Professional Documents
Culture Documents
Figerprint Based Evm Journal
Uploaded by
venuOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Figerprint Based Evm Journal
Uploaded by
venuCopyright:
Available Formats
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Fingerprint and RFID based Electronic Voting
System Linked with AADHAAR for rigging
free elections
1
B.Mary Havilah Haque , G.M.Owais Ahmed2,D.Sukruthi3, K.Venu Gopal Achary4,C.Mahendra Naidu5
Assistant Professor, Dept. of ECE, Brindavan Institute of Technology & Science, Kurnool, Andhra Pradesh, India
UG Student (B.Tech), Dept. of ECE, Brindavan Institute of Technology & Science, Kurnool, Andhra Pradesh, India2-5
ABSTRACT: This paper proposes a method for safe and secure aadhaar based biometric voting system to avoid
misconceptions which are going to takes place in elections. From last few years in India, aadhaar enrollment
process is going on in Andhra Pradesh. At that time, Indian government collects details of finger prints and IRIS
of every person. This entire data of each and every person persists in the database of Indian government. If Indian
Government links this database to authors proposed method, Indian Government no need to collect details of
finger print of every person. So, if Indian Government adopts biometric voting system for voting purpose, we can
easily avoid rigging in elections. One more advantage of this project is, if an alcoholic person enters into
polling booth, buzzer will alert authorized persons or constables who are in election duty. Because of Alcoholic
sensor, we can provide peaceful environment at polling booth. If an unauthorized person enters into polling booth
to cast his vote, buzzer will alert booth level officer. If already vote casted person enters into booth with his
RFID tag for 2nd time voting, then also buzzer will alert booth level officer.
KEYWORDS: AADHAAR, EPIC, Finger Print Identification Module, RFID, GAS SENSOR, ALCOHOL
SENSOR, METAL DETECTOR
I.
INTRODUCTION
After getting freedom, Indian Government provide a right to Indian people to elect their interested leader. For
conducting and controlling voting in India, a separate commission was introduced which was named as Election
Commission of India(ECI). This commission is not favorable or support to any political party. As per rules
which have been in law, this commission works. For the persons, who have age of 18 and above are eligible to
enroll their vote. To cast their vote, Election commission provides voter id cards. From last few decades paper
voting procedure is going on. After polling votes in polling booths, Those paper format votes have been placed in
ballot boxes. That entire box placed in the rooms of schools or colleges. If those rooms are perfect with
interior walls, then there is no problem. If those inner walls are older one, then ants will damage that valuable
ballot box. At this instant, Election commission needs to conduct elections at that particular place once again.
Electronic voting (also known as E-voting) is voting using electronic systems to aid casting and counting
votes. Voting machines use a two-piece system with a balloting unit presenting the voter with a button for each
Copyright to IJAREEIE
1
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
choice connected by a cable to an electronic ballot box.
An EVM consists of two units:
1. Control Unit
2. Balloting Unit
The two units are joined by a five-meter cable. The Control Unit is with the Presiding Officer or a Polling
Officer and the Balloting Unit is placed inside the voting compartment. Instead of issuing a ballot paper, the
Polling Officer in-charge of the Control Unit will press the Ballot Button. This will enable the voter to cast his
vote by pressing the blue button on the Balloting Unit against the candidate and symbol of his choice. The
controller used in EVMs has its operating program etched permanently in silicon at the time of manufacturing by
the
manufacturer. No one can change the program once the controller is manufactured.
The main drawback of this system is that, voters id checking process is manual hence possibilities of illegal
voting by a wrong candidate. And also, possibility of multiple votes by same person. To avoid this problem,
Author going to use E- voting system.
st
In this project, two step verification goes on. In 1 step, RFID tag is verified with data base of AT89S52 to
nd
check whether the person belongs to that particular polling booth or not. In 2 step, Finger print scanner is used
to check whether the voter is original or not. If these two steps are successful then microcontroller enables
switches to cast vote to particular political party. RFID tag contains its own ID. When we place this RFID tag
near RFID reader, it reads the Tag ID. It will be checked with the database of micro controller. If that Tag ID
persists in the database of microcontroller, then the information related person(name of the person, AADHAAR
Number, Voter Number)will be revealed on LCD screen. In our project, for enrolling purpose, Enroll button is
provided. If voter is not enroll his Vote on the database of microcontroller, Vote will not be casted. After casting
votes, results will be announced through LCD display. LCD display is an instructor for citizens of India to follow
step by step procedure. Our proposed system will detect alcoholic person who tries to enter into polling
booth. Alcoholic person doesnt have patience. He dont know what is going on around him while he was in
drunk state. He can create nuisance at polling booth. To avoid this kind of nuisance alcoholic sensor is used.
II.
SYSTEM ANALYSIS AND RELATED WORK
1) RFID:
In this project, four RFID tags have been used. Each and every tag contains the information related to
individual voters. Our micro controller AT89S52 contains the following details such as Name of the voter, voter
ID, AADHAAR ID, Date of Birth of the voter. When RFID tag placed near to RFID reader, RFID reader
activate the details of particular information of RFID tag which is preloaded into micro controller memory. If
that RFID tag exists in the database of micro controller, then biometric authentication process. Else, our system
goes to check next RFID Tag. In this way, entire voting process goes on. RFID tag transmits its information to
the RFID reader by taking advantage of the fact that each time the tag draws energy from the RFID reader's
magnetic field, the RFID reader itself can detect a corresponding voltage drop across its antenna leads.
Capitalizing on this phenomenon, the tag can communicate binary information to the reader by switching ON
and OFF a load resistor to perform load modulation.
Copyright to IJAREEIE
2
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
2) Fingerprint Identification Module:
Fingerprint processing includes two parts: fingerprint enrollment and fingerprint matching (the matching can
be 1:1 or 1:N).When enrolling, user needs to enter the finger two times. The system will process the two time finger
images, generate a template of the finger based on processing results and store the template. When matching, user
enters the finger through optical sensor and system will generate a template of the finger and compare it with
templates of the finger library. For 1:1 matching, system will compare the live finger with specific template
designated in the Module; for 1:N matching, or searching, system will search the whole finger library for the
matching finger. In both circumstances, system will return the matching result, success or failure.
Fig 1. R305 Module
In this proposed paper, Finger print Optical scanner is used for authentication purpose. When RFID tag
authentication occurs, user need to go for second stage authentication. There is a scope to misuse of votes if we
wont adopt biometric voting system. There is scope to use of RFID Tag by somebody to cast some ones vote
illegally. To avoid this, we are using biometric voting system. Finger prints of each and every person may get
varied. None of a man in the earth have same kind of finger prints. Finger print optical scanner is an input
module for AT89S52. After 1st stage verification, user need to put his proper thumb upon fingerprint scanner. If
that particular fingerprint matches with the database of AT89S52 then only switches will be enabled by AT89S52
to cast vote.
Fingerprint is very safe and convenient device for security instead of password that is vulnerable to fraud and is
hard to remember biometric process for authentication, identification and verification functions that let your
fingerprints act like digital passwords that cannot be lost, forgotten or stolen.
3) Liquid Crystal Display:
LCD stands for Liquid Crystal Display. LCD components are specialized for being used with the
microcontrollers, which means that they cannot be activated by standard IC circuits. They are used for writing
different messages on a miniature LCD.
In authors proposed paper, LCD display is an output module which have been controlled by AT89S52.
When user places RFID tag near RFID reader, user details will be displayed on LCD screen. If those details
belongs to you, then it asks for place your finger upon module for authentication (Please verify your Thumb
Impression.).if your thumb impression matches with data base, one message will be displayed like this,
Copyright to IJAREEIE
3
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Authentication SUCCESSFUL PLEASE CAST YOUR VOTE. To cast your vote, you need to switch a button
which is present in the ballot. If LED blinks once, then one message will be shown like this in the LCD screen,
nd
YOUR VOTE IS CASTED SUCCESSFULLY. If a person enters 2 time to cast his vote, then an error
message will be likes this ALERT!! YOUR VOTE IS ALREADY CASTED. If an alcoholic person enters
into booth, then an error message on the LCD screen will be like this ALCOHOLIC person Entered. BE
ALERT. If an unauthorized RFID tag enters into the field of RFID reader, a proper error message will be shown
like this.. YOUR CARD is UNAUTHORISED. Like this LCD module useful in our project.
4) Switches:
In this project, instead of EVM(Electronic Voting Machine), switches are used to cast vote by voters. Here four
switches have been provided named as SW1,SW2,SW3 and result button. Each and every switch belongs to
their respective political party except result button. Moreover in authors project for enrolling voters, Enroll
Button is provided. While casting vote, user need to press a button named as Authentication Button. If the
person is Already enrolled one, then only vote casting takes place. When voter press a button named as
SW1, vote is polled for respective political party. Like this, entire voting process completes. After voting process
completes, when election commission opens the result by using particular confidential password, then only list
of polled votes to particular political party will be shown on LCD screen. Based on that information, user has to
decide who is the winner.
5) RS232 (Serial Communication Interface):
In this project, RS232 serial data transmission cable is used to connect finger print module with AT89S52.
In general images will be store in chip memory in the form of binary digits like ON(1) and OFF(0). Like this,
voters finger print also stored in the memory of ARM7 in the form of Binary digits. When we place our finger
for biometric authentication, the data will be transfer to AT89S52 in the form of stream of bits serially through
RS232 cable. This entire stream of bits will be collected and compared by AT89S52. If perfect match found,
voting process initiated.
UART (Universal Asynchronous Receiver Transmitter) or USART (Universal Synchronous Asynchronous
Receiver Transmitter) are one of the basic interface which you will find in almost all the controllers available in
the market till date. This interface provide a cost effective simple and reliable communication between one
controller to another controller or between a controller and PC.
6) Smoke or Alcohol Sensor and Metal Detector:
MQ5 is basically a smoke sensor. We can also use it for detecting alcoholic person. If we adjust sensitivity of
MQ5 using potentiometer, we can get better results in spite of weather conditions are bad. Most of Alcoholic
persons will create nuisance everywhere in the public. Due to this, decent voters suffers from lots of problems.
Because of this, election in that particular polling booth is going to cancel. To avoid these kind of serious
problems author had adopted alcohol sensor. In this project, to detect alcoholic person MQ5 sensor is used.
In this project, Metal detector is used to detect a person who have been entering into polling booth with gun
or knifes. Here, Metal detector will alert us to faraway Maoists from polling booth. Authors project is especially
for safe and secure voting.
Resistance value of MQ-5 is different for different gases. We need to adjust sensitivity by varying resistance
value for various concentration of gases. For example, the concentration of gases for LPG, Natural Gas, Cigarette
Copyright to IJAREEIE
4
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
and Town Gas are not unique. Based on requirement, we have to adjust resistance to get better sensitivity.
III.
BLOCK DIAGRAM
Fig 2. Block Diagram of our Project
IV.
APPLICATIONS OF OUR PROJECT
1.
Especially for safe and Secure Voting using Biometric System.
2.
To Detect Alcoholic person who tries to enter into polling booth.
3.
To detect moist who are trying to enter into polling booth with guns and bombs.
4.
To Detect Gas Leakage near polling booth.
5.
AADHAAR, VOTER ID(EPIC) Linked with RFID Tag to avoid dummy votes.
V.
Copyright to IJAREEIE
5
FLOW CHART OF OUR PROJECT
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Fig 3. Flow Chart of our Proposed System
VI.
Copyright to IJAREEIE
6
STATE TRANSITION DIAGRAM
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Fig 4. State Diagram of our Proposed System
VII.
OVERVIEW OF OUR SYSTEM
Fig 5. Overview of our system
VIII.
FUTURESCOPE
If we adopt, IRIS Technology for authentication purpose, we can get better results compared to Biometric
System. If we provide networking among polling booths with AADHAAR data collected Server with the help
of internet, we can easily get better security. If we use very sensitive alcohol sensor and metal detector, we can
provide better safety and peaceful environment near polling booth.
Copyright to IJAREEIE
7
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Fig 6. Our proposed system architecture with internet and AADHAAR database
IX.
Copyright to IJAREEIE
8
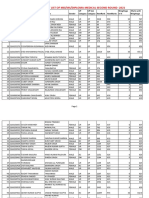
RESULTS AND DISCUSSION
DOI:10.15662/IJAREEIE.2015.0503001
3765
ISSN (Print) : 2320
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Fig 8. Results of our project
Copyright to IJAREEIE
9
DOI:10.15662/IJAREEIE.2015.0503001
ISSN (Print) : 2320
3765
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
X.
CONCLUSION
Our project provides safety and security in voting process. Our system provides security with RFID based
Biometric Voting Method. And provides safety from alcoholic persons and Maoists who comes to polling booth to
blast polling booth. This system perfectly suited for 99% of voters. The remaining 1% is who are physically
handicapped. If we adopt face recognition based retinal scan method, we can solve this authentication problem up
to 100%. Our system is linked to AADHAAR to avoid votes duplication. This system inter linked with three
primary specifications such as voter id, AADHAAR ID, Biometric Authentication. There is no scope to take place
rigging in elections.
XI.
REFERENCES
[1] Tai-Pang Wu, , Sai-Kit, Yeung,JiayaJia, Chi-Keung Tang, AndGe RardMedioni Closed-Form Solution To Tensor Voting:Theory And
ApplicationsTransactions On Pattern Analysis And Machine Intelligence, Vol. 34, No. 8, August 2012
[2] Scott Wolchok, Eric Wustrow, Dawn Isabel, and J. Alex Halderman Attacking the Washington, D.C. Internet Voting System In Proc. 16th
Conference on Financial Cryptography & Data Security, Feb. 2012H. Khalife, N. Malouch, S. Fdida, Multihop cognitive radio networks: to route
or not to route, IEEE Network, vol. 23, no. 4, pp. 20-25, 2009.
[3] D. Ashok Kumar, T. UmmalSariba Begum A Novel design of Electronic Voting System Using Fingerprint International Journal Of Innovative
Technology & Creative Engineering (Issn: 2045-8711) Vol.1 No.1 January 2011P. K. Visscher, How Self-Organization Evolves, Nature, vol.
421, pp. 799800 Feb.2003.
[4] DavideBalzarotti, Greg Banks, Marco Cova, ViktoriaFelmetsger, Richard A. Kemmerer, William Robertson,Fredrik Valeur, And Giovanni Vigna,
An Experience In Testing The Security Of Real-World Electronic Voting Systems Ieee Transactions On Software Engineering, Vol. 36, No. 4,
July/August 2010
XII.
BIOGRAPHY
Ms.B.Mary Havilah Haque1 was born in Guntakal, Andhra Pradesh, India. She received her Masters
degree in Electronics and Communication Engineering from Karunya University, Coimbatore in 2015 and is
working as an Assistant Professor at Brindavan Institute of Technology and Science, Kurnool, India. Her
research interests focus on security and wireless networks.
Mr.G.M.Owais Ahmed2 was born in Kurnool, Andhra Pradesh, India. He is pursuing his B.Tech in
Electronics and Communication Engineering from Brindavan Institute of Technology & science, Kurnool.
His areas of interest are Embedded System and its security and Communications.
Ms.D.Sukruthi3 was born in Kurnool, Andhra Pradesh, India. She is pursuing her B.Tech in Electronics
and Communication Engineering from Brindavan Institute of Technology & science, Kurnool. Her areas of
interest are Embedded Systems.
Mr.K.Venu Gopal Achary4 was born in Kurnool, Andhra Pradesh, India. He is pursuing his B.Tech in
Electronics and Communication Engineering from Brindavan Institute of Technology & science, Kurnool.
His areas of interest are Embedded System and Android Applications.
Copyright to IJAREEIE
10
DOI:10.15662/IJAREEIE.2015.0503001
ISSN (Print) : 2320
3765
ISSN (Online): 2278
8875
International Journal of Advanced Research in Electrical,
Electronics and Instrumentation Engineering
(An ISO 3297: 2007 Certified Organization)
Vol. 5, Issue 3, March 2016
Mr.C.Mahendra Naidu5 was born in Kurnool, Andhra Pradesh, India. He is pursuing his B.Tech in
Electronics and Communication Engineering from Brindavan Institute of Technology & science, Kurnool.
His areas of interest are Embedded System and its Applications.
Copyright to IJAREEIE
11
DOI:10.15662/IJAREEIE.2015.0503001
You might also like
- 50th Anniversary of Korean War Issue, Military ReviewDocument98 pages50th Anniversary of Korean War Issue, Military ReviewBob CashnerNo ratings yet
- USAID Civil Society Engagement ProgramDocument3 pagesUSAID Civil Society Engagement ProgramUSAID Civil Society Engagement ProgramNo ratings yet
- Nishida Kitaro Ontology of Production Three EssaysDocument218 pagesNishida Kitaro Ontology of Production Three EssaysJacqueChe100% (1)
- Biometrics Using Electronic Voting System With Embedded SecurityDocument8 pagesBiometrics Using Electronic Voting System With Embedded SecurityrashmibuntyNo ratings yet
- IJCRTT020017Document15 pagesIJCRTT020017KamanziNo ratings yet
- Fin Irjmets1665293271Document7 pagesFin Irjmets1665293271sdarwindNo ratings yet
- Biometric Voting Machine Based On Finger Print Scanner and ArduinoDocument5 pagesBiometric Voting Machine Based On Finger Print Scanner and Arduinovamsi saiNo ratings yet
- Biometric Voting MachineDocument14 pagesBiometric Voting MachineNationalinstituteDsnrNo ratings yet
- Iot Based Voting Machine With Fingerprint VerificationDocument8 pagesIot Based Voting Machine With Fingerprint VerificationLionel BoopathiNo ratings yet
- 08289010Document3 pages08289010Avinash ReddyNo ratings yet
- Unique ID Based Voting SystemDocument8 pagesUnique ID Based Voting SystemIJRASETPublicationsNo ratings yet
- IoT Based Voting Machine With Fingerprint VerificationDocument9 pagesIoT Based Voting Machine With Fingerprint VerificationIJRASETPublicationsNo ratings yet
- Smart Voting System IJERTV8IS040257Document3 pagesSmart Voting System IJERTV8IS040257hx hNo ratings yet
- Aadhaar-Based E-Voting MachineDocument87 pagesAadhaar-Based E-Voting MachineChandu ChandrakanthNo ratings yet
- Biometric Based Secured Remote Electronic Voting SystemDocument5 pagesBiometric Based Secured Remote Electronic Voting SystemRushikesh Dale PatilNo ratings yet
- Aadhar Based Electronic Voting Machine PDFDocument4 pagesAadhar Based Electronic Voting Machine PDFSreekanth PagadapalliNo ratings yet
- Biometric System Based Electronic Voting MachineDocument3 pagesBiometric System Based Electronic Voting MachineEditor IJRITCC100% (1)
- Bio Metric Authentication System Based On Aadhar Card: 2. Previous WorkDocument6 pagesBio Metric Authentication System Based On Aadhar Card: 2. Previous Worku prasanna kumar ulluriNo ratings yet
- Design of Highly Secured Biometric Voting SystemDocument4 pagesDesign of Highly Secured Biometric Voting SystemDarshan MNo ratings yet
- Fingerprint Based Voting Machine Using ARM7Document5 pagesFingerprint Based Voting Machine Using ARM7Sumayya FathimaNo ratings yet
- Fingerprint Identification System Based Voting MachineDocument6 pagesFingerprint Identification System Based Voting MachineInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Aadhar Based Election Voting SystemDocument4 pagesAadhar Based Election Voting SystemManpreet Singh100% (1)
- FUID SEVM Fingerprint Unique ID Smart Electronic Voting MachineDocument8 pagesFUID SEVM Fingerprint Unique ID Smart Electronic Voting MachineIJRASETPublicationsNo ratings yet
- SamarthA RP ICSSS2020 CamreadyDocument5 pagesSamarthA RP ICSSS2020 CamreadySamarth AgarwalNo ratings yet
- PPTDocument21 pagesPPTBujji GaduNo ratings yet
- Secure and Efficient Electronic Voting Machine Using IoTDocument8 pagesSecure and Efficient Electronic Voting Machine Using IoTIJRASETPublicationsNo ratings yet
- Arduino based fingerprint voting systemDocument18 pagesArduino based fingerprint voting systemSravaniNo ratings yet
- Journal of Environmental Science, Computer Science and Engineering & TechnologyDocument7 pagesJournal of Environmental Science, Computer Science and Engineering & TechnologyMuhamad RamadanNo ratings yet
- Advanced Electronic Voting Machine: Mathew AbrahamDocument4 pagesAdvanced Electronic Voting Machine: Mathew AbrahamPoly Ben AntonyNo ratings yet
- Fingerprint Based Electronic Voting Machine: ISSN (PRINT) : 2393-8374, (ONLINE) : 2394-0697, VOLUME-5, ISSUE-2, 2018Document4 pagesFingerprint Based Electronic Voting Machine: ISSN (PRINT) : 2393-8374, (ONLINE) : 2394-0697, VOLUME-5, ISSUE-2, 2018Kalu SamuelNo ratings yet
- FinalDocument29 pagesFinalgajjala402No ratings yet
- Modernized Voting Machine Using Fingerprint Recognition 1383911867Document7 pagesModernized Voting Machine Using Fingerprint Recognition 1383911867Beekaan AlamuuNo ratings yet
- Biometric Voting Machine: International Research Journal of Engineering and Technology (IRJET)Document11 pagesBiometric Voting Machine: International Research Journal of Engineering and Technology (IRJET)Vits18 0573No ratings yet
- IoT Based Biometric Voting SystemDocument12 pagesIoT Based Biometric Voting SystemNgezeNo ratings yet
- Java Cards in Voting SystemDocument17 pagesJava Cards in Voting SystemstrokenfilledNo ratings yet
- C O A W: Ertificate F Uthenticated ORKDocument35 pagesC O A W: Ertificate F Uthenticated ORKsuman2winNo ratings yet
- Arduino Based Smart and Remote Voting System With Smart Card Implementation and Dual Biometric AuthenticationDocument8 pagesArduino Based Smart and Remote Voting System With Smart Card Implementation and Dual Biometric AuthenticationIJRASETPublicationsNo ratings yet
- An Online Voting System Using Biometric Fingerprint and Aadhaar CardDocument6 pagesAn Online Voting System Using Biometric Fingerprint and Aadhaar CardNahidaNigarNo ratings yet
- Part 3 PDFDocument29 pagesPart 3 PDFAnonymous mDP2v0HNo ratings yet
- E Voting Using AadharDocument7 pagesE Voting Using AadharSaivenkat BingiNo ratings yet
- DiGiVoter An Online Voting SystemDocument10 pagesDiGiVoter An Online Voting SystemIJRASETPublicationsNo ratings yet
- 256 - IOT - Aadhar Card Based Biometrics Electronic Voting System With Embedded Security Along With Remote AccessDocument8 pages256 - IOT - Aadhar Card Based Biometrics Electronic Voting System With Embedded Security Along With Remote Accessnanda dhapteNo ratings yet
- Fingerprint Exam Hall AuthenticationDocument5 pagesFingerprint Exam Hall AuthenticationHarsh SinghNo ratings yet
- A Review Paper On Improving Security of ATM SystemDocument4 pagesA Review Paper On Improving Security of ATM SystemEditor IJRITCCNo ratings yet
- A Matlab Based Electronic Voting MachineDocument7 pagesA Matlab Based Electronic Voting MachineIJRASETPublicationsNo ratings yet
- A Secured Approach For Authentication System Using Fingerprint and IrisDocument6 pagesA Secured Approach For Authentication System Using Fingerprint and Iriss_sankaraaNo ratings yet
- Anti-Rigging Voting System Smart CardDocument4 pagesAnti-Rigging Voting System Smart CardkarthikdmNo ratings yet
- DigiVoter-Smart Voting System Using Biometrics-Based Facial FeaturesDocument8 pagesDigiVoter-Smart Voting System Using Biometrics-Based Facial FeaturesIJRASETPublicationsNo ratings yet
- Iot Based Smart Public Distribution SystemDocument5 pagesIot Based Smart Public Distribution Systemmishranintin543No ratings yet
- (IJCST-V9I2P5) :kevin Gabriel Houlder, Nithishwar P, Santhosh G, Venkatesh EDocument7 pages(IJCST-V9I2P5) :kevin Gabriel Houlder, Nithishwar P, Santhosh G, Venkatesh EEighthSenseGroupNo ratings yet
- Smart Voting System With Face RecognitionDocument3 pagesSmart Voting System With Face RecognitionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- V.online Voting SystemDocument15 pagesV.online Voting SystemNitesh ChauhanNo ratings yet
- A Secured Automated Bimodal Biometric Electronic Voting SystemDocument8 pagesA Secured Automated Bimodal Biometric Electronic Voting SystemIAES IJAINo ratings yet
- A Novel Method of E-Voting System Using Biometrics Thumb Impression and Face RecognitionDocument4 pagesA Novel Method of E-Voting System Using Biometrics Thumb Impression and Face RecognitionLionel BoopathiNo ratings yet
- SmartDocument34 pagesSmartKaushikNo ratings yet
- Aadhar Based Electronic Voting SystemDocument4 pagesAadhar Based Electronic Voting SystemEditor IJTSRDNo ratings yet
- Online Voting System for Secure AuthenticationDocument4 pagesOnline Voting System for Secure AuthenticationTriono HidayatNo ratings yet
- 1) Karthik S 1BH15EC003 2) Darshan R 1BH16EC003 3) Rupini R 1BH16EC014 1) Auto Temperature Detector For Entrance Covid SafetyDocument7 pages1) Karthik S 1BH15EC003 2) Darshan R 1BH16EC003 3) Rupini R 1BH16EC014 1) Auto Temperature Detector For Entrance Covid SafetyPuneethHjNo ratings yet
- Convenient Voting MachineDocument6 pagesConvenient Voting MachineInternational Journal of Research in Engineering and TechnologyNo ratings yet
- Review of Related LiteratureDocument4 pagesReview of Related LiteratureJovit S. AlbinoNo ratings yet
- Beyond Biohacking: Remote Electromagnetic Microchips Implantation and the Coming Age of Human Augmentation: 1A, #1From EverandBeyond Biohacking: Remote Electromagnetic Microchips Implantation and the Coming Age of Human Augmentation: 1A, #1No ratings yet
- BTEFA Minutes of January 30,2023 MeetingDocument7 pagesBTEFA Minutes of January 30,2023 MeetingJoshua AssinNo ratings yet
- Global Traffic Technologies v. STCDocument7 pagesGlobal Traffic Technologies v. STCPriorSmartNo ratings yet
- Social Teachings of The Church: Rights and ResponsibilitiesDocument23 pagesSocial Teachings of The Church: Rights and ResponsibilitiesKê MilanNo ratings yet
- 2022 Farewell To The German IdeologyDocument19 pages2022 Farewell To The German IdeologyJames BNo ratings yet
- TOI Hyderabad 22.11.2019Document32 pagesTOI Hyderabad 22.11.2019Vibhats VibhorNo ratings yet
- German Management Style ExploredDocument3 pagesGerman Management Style ExploredNaveca Ace VanNo ratings yet
- Student-Father Mobile Stream DatabaseDocument20 pagesStudent-Father Mobile Stream DatabaseDeepak DasNo ratings yet
- EIIB Employees Challenge Deactivation OrderDocument7 pagesEIIB Employees Challenge Deactivation OrderjannahNo ratings yet
- Consti 01Document57 pagesConsti 01Malen Roque SaludesNo ratings yet
- Secret of Shimla AgreementDocument7 pagesSecret of Shimla Agreement57i100% (1)
- A History of England's Irish Catholic Slavery in America and Throughout The WorldDocument6 pagesA History of England's Irish Catholic Slavery in America and Throughout The WorldConservative Report100% (1)
- X. Property Relations - Salas, Jr. Vs AguilaDocument2 pagesX. Property Relations - Salas, Jr. Vs AguilaSyElfredG100% (1)
- Anderson - Toward A Sociology of Computational and Algorithmic JournalismDocument18 pagesAnderson - Toward A Sociology of Computational and Algorithmic JournalismtotalfakrNo ratings yet
- M.A (Pol Science) Scheme of StudyDocument2 pagesM.A (Pol Science) Scheme of StudyahsanNo ratings yet
- UP MDMS Merit List 2021 Round2Document168 pagesUP MDMS Merit List 2021 Round2AarshNo ratings yet
- Should Women Work at Late Night Shifts in Offices ?Document13 pagesShould Women Work at Late Night Shifts in Offices ?RITIKANo ratings yet
- Problems Faced by Children Growing Up With Two CulturesDocument4 pagesProblems Faced by Children Growing Up With Two CulturesPrabhjot Singh90% (10)
- FP Mumbai Edition 23 January 2024Document28 pagesFP Mumbai Edition 23 January 2024Hrushikesh ShejaoNo ratings yet
- Ucsp (Reviewer)Document4 pagesUcsp (Reviewer)Jewel ValenciaNo ratings yet
- Regu PramukaDocument3 pagesRegu Pramukazakyabdulrafi99No ratings yet
- Global DemocracyDocument42 pagesGlobal DemocracyAlex MárquezNo ratings yet
- National Judicial Service-ThaniaDocument26 pagesNational Judicial Service-ThaniaAnn Thania Alex100% (1)
- LA DPW Engineering NewsletterDocument12 pagesLA DPW Engineering NewsletterBill RosendahlNo ratings yet
- National ARtistDocument6 pagesNational ARtistFrancis DacutananNo ratings yet
- Types of UnemploymentDocument2 pagesTypes of UnemploymentSwapnil PednekarNo ratings yet
- Government of India Act (1935) Study MaterialsDocument2 pagesGovernment of India Act (1935) Study Materialschandan kumarNo ratings yet
- MECA News Summer 2012Document8 pagesMECA News Summer 2012Middle East Children's AllianceNo ratings yet