefore it is important to utilize a variety of tools as well as
conduct careful manual testing in order to find the most
number of vulnerabilities in a web application.
VIII. CONCLUSION
This paper describes a case study of testing for security
vulnerabilities of an example application Tunestore. It
provides an overview of web application security testing tools
such as Paros, WebScarab, JBroFuzz, Acunetix, and Fortify. It
presents the security vulnerabilities found within an
application by using these tools, and by manual testing. While
commercial tools are not easily available in an academic
environment, open source tools can be used to conduct
security testing with limited results. Our case study shows
manual testing is very important since some vulnerability
types can only be found through manual testing and testers
observations. It is important to utilize a variety of tools as well
as conduct careful manual testing in order to find the most
number of vulnerabilities in a web application. Based on this
case study, hands-on labs can be developed for teaching web
security, software security testing, and other topics.
REFERENCES
[1] Studdard, D., & Pinto, M. The Web Application Hackers
Handbook: Discovering and Exploiting Security Flaws,
Wiley Publishing: Indianapolis, Indiana, 2008.
[2] The Open Web Application Security Project, Testing:
Introduction
and
Objectives,
2012
https://www.owasp.org/index.php/Testing:_Introduction_
and_objectives, retrieved on November 6, 2012.
[3] McGraw, G. Software Security: Building Security In.
Pearson Education: Boston, Massachusetts, 2006.
[4] The Open Web Application Security Project, OWASP,
Top
Ten
2010
Main,
2010,
www.owasp.org/index.php/Top_10_2010-Main, retrieved
on January 13, 2013.
[5] Web-Hacking-Incident-Database. Retrieved on Jan 6,
2013
http://projects.webappsec.org/w/page/13246995/WebHacking-Incident-Database
[6] Top 10 2010. Retrieved on January 10, 2013:
https://www.owasp.org/index.php/Top_10_2010-Main
[7] Paros, Paros for web application security assessment,
2004,
http://www.parosproxy.org/,
retrieved
on
November 6, 2012.
[8] Paros, User
Guide for
Paros v2.x, 2003,
http://www.parosproxy.org/paros_user_guide.pdf,
retrieved on November 6, 2012.
[9] The Open Web Application Security Project, Category:
OWASP
WebScarab
Project,
2012,
https://www.owasp.org/index.php/Category:OWASP_We
bScarab_Project, retrieved on November 6, 2012.
[10] The Open Web Application Security Project, OWASP,
2012, www.owasp.org, retrieved on November 6, 2012.
[11] Dustin, E., Nelson, L., Wysopal, C., Zovi, D. The Art of
Software Security Testing: Identifying Software Security
Flaws. Symantec Corporation: Upper Saddle River, New
Jersey, 2007.
[12] The Open Web Application Security Project, JBroFuzz,
2012,
https://www.owasp.org/index.php/JBroFuzz,
retrieved on November 6, 2012.
[13] Acunetix Ltd., Acunetix Web Application Security,
www.acunetix.com/vulnerability-scanner/, retrieved on
November 6, 2012.
[14] HP Enterprise Security, HP Fortify Static Code Analyzer,
2012, http://www.hpenterprisesecurity.com/products/hpfortify-software-security-center/hp-fortify-static-codeanalyzer/, retrieved on November 6, 2012.
You might also like
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Recent Advances in Liquid Organic Hydrogen Carriers: An Alcohol-Based Hydrogen EconomyDocument15 pagesRecent Advances in Liquid Organic Hydrogen Carriers: An Alcohol-Based Hydrogen EconomySajid Mohy Ul Din100% (1)
- Intrinsic and Extrinsic Motivation For University Staff Satisfaction: Confirmatory Composite Analysis and Confirmatory Factor AnalysisDocument27 pagesIntrinsic and Extrinsic Motivation For University Staff Satisfaction: Confirmatory Composite Analysis and Confirmatory Factor AnalysisSajid Mohy Ul DinNo ratings yet
- Submission Date: 10-Mar-2021 07:58AM (UTC-0800) Submission ID: 1529370323 File Name: Essay - Docx (29.22K) Word Count: 1371 Character Count: 8583Document7 pagesSubmission Date: 10-Mar-2021 07:58AM (UTC-0800) Submission ID: 1529370323 File Name: Essay - Docx (29.22K) Word Count: 1371 Character Count: 8583Sajid Mohy Ul DinNo ratings yet
- Wall Street Prep - Financial Modeling Quick Lesson - Building A Simple Discounted Cash Flow ModelDocument6 pagesWall Street Prep - Financial Modeling Quick Lesson - Building A Simple Discounted Cash Flow ModelSajid Mohy Ul DinNo ratings yet
- Insurance Activity and Economic Performance: Fresh Evidence From Asymmetric Panel Causality TestsDocument20 pagesInsurance Activity and Economic Performance: Fresh Evidence From Asymmetric Panel Causality TestsSajid Mohy Ul DinNo ratings yet
- ChartDocument1 pageChartSajid Mohy Ul DinNo ratings yet
- Wall Street Prep - Financial Modeling Quick Lesson - Building A Simple Discounted Cash Flow ModelDocument6 pagesWall Street Prep - Financial Modeling Quick Lesson - Building A Simple Discounted Cash Flow ModelSajid Mohy Ul DinNo ratings yet
- The Impact of Corporate Social Responsibility On Firms' Financial Performance in South AfricaDocument23 pagesThe Impact of Corporate Social Responsibility On Firms' Financial Performance in South AfricaSajid Mohy Ul DinNo ratings yet
- Institutional Quality and Initial Public Offering Underpricing: Evidence From Hong KongDocument12 pagesInstitutional Quality and Initial Public Offering Underpricing: Evidence From Hong KongSajid Mohy Ul DinNo ratings yet
- Linking Anthropology: History ClothingDocument5 pagesLinking Anthropology: History ClothingSajid Mohy Ul DinNo ratings yet
- Surroca PDFDocument28 pagesSurroca PDFGuillem CasolivaNo ratings yet
- An Inter Disciplinary Review of The Literature On Mental Illness Disclosure in The Workplace Implications For Human Resource ManagementDocument38 pagesAn Inter Disciplinary Review of The Literature On Mental Illness Disclosure in The Workplace Implications For Human Resource ManagementSajid Mohy Ul DinNo ratings yet
- SHWMDocument24 pagesSHWMVineet RathoreNo ratings yet
- A Theoretical Basis For Innovation, Institutions and Insurance Penetration NexusDocument13 pagesA Theoretical Basis For Innovation, Institutions and Insurance Penetration NexusSajid Mohy Ul DinNo ratings yet
- U.S. Ssecurity Ppolicy Iin Ssouth Aasia Since 9/11 - Cchallenges Aand Implications Ffor Tthe FfutureDocument16 pagesU.S. Ssecurity Ppolicy Iin Ssouth Aasia Since 9/11 - Cchallenges Aand Implications Ffor Tthe FfutureSajid Mohy Ul DinNo ratings yet
- Colloids and Surfaces A: Physicochemical and Engineering AspectsDocument10 pagesColloids and Surfaces A: Physicochemical and Engineering AspectsSajid Mohy Ul DinNo ratings yet
- File000001 999062024Document1 pageFile000001 999062024Sajid Mohy Ul DinNo ratings yet
- Student Teacher Challenges Using The Cognitive Load Theory As An Explanatory Lens PDFDocument16 pagesStudent Teacher Challenges Using The Cognitive Load Theory As An Explanatory Lens PDFSajid Mohy Ul DinNo ratings yet
- Frequency Changes in AC Systems Connected To DC Grids: Impact of AC vs. DC Side EventsDocument5 pagesFrequency Changes in AC Systems Connected To DC Grids: Impact of AC vs. DC Side EventsSajid Mohy Ul DinNo ratings yet
- In The University of Chakwal: Form of Application For The Use of Candidates For AppointmentDocument6 pagesIn The University of Chakwal: Form of Application For The Use of Candidates For AppointmentSajid Mohy Ul DinNo ratings yet
- Insurance Growth Nexus A Comparative Analysis With Multiple Insurance Proxies PDFDocument20 pagesInsurance Growth Nexus A Comparative Analysis With Multiple Insurance Proxies PDFSajid Mohy Ul DinNo ratings yet
- Can 2017Document29 pagesCan 2017Sajid Mohy Ul DinNo ratings yet
- Marceau 2009Document36 pagesMarceau 2009Sajid Mohy Ul DinNo ratings yet
- Jacob 2008Document37 pagesJacob 2008Sajid Mohy Ul DinNo ratings yet
- (Doi 10.1007/978-981!10!8147-7 - 4) Tan, Lee-Ming Lau Poh Hock, Evan Tang, Chor Foon - Finance & Economics Readings - Management of Mobile Financial Services-Review and Way ForwardDocument19 pages(Doi 10.1007/978-981!10!8147-7 - 4) Tan, Lee-Ming Lau Poh Hock, Evan Tang, Chor Foon - Finance & Economics Readings - Management of Mobile Financial Services-Review and Way ForwardSajid Mohy Ul DinNo ratings yet
- A New Era For Women? Some Reflections On Blind Spots of ICT-based Development Projects For Women's Entrepreneurship and EmpowermentDocument16 pagesA New Era For Women? Some Reflections On Blind Spots of ICT-based Development Projects For Women's Entrepreneurship and EmpowermentSajid Mohy Ul DinNo ratings yet
- Mobile Banking A Potential CADocument32 pagesMobile Banking A Potential CASajid Mohy Ul DinNo ratings yet
- And 1992Document14 pagesAnd 1992Sajid Mohy Ul DinNo ratings yet
- Study On Technologies For Financial Inclusion in BRICSDocument17 pagesStudy On Technologies For Financial Inclusion in BRICSSajid Mohy Ul DinNo ratings yet
- Ijse 05 2017 0194Document23 pagesIjse 05 2017 0194Sajid Mohy Ul DinNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)