Professional Documents
Culture Documents
Vehicle Monitoring System
Uploaded by
Anirudha MhaseCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Vehicle Monitoring System
Uploaded by
Anirudha MhaseCopyright:
Available Formats
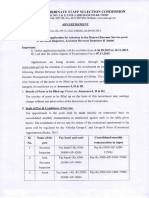
VEHICLE MONITORING SYSTEM
INDEX
CONTENTS PAGE No.
Certificate
Acknowledgement i
Preface 3
List of Figures 4
List of symbols and Abbreviations 4
Abstract 5
Chapter-1 Introduction 6
Chapter-2 Literature Survey 8
2.1 Smart Card 9
2.2 Radio Frequency Identification 16
2.3 Pollution Sensor 21
2.4 Wireless communication using GSM 23
2.5 Microcontroller 24
Chapter-3 Block Diagram and Methodology 28
Block Diagram 29
3.1 Vehicle unit 30
3.2 Server unit 35
3.3 Traffic Signal unit 36
Chapter-4 Hardware Design 37
4.1 Power supply 38
4.2 Oscillator Circuit 39
E&TC Department R.S.C.O.E, PUNE 1|Page
VEHICLE MONITORING SYSTEM
4.3 Reset Circuit 40
4.4 LCD interfacing to microcontroller 41
4.5 Relay Interfacing and Driver 42
Circuitry
4.6 Memory Interfacing 43
4.7 MAX-232 interfacing to 45
microcontroller
4.8 Pollution sensor interfacing to 46
microcontroller
Chapter-5 Software Design 47
5.1 WinAVRGCC 48
5.2 AVR studio 49
5.3 PonyProg 49
5.4 Visual Basic 49
5.5 ExpressPCB 52
Chapter-6 Flowchart 53
Chapter-7 Testing and troubleshooting 57
Chapter-8 Conclusion and Future scope 59
Annexure
Annexure-I Circuit Diagram 62
Annexure-II PCB Art Work and layout 63
Annexure-III Component list and Total cost 67
Annexure-IV Datasheets 69
E&TC Department R.S.C.O.E, PUNE 2|Page
VEHICLE MONITORING SYSTEM
PREFACE
Nowadays vehicle monitoring and traffic control have become very tedious and
inefficient job due to many loop holes present in the existing system. Due to Human interaction
at each and every phase reduces the efficiency of the system. Also because of greediness of
human nature there is a lot of corruption. Absence of central controlling server to maintain
REAL TIME DATABASE which can be really useful to monitor each and every vehicle and
driver. As number of vehicles have increased drastically it is practically impossible to check
every vehicle for pollution control. Moreover, due to insufficient man power it is impossible to
monitor Traffic violation viz. Signal breaking, driving without Valid License etc. Hence, the
above discussion has inspired the development of VEHICLE MONITORING SYSTEM.
CHAPTER 1: INTRODUTION
This chapter clearly distinguishes the current existing system and proposed system to
monitor the vehicle and also gives brief description about the inspired system.
CHAPTER 2: LITERATURE SURVEY
This chapter is based on the extensive survey which was carried out before proceeding to
design the system. It covers all the different types of smart cards, RFID reader, RFID tags,
Pollution sensor available in the market and there brief description
CHAPTER 3: BLOCK DIAGRAM AND METHODOLY
After the survey Block diagram for the system was prepared and methodology to be used
was finalized. This chapter covers the same with detailed description and cause of the block used
in the system
CHAPTER 4: HARDWARE DESIGN
This chapter covers the detailed description and design of the circuit diagram of the
system. It also covers selection criteria and interfacing of the components to microcontroller
CHAPTER 5: SOFTWARE DESIGN
This chapter gives the idea about different software utilized to program the
microcontroller and to prepare GUI for the user.
CHAPTER 6: FLOWCHART
Flowchart is the graphical representation of the flow of program. Hence, this chapter
describes the same.
CHAPTER-7: TESTING AND TROUBLESHOOTING
This chapter gives the detailed description of various faults which occurred during the
design of the system and provides with necessary troubleshooting method
E&TC Department R.S.C.O.E, PUNE 3|Page
VEHICLE MONITORING SYSTEM
List of Figures
Figure. 1 Classification of chip cards Page No. 12
Figure. 2 RFID reader setup Page No. 16
Figure. 3 Block Diagram Page No. 30
Figure. 4 Smart Card Page No. 31
Figure. 5 Smart Card Connector Page No. 32
Figure. 6 RFID Tag Page No. 34
Figure. 7 MQ-7 Pollution sensor Page No. 34
Figure. 8 LCD Page No. 35
Figure. 9 Oscillator Circuit Page No. 39
Figure. 10 Reset Circuit Page No. 40
Figure. 11 Interfacing Diagram of LCD Page No. 41
Figure. 12 Relay Driver Circuitry Page No. 43
Figure. 13 Interfacing diagram of memory Page No. 44
Figure. 14 Interfacing diagram of MAX-232 Page No. 45
Figure. 15 Activation of pollution sensor Page No. 46
List of abbreviations and symbol
1. RFID Radio Identification Device
2. ISP In system Programming
3. GCC GNU cross compiler
4. GSM Global System for Mobile Communication
5. AT commands Attention Commands
6. GUI Graphical User Interface
7. LCD Liquid Crystal Display
E&TC Department R.S.C.O.E, PUNE 4|Page
VEHICLE MONITORING SYSTEM
ABSTRACT
Driving license from the competent authority is mandatory for driving any
automated vehicle which confirms the suitability of the vehicle with respect to pollution,
condition of the vehicle, its registration, and last but not least the capability of driver to drive the
vehicle. It is necessary to check the license from the competent authority from time to time so as
to avoid driving of unauthorized vehicles by the unauthorized persons who may lead to road
accidents and increase in the pollution level. However, due to tremendous increase in the number
of vehicles it has become impossible to check the validity of license and the vehicles.
In view of the above problems, it is felt necessary to design Sophisticated
Multiple Aid Remote Tool (SMART) electronic device which will prevent the vehicle from
starting without valid license issued by the competent authority. The device will also display the
present status of the pollution level of the vehicle and the same will be intimated to competent
authority in case of non-confirmatory.
The device consists of two subsystems, one placed in the vehicle and other
placed in the traffic control room. The system placed in the vehicle consists of smart card
reader, display, RFID reader while the system in the traffic control room consist GSM modem
and PC. When the driver wants to drive the vehicle, then he/she has to insert the smart card into
the smart card reader. The inserted smart card will be online authenticated from the traffic
control room using wireless communication (GSM). The vehicle will start, if license is valid.
Vehicle will also contain the pollution sensors to indicate the current pollution level of exhaust.
When the smart card is inserted, the traffic control room will come to know about relevant
information about the vehicle using wireless communication like insurance, road tax payment
details, fine collection details etc. If the data is non-confirmatory it will send the relevant
intimation to the vehicle driver which will help the driver to take necessary actions
E&TC Department R.S.C.O.E, PUNE 5|Page
VEHICLE MONITORING SYSTEM
CHAPTER1
INTRODUCTION
E&TC Department R.S.C.O.E, PUNE 6|Page
VEHICLE MONITORING SYSTEM
Nowadays vehicle monitoring and traffic control have become very tedious and
inefficient job due to many loop holes, present in the existing system.
Loop Holes In the existing system
• Human interaction at each and every phase reduces the efficiency of the system.
• Due to greediness of human nature there is a lot of corruption
• Absence of central controlling server to maintain REAL TIME DATABASE.
• Due to pollution it is practically impossible to check every vehicle for pollution control.
• Due to insufficient man power it is impossible to monitor Traffic violation viz. Signal
breaking, driving without Valid License etc.
Ways in which the proposed system will counter the above drawbacks
• Human interaction is minimal thus, increase in the efficiency.
• Corruption free fine receipt system thus increasing the revenue
• A server with real time database which could be updated timely.
• Presence of Pollution sensor to note the pollution in every vehicle
• Traffic violation like signal breaking, driving without valid license is overcome by the
electronic system developed.
Hence, the above discussion has inspired the development of VEHICLE MONITORING
SYSTEM. The device consists of two subsystems, one placed in the vehicle and other placed in
the traffic control room. The system placed in the vehicle consists of smart card reader, display,
RFID reader while the system in the traffic control room consist GSM modem and PC. When the
driver wants to drive the vehicle, then he/she has to insert the smart card into the smart card
reader. The inserted smart card will be online authenticated from the traffic control room using
wireless communication (GSM). The vehicle will start if license is valid. Vehicle will also
contain the pollution sensors to indicate the current pollution level of exhaust. When the smart
card is inserted the traffic control room will come to know about relevant information about the
vehicle using wireless communication like insurance, road tax payment details, fine collection
details etc. If the data is non-confirmatory it will send the relevant intimation to the vehicle
driver which will help the driver to take necessary actions.
Also for monitoring as well as issuing fine receipt for signal breaking there is a RFID
reader. This RFID reader comes into act when signal goes red. Each vehicle is having a passive
RFID tag with unique number, whenever there is a traffic violation RFID reader will sense the
tag and send the tag number to the RTO server via a intra network. RTO server will issue the
Fine receipt to the vehicle.
E&TC Department R.S.C.O.E, PUNE 7|Page
VEHICLE MONITORING SYSTEM
CHAPTER 2
LITERARTURE
SURVEY
E&TC Department R.S.C.O.E, PUNE 8|Page
VEHICLE MONITORING SYSTEM
To implement the system following components are required
1. Smart card (Memory Card)
2. Smart card Connector
3. Radio frequency identification
4. Pollution sensors
5. Wireless communication using GSM
6. Microcontroller
2.1 SMART CARD
A smart card, a type of chip card is a plastic card embedded with a computer chip that
stores and transacts data between users. This data is associated with either value or information
or both and is stored and processed within the card's chip, either a memory or microprocessor.
The card data is transacted via a reader that is part of a computing system. Smart card-enhanced
systems are in use today throughout several key applications, including healthcare, banking,
entertainment and transportation. To various degrees, all applications can benefit from the added
features and security that smart cards provide.
2.1.1 APPLICATIONS
First introduced in Europe over a decade ago, smart cards debuted as a stored value tool
for pay phones to reduce theft. As smart cards and other chip-based cards advanced, people
found new ways to use them, including charge cards for credit purchases and for record keeping
in place of paper.
In the U.S., consumers have been using chip cards for everything from visiting libraries
to buying groceries to attending movies, firmly integrating them into our everyday lives. Several
states have chip card programs in progress for government applications ranging from the
Department of Motor Vehicles to Electronic Benefit Transfer (EBT). Many industries have
implemented the power of smart cards into their products such as the new GSM digital cellular
phones to TV-satellite decoders.
2.1.2 WHY SMART CARDS?
Smart cards greatly improve the convenience and security of any transaction. They
provide tamper-proof storage of user and account identity. Smart cards also provide vital
components of system security for the exchange of data throughout virtually any type of
network. They protect against a full range of security threats, from careless storage of user
passwords to sophisticated system hacks. Multifunction cards can also serve as network system
access and store value and other data. People worldwide are now using smart cards for a wide
variety of daily tasks, these include:
E&TC Department R.S.C.O.E, PUNE 9|Page
VEHICLE MONITORING SYSTEM
2.1.3 LOYALTY AND STORED VALUE
A primary use of smart cards is stored value, particularly loyalty programs that track and
incentivize repeat customers. Stored value is more convenient and safer than cash. For issuers,
float is realized on unspent balances and residuals on balances that are never used.
For multi-chain retailers that administer loyalty programs across many different
businesses and Point of sale systems, smart cards can centrally locate and track all data. The
applications are numerous, from parking and laundry to gaming, as well as all retail and
entertainment uses.
2.1.4 SECURING INFORMATION AND PHYSICAL ASSETS
In addition to information security, smart cards achieve greater physical security of
services and equipment, because the card restricts access to all but the authorized user(s). E-mail
and PCs are being locked-down with smart cards. Information and entertainment is being
delivered via to the home or PC. Home delivery of service is encrypted and decrypted per
subscriber access. Digital video broadcasts accept smart cards as electronic keys for protection.
Smart cards can also act as keys to machine settings for sensitive laboratory equipment and
dispensers for drugs, tools, library cards, health club equipment etc.
2.1.5 E-COMMERCE
Smart cards make it easy for consumers to securely store information and cash for
purchasing. The advantages they offer consumers are:
• The card can carry personal account, credit and buying preference information that can be
accessed with a mouse click instead of filling out forms.
• Cards can manage and control expenditures with automatic limits and reporting.
• Internet loyalty programs can be deployed across multiple vendors with disparate POS
systems and the card acts as a secure central depository for points or rewards.
• Micro Payments - paying nominal costs without transaction fees associated with credit
cards or for amounts too small for cash, like reprint charges.
2.1.6 PERSONAL FINANCE
As banks enter competition in newly opened markets such as investment brokerages, they
are securing transactions via smart cards at an increased rate. This means:
• Smart cards increase trust through improved security. Two-Factor Authentication insures
protection of data and value across the internet. Threats such as the "Man in the middle"
and "Trojan Horses" that replay a user name and password are eliminated
• This will improve customer service. Customers can use secure smart cards for fast, 24-
hour electronic funds transfers over the internet
E&TC Department R.S.C.O.E, PUNE 10 | P a g e
VEHICLE MONITORING SYSTEM
• Costs are reduced: transactions that normally would require a bank employee's time and
paperwork can be managed electronically by the customer with a smart card
2.1.7 Health Care
The explosion of health care data brings up new challenges to the efficiency of patient
care and privacy safeguards. Smart cards solve both challenges with secure storage and
distribution of everything from emergency data to benefits status.
• Rapid identification of patients; improved treatment
• A convenient way to carry data between systems or to sites without systems
• Reduction of records maintenance costs
2.1.8 Network Security
Business to business Intranets and Virtual Private Networks "VPNs" are enhanced by the
use of smart cards. Users can be authenticated and authorized to have access to specific
information based on preset privileges. Additional applications range from secure email to
electronic commerce.
2.1.9 Physical Access
Businesses and universities of all types need simple identity cards for all employees and
students. Most of these people are also granted access to certain data, equipment and departments
according to their status. Multifunction, microprocessor-based smart cards incorporate identity
with access privileges and also store value for use in various locations, such as cafeterias and
stores.
2.1.10 TYPES OF CHIP CARDS
Smart cards are defined according to 1). How the card data is read and written, and 2). The type
of chip implanted within the card and its capabilities. There is a wide range of options to choose
from when designing your system.
E&TC Department R.S.C.O.E, PUNE 11 | P a g e
VEHICLE MONITORING SYSTEM
Fig.1 Classification of Chip Cards
2.1.11 CONTACT CARDS
The most common type of smart card. Electrical contacts located on the outside of the
card connect to a card reader when the card is inserted.
Increased levels of processing power, flexibility and memory add cost. Single function
cards are often the most cost-effective solution. Choose the right type of smart card for your
application by evaluating cost versus functionality and determine your required level of security.
All of these variables should be weighed against the expected lifecycle of the card. On average
the cards typically comprise only 10 to 15 percent of the total system cost with the infrastructure,
issuance, training and advertising making up the other 85 percent.
E&TC Department R.S.C.O.E, PUNE 12 | P a g e
VEHICLE MONITORING SYSTEM
2.1.12 MEMORY CARDS
Memory cards have no sophisticated processing power and cannot manage files
dynamically. All memory cards communicate to readers through synchronous protocols. In all
memory cards you read and write to a fixed address on the card. There are three primary types of
memory cards: 1). Straight, 2). Protected, and 3). Stored Value.
1. Straight Memory Cards
These cards just store data and have no data processing capabilities. These cards are the
lowest cost per bit for user memory. They should be regarded as floppy disks of varying sizes
without the lock mechanism. These cards cannot identify themselves to the reader, so your host
system has to know what type of card is being inserted into a reader. These cards are easily
duplicated and cannot be tracked by on-card identifiers.
2. Protected / Segmented Memory Cards
These cards have built-in logic to control the access to the memory of the card.
Sometimes referred to as Intelligent Memory cards, these devices can be set to write protect
some or all of the memory array. Some of these cards can be configured to restrict access to both
reading and writing. This is usually done through a password or system key. Segmented memory
cards can be divided into logical sections for planned multi-functionality. These cards are not
easily duplicated but can possibly be impersonated by hackers. They typically can be tracked by
an on-card identifier.
3. Stored Value Memory Cards
These cards are designed for the specific purpose of storing value or tokens. The cards
are either disposable or rechargeable. Most cards of this type incorporate permanent security
measures at the point of manufacture. These measures can include password keys and logic that
are hard-coded into the chip by the manufacturer. The memory arrays on these devices are set-up
as decrements or counters. There is little or no memory left for any other function. For simple
applications such as a telephone card the chip has 60 or 12 memory cells, one for each telephone
unit. A memory cell is cleared each time a telephone unit is used. Once all the memory units are
used, the card becomes useless and is thrown away. This process can be reversed in the case of
rechargeable cards.
4. CPU/MPU Microprocessor Multifunction Cards
These cards have on-card dynamic data processing capabilities. Multifunction smart
cards allocate card memory into independent sections or files assigned to a specific function or
application. Within the card is a microprocessor or microcontroller chip that manages this
memory allocation and file access. This type of chip is similar to those found inside all personal
computers and when implanted in a smart card, manages data in organized file structures, via a
card operating system (COS). Unlike other operating systems, this software controls access to
E&TC Department R.S.C.O.E, PUNE 13 | P a g e
VEHICLE MONITORING SYSTEM
the on-card user memory. This capability permits different and multiple functions and/or
different applications to reside on the card, allowing businesses to issue and maintain a diversity
of ‘products’ through the card. One example of this is a debit card that also enables building
access on a college campus. Multifunction cards benefit issuers by enabling them to market their
products and services via state-of-the-art transaction and encryption technology. Specifically, the
technology enables secure identification of users and permits information updates without
replacement of the installed base of cards, simplifying program changes and reducing costs. For
the card user, multifunction means greater convenience and security, and ultimately,
consolidation of multiple cards down to a select few that serve many purposes.
There are many configurations of chips in this category including chips that support
cryptographic PKI functions with on board math co-processors or Java virtual machine hardware
blocks. As a rule of thumb - the more functions the higher the cost.
2.1.13 CONTACTLESS CARDS
These are smart cards that employ a radio frequency (RFID) between card and reader
without physical insertion of the card. Instead the card is passed along the exterior of the reader
and read. Types include proximity cards which are implemented as a read-only technology for
building access. These cards function with a limited memory and communicate at 125 MHz True
read & write contactless cards were first used in transportation for quick decrementing and re-
loading of fare values where their lower security was not an issue. They communicate at 13.56
MHz, and conform to the ISO14443 standard. These cards are often straight memory types. They
are also gaining popularity in retail stored value, since they can speed-up transactions and not
lower transaction processing revenues (i.e. VISA and MasterCard), like traditional smart cards.
Variations of the ISO14443 specification include A, B, and C, which specify chips from
either specific or various manufacturers. A=Philips B=everybody else and C=Sony chips.
Contactless card drawbacks include the limits of cryptographic functions and user memory
versus microprocessor cards and the limited distance between card and reader required for
operation.
2.1.14 COMBINATION CARDS
These are hybrids that employ both contact and contactless technology in one card. Combo-cards
can also contain two different types of chips in contrast to a Dual-Interface card where a single
chip manages both functions.
2.1.15 OPERATING SYSTEMS
The two primary types of smart card operating systems
1). Fixed File Structure and
2). Dynamic Application System.
As with card types, selection of a card OS depends on the application the card is
developed for. The other defining difference is in the Encryption Capabilities of the OS and the
Chip. These are typically distinguished by Symmetric Key and Public Key. See the security
E&TC Department R.S.C.O.E, PUNE 14 | P a g e
VEHICLE MONITORING SYSTEM
section of this site for more information.
1). Fixed File Structure
This type treats the card as a secure computing and storage device. Files and permissions
are set in advance by the issuer. These specific parameters are ideal and economical for a fixed
type of card structure and functions that will not change in the near future. An example of this
kind of card is a low-cost employee multi-function badge.
2). Dynamic Application System
This type of operating system, which includes the MULTOS and JAVA card varieties,
enables developers to build, test, and deploy different applications securely. Because the OS and
applications are more separate, updates can easily and repeatedly be made. See our software page
for more information. An example card is a SIM card for mobile GSM where updates and
security are downloaded to the phone and dynamically changed.
2.1.16 BENEFITS
1. Smart cards can be used for identification, authentication, and data storage.
2. Smart cards provide a means of effecting business transactions in a flexible, secure,
standard way with minimal human intervention.
3. Smart card can provide strong authentication for single sign-on or enterprise single sign-
on to computers, laptops, data with encryption, enterprise resource planning platforms
such as SAP, etc.
E&TC Department R.S.C.O.E, PUNE 15 | P a g e
VEHICLE MONITORING SYSTEM
2.2 RADIO FREQUENCY IDENTIFICATION
Fig.2 RFID reader steup
Radio-frequency identification (RFID) is the use of an object (typically referred to as an
RFID tag) applied to or incorporated into a product, animal, or person for the purpose of
identification and tracking using radio waves. Some tags can be read from several meters away
and beyond the line of sight of the reader. Most RFID tags contain at least two parts. One is an
integrated circuit for storing and processing information, modulating and demodulating a radio-
frequency (RF) signal, and other specialized functions. The second is an antenna for receiving
and transmitting the signal.
There are generally three types of RFID tags: active RFID tags, which contain a battery
and can transmit signals autonomously, passive RFID tags, which have no battery and require an
external source to provoke signal transmission and battery assisted passive (BAP) which require
an external source to wake up but have significant higher forward link capability providing great
read range.
• Today, RFID is used in enterprise supply chain management to improve the efficiency of
inventory tracking and management.
• The antenna emits radio signals to activate the tag and to read and write data to it. The
reader emits radio waves in ranges of anywhere from one inch to 100 feet or more,
depending upon its power output and the radio frequency used.
• When an RFID tag passes through the electromagnetic zone, it detects the reader's
activation signal. The reader decodes the data encoded in the tag's integrated circuit
(silicon chip) and the data is passed to the host computer for processing.
• The purpose of an RFID system is to enable data to be transmitted by a portable device,
called a tag, which is read by an RFID reader and processed according to the needs of a
particular application. The data transmitted by the tag may provide identification or
location information, or specifics about the product tagged, such as price, color, date of
purchase, etc. RFID technology has been used by thousands of companies for a decade or
more.
• RFID quickly gained attention because of its ability to track moving objects. As the
technology is refined, more pervasive - and invasive - uses for RFID tags are in the
works. A typical RFID tag consists of a microchip attached to a radio antenna mounted
on a substrate. The chip can store as much as 2 kilobytes of data.
E&TC Department R.S.C.O.E, PUNE 16 | P a g e
VEHICLE MONITORING SYSTEM
2.2.1 WHAT IS RFID?
Radio Frequency Identification, or RFID, is a rapidly-emerging identification and
logging technology. Whether or not you have come across RFID systems in your work, you have
probably encountered RFID in your daily life, perhaps without even being aware of it. At their
simplest, RFID systems use tiny chips, called "tags," to contain and transmit some piece of
identifying information to an RFID reader, a device that in turn can interface with computers. To
begin understanding RFID, think of a conventional Point-of-Sale barcode reader scanning
grocery barcodes. In its simplest active tags are self-powered, usually by some The terms
"passive" and "active" are however form, an RFID system is much the same: it also type of
battery. potentially confusing: in all cases of can identify a package. However, unlike
communication with a passive tag, the reader barcodes, RFID tags don't need a direct line of
"talks" first; the RFID tag is essentially a server. sight: within limits, we can now scan an But, in
the case of active tags, communications unpacked skid of boxes.
Next, think of RFID can be initiated by either the tag or the reader. tags as mini
databases, or as barcodes that can Also potentially confusing is the term be written to, and that
can accumulate "reader," for a reader can also write information as they travel. At this point,
RFID information to an RFID tag. Diverges qualitatively from bar coding, giving it great new
potential. Both tagging technologies–active and Active tags, with their own power source, can
passive–are needed for RFID to realize its full actively and intensively transmit and potential.
The cost savings afforded by passive processing data, and over considerable tags makes RFID
tagging possible at a much In an RFID system, RFID tags are "interrogated" physical distances.
Active tags ca n lower price point than would be possible with by an RFID reader. The
tag reader generates a communicate with readers 100 meters or active tags alone; on the other
hand, active radio frequency "interrogation" signal that more away. Active tags need much less
signal tags add functionality not possible with communicates with the tags. The reader also from
the RFID reader than passive tags passive tags at this time has a receiver that captures a reply
signal from require, and so can contain sensors and data the tags, and decodes that signal. The
reply loggers, for instance, as they are continually signal from the tags reflects, both literally and
powered. Active tags are also suited as data figuratively, the tag's data content. The reply loggers
because they can support a clock (for signal is created as passive "backscatter" (to time-stamping
data) and can contain use the radio term). Significant amounts of memory. Also, active tags are
much better suited than passive tags when a collection of tags needs to be simultaneously read:
they do not all need to RFID has a couple of basic types of tag. Passive be in range of the reader
at the same time.
E&TC Department R.S.C.O.E, PUNE 17 | P a g e
VEHICLE MONITORING SYSTEM
2.2.2 HOW IS RFID TECHNOLOGY EVOLVING?
Within EAN.UCC are a number of sub- definitions are being framed. Within the 64-
bit organizations. As far as RFID is concerned, EPC definitions are header and definition bits,
EPC global is the most relevant. EPC global is a as well as bits for what are effectively a
consortium of supply chain partners manufacturer number (called the "domain RFID is evolving
technologically on at least developing a system of Electronic Product manager number"), a
product number (called three fronts: readers, standards, and tags. Codes™ (EPC). The EPC
global Network aims to the "object class"), and a serial number.
In provide immediate, automatic, and accurate effect, the EPC is like a combination of
UPC bar Reader development identification of any item in the supply chain code plus serial
number. Regardless of company, industry, or RFID readers have evolved and are now
geography. The idea here is that products Tag development frequently wireless handheld units
that tagged by different manufacturers will all enable the user to roam through a warehouse,
interoperate, and refer to the same database At this stage in the development of RFID, most
capturing RFID data wherever RFID tags are of company identifiers, much as barcodes do
business cases really boil down to the cost of found. Some readers are adapters that add now.
RFID tags.
The cheaper they are, the more RFID reader capability to a PDA that can snap deeply
deployed RFID can be. Nobody is into a cradle. Readers are growing more RF To this end,
EAN.UCC has recently defined a going to put three-cent RFID tags on one sensitive, and more
capable of processing, as number of tag classes. The most complete dollar products. Looking
ahead though, tags well as just collecting, RFID data. definition currently is for the most basic
RFID that today cost three cents are projected to tag–the "Class 0" tag mentioned above. This is
cost one cent in a year, as volumes increase
2.2.3 STANDARDS DEVELOPMENT
Standard Development now and probably always will be the most and manufacturing
technologies improve common of tags. It is in the humble Class 0 RFID standards development,
particularly for RFID tag that the rubber hits the road, at least At the other end of the scale, other
business supply chain management, is becoming as far as retail and POS tagging are concerned.
cases for more costly RFID tags can be found. Centralized internationally, primarily under These
tiny chips–by "tiny" I mean sometimes a The enhanced capabilities of active RFID tags, the
auspices of a new hybrid body, EAN.UCC. quarter the size of a grain of sand–hold the their
increased distances of operation EAN.UCC combines two previously separate internationally
standardized RFID identity, the between the RFID tag and the reader, their Standards
organizations: EAN ("European EPC. These tags are passive tags–they have no continuous
power capability, and so forth, Article Numbering"), now EAN International, energy source of
their own–and they are make these tags suitable in higher-unit value and the Uniform Code
E&TC Department R.S.C.O.E, PUNE 18 | P a g e
VEHICLE MONITORING SYSTEM
Council, Inc. (UCC). Generally read-only. Situations–automobile tracking and anti- Together,
these organizations standardize theft systems, for instance.
Identification numbers, transaction sets, XML The simplest EPC currently defined is 64
bit schemas, and other supply chain solutions. Number. In addition, 96- and 256-bit data As the
RFID marketplace evolves, more and more uses for the technology are being developed. First
among them are applications that replicate the uses already in place for barcodes. The cost
savings in scanning a grocery cart without the need to unpack each item is compelling. More
sophisticated applications use the capability of RFID to receive and store data as well as simply
to identify itself. This means that an RFID tag can carry along with it a history of transactions.
In addition, newly-developed tags can incorporate a sensor, making the tag now aware of
its environment, after a fashion. The automotive industry is testing the capability of an RFID tag
to sense tire pressure while a vehicle is in motion. RFID has many applications in the security
field, as can be imagined. The traditional magnetic-stripe security card used for access control is
beginning to be supplanted by RFID tagged cards that can offer a greater degree of security and
record-keeping. Toll-gates are another frequent application; vehicles can pass an RFID reader
and have a toll deducted, often without slowing down. RFID tags will replace printed bar codes
where a business case can be made. An RFID tag that can write information to itself may be used
to create an audit trail or tracking record, particularly for high-value goods. The cost of RFID
tags will need to fall substantially before RFID will be a cost-effective means of coding
inexpensive consumer goods, such as cereal boxes or candy bars.
How soon will RFID dominate as a means of identification on a broad scale? The answer
to this question depends in part on simple computations of cost and benefit, but also on
acceptance and "mood," for lack of a better word. Contributing to mood are factors such as the
current political desire to enhance anti-terrorism security systems, or Wal-Mart's recent
requirement that its top 100 suppliers ship cartons and pallets with RFID tags by January 2005.
Wal-Mart's initial goal is to use RFID tags for tracking shipments and efficient warehousing; the
longer-term goal in the retail industry is the "smart shelf" that can monitor stock levels on a more
granular level. The problem of tracking individual items on store shelves is akin to the Internet
problem of running fibre optic cabling the "last mile" from the Internet backbone to the user: the
cost increases exponentially as the deployment deepens. Correspondingly exponential reductions
in costs, or exponential increases in savings, must ensue to make the case sell.
2.2.4 SUPPLY CHAIN MANAGEMENT
The first of these challenges is key to many of the business cases for RFID. Supply chain
management, in particular, is one of the first places where RFID can make a business case for
itself. Supply chain applications are what drive the RFID implementation initiatives by both
Wal- Mart and the US Department of Defense, two major organizations on the leading edge of
RFID rollouts. For both of these entities, supply chain logistics are essential to their success.
E&TC Department R.S.C.O.E, PUNE 19 | P a g e
VEHICLE MONITORING SYSTEM
Wal-Mart's business model requires sophisticated supply chain logistics to enable the high rates
of turnover that in turn enable it to often sell inventory to customers before suppliers require
payment. For the Department of Defense, executing military operations in locations where
infrastructure is weak or non-existent requires moving vast quantities of supplies quickly and
efficiently. In both cases, the "depth" of an RFID deployment depends on reducing the costs of
the tags themselves to the lowest point possible. Similarly, supply chain users need to both
differentiate individual tags ("tag singulation") and to be able to address or read large numbers of
tags as groups ("tag aggregation").
Successful tag singulation is a function of the sensitivity of the RFID reader, the
sophistication of the tag anti-collision algorithm used by the reader, and the uniqueness of the tag
identification numbering. Tag singulation is what will allow that grocery cart to be successfully
read in a single pass. On the other hand, successful tag aggregation is necessary to reduce RFID
bandwidth requirements and to allow the selection of groups of tags for batch processing,
sorting, "killing," and so forth.
Carefully defined numbering systems, such as that being defined by EPC global, will assist
in this area. Closely related to supply chain management are other areas, such as healthcare and
animal tagging, that are growing areas for RFID tagging. In the health care field, tracking
inventories and and dosages of medicines is essential; in the cattle industry, concerns about mad
cow disease are impelling cattle producers to look at ways to track a cow from birth to table. In
some of these areas passive tags may not have the range needed, and active tags might be used to
increase the distance at which a tag can communicate with a reader.
2.2.5 IDENTIFICATION AND SECURITY
A second obvious area where RFID makes immediate economic sense is in areas where
costs of failure are great. RFID is an ideal means of tracking and authenticating movements of
people, and security is frequently an area where a premium is placed on preventing problems
before they occur. One of the earliest RFID implementations was part of an authentication
system to prevent welfare fraud. RFID systems are still evolving in this area to broaden their
value for security uses. For example, developing secure transmission protocols requires a means
of negotiation a tag identity without also revealing its data. Perhaps revealing even the number of
tags being identified would represent a security concern. Identifiers dynamically derived as
pseudo-random numbers based on a portion of the unique user data might be a solution here, at
the cost of a more complex reader implementation. Also related to security concerns is the
distance at which RFID systems operate. Eavesdropping is possible, particularly on the reader
transmit channel, as it has the highest power level. Implementing methods of encryption will
help here. Whatever the hurdles, the cost savings RFID can offer provide a strong incentive for
technology breakthroughs and innovation.
E&TC Department R.S.C.O.E, PUNE 20 | P a g e
VEHICLE MONITORING SYSTEM
2.3 POLLUTION SENSOR
Pollutants are substances that are perceived to have an adverse effect on the environment
and either directly or indirectly on human health. Airborne pollutants can be gaseous or
suspended particulate matter (liquids or solids ranging in diameter from 10nm to 100μm).
Pollutants can be natural gaseous emissions such as carbon dioxide produced in animal and plant
respiration, sulphur dioxide from geysers, or suspended matter such as salt spray or dust from
volcanic eruptions. However in densely populated areas studies have shown that greater than 90
percent of the volumes of airborne pollutants are the result of human activities. Sources of
pollution in these areas include combustion processes, solid waste disposal, construction and
demolition.
With an increasing number of vehicles on our roads annually the internal combustion
process in a land transport vehicle is responsible for a significant amount of pollution in these
densely populated areas [1]. The pollutant emissions from a vehicle include carbon monoxide
(CO), oxides of nitrogen (nitric oxide, NO, and nitrogen dioxide, NO2), hydrocarbons (HC),
smoke particles (diameters of 0.05μm to 1μm) and also particulate matter. CO is produced when
an engine does not completely burn fuel and is poisonous to humans at high concentrations
(greater than 400 parts-per-million).
NO is formed in an engine by the reaction of nitrogen present in fuel with oxygen (O2) at
very high temperatures (>1000°C). Although NO is not considered to be a health concern itself it
further oxides to NO2 which is believed to be a pulmonary irritant. Carbon dioxide (CO2)
although not strictly speaking a pollutant, is also produced by exhaust gas emissions. The excess
of CO2 produced by exhaust emissions is considered to be responsible for the climate change
known as the “Greenhouse Effect” [2]. In order to protect human health and limit damage to the
environment, the European Commission has introduced a series of directives to automobile
manufacturers to limit levels of exhaust emissions entering the environment [3]. The first of
these directives was implemented in 1992 and is referred to as Euro I while the latest, which will
be implemented in 2008, is Euro V. Each successive directive has lowered the acceptable
amounts of CO, NOx, HC, particulate matter and smoke which may enter the atmosphere from
land transport vehicles. The Euro I, for example, stated that the acceptable levels of CO leaving a
heaving goods vehicle (HGV) as 4.5 grams per kilowatt hour (g/kWh). In contrast to this the
Euro V states that a HGV may only have 1.5g/kWh of CO leaving its exhaust [4]. Figure
illustrates the decrease in acceptable emission levels.
E&TC Department R.S.C.O.E, PUNE 21 | P a g e
VEHICLE MONITORING SYSTEM
The Lambda Sensor: The sensor that is primarily used in automobiles to detect if pollution is
occurring is the Lambda sensor. The Lambda sensor compares the ratio of ambient air to the
amount of oxygen in the exhaust of the vehicle and signals to the engine if the ratio is correct. If
oxygen is present in the exhaust of an engine it indicates that the engine is burning fuel, however
if there is an absence of oxygen, pollution can be assumed to be taking place, as the engine is not
burning fuel correctly. If the ratio of fuel to air is correct then the output voltage of the sensor
will be low [5]. On the other hand if the vehicle is not burning fuel correctly and pollution is
occurring then the output voltage will be high. The Lambda sensor may fail prematurely if it
becomes clogged with carbon, or is contaminated by silicone from an antifreeze leak. In addition
to this as the sensor deteriorates with age, its response to changing fuel ratios becomes slower.
The malfunctioning of the sensor due to contamination or ageing leads to an increase in the fuel
mixture resulting in higher levels of pollution or it can lead to the engine misfiring. If the fuel
mixture is excessively high for a long period of time, the catalytic converter that cleans the
exhaust emissions will become damaged [6]. It should also be noted that the Lambda sensor does
not satisfy European emission control laws as it merely indicates if pollution is occurring or not.
As was noted in the preceding section, the specified levels of a particular pollutant are quite
exact and in order to prove that the standards for each substance are being met it is necessary to
develop a new type of sensor.
The NOx Sensor: The NOx sensor was designed to detect the presence of nitric oxide (NO) and
nitrogen dioxide (NO2) in exhaust emissions at temperatures of greater than 600°C [7]. It can
measure the gases down to parts-per million (ppm) levels and is therefore suitable for the
quantifying the levels of each gas leaving the exhaust as required by the aforementioned
emission control laws. However in a similar manner to the Lambda sensor the NOx sensor
becomes poisoned by the harmful gases it monitors which reduces its effectiveness and
eventually prevents it working altogether. The NOx sensor also has cross-sensitivity to other
gases such as oxygen in the 20-80% range and is unable to 34 discriminate between NO and
NO2. It is also clear that it only addresses two out of several gaseous pollutants that are required
to be monitored.
E&TC Department R.S.C.O.E, PUNE 22 | P a g e
VEHICLE MONITORING SYSTEM
2.4 WIRELESS COMMUNICATION USING GSM
The GSM system is the most widely used cellular technology in use in the world today. It
has been a particularly successful cellular phone technology for a variety of reasons including the
ability to roam worldwide with the certainty of being able to be able to operate on GSM
networks in exactly the same way - provided billing agreements are in place.
The letters GSM originally stood for the words Groupe Speciale Mobile, but as it became
clear this cellular technology was being used worldwide the meaning of GSM was changed to
Global System for Mobile Communications. Since this cellular technology was first deployed in
1991, the use of GSM has grown steadily, and it is now the most widely cell phone system in the
world. GSM reached the 1 billion subscriber point in February 2004, and is now well over the 3
billion subscriber mark and still steadily increasing.
The GSM system was designed as a second generation (2G) cellular phone technology.
One of the basic aims was to provide a system that would enable greater capacity to be achieved
than the previous first generation analogue systems. GSM achieved this by using a digital
TDMA (time division multiple access approach).
2.4.1 TIME DOMAIN MULTIPLEXING
The main novelty introduced in GSM is the time domain multiple access, a multiplexing
approach with enables 8 phones to share one single frequency channel .This adds considerable
complexity to the protocol ,compared to a single user for each channel .Over a frame of 4.61 ms
,each phone takes the lead on the channel and emits its information, during a burst of 577µs.
2.4.2 SPEECH SAMPLING AND COMPRESSION
The sound captured by the microphone is filtered to remove harmonics lower than 300Hz
and higher than 3000Hz. Then, a gain control stage keeps the signal envelope more or less
constant before a sampling at the rate of 8000Hz, in a 13 bits format. This leads to a rate of
104Kbit/s. This means that a compression algorithm is mandatory to obtain an acceptable rate of
12Kbit/s.
The voice coder implemented in the GSM handset splits the sound into portions of 20ms,
with a time-domain aspect reported in the upper part of figure. The redundant periodic structure
of the sound (80% of the speech), is removed by the coder. Linear prediction and root mean
square minimization are the mathematical basis for computing the best coefficients to
approximate each portion of sound by an adaptive filter. Consequently the filter coefficients are
transmitted, not the sampled sound. This features a significant reduction of data. Low order
coefficients are coded in a 6 bit format, high order coefficients are coded in a 3 bit format.
E&TC Department R.S.C.O.E, PUNE 23 | P a g e
VEHICLE MONITORING SYSTEM
2.4.3 MODULATION
The modulation used in GSM is derived from quadrature phase shift keying. Each byte of
data is split into four pairs of bits. To each pair of bit corresponds a particular phase for I(t) and
Q(t). The modulated signal is the sum of two sinusoidal waves, with a phase shift depending on
the logic symbol. The Guassian Modulated shift has smooth transitions to avoid the spread of
harmonics in the emission spectrum.
2.4.4 DEMODULATION
The principles for numerical demodulation of phase modulated signals are based on the
multiplication of the received signal by a sinus and cosine with the same frequency. The result
shown in figure is a composition of two effects: a sinusoidal wave with twice the initial
frequency (removed by filtering) and steps of voltage, that are corresponding to the initial bits
send by emitter. Half of the bits are issued from multiplication by cosine, the other half is
obtained by the multiplication by sinus. At the price of multiplication, the bytes are easily
reconstructed.
2.5 MICROCONTROLLER
A microcontroller (also microcomputer, MCU or µC) is a small computer on a
single integrated circuit consisting internally of a relatively simple CPU, clock, timers, I/O ports,
and memory. Program memory in the form of NOR flash or OTP ROM is also often included on
chip, as well as a typically small amount of RAM. Microcontrollers are designed for small or
dedicated applications. Thus, in contrast to the microprocessors used in personal computers and
other high-performance or general purpose applications, simplicity is emphasized. Some
microcontrollers may use four-bit words and operate at clock rate frequencies as low as 4 kHz, as
this is adequate for many typical applications, enabling low power consumption (mill watts or
microwatts).
They will generally have the ability to retain functionality while waiting for an event such
as a button press or other interrupt; power consumption while sleeping (CPU clock and most
peripherals off) may be just nano watts, making many of them well suited for long lasting battery
applications. Other microcontrollers may serve performance-critical roles, where they may need
to act more like a digital signal processor (DSP), with higher clock speeds and power
consumption.
Microcontrollers are used in automatically controlled products and devices, such as
automobile engine control systems, implantable medical devices, remote controls, office
machines, appliances, power tools, and toys. By reducing the size and cost compared to a design
that uses a separate microprocessor, memory, and input/output devices, microcontrollers make it
economical to digitally control even more devices and processes. Mixed signal microcontrollers
are common, integrating analog components needed to control non-digital electronic systems.
E&TC Department R.S.C.O.E, PUNE 24 | P a g e
VEHICLE MONITORING SYSTEM
Microcontrollers usually contain from several to dozens of general purpose input/output
pins (GPIO). GPIO pins are software configurable to either an input or an output state. When
GPIO pins are configured to an input state, they are often used to read sensors or external
signals. Configured to the output state, GPIO pins can drive external devices such as LED's or
motors.
Many embedded systems need to read sensors that produce analog signals. This is the
purpose of the analog-to-digital converter (ADC). Since processors are built to interpret and
process digital data, i.e. 1s and 0s, they won't be able to do anything with the analog signals that
may be sent to it by a device. So the analog to digital converter is used to convert the incoming
data into a form that the processor can recognize. A less common feature on some
microcontrollers is a digital-to-analog converter (DAC) that allows the processor to output
analog signals or voltage levels.
In addition to the converters, many embedded microprocessors include a variety of timers
as well. One of the most common types of timers is the Programmable Interval Timer (PIT). A
PIT just counts down from some value to zero. Once it reaches zero, it sends an interrupt to the
processor indicating that it has finished counting. This is useful for devices such as thermostats,
which periodically test the temperature around them to see if they need to turn the air conditioner
on, the heater on, etc.
Time Processing Unit (TPU) is a sophisticated timer. In addition to counting down, the
TPU can detect input events, generate output events, and perform other useful operations.
A dedicated Pulse Width Modulation (PWM) block makes it possible for the CPU to
control power converters, resistive loads, motors, etc., without using lots of CPU resources in
tight timer loops.
Universal Asynchronous Receiver/Transmitter (UART) block makes it possible to
receive and transmit data over a serial line with very little load on the CPU. Dedicated on-chip
hardware also often includes capabilities to communicate with other devices (chips) in digital
formats such as I2C and Serial Peripheral Interface (SPI).
2.5.1 PIC MICROCONTROLLER
PIC is a family of Harvard architecture microcontrollers made by Microchip Technology,
derived from the PIC1640 originally developed by General Instrument's Microelectronics
Division. The name PIC initially referred to "Programmable Interface Controller".
PICs are popular with both industrial developers and hobbyists alike due to their low
cost, wide availability, large user base, extensive collection of application notes, availability of
low cost or free development tools, and serial programming (and re-programming with flash
memory) capability.
E&TC Department R.S.C.O.E, PUNE 25 | P a g e
VEHICLE MONITORING SYSTEM
The PIC architecture is distinctively minimalist. It is characterized by the following features:
• Separate code and data spaces (Harvard architecture)
• A small number of fixed length instructions
• Most instructions are single cycle execution (4 clock cycles), with single delay cycles
upon branches and skips
• A single accumulator (W), the use of which (as source operand) is implied (i.e. is not
encoded in the opcode)
• All RAM locations function as registers as both source and/or destination of math and
other functions.
• A hardware stack for storing return addresses
• A fairly small amount of addressable data space (typically 256 bytes), extended through
banking
• Data space mapped CPU, port, and peripheral registers
• The program counter is also mapped into the data space and writable (this is used to
implement indirect jumps).
Unlike most other CPUs, there is no distinction between memory space and register space
because the RAM serves the job of both memory and registers, and the RAM is usually just
referred to as the register file or simply as the registers.
2.5.2 AVR MICROCONTROLLER
The AVR is a modified Harvard architecture 8-bit RISC single chip microcontroller (µC)
which was developed by Atmel in 1996. The AVR was one of the first microcontroller families
to use on-chip flash memory for program storage, as opposed to One-Time Programmable
ROM, EPROM, or EEPROM used by other microcontrollers at the time.
AVRs are generally classified into five broad groups:
• tinyAVR — the ATtiny series
o 0.5–8 kB program memory
o 6–32-pin package
o Limited peripheral set
• megaAVR — the ATmega series
o 4–256 kB program memory
o 28–100-pin package
o Extended instruction set (Multiply instructions and instructions for handling
larger program memories)
o Extensive peripheral set
• XMEGA — the ATxmega series
o 16–384 kB program memory
o 44–64–100-pin package (A4, A3, A1)
E&TC Department R.S.C.O.E, PUNE 26 | P a g e
VEHICLE MONITORING SYSTEM
o Extended performance features, such as DMA, "Event System", and cryptography
support.
o Extensive peripheral set with DACs
• Application specific AVR
o megaAVRs with special features not found on the other members of the AVR
family, such as LCD controller, USB controller, advanced PWM, CAN etc.
o Atmel At94k FPSLIC (Field Programmable System Level Integrated Circuit), an
AVR core on-die with an FPGA. The FPSLIC uses SRAM for the AVR program
code, unlike all other AVRs. Partly due to the relative speed difference between
SRAM and flash, the AVR core in the FPSLIC can run at up to 50 MHz.
E&TC Department R.S.C.O.E, PUNE 27 | P a g e
VEHICLE MONITORING SYSTEM
CHAPTER 3
Block Diagram
and methodology
E&TC Department R.S.C.O.E, PUNE 28 | P a g e
VEHICLE MONITORING SYSTEM
GSMmobile
MODEM
SMART SMART CARD
SMART CARD
SMART CARD
CARD READER
CONNECTOR
avr
ATmega16
AVR
MICROCONTROLLER
PASSIVE
POLLUTION
RFID TAG
SENSOR
Passive RFID tag located in the
vehicle but isolated from the system
LIQUID CRYSTAL
DISPLAY
VEHICLE UNIT
RADIO
GSM FREQUENCY
MODEM IDENTIFICATION
READER
SERVER UNIT TRAFFIC SIGNAL
UNIT
Fig.3 Block Diagram
E&TC Department R.S.C.O.E, PUNE 29 | P a g e
VEHICLE MONITORING SYSTEM
There are three units present in the overall system
1. Vehicle unit
2. Server unit
3. Traffic signal unit
3.1 VEHICLE UNIT
Following are the various blocks in the vehicle unit;
1. Smart card
2. Smart card connector
3. RFID tag
4. GSM modem
5. Pollution sensor
6. Microcontroller
3.1.1 SMART CARD
A smart card, chip card, or integrated circuit card (ICC), is any pocket-sized card with
embedded integrated circuits which can process data. This implies that it can receive input which
is processed — by way of the ICC applications — and delivered as an output. There are two
broad categories of ICCs. Memory cards contain only non-volatile memory storage components,
and perhaps some specific security logic. Microprocessor cards contain volatile memory and
microprocessor components. The card is made of plastic, generally PVC, but
sometimes ABS or polycarbonate. The card may embed a hologram to avoid counterfeiting.
Using smart cards is also a form of strong security authentication for single sign-on within large
companies and organizations. After surveying various types of smart card we decided to use the
memory card of contact type which makes the system cost effective and robust.
Fig.4 Smart Card
Smart card is characterized as follows:
• Dimensions are normally credit card size. The ID-1 of ISO/IEC 7810 standard defines
them as 85.60 × 53.98 mm. Another popular size is ID-000 which is 25 × 15 mm
(commonly used in SIM cards). Both are 0.76 mm thick.
E&TC Department R.S.C.O.E, PUNE 30 | P a g e
VEHICLE MONITORING SYSTEM
• Contains a security system with tamper-resistant properties (e.g. a secure crypto
processor, secure file system, human-readable features) and is capable of providing
security services (e.g. confidentiality of information in the memory).
• Asset managed by way of a central administration system which interchanges
information and configuration settings with the card through the security system. The
latter includes card hot listing, updates for application data.
• Card data is transferred to the central administration system through card reading devices,
such as ticket readers, ATMs etc.
Contact smart cards have a contact area, comprising several gold-plated contact pads, that
is about 1 cm square. When inserted into a reader, the chip makes contact with electrical
connectors that can read information from the chip and write information back. The ISO/IEC
7816 and ISO/IEC 7810 series of standards define:
• The physical shape
• The positions and shapes of the electrical connectors
• The electrical characteristics
• The communications protocols, that includes the format of the commands sent to the card
and the responses returned by the card.
• Robustness of the card
• The functionality
3.1.2 SMART CARD CONNECTOR
Smart card is an electronic device which contains IC which is mounted on the plastic
card. Due to its unique shape, to access various pins of the IC smart connector is requires. It is a
connector which holds the smart card and has pins which are printed circuit board (PCB)
mountable.
Fig.5 Smart Card Connector
3.1.3 POLLUTION SENSOR
There are various effluents which are been exhausted in the environment by the vehicle.
To monitor the level of effluents electronically pollution sensors are utilized. There are various
types of effluents exhausted like Carbon monoxide, NOx, carbon dioxide etc. Carbon monoxide
is the most harmful effluent which is produced due to the incomplete combustion of the fuel.
Hence, we are using Carbon monoxide sensor MQ-7 to detect the CO.
E&TC Department R.S.C.O.E, PUNE 31 | P a g e
VEHICLE MONITORING SYSTEM
Sensitive material of MQ-7 gas sensor is SnO2, which with lower conductivity in clean
air. It make detection by method of cycle high and low temperature, and detect CO when low
temperature (heated by 1.5V). The sensor’s conductivity is more higher along with the gas
concentration rising. When high temperature (heated by 5.0V), it cleans the other gases adsorbed
under low temperature. MQ-7 gas sensor has high sensitity to Carbon Monoxide. The sensor
could be used to detect different gases contains CO, it is with low cost and suitable for different
application.
Fig.6 MQ-7 Pollution sensor
3.1.4 MICROCONTROLLER
Microcontroller is the brain of any embedded system. The system performs its operation
as per the program which is stored in the flash memory of the microcontroller. Microcontroller is
the single chip which comprises of the processor and various other peripherals viz. Analog to
Digital Converter, Timer, memory etc. After surveying different types of microcontroller we
chose ATmega16 which has 8-bit AVR processor. It has 16kb of flash memory to store the
program. Following are the various other features of the AVR microcontroller;
• Advanced RISC Architecture
– 131 Powerful Instructions – Most Single-clock Cycle Execution
– 32 x 8 General Purpose Working Registers
– Fully Static Operation
– Up to 16 MIPS Throughput at 16 MHz
– On-chip 2-cycle Multiplier
• High Endurance Non-volatile Memory segments
– 16K Bytes of In-System Self-programmable Flash program memory
– 512 Bytes EEPROM
– 1K Byte Internal SRAM
– Write/Erase Cycles: 10,000 Flash/100,000 EEPROM
– Data retention: 20 years at 85°C/100 years at 25°C
– Optional Boot Code Section with Independent Lock Bits
– In-System Programming by On-chip Boot Program
– True Read-While-Write Operation
– Programming Lock for Software Security
• JTAG (IEEE std. 1149.1 Compliant) Interface
E&TC Department R.S.C.O.E, PUNE 32 | P a g e
VEHICLE MONITORING SYSTEM
– Boundary-scan Capabilities According to the JTAG Standard
– Extensive On-chip Debug Support
– Programming of Flash, EEPROM, Fuses, and Lock Bits through the JTAG Interface
• Peripheral Features
– Two 8-bit Timer/Counters with Separate Prescalers and Compare Modes
– One 16-bit Timer/Counter with Separate Prescaler, Compare Mode, and Capture Mode
– Real Time Counter with Separate Oscillator
– Four PWM Channels
– 8-channel, 10-bit ADC
– Byte-oriented Two-wire Serial Interface
– Programmable Serial USART
– Master/Slave SPI Serial Interface
– Programmable Watchdog Timer with Separate On-chip Oscillator
– On-chip Analog Comparator
• Special Microcontroller Features
– Power-on Reset and Programmable Brown-out Detection
– Internal Calibrated RC Oscillator
– External and Internal Interrupt Sources
– Six Sleep Modes: Idle, ADC Noise Reduction, Power-save, Power-down, Standby and
Extended Standby
• I/O and Packages
– 32 Programmable I/O Lines
– 40-pin PDIP, 44-lead TQFP, and 44-pad QFN/MLF
• Operating Voltages
– 2.7 - 5.5V for ATmega16L
– 4.5 - 5.5V for ATmega16
• Speed Grades
– 0 - 8 MHz for ATmega16L
– 0 - 16 MHz for ATmega16
• Power Consumption @ 1 MHz, 3V, and 25⋅ C for ATmega16L
– Active: 1.1 mA
– Idle Mode: 0.35 mA
– Power-down Mode: < 1 μA
3.1.5 RFID TAG
RFID tag is placed in the vehicle to allow the traffic signal unit to detect the vehicle when
it breaks the signal. It has no communication or it is isolated from the vehicle unit. RFID tag is a
passive tag that means it remains passive till it come in the range of RFID reader. As soon as it is
in the range of RFID reader it sends the unique number to the reader. An RFID tag is a microchip
combined with an antenna in a compact package; the packaging is structured to allow the RFID
tag to be attached to an object to be tracked. "RFID" stands for Radio Frequency Identification.
The tag's antenna picks up signals from an RFID reader or scanner and then returns the signal,
usually with some additional data (like a unique serial number or other customized information).
E&TC Department R.S.C.O.E, PUNE 33 | P a g e
VEHICLE MONITORING SYSTEM
RFID tags can be very small - the size of a large rice grain. Others may be the size of a small
paperback book.
A passive tag is an RFID tag that does not contain a battery; the power is supplied by the
reader. When radio waves from the reader are encountered by a passive rfid tag, the coiled
antenna within the tag forms a magnetic field. The tag draws power from it, energizing the
circuits in the tag. The tag then sends the information encoded in the tag's memory.
Fig.7 RFID tag
The major disadvantages of a passive RFID tag are:
• The tag can be read only at very short distances, typically a few feet at most. This greatly
limits the device for certain applications.
• It may not be possible to include sensors that can use electricity for power.
• The tag remains readable for a very long time, even after the product to which the tag is
attached has been sold and is no longer being tracked.
The advantages of a passive tag are:
• The tag functions without a battery; these tags have a useful life of twenty years or more.
• The tag is typically much less expensive to manufacture
• The tag is much smaller (some tags are the size of a grain of rice). These tags have almost
unlimited applications in consumer goods and other areas.
E&TC Department R.S.C.O.E, PUNE 34 | P a g e
VEHICLE MONITORING SYSTEM
3.1.6 LIQUID CRYSTAL DISPLAY
Any display is the user-machine interface which indicates the status of the system and
provides the information to the user. Here we are using liquid crystal display because it is low
power consuming, easy to interface and it provides very attractive look to the system. As the
message to be displayed on the LCD is very small we are using 16x2 displays which have 16
columns and 2 rows.
Fig.8 LCD
3.2 SERVER UNIT
Following are the blocks which are makes server unit;
1. GSM modem
2. Computer with Microsoft Windows©
Server unit contains a database of vehicle driver which include all the relevant
information about the vehicle and driver. It contains driving license number, driver personal
information and unique ID of vehicle (RFID tag).
Server monitors all the vehicle and driver information real time that is it gets updated
continuously. For carrying out the communication between the vehicle unit and Server unit
we are using GSM wireless communication technology.
To carry out the communication via GSM modem we require AT (attention) command.
AT commands are required to setup and control the GSM modem. Following are some of the
AT Commands which are used in the server unit;
1. AT Check if serial interface and GSM modem is working.
2. ATE0 Turn echo off, less traffic on serial line.
3. AT+CNMI Display of new incoming SMS.
4. AT+CPMS Selection of SMS memory.
5. AT+CMGF SMS string format, how they are compressed.
6. AT+CMGR Read new message from a given memory location.
7. AT+CMGS Send message to a given recipient.
8. AT+CMGD Delete message.
We are using visual basics for the graphical user interface between server unit and user
for accessing the database and making new entry in the database.
E&TC Department R.S.C.O.E, PUNE 35 | P a g e
VEHICLE MONITORING SYSTEM
3.3 TRAFFIC SIGNAL UINT
Traffic signal unit is made up of only RFID reader. RFID reader produces RF signal
around it in a circular region having some radius. We are using RFID reader to monitor the
signal breaking by the vehicle. Every vehicle contains the unique RFID tag which contains the
number. Whenever RFID tag comes in the range of RFID reader, it reads the data from the tag
and sends the data to the server using internal network.
E&TC Department R.S.C.O.E, PUNE 36 | P a g e
VEHICLE MONITORING SYSTEM
CHAPTER 4
HARDWARE DESIGN
E&TC Department R.S.C.O.E, PUNE 37 | P a g e
VEHICLE MONITORING SYSTEM
The most important and basic aspect of the any system is to design the circuit (i.e.
hardware design) for the specific application. This involves deciding which component to use,
specifications of different components, mathematical calculations, component selection and
other related issues. The detailed information of the hardware design of the our system is as
follows.
4.1 POWER SUPPLY
The basic step in the designing of any system is to design the power supply required for that
system. The steps involved in the designing of the power supply are as follows
1) Determine the total current that the system sinks from the supply.
2) Determine the voltage rating required for the different components.
D1
1N4007
7805 VCC
D2
1 8 2 3
IN OUT
TRNSFMER
1N4007
4 5 D3 U1
C2 C1 C3 C4
1000uf 0.1uf 220uf 0.1uf
1N4007
D4
1N4007
Fig.Power Supply
VO=VR +VL
VR =5V
VL = IL *RL
RL=10Ω, VL=5V
VO=10V
VIN =10 +2
VIN =12V
In our system most of the components used require 5 V as operating voltage such as
micro controller, MAX 232, MCT2E etc. The total current, which our circuit sinks from the
power supply, is not more than 200 mA. We have used Regulator IC 7805 that gives output
voltage of 5V.The minimum input voltage required for the 7805 is near about 7 v. Therefore we
have used the transformer with the voltage rating 230v-10v and current rating 500 mA. The
output of the transformer is 12 V AC. This Ac voltage is converted into 12 V DC by Bridge
rectifier circuit.
E&TC Department R.S.C.O.E, PUNE 38 | P a g e
VEHICLE MONITORING SYSTEM
The reasons for choosing the bridge rectifier are
1. The TUF is increased to 0.812 as compared the full wave rectifier.
2. The PIV across each diode is the peak voltage across the load =Vm, not 2Vm as in the two
diode rectifier
Output of the bridge rectifier is not pure DC and contains some AC some AC ripples in it. To
remove these ripples we have used capacitive filter, which smoothens the rippled out put that we
apply to 7805 regulators IC that gives 5V DC. We preferred to choose capacitor filters since it is
cost effective, readily available and not too bulky.
The value of the capacitor filter can be found by following formula,
IL * t1
C =
Vr
4.2 OSCILLATOR CIRCUIT
Any micro controller requires circuitry that generates the clock pulses by which all internal
operations are synchronized.
PIN 13(XTAL1)
PIN 12( XTAL2)
12MHz
CRYSTAL
C1 22pF C2 22pF
Fig.9 Oscillator Circuit
In ATMEGA16 two pins viz.pin no 13 & 12 ( XTAL1 & XTAL2 ) are provided for
connecting a resonant network to form an oscillator. A quartz crystal is used with ceramic
capacitors as shown in above circuit diagram. The crystal frequency is the basic internal
frequency of the micro controller. The range of the crystal that can be connected to the micro
controller is 1Mhz to 16 Mhz. Different crystals are available such as the Quartz, Rochelle salts,
E&TC Department R.S.C.O.E, PUNE 39 | P a g e
VEHICLE MONITORING SYSTEM
and Tourmaline etc. We have preferred to use Quartz crystal because it is inexpensive and
readily available.
C1 and C2 are between 10pF to 40 pF. The capacitors C1, C2 are used for stable
frequency operation i.e. in the condition where there is high noise and humidity as in the case of
factories. Due to this the oscillator frequency can alter, for the suppression or do we can say
deletion of this the two capacitor are used for stable frequency.
4.3 RESET CIRCUIT
The ATMEGA16 uses an active low reset pin. The reset input must go low for two
machine cycles when power is first applied and then go high. We have used simple RC circuit,
which provide system voltage (Vcc) to the reset pin until the capacitor begins to charge .The
time for which the reset pin is kept low depends on the RC time constant of the reset circuit.
Fig.10 Reset Circuit
The value of the capacitor used is calculated using following steps,
1. The value of the resistor is assumed as 10 K and the value of the capacitor is calculated
using following formula,
2. Capacitor voltage during discharging is
Vc = Vcc * e –t/RC
And during discharging is,
Vc = Vcc (1-e –t/RC)
E&TC Department R.S.C.O.E, PUNE 40 | P a g e
VEHICLE MONITORING SYSTEM
4.4 LIQUID CRYSTAL DISPLAY
Advantages of LCD over LED display:
1. It can display numbers, characters and graphics, whereas LED displays are limited to
numbers and few characters.
2. LCD has its own processor, so there is no need for refreshing it through micro controller.
3. Ease of programming for characters and graphics
4. It is cost effective.
LCD has eight data lines which is interfaced with the microcontroller. This data bus is
utilized to carry data which is to be displayed on the LCD. Along with the data bus there are
three control pins which are required to control the operation. Hence to interface LCD we require
ten pins. To minimize number of pins we use only four data pins by sending lower nibble first
followed by upper nibble.
Fig.11 Interafcing Diagram Of LCD
• Pin1- GND: For digital ground
• Pin2- VCC: VCC (5v) supply is given to this pin
• Pin3-(-VEE): We can control the contrast of LCD by connecting appropriate value POT
to this pin. The connection is as shown in above fig.
• Pin 4- RS- Register Select: The display contains two internal 8-bit registers. One is for
commands and another is for data (characters) to be displayed.
When RS=0 Command Register is selected
RS=1 Data register is selected
• Pin5- Read/Write: This pin is used to select read/write operation of LCD
When R/W=1 Read Operation is Selected
E&TC Department R.S.C.O.E, PUNE 41 | P a g e
VEHICLE MONITORING SYSTEM
R/W=0 Write Operation is Selected
Read operation is performed during status checking of busy flag. The MSB of
data lines i.e. D7 bit acts as busy flag.
• Pin6-Enable: A high to low pulse is given to this pin to enable the operation of LCD
• Pin 7-14: Pin 7to14 are data lines (i.e. D0 to D7) of LCD. These pins can be connected to
port pins of Micro Controller. Any data transfer will take place through these pins.
• Pin15-( LED+): It is connected to VCC
• Pin 16-(LED-): It is connected to Ground
Pin no 15 and 16 are used for backlight control of LCD. To limit the current,
220Ω resistor is connected.
4.5 RELAY AND RELAY DRIVER CIRCUIT
Relay is an electromagnetic switch, consist of a coil, 1 common terminal, 1 normally
closed terminal, and one normally open terminal.
Circuit symbol for a relay
The relay's switch connections are usually labeled COM, NC and NO:
COM = Common, always connect to this, it is the moving part of the switch
NC = Normally Closed, COM is connected to this when the relay coil is off.
NO = Normally Open, COM is connected to this when the relay coil is on.
Relays allow one circuit to switch a second circuit, which can be completely separate from the
first. For example a low voltage battery circuit can use a relay to switch a 230V AC mains
circuit. There is no electrical connection inside the relay between the two circuits; the link is
magnetic and mechanical.
E&TC Department R.S.C.O.E, PUNE 42 | P a g e
VEHICLE MONITORING SYSTEM
Driver circuit for the relay :
Fig.12 Relay Drive Circuitry
Advantages of relays:
• Relays can switch AC and DC, transistors can only switch DC.
• Relays can switch high voltages, transistors cannot.
• Relays are a better choice for switching large currents (> 5A).
• Relays can switch many contacts at once.
4.6 MEMORY AT24C04
The AT 24C04 provides 4096 bits of serially electrically erasable and programmable read
only memory (EEPROM) organized as 512 bytes of 8 bit each. It is accessed via a wire serial
interface.
Feature
1. Write protect pin for Hardware data protection..
2. Low voltage & standard voltage operation.
3. 2-wire serial interface.
4. Bidirectional data transfer protocol.
5. Partial page writes are allowed.
6. High reliability – Endurance is 1 million write cycle.
7. Data retention – 100 year.
E&TC Department R.S.C.O.E, PUNE 43 | P a g e
VEHICLE MONITORING SYSTEM
To microcontroller
pins 24 and 23
Fig.13 Interfacing Diagram Of Memory
Serial clock (SCL)
The SCL input is used to positive edge clock data in to each EEPROM device and
negative edge clock data out of each device.
Serial data (SDA)
The SDA pin is bidirectional for serial data transfer. The pin is open drain driven and
may be wired – with any number o other open drain or open collector device.
The chip issuing the Start condition first pulls the SDA (data) line low, and
Start
next pulls the SCL (clock) line low.
Stop The Bus Master first releases the SCL and then the SDA line.
Reading Data from Memory
E&TC Department R.S.C.O.E, PUNE 44 | P a g e
VEHICLE MONITORING SYSTEM
Device / page Addresses (A2,A1,A0)
The A2,A1,and A0 pins are device address input . For AT24104 pins A2&A1 will be
used . We can connect eight device with 2K capacity .
Write protect (WP)
This pin provides Hardware data protection . The write pin allows normal read / write
operations when connected to ground . When the write protect pin is connected to V cc the write
protect features is enable.
4.7 MAX 232 & ITS INTERFACING WITH MICRO-CONTROLLER
The various devices such as PC, GSM handset operates with RS232 standard.
Microcontroller operates with TTL voltage levels .To interfacing these devices with Micro-
controller, we need to use s line driver (voltage converter) to convert the RS232’s Signal to TTL
voltage levels that will be acceptable to the ATmega16’s TXD & RXD pins For this purpose
MAX232 level converter is used.
Fig.14 Interfacing Diagram of MAX-232
The MAX 232 has tow sets of line drivers for transferring & receiving data. The line
drivers used for TXD are called T1& T2 the line drivers for RXD are called R1&R2 T1&T2 Are
used together for TXD & RXD of the microcontroller & 2nd set is left unused.HereT1IN is TTL
side& is connected to TXD of microcontroller while T1 out is the ES232 side which is connected
E&TC Department R.S.C.O.E, PUNE 45 | P a g e
VEHICLE MONITORING SYSTEM
to the RXD pin of RS232 DB connecters, and R1 out is the TTL side which is connected to the
RXD pin of the microcontroller.
MAX232 requires four capacitors ranging from 1 to 22 micro-fared .These capacitors are
connected to internal D.C. to D.C. converters. If we will use MAX 233 instead of Max 232 the
external capacitors are not required. But cost of the MAX 2333 is 10 times greater than Max 232.
4.8 POLLUTION SENSOR
Sensor is a type of transducer which converts any physical/environmental change to the
electrical signal which is analog in nature. Pollution sensor measures the concentration of the
carbon monoxide and converts it into analog voltage levels from 0V to 5 V.
Fig.15 Activation of Pollution sensor
To process the sensor output we have to convert the analog signal to the digital data as
microcontroller process digital data only. Hence we require Analog to digital converter.
ATmega16 has the internal 10 bit ADC which is connected to port A’s PA0. Thus, we connect
pollution a sensor analog output to the ADC input and microcontroller process the data and
displays the data on LCD and sends the information to the server via GSM.
E&TC Department R.S.C.O.E, PUNE 46 | P a g e
VEHICLE MONITORING SYSTEM
CHAPTER 5
SOFTWARE DESIGN
E&TC Department R.S.C.O.E, PUNE 47 | P a g e
VEHICLE MONITORING SYSTEM
In an embedded system software is very important, to drive the hardware as per the user
need. To make microcontroller work as per the customer’s need, program is to be burned in the
microcontroller’s memory. As per the algorithm used in the program, microcontroller will
behave. Program can be written in C language or assembly language. We have used C language
as it is easy to understand and it is speedier than any other language.
As in our project we are using ATmega16 which has an AVR processor it requires
following software to program the ATmega16.
1. WinAVRGCC
2. AVR studio
3. Pony Prog
5.1 WinAVRGCC
WinAVRTM (pronounced "whenever") is a suite of executable, open source software
development tools for the Atmel AVR series of RISC microprocessors hosted on the Windows
platform. It includes the GNU GCC compiler for C and C++. The compiler in WinAVR is the
GNU Compiler Collection, or GCC. This compiler is incredibly flexible and can be hosted on
many platforms, it can target many different processors / operating systems (back-ends), and can
be configured for multiple different languages (front-ends).
The GCC included in WinAVR is targeted for the AVR processor, is built to execute on the
Windows platform, and is configured to compile C, or C++.
GNU Binutils is a collection of binary utilities. This also includes the assembler, as. Sometimes
you will see it referenced as GNU as or gas. Binutils includes the linker, ld; the librarian or
archiver, ar. There are many other programs included that provide various functionality. avr-
libc is the Standard C Library for AVR GCC. It contains many of the standard C routines, and
many non-standard routines that are specific and useful for the AVR processor.
Debugging encompasses simulation and emulation. Both are available in WinAVR.
The GNU Debugger (GDB) is the main package that can be used for general debugging. GDB is
a command-line program only. Insight is GDB plus a GUI written in Tcl/Tk.
Both GDB and Insight are configured for the AVR and the main executables are prefixed with
the target name: avr-gdb, and avr-insight. There is now also a "text mode" GUI for GDB: avr-
gdbtui.
To do emulation with the JTAG ICE, GDB / Insight requires a "helper" program
called avarice which is also included.
E&TC Department R.S.C.O.E, PUNE 48 | P a g e
VEHICLE MONITORING SYSTEM
5.2 AVR STUDIO
AVR Studio 4 is the Integrated Development Environment (IDE) for developing 8-bit AVR
applications in Windows NT/2000/XP/Vista/7 environments. AVR Studio 4 provides a complete
set of features including debugger supporting run control including source and instruction-level
stepping and breakpoints; registers, memory and I/O views; and target configuration and
management as well as full programming support for standalone programmers.
AVR Studio 4 features
• Integrated Assembler
• Integrated Simulator
• Integrates with GCC compiler plug-in
• Support for all Atmel tools that support the 8-bit AVR architecture, including the AVR
ONE!, JTAGICE mkI, JTAGICE mkII, AVR Dragon, AVRISP, AVR ISPmkII, AVR
Butterfly, STK500 and STK600
• AVR RTOS plug-in support
• support for AT90PWM1 and ATtiny40
• Command Line Interface tools updated with TPI support
• Online help
5.3 PONY PROG
PonyProg is a serial device programmer software with a user friendly GUI framework
available for Windows95/98/ME/NT/2000/XP and Intel Linux. Its purpose is reading and writing
every serial device. At the moment it supports I²C Bus, Microwire, SPI eeprom, the
Atmel AVR and Microchip PIC micro. SI-Prog is the programmer hardware interface for
PonyProg. With PonyProg and SI-Prog you can program Wafercard for SAT, eeprom within
GSM, TV or CAR-RADIO. Furthermore it can be used as a low cost starter kit for PIC and
AVR. PonyProg works also with other simple hardware interfaces like AVR
ISP (STK200/300), JDM/Ludipipo, EasyI2C and DT-006 AVR (by Dontronics).
5.4 VISUAL BASICS
On the PC side we are using Visual basic for Graphic user interface. PC contains
database of all the drivers hence, to make the access of data simple and sophisticated we
implemented a program in visual basic. Visual Basic (VB) is an event driven programming
language and associated development environment from Microsoft for its COM programming
model. VB has been replaced by Visual Basic .NET. The older version of VB was derived
heavily from BASIC and enables the rapid application development (RAD) of graphical user
interface (GUI) applications, access to databases using DAO, RDO, or ADO, and creation of
ActiveX controls and objects.
E&TC Department R.S.C.O.E, PUNE 49 | P a g e
VEHICLE MONITORING SYSTEM
A programmer can put together an application using the components provided with Visual
Basic itself. Programs written in Visual Basic can also use the Windows API, but doing so
requires external function declarations.
In business programming, Visual Basic has one of the largest user bases. With 62% of
developers using some form of Visual Basic, it currently competes with C++ and JavaScript as
the third most popular programming language behind C# and Java.
Language features:
A typical session in Microsoft Visual Basic 6Visual Basic was designed to be easy to
learn and use. The language not only allows programmers to easily create simple GUI
applications, but also has the flexibility to develop fairly complex applications as well.
Programming in VB is a combination of visually arranging components or controls on a form,
specifying attributes and actions of those components, and writing additional lines of code for
more functionality. Since default attributes and actions are defined for the components, a simple
program can be created without the programmer having to write many lines of code.
Performance problems were experienced by earlier versions, but with faster computers and
native code compilation this has become less of an issue.
Although programs can be compiled into native code executables from version 5 onwards,
they still require the presence of runtime libraries of approximately 2 MB in size. This runtime is
included by default in Windows 2000 and later, but for earlier versions of Windows it must be
distributed together with the executable.
Forms are created using drag and drop techniques. A tool is used to place controls (e.g.,
text boxes, buttons, etc.) on the form (window). Controls have attributes and event handlers
associated with them. Default values are provided when the control is created, but may be
changed by the programmer. Many attribute values can be modified during run time based on
user actions or changes in the environment, providing a dynamic application. For example, code
can be inserted into the form resize event handler to reposition a control so that it remains
centred on the form, expands to fill up the form, etc. By inserting code into the event handler for
a key press in a text box, the program can automatically translate the case of the text being
entered, or even prevent certain characters from being inserted.
Visual Basic can create executables (EXE), ActiveX controls, DLL files, but is primarily
used to develop Windows applications and to interface web database systems. Dialog boxes with
less functionality (e.g., no maximize/minimize control) can be used to provide pop-up
capabilities. Controls provide the basic functionality of the application, while programmers can
insert additional logic within the appropriate event handlers. For example, a drop-down
combination box will automatically display its list and allow the user to select any element. An
event handler is called when an item is selected, which can then execute additional code created
E&TC Department R.S.C.O.E, PUNE 50 | P a g e
VEHICLE MONITORING SYSTEM
by the programmer to perform some action based on which element was selected, such as
populating a related list.
Alternatively, a Visual Basic component can have no user interface, and instead provide
ActiveX objects to other programs via Component Object Model (COM). This allows for server-
side processing or an add-in module.
The language is garbage collected using reference counting, has a large library of utility
objects, and has basic object oriented support. Since the more common components are included
in the default project template, the programmer seldom needs to specify additional libraries.
Unlike many other programming languages, Visual Basic is generally not case sensitive,
although it will transform keywords into a standard case configuration and force the case of
variable names to conform to the case of the entry within the symbol table entry. String
comparisons are case sensitive by default, but can be made case insensitive if so desired.
Performance:
Early versions of Visual Basic were not competitive at performing computationally
intensive tasks because they were interpreted, and not compiled to machine code. Although this
roadblock was removed with VB5 (which compiles to the same intermediate language and uses
the same back end as Visual C, some features of the language design still introduce overhead
which can be avoided in languages like Delphi or C++. These are more likely to be encountered
in code involving objects, methods, and properties than in strictly numerical code.
Simplicity:
While some detractors argue that the simplicity of Visual Basic is a weakness, many
proponents of Visual Basic explain that the simple nature of Visual Basic is its main strength,
allowing very rapid application development to experienced Visual Basic coders and a very
slight learning curve for programmers coming from other languages. Additionally, Visual Basic
applications can easily be integrated with databases, a common requirement. For example, by
using controls that are bound to a database, it is possible to write a VB application that maintains
information within the database without writing any lines of VB code.
E&TC Department R.S.C.O.E, PUNE 51 | P a g e
VEHICLE MONITORING SYSTEM
5.5 EXPRESS PCB
Express PCB is a free PCB software and is a snap to learn and use. The board
manufacturing service makes top quality two and four layer PCBs. Drawing a schematic with
TheExpressSCH program is as easy as placing the components on the page and wiring the pins
together. The schematic can then be linked to your PCB file, so that the PCB knows what needs
to be connected together. Designing 2 or 4 layer boards using the ExpressPCB program is very
simple. Start by inserting the component footprints, then drag them into position. Next, connect
the pins by drawing the traces. If you link your schematic file to the PCB,
the ExpressPCB program will highlight the pins that should be wired together in blue.
E&TC Department R.S.C.O.E, PUNE 52 | P a g e
VEHICLE MONITORING SYSTEM
CHAPTER 6
Flow Chart
E&TC Department R.S.C.O.E, PUNE 53 | P a g e
VEHICLE MONITORING SYSTEM
FLOW CHART FOR PROGRAM IN MICROCONTROLLER
E&TC Department R.S.C.O.E, PUNE 54 | P a g e
VEHICLE MONITORING SYSTEM
E&TC Department R.S.C.O.E, PUNE 55 | P a g e
VEHICLE MONITORING SYSTEM
FLOW CHART FOR PROGRAM IN VISUAL BASICS
E&TC Department R.S.C.O.E, PUNE 56 | P a g e
VEHICLE MONITORING SYSTEM
CHAPTER 7
TESTING AND
TROUBLESHOOTING
E&TC Department R.S.C.O.E, PUNE 57 | P a g e
VEHICLE MONITORING SYSTEM
7.1 PCB TESTING
Cold Test: The first step was to carry out the visual inspection of the PCB. This means to check
any short or cut in the tracks, inspects the tracks on PCB, find any missing pads. If anywhere
found on it we did mechanical repair of the same. The second step involved the continuity testing
.this means to check that the current is flowing through all the tracks or not. Thirdly, testing
solder of the socket, crystal & reset circuitry.
FAULT TROUBLESHOOTING
Voltage on Vcc pin is not 5volt Whenever the ac power supply was given to
the circuit. The IC 7805 and the core of the
transformer was dissipating undesirable
amount of heat. This could be because of the
short circuit in the PCB. Hence, PCB was
checked and short circuit was removed.
LCD was not showing any character We are using LCD with 4 bit data line and
enable and write pin also connected to the
port. This type of error could be caused
because of the improper signal given to the
enable pin. Hence. The program was again
checked and the proper signal was given to
troubleshoot the same.
Memory card’s memory was unable to access To access the memory 24C04 we are using
I2C bus protocol. In I2c protocol we have to
give external pull up to clock and data line but
the pull up used in our system was of very
small value. Hence, high pull up was used.
Program was stuck in between Program for our project was written in C
language. While debugging the program it was
observed that program was not moving ahead
from the GSM modem access loop. Hence the
function was checked and it was observed that
one AT command was missing.
E&TC Department R.S.C.O.E, PUNE 58 | P a g e
VEHICLE MONITORING SYSTEM
CHAPTER 8
CONCLUSION AND
FUTURESCOPE
E&TC Department R.S.C.O.E, PUNE 59 | P a g e
VEHICLE MONITORING SYSTEM
8.1 CONCLUSION
System has been designed for closed loop solution for complete traffic management and
pollution control. System authentication has been done through smart card and various creeper
algorithms used in it. For traffic management RFID solution has been provided in the system.
GSM modem has been used for wireless communication with the server, with
bidirectional traffic. Online pollution control is the asset of the system, gives a complete control
over whole system.
8.2 FUTURE SCOPE
Vehicle tracking using GPS.
LCD showing current status of vehicle on map showing its route.
Implementation of complete security features for vehicle.
Electronic toll collection
Fine payment through smart card
On line pollution detection
Tracking vehicle through GSM interfaces
Control of traffic through various RFID feedback system
Traffic signal monitoring and signal violation detection
E&TC Department R.S.C.O.E, PUNE 60 | P a g e
VEHICLE MONITORING SYSTEM
Annexure
E&TC Department R.S.C.O.E, PUNE 61 | P a g e
VEHICLE MONITORING SYSTEM
ANNEXURE 1
CIRCUIT DIAGRAM
E&TC Department R.S.C.O.E, PUNE 62 | P a g e
VEHICLE MONITORING SYSTEM
ANNEXURE 2
PCB ARTWORK AND LAYOUT
Layout basically means placing or arranging things in a specific order on the PCB. Layout
means placing of components in an order. This placement is made such that the interconnection
lengths are optimal .At the same time, it also aims at providing accessibility to the components
for insertion testing and repair. The PCB layout is the starting point for the final artwork
preparation layout design should reflect the concept of final equipment.
There are several factors, which we must keep in mind for placing the layout.
Schematic Diagram:
The schematic diagram forms main input document for preparation of the layout For this
purpose the software for PCB design, ORCAD was used.
Electrical and thermal requirement :
The PCB designer must be aware of the circuit performance in critical aspects of the same
concerning electrical conditions and the environment to be used in.
Mechanical requirement :
The designer should have the information about physical size of the board, type of installation of
board (vertical/horizontal). The method of cooling adopted, front panel operated components etc.
Component placing requirement:
All component are to placed first in a configuration that demands only the minimum length for
critical conductors. These key components are placed first and the others are grouped around like
satellites.
Components mounting requirements:
All components must be placed parallel to one another as far as possible .i.e. in the same
direction and orientation mechanical over stressing of solder should be avoided.
Layout Methodology:
For proper layout design minimal, steps to be followed a
1. Get the final circuit diagram and component list.
2. Choose the board types, single sided / double sided / multilayer
3. Identify the appropriate scale for layout.
4. Select suitable grid pattern.
5. Choose the correct board size keeping in view the constraints.
6. Select appropriate layout technique, manual / automated.
7. Document in the form of the layout scale.
E&TC Department R.S.C.O.E, PUNE 63 | P a g e
VEHICLE MONITORING SYSTEM
ART WORK:
Art work is accurately scaled configuration of the printed circuit from which the master
pattern is made photographically.
ART WORK RULES :
Rules followed while selecting artwork symbol takes
1. Minimum spacing between conductor and pad should be 0 / 35 mm in 1:1 scale .
2. Minimum spacing between parallel conductors should be 0.4 mm in 1:1 scale.
3. The area of non-PTH solder pad should not be less than 5 sq.mm.
4. The width of current carrying conductors should be determined for max.. temp. rise 20 ْC
GENERAL ART WORK RULES:
When there is higher conductor density assumes the conductors parallel to any one of the
edge of the board. When conductors have to be placed in other direction preference should be
given to the 45ْ direction or to the 30ْ / 60ْ direction. Whenever there is sufficient space available
the conductors can be run in any direction so as to achieve sorted possible interconnection.
As far as possible, design and the conductor on the solder pad. Conductor forming sharp
internal angles must be avoided. When a member of conductor has to run between two pads the
conductor lines are run perpendicular w.r.t. the center-to-center line of pair of pads. Equally
distributed spacing is to be provided when three or more conductors run along a direction and /
or between two pads. Minimum spacing is provided when three or more lines run along a
direction and / or between two pads. The diameter of solder pad should be approximately 8 times
the drilled hole diameter.
E&TC Department R.S.C.O.E, PUNE 64 | P a g e
VEHICLE MONITORING SYSTEM
ANNEXURE 3
LIST OF COMPONENTS AND TOTAL COST
Component Rate per
Reference Number Quantity Unit Total Cost (Rs)
Name
AVR AT-mega16 1 160 160
Microcontroller
Crystal 11MHz 1 16 16
Diode 1N4007 5 0.50 2.50
Regulator IC LM7805 1 7 7
LED Red 1 1 1
Max 232 1 16 16
DB 9 connector-F 1 12 12
RS-232 Cable 1 60 60
Resistors 220 ohm 5 0.20 1
1 Kohm 5 0.20 1
10 Kohm 5 0.20 1
Pull Up resisitor 10 Kohm 6pin 1 5 5
10Kohm 9 pin 1 5 5
Capacitors 10uf ,63V 8 5 40
1000uf ,50V 2 5 10
22uf 2 1 2
0.01uf 2 1 2
E&TC Department R.S.C.O.E, PUNE 65 | P a g e
VEHICLE MONITORING SYSTEM
IC Base 40 pin 1 4 4
16 pin 1 2 2
Transformer 12-0-12V,1A 1 120 120
PCB’s + Etching 5.5”x5.5” 1 250 250
Solder Gun Soldron 1 160 160
Multimeter 830BZ 1 230 230
Solder metal ARX 3 6 18
Connecting Wires 2 12 12
RFID Reader Bioenable 1 2500 2500
GSM modem Wavecom 1 3000 3000
Total Cost(Rs) 6640/-
E&TC Department R.S.C.O.E, PUNE 66 | P a g e
VEHICLE MONITORING SYSTEM
ANNEXURE 4
E&TC Department R.S.C.O.E, PUNE 67 | P a g e
You might also like
- SafejniDocument10 pagesSafejniAnirudha MhaseNo ratings yet
- Electronic Compass IC - HM55B (Datasheet)Document7 pagesElectronic Compass IC - HM55B (Datasheet)Anirudha Mhase100% (1)
- Project ListDocument13 pagesProject ListAnirudha MhaseNo ratings yet
- Hints and Tips For Using Surface Mount Technology (SMT)Document11 pagesHints and Tips For Using Surface Mount Technology (SMT)Anirudha MhaseNo ratings yet
- How To Build A ComputerDocument52 pagesHow To Build A ComputersankopubNo ratings yet
- Wireless Local LoopDocument31 pagesWireless Local LoopAnirudha MhaseNo ratings yet
- Electronic Compass IC - HM55B (Documentation)Document25 pagesElectronic Compass IC - HM55B (Documentation)Anirudha MhaseNo ratings yet
- CAN Specification Version 2 BOSCHDocument73 pagesCAN Specification Version 2 BOSCHdigitales100% (4)
- Online Monitoring of Exhaust Emissions Using Mid-Infrared SpectrosDocument6 pagesOnline Monitoring of Exhaust Emissions Using Mid-Infrared SpectrosAnirudha MhaseNo ratings yet
- Audio CD Player WorksDocument2 pagesAudio CD Player WorksSharmain QuNo ratings yet
- Video Compression TechniquesDocument42 pagesVideo Compression TechniquesAnirudha Mhase100% (1)
- A Novel System For The Detection and Analysis of Vehicles Exhaust PollutionDocument5 pagesA Novel System For The Detection and Analysis of Vehicles Exhaust PollutionAnirudha MhaseNo ratings yet
- Co Ak01Document2 pagesCo Ak01Kavyashree P RaoNo ratings yet
- Color TV Service ManualDocument49 pagesColor TV Service ManualAnirudha Mhase100% (4)
- Avr TutorialDocument111 pagesAvr Tutoriallabirint10100% (7)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5782)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (72)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Presentation3.pptPD Dialer TouchStar SupervisorSoftware by INAYAT ALI ABBASDocument61 pagesPresentation3.pptPD Dialer TouchStar SupervisorSoftware by INAYAT ALI ABBASinayatali123No ratings yet
- IBM Certified Solution Architect - Cloud Pak For Automation v20.0.1Document20 pagesIBM Certified Solution Architect - Cloud Pak For Automation v20.0.1Mauricio ChávarroNo ratings yet
- MQDocument197 pagesMQAnand BiradarNo ratings yet
- Semrush-Site Audit Issues-Www Whitehatjr Com-5 Déc. 2022Document11 pagesSemrush-Site Audit Issues-Www Whitehatjr Com-5 Déc. 2022Raghav sowryaNo ratings yet
- Zoo Management System: Shubham Maratha (230) Abhishek Jadhav (233) Hrushikesh Dolas (238) Namam MadariyaDocument13 pagesZoo Management System: Shubham Maratha (230) Abhishek Jadhav (233) Hrushikesh Dolas (238) Namam Madariyabhumika.verma00100% (2)
- SOP090-Reverse Engineer Your Competitor's Backlink StrategyDocument15 pagesSOP090-Reverse Engineer Your Competitor's Backlink StrategyАртем КлобаNo ratings yet
- Start - RokDocDocument12 pagesStart - RokDocdiditkusuma100% (2)
- White Paper KRI It GovernanceDocument11 pagesWhite Paper KRI It GovernancevevrinNo ratings yet
- Staad FoundationDocument25 pagesStaad FoundationAnonymous nwByj9L100% (2)
- EBuzzzz Email PDFDocument4 pagesEBuzzzz Email PDFHeatherNo ratings yet
- Data Structures LightHall ClassDocument43 pagesData Structures LightHall ClassIwuchukwu ChiomaNo ratings yet
- Symbolic ProcessorDocument18 pagesSymbolic ProcessorAyan Ganguly0% (2)
- Oracle AR SLA QueriesDocument3 pagesOracle AR SLA QueriesutkarhNo ratings yet
- BW SecurityDocument2 pagesBW SecurityBOBBILINo ratings yet
- MIS5214-Spring 2018 MidTerm-SolutionsDocument11 pagesMIS5214-Spring 2018 MidTerm-SolutionsLeary John Herza TambagahanNo ratings yet
- MSPublisher NotesDocument16 pagesMSPublisher NotesEvans OchiengNo ratings yet
- What Is Excel A Beginner's Overview DeskbrightDocument1 pageWhat Is Excel A Beginner's Overview DeskbrightLavanya ChandraNo ratings yet
- NPO Reorg IndoDocument21 pagesNPO Reorg IndoAnonymous g8YR8b9No ratings yet
- Publish Shows Keyboard ShortcutsDocument2 pagesPublish Shows Keyboard ShortcutsMAKNo ratings yet
- Electronic Engineering Laboratory IV BEE31101 Instruction Sheet BEJ40401Document13 pagesElectronic Engineering Laboratory IV BEE31101 Instruction Sheet BEJ40401sarahNo ratings yet
- Global Mapper Users ManualDocument395 pagesGlobal Mapper Users ManualCyprien YENo ratings yet
- Company ListDocument7 pagesCompany Listdipsmech18No ratings yet
- Inter Banking Screen Tracer & Black Screen Debit ConfirmationDocument3 pagesInter Banking Screen Tracer & Black Screen Debit ConfirmationMasoud Dastgerdi100% (2)
- BakkesMod Antivirus Help - Whitelist Tutorial and AV LinksDocument2 pagesBakkesMod Antivirus Help - Whitelist Tutorial and AV LinksNicolas MadeiraNo ratings yet
- DB211 - Unit 9 Assignment ADocument3 pagesDB211 - Unit 9 Assignment ATim WilliamsNo ratings yet
- TideMaster Operating ManualDocument59 pagesTideMaster Operating Manualyushantono100% (1)
- Plant Automation and Telecontrol in One System: Simatic Pcs 7Document8 pagesPlant Automation and Telecontrol in One System: Simatic Pcs 7alainNo ratings yet
- 3-Tier ArchitectureDocument4 pages3-Tier ArchitecturepalakayalaNo ratings yet
- Seminar ReportDocument42 pagesSeminar Reportsammuel john100% (1)
- Post - Detail - Information RI ARI AMINDocument18 pagesPost - Detail - Information RI ARI AMINHarish MohantyNo ratings yet