Professional Documents
Culture Documents
Detecting Attacks in Wireless Sensor Network Using Genetic Algorithms
Uploaded by
premsonyCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Detecting Attacks in Wireless Sensor Network Using Genetic Algorithms
Uploaded by
premsonyCopyright:
Available Formats
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
Detecting Attacks in Wireless Sensor Network Using Genetic Algorithms
1
1
Novin Makvandi, 2Seyyed Mohsen Hashemi, 3Peiman Haghighat
Student of Department of Computer Engineering, Islamic Azad University (IAU), UAE Branch, Dubai, UAE,
nmakvandi@yahoo.com,
2
Faculty of Department of Software Engineering and Artificial Intelligence, Science and Research Branch,
Islamic Azad University, Tehran, Iran
isrup@yahoo.com,
3
Faculty of Department of Computer Engineering, Islamic Azad University (IAU), UAE Branch Dubai, UAE,
P_haghighat@iau.ae
ABSTRACT
1 INTRODUCTION
Wireless Sensor Network (WSN) technology has
attracted much attention in recent years and enables
new applications but it requires nonconventional
paradigms for the protocol design due to limited
amount of energy source, memory, and computation
constraints. This technology is used in military,
medicine, environmental and industrial monitoring
applications. Many attempts have been done, to
promote these networks in order to meet objectives
such as increasing lifetime, speed of transfer
information, quality of service and security. One of the
challenging subjects in these networks is surveying the
security attacks to the network layer and finding a
solution for them. Thus, we need to establish a method
which can detect the attack and disable the attacker
from the network access, by using the minimum battery
consumption, and with a simple, effective and robust
algorithm to perform our objectives.
The purpose of this research is to identify the threats
detected by clustering genetic algorithm in the
clustered sensor networks, which will lead to prolong
the network lifetime. In addition, the optimal routing is
done by applying fuzzy function. The simulation results
show that the simulated genetic algorithm has speeded
up the detection and improved the energy consumption
cost.
KEYWORDS
Wireless sensor network, detecting attack, genetic
algorithm, fuzzy function, energy
ISBN: 978-0-9891305-5-4 2014 SDIWC
Sensor networks consist of a large number of tiny
sensor nodes that are used to collect and process
environmental information. These tiny sensor
nodes consist of three parts: sensors, information
processing and information exchange (in wireless
format). Security is a vital requirement for many
applications of sensor networks. However, with the
limited capabilities of smart sensors (battery
storage, CPU, memory, etc.) and the unfavorable
development environment of a sensor network
(infrastructure-less, unattended, wireless, ad-hoc,
etc) makes this problem so challenging.
The attacker can easily perform an internal attack
with converting the data, ignoring the messages,
selected forwarding, making disruptive noise, etc.
The internal attackers are highly destructive for
the network performance.
An inexpensive sensor has a limited memory
capacity and limited computing capabilities so it
cannot create a log file for tracking and
identifying the internal attacks. Moreover, due to
the large scale of the networks and their
infrastructure-less architectures, the central
station cannot use the data collected to identify
attacker node. A detection plan should be
designed locally and computationally efficient to
reduce battery power and bandwidth. In addition,
the only resources available for tracing
374
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
algorithms are the communication activities within
a limited range, which will create a new challenge
in detecting internal attacker. Considered the
algorithm should be based on local data.
The attacks in wireless sensor networks can be
categorized to the ones occurring at physical,
communication (access control to media or
interface), network, transfer, and application
layers attacks. The attacks can also be divided into
two categories: internal and external [3].
The main function of wireless sensor networks is
sensing the environmental events and transferring
the information to the base station for further
processing. Thus, routing is an essential operation
in sensor networks. A number of routing protocols
has been proposed for sensor networks. So routing
in wireless sensor networks is the best way of
providing security and detecting attacks in these
networks [7].
2REVIEW
Many universities and research institutions have
started to work on these networks. Most of them
were performed with the financial help of DARPA.
Briefly, the projects are as follow: Building an
operating system for sensor nodes, creating
sensors of very small size and up to a dollar,
known as Smart Dust, at UC Berkeley, Using
sensor nodes to create pervasive computing at
Carnegie
Mellon
University
and
the
Massachusetts Institute of Technology.
Guo[2010]et.al has shown that the genetic
algorithm is an appropriate solution to find the
optimal path for WSN[4].
Younis[2006]et.al , have proposed a survey on
clustering algorithms for WSN. The result shows
that this clustering has best routing and long
lifetime for WSN [6].
Khanna[2009] et.al, have proposed Reduced
Complexity Intrusion Detection in Sensor
Networks Using Genetic Algorithm. The proposed
method increases lifetime in WSN with GA [2].
ISBN: 978-0-9891305-5-4 2014 SDIWC
3 PROPOSED METHOD
Evolutionary algorithms can be an effective
method for finding the path with optimal
consumption of energy in wireless sensor
networks.
In Genetic algorithms, each solution might be
shown as a binary string (chromosome) and the
measurement of the related fitness function.
Successive solutions are parts of an evolutionary
process, in which one of the selective solutions
chooses an individual to set for the next
generation. The probability of choosing a solution
is presented as follows:[1]
(1)
In which Pi is the probability of choosing a
specific solution for the parent population. Fi is
the fitness function of the candidate solution and N
is all of the optimal ways for a population.
In this treatise, genetic algorithm is used to
distribute the randomly deployed sensors with the
clustered network. The network is divided to
optimal number of independent clusters with the
cluster heads. The proposed method uses the
genetic algorithm for clustering and performs the
routing based on the fuzzy selection, which is
addressed to detect the attacker nodes routing.
The incompatible (malicious) nodes provide extra
observations of the network behavior due to
analyzing the sensor events in its neighborhood.
The considered cases consist of:
Data massage patterns, massage collision, the
active trend of traffic rout, sensor positioning, and
synchronized events.
An important issue in these networks is increasing
the lifetime. Long communication distance
between sensors and the sink in a wireless sensor
network consumes a lot of energy and decreases
the network lifetime [5]. As clustering can reduce
energy consumption for the wireless sensor
network, we can reduce the communication
375
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
distance significantly and prolong the network
lifetime as a result.
a. Initial population random (Random
selection from distance, energy)
First, we use genetic algorithm for clustering the
network. It has a significant role in decreasing the
energy consumption and optimized routing.
b. Crossover (node); // A New child is created
with 2 parents. Then the distance between the new
node and the sink is determined
In this treatise, genetic algorithm is used to
distribute the randomly deployed sensors with the
clustered network.
c. Mutation (node); // A chromosome from each
parent changes. Then the distance between the
new node and the sink is determined
The network is divided to optimal number of
independent clusters with the cluster heads.
d. Merge (2new populations);
e. Sort (node); // (distance to sink, energy)
The proposed method uses the genetic algorithm
for clustering and performs the routing based on
the fuzzy selection, which is addressed to detect
the attacker nodes routing.
Also sink is considered as a reliable element,
which creates the required secure connection
between different nodes. The nearest nodes to the
sink make the most reliable connections.
Different sensor nodes communicate with each
other by sending and receiving messages and the
sink is responsible for the node authentication.
The attack detection GA contains monitoring
nodes that control the network and determine any
conflict with network criteria (communication cost
and battery energy) which increases the reliability
of the network.
The cluster head or any of the cluster nodes can
act as the monitoring node. This node receives the
information about the other nodes and after
comparing them to the previous information from
the initial configuration of the network; it detects
the attacker and transmits the information to the
sink.
4 ALGORITHM
1. Start
2.node= Distribute (round (200))
3. Read Fuzzy function
f. size( new-population)=size(population)
g. Sort (new population); // the second time
(distance, energy)
h. Creating cluster head; // Identifying the
distance between clustering and membership
5. while( size(node)>=(sink_number +
cluster_number))
{
5.1[select1]=fuzzy_select(node);
5.2 node_find = find(select_find ==
// The selected route s node
is added to the selected nodes list.
5.3 If size (node_find)>1
Size-node--;
5.4 if (node==in_cluster)
D = distance from data;
Else
D = D1 + D2 + d_center;
//D1=distance node to ch1 D2=distance
chi to ch2, d_center = distance from
center
End
5.5 If (D < 1)
Size-node--; // The node is dead.
if size_node!= threshold
4.[center_ch] = GA; //GA start to select ch and
membership of ch
ISBN: 978-0-9891305-5-4 2014 SDIWC
[center_ch] = GA; //GA select ch
376
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
} end while
6. End
5- SIMULATION
The proposed method is simulated in MATLAB.
We consider an area of 100100. 200 nodes with
the initial energy of 1000 J are randomly
distributed in the network. The number of clusters
is considered 10. A 3D matrix is taken with the
first and the second dimensions involving
coordinates and the third dimension involving
energy. The sink is located at the point (0, 0) of the
plate.
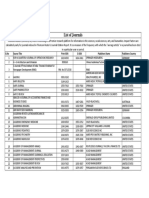
Figure2. End of network life time
5.1 Simulation Results
We define the values of genetic algorithm as:
Initial population=10, length of each chromosome
= number of Ch * 2=10, Crossover=0.7,
mutation=0.4, mutation rate=0.2. Every node acts
as a counter of hops to the sink.
First, MOGA performs clustering and routing on
the nodes in the area, and then the best optimal
route is chosen using fuzzy method. If a node dies,
it is omitted and a new clustering is done. GA
checks the nodes in the optimal route. Then it
detects and eliminates every node matching the
attack criteria. A new clustering is done at the
end.
In MOGA, two criterions for optimality are
considered, battery consumption and the best
route. Since the genetic algorithm chooses
multiple optimal routes, fuzzy method is proposed
to select the best route among them. In fuzzy
method, the route with the lowest density and the
shortest distance from the sink is chosen as the
response.
At higher densities, the nodes have also higher
energy consumption, and the routes through these
nodes consume more energy. In addition, the
nodes with a short distance to the sink have less
energy waste in forwarding the message and save
the energy of the network.
In multi-purpose genetic algorithm, two criterions
for optimality are considered, battery consumption
and the best route. Since the genetic algorithm
chooses multiple optimal routes, fuzzy method is
proposed to select the best route among them. In
fuzzy method, the route with the lowest density and
the shortest distance from the sink is chosen as the
response.
The network lifetime with the proposed method is
compared to the network lifetime with genetic
.This algorithm is examined
for over 200 numbers of nodes.
Figure1. WSN in 100*100
ISBN: 978-0-9891305-5-4 2014 SDIWC
377
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
We proposed a GA approach to raises the attack
detection schemes. We demonstrated that
clustering is a suitable method to reduce the
energy consumption of the network and
accordingly, the intrusion detection algorithm is
proposed. The obtained results are summarized as
follows:
1- Due to perceptible overhead of packet
transmission in the network, the nature of
clustering idea in integrating data and reducing
the network traffic is highly desired and
significant.
Figure3. The network lifetime with the proposed method
compared to the network lifetime with genetic algorithm.
In our proposed method, the whole sensor network
is not checked to detect the attacker node and only
the selected route is checked by fuzzy algorithm.
As a result, we just consider the selected nodes
instead of checking them all.
Different Cases considered are as follows:
Another node presents itself as the cluster head.
A message repeats constantly.
2- Considering that security and management
tasks are costly in cluster head nodes, there is no
need for other sensor nodes to keep this service
active during the clustering. It will help reducing
the average energy consumption of each node in
the network.
3-In our proposed method, the whole sensor
network is not checked to detect the attacker node
and only the selected route is checked by fuzzy
algorithm. As a result, we just consider the
selected nodes instead of checking them all.
Different Cases considered are as follows:
Another node presents itself as the cluster
head.
A message repeats constantly.
7- REFERENCES
[1] R. Khanna, H. Liu and H. H. Chen, Self-organization of
sensor networks using genetic algorithms, in Proc. IEEE
ICC, Istanbul, Jun. 2006.
[2] R.Khanna, H.Liu, and H-H. Chen Reduced Complexity
Intrusion Detection in Sensor, Networks Using Genetic
Algorithm , IEEE ICC 2009
[3] F. Liu, X. Cheng , Insider Attacker Detection in
Wireless Sensor Networks IEEE INFOCOM 2007.
Figure4. Detection of malicious with Fuzzy-GA
6 REASEARCH SUMMARIES
ISBN: 978-0-9891305-5-4 2014 SDIWC
[4] L.Guo, Q. Tang, An Improved Routing Protocol in WSN
with Hybrid Genetic Algorithm Second International
Conference on Networks Security Wireless Communications
and Trusted Computing (NSWCTC), Vol.: 2, pp. 289 292,
2010.
[5] K. Lee, H. Jeon, and D. Kim, Wormhole Detection
Method based on Location in Wireless Ad-Hoc Networks , in
378
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
New Technologies, Mobility
Netherlands, 2007, pp. 361-372.
and
Security:
Springer
[6] O.Younis, M.Krunz , Node Clustering in Wireless
Sensor Networks: Recent Developments and Deployment
Challenges, IEEE Network (special issue on wireless sensor
networking), vol. 20, issue 3, pp. 20-25, May 2006
[7] M.Ismail , M.Y Sanavullah, Security Topology in
Wireless Sensor Networks With Routing Optimisation ,
Authorized licensed use limited to: Korea Advanced Institute
of Science and Technology, IEEE Explore, August 26, 2009
ISBN: 978-0-9891305-5-4 2014 SDIWC
379
Proceedings of the International conference on Computing Technology and Information Management, Dubai, UAE, 2014
This document was created with Win2PDF available at http://www.daneprairie.com.
The unregistered version of Win2PDF is for evaluation or non-commercial use only.
ISBN: 978-0-9891305-5-4 2014 SDIWC
380
You might also like
- Solar Energy: A. Nazar Ali, K. Premkumar, M. Vishnupriya, B.V. Manikandan, T. ThamizhselvanDocument18 pagesSolar Energy: A. Nazar Ali, K. Premkumar, M. Vishnupriya, B.V. Manikandan, T. ThamizhselvanpremsonyNo ratings yet
- Solar Energy: SciencedirectDocument9 pagesSolar Energy: SciencedirectpremsonyNo ratings yet
- Solar Energy: Hassan FathabadiDocument8 pagesSolar Energy: Hassan FathabadipremsonyNo ratings yet
- Realization of An Asymmetric Switched-Capacitor Multilevel Inverter Using Nearest Level ControlDocument6 pagesRealization of An Asymmetric Switched-Capacitor Multilevel Inverter Using Nearest Level ControlpremsonyNo ratings yet
- Cylindrical multilayer cloaks reduce scatteringDocument10 pagesCylindrical multilayer cloaks reduce scatteringpremsonyNo ratings yet
- Environmental EthicsDocument12 pagesEnvironmental EthicspremsonyNo ratings yet
- A Grid-Connected Photovoltaic System: Mathematical Modeling Using MATLAB/SimulinkDocument7 pagesA Grid-Connected Photovoltaic System: Mathematical Modeling Using MATLAB/SimulinkpremsonyNo ratings yet
- Solar Energy: A B C A ADocument13 pagesSolar Energy: A B C A ApremsonyNo ratings yet
- Power and Voltage Control in A Grid-Connected Microgrid System With A Back-to-Back ConverterDocument6 pagesPower and Voltage Control in A Grid-Connected Microgrid System With A Back-to-Back ConverterpremsonyNo ratings yet
- Introduction: Biology and Conservation of The American White PelicanDocument10 pagesIntroduction: Biology and Conservation of The American White PelicanpremsonyNo ratings yet
- Journal of Sound and Vibration: Zhang Jun, Cheng Geng-Dong, Zhao Wen-Zhong, Zhao Guo-ZhongDocument11 pagesJournal of Sound and Vibration: Zhang Jun, Cheng Geng-Dong, Zhao Wen-Zhong, Zhao Guo-ZhongpremsonyNo ratings yet
- (Genetic Algorithm) Acoustic Scattering Reduction Using Layers of Elastic MaterialsDocument16 pages(Genetic Algorithm) Acoustic Scattering Reduction Using Layers of Elastic MaterialspremsonyNo ratings yet
- Journallist 1 PDFDocument400 pagesJournallist 1 PDFRajasekar PichaimuthuNo ratings yet
- Accepted Manuscript: Journal of Sound and VibrationDocument34 pagesAccepted Manuscript: Journal of Sound and VibrationpremsonyNo ratings yet
- Multinational Company&Computer EthicsDocument29 pagesMultinational Company&Computer EthicspremsonyNo ratings yet
- Design of Discrete PID Controller To Imp PDFDocument6 pagesDesign of Discrete PID Controller To Imp PDFpremsonyNo ratings yet
- 10 31 2013 Energy Cost Calculator Biogas ModelDocument5 pages10 31 2013 Energy Cost Calculator Biogas ModelpremsonyNo ratings yet
- Fuzzy Anti-Windup PID Controlled Induction MotorDocument6 pagesFuzzy Anti-Windup PID Controlled Induction MotorpremsonyNo ratings yet
- 10 31 2013 Energy Cost Calculator Biogas ModelDocument5 pages10 31 2013 Energy Cost Calculator Biogas ModelpremsonyNo ratings yet
- Reactive Power Compensation by Using V2G Technology: International Journal of Pure and Applied Mathematics No. 24 2018Document13 pagesReactive Power Compensation by Using V2G Technology: International Journal of Pure and Applied Mathematics No. 24 2018premsonyNo ratings yet
- Voltage Stability Enhancement of Wind Energy Conversion System Using SVPWM ControllerDocument13 pagesVoltage Stability Enhancement of Wind Energy Conversion System Using SVPWM ControllerpremsonyNo ratings yet
- UNIT I Embedded SystemsDocument60 pagesUNIT I Embedded SystemspremsonyNo ratings yet
- 367Document18 pages367premsonyNo ratings yet
- Simulation and Experimental Analysis of Hybrid DC-DC Converter For Electric Vehicle ApplicationsDocument10 pagesSimulation and Experimental Analysis of Hybrid DC-DC Converter For Electric Vehicle ApplicationspremsonyNo ratings yet
- S UIDo PDs A80 CDocument491 pagesS UIDo PDs A80 CpremsonyNo ratings yet
- Memory and I/O Interfacing: Demultiplexing Address/Data LinesDocument37 pagesMemory and I/O Interfacing: Demultiplexing Address/Data LinespremsonyNo ratings yet
- 371Document12 pages371premsonyNo ratings yet
- Alcohol Impaired Vehicle Tracking System Using Wearable Smart Helmet With Emergency AlertDocument9 pagesAlcohol Impaired Vehicle Tracking System Using Wearable Smart Helmet With Emergency AlertpremsonyNo ratings yet
- Tel Kom NikaDocument3 pagesTel Kom NikapremsonyNo ratings yet
- EE6603 Uw PDFDocument85 pagesEE6603 Uw PDFpremsonyNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5783)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (72)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- 130nm Techbrief01Document3 pages130nm Techbrief01Gilang Mardian KNo ratings yet
- Ultra-Deepwater Semi-Submersible: General Description Storage CapacitiesDocument2 pagesUltra-Deepwater Semi-Submersible: General Description Storage CapacitiesFrank CloseNo ratings yet
- Subject Link 8 - TGDocument73 pagesSubject Link 8 - TGPi PiNo ratings yet
- Sap StoDocument7 pagesSap StoPavilion67% (3)
- Leadership Styles - Types of Leadership Styles - BBA - MantraDocument5 pagesLeadership Styles - Types of Leadership Styles - BBA - Mantrakarthik sarangNo ratings yet
- (1X Erma First Fit 400) : Technical OfferDocument23 pages(1X Erma First Fit 400) : Technical OfferVikas Singh100% (1)
- Math8 Q1 Module8of8 SolvingRationalALgebraicEquationsIn2Variables v2Document24 pagesMath8 Q1 Module8of8 SolvingRationalALgebraicEquationsIn2Variables v2Jumar MonteroNo ratings yet
- CASE 2901: Inquiry: Under What Requirements May External Loads (Forces and Bending Moments) Be Evaluated ForDocument2 pagesCASE 2901: Inquiry: Under What Requirements May External Loads (Forces and Bending Moments) Be Evaluated ForDijin MaroliNo ratings yet
- Barangay Clearance2014Document68 pagesBarangay Clearance2014Barangay PangilNo ratings yet
- Electric Power Distribution - Wikipedia, The Free EncyclopediaDocument3 pagesElectric Power Distribution - Wikipedia, The Free EncyclopediasacuarsNo ratings yet
- Type AKP20 MICRO-Axial Piston Pumps: Up To 300 Bar 0,012 CM /revDocument6 pagesType AKP20 MICRO-Axial Piston Pumps: Up To 300 Bar 0,012 CM /revpeterNo ratings yet
- 8 State Based or Graph Based TestingDocument4 pages8 State Based or Graph Based TestingZINNIA MAZUMDER 19BIT0155No ratings yet
- WCO - Data Model PDFDocument25 pagesWCO - Data Model PDFCarlos Pires EstrelaNo ratings yet
- Classroom Management PlanDocument6 pagesClassroom Management Planapi-607580556No ratings yet
- University of Tripoli Faculty of Engineering Petroleum EngineeringDocument10 pagesUniversity of Tripoli Faculty of Engineering Petroleum EngineeringesraNo ratings yet
- Cat DP150 Forklift Service Manual 2 PDFDocument291 pagesCat DP150 Forklift Service Manual 2 PDFdiegoNo ratings yet
- Sustainable Urban Transport Index for Bhopal, IndiaDocument43 pagesSustainable Urban Transport Index for Bhopal, IndiaSayani MandalNo ratings yet
- 3 IE7591 Work System DesignDocument33 pages3 IE7591 Work System DesignMADANKISHORE KUMARNo ratings yet
- An Urgent Need To Modernize: Public Health Data Modernization InitiativeDocument2 pagesAn Urgent Need To Modernize: Public Health Data Modernization InitiativeRyza Jazid BaharNo ratings yet
- Drawing and Sketching Portraits: How To Draw Realistic Portraits For Beginners by Jacquelyn DescansoDocument3 pagesDrawing and Sketching Portraits: How To Draw Realistic Portraits For Beginners by Jacquelyn DescansoSent Mail0% (1)
- CPDocument29 pagesCPsandugandhiNo ratings yet
- Steps To Design A PCB Using OrcadDocument3 pagesSteps To Design A PCB Using OrcadkannanvivekananthaNo ratings yet
- Safety and Security Manual For Safety Manager SCDocument101 pagesSafety and Security Manual For Safety Manager SCk2tzgwmsc5No ratings yet
- Rt380T 230/400 PCB Rohs: Analog Three-Phase Thyristor Trigger ModuleDocument3 pagesRt380T 230/400 PCB Rohs: Analog Three-Phase Thyristor Trigger ModuleFelipe CasasNo ratings yet
- This Manual Includes: Repair Procedures Fault Codes Electrical and Hydraulic SchematicsDocument135 pagesThis Manual Includes: Repair Procedures Fault Codes Electrical and Hydraulic Schematicsrvalverde50gmailcomNo ratings yet
- Stranger PaperDocument3 pagesStranger Paperellie haNo ratings yet
- Rule 4 - Types of Construction (Book Format)Document2 pagesRule 4 - Types of Construction (Book Format)Thea AbelardoNo ratings yet
- Jurnal BE ValsartanDocument10 pagesJurnal BE ValsartanFutisya AlvitaNo ratings yet
- 2019 Orientation PresentationDocument45 pages2019 Orientation Presentationaee2 gm2100% (1)
- WTAC Study-NotesDocument9 pagesWTAC Study-NotesBillNo ratings yet