Professional Documents
Culture Documents
(IJCST-V7I2P23) :Dr.S. Sasikala Devi
Uploaded by
EighthSenseGroupOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
(IJCST-V7I2P23) :Dr.S. Sasikala Devi
Uploaded by
EighthSenseGroupCopyright:
Available Formats
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
RESEARCH ARTICLE OPEN ACCESS
Performance Evolution of Dynamic Replication in a Data
Grid Using FDDRA Algorithm
Dr.S. Sasikala Devi
Assistant Professor and Head,
Department of BCA, PPG College of Arts and Science, Coimbatore -35
Tamil Nadu - India
ABSTRACT
Data replication in data grids is an efficient technique that aims to improve response time, reduce the bandwidth
consumption and maintain reliability. In this context, a lot of work is done and many strategies have been
proposed. Unfortunately, most of existing replication techniques are based on single file granularity and neglect
correlation among different data files. Indeed, file correlations become an increasingly important consideration
for performance enhancement in data grids. In fact, the analysis of real data intensive grid applications reveals
that job requests for groups of correlated files and suggests that these correlations can be exploited for
improving the effectiveness of replication strategies. In this paper, propose a new dynamic data replication
strategy, called FDDRA (Fuzzy based dynamic replication algorithm), which consider a set of files as
granularity. Our strategy gathers files according to a relationship of simultaneous accesses between files by jobs
and stores correlated files at the same site. In order to find out these correlations data mining field is introduced.
Keywords:- Replication; data grid; file correlations; data mining;
I. INTRODUCTION of data mining field. Data mining techniques are
analytical tools that can be used to extract
Data grid is a distributed collection of storage meaningful knowledge from large data sets. Even
and computational resources that are not bounded though data mining (DM) has been applied in
within a geophysical location. It is now gaining numerous areas and sectors, the application of DM
much important interest in important areas such as to replication in data grids contexts is limited. In
high energy physics, bioinformatics, earth this respect, several works have used data mining
observations, global climate changes, image techniques to explore file correlations in data grids.
processing. One of the biggest challenges that data The main approaches to mining file correlations
grids face today is to improve the data management can be classified into two categories: access
since the techniques must scale up while addressing sequence mining and association rule mining.
the autonomy, dynamicity and heterogeneity of the Unfortunately, these two approaches are not
data sources. One way to effectively address the effective. On the other hand, various studies have
challenges for improving the data management is to shown the limits of association rule mining based
use replication techniques. Replication creates on the support and confidence approach and
multiple copies of the same file in several storage confirm that it results on an excessively large
resources to improve response time, load balancing, number of rules, with a majority of them either are
reduce the bandwidth consumption and maintain redundant or do not reflect the true correlation
reliability. In this context, many strategies have relationship among data. To overcome these
been proposed. However, most of existing drawbacks, propose to use frequent correlated
replication techniques are based on single file pattern mining to explore correlations between
granularity and neglect correlation among different files. The main idea is to replace the support
data files. Actually, in many applications, data files measure with a more expressive measure that better
may be correlated in terms of accesses and have to captures whether the items in a set are associated.
be considered together in order to reduce the access Correlated patterns mining was shown to be more
cost. By analysing a real data intensive grid complex and more informative than frequent
application, called Coadd, found that there is a patterns mining and association rules.
strong correlation between requested files and those
jobs tend to demand groups of correlated files. The
knowledge of correlation between data can be
extracted from historical data using the techniques
ISSN: 2347-8578 www.ijcstjournal.org Page 105
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
II. BACKGROUND AND RELATED on the file access history by all client nodes in the
WORKS grid over a period of time. The outputs of this
operation are correlated file sets related to the
In this section, classify and survey the access habits of users. At the second stage, a
replication strategies which take into account file replication is done on the basis of those sets, which
correlations. Propose to classify these strategies achieves the aim of pre-fetching and buffering data.
according to whether they are based on data mining The clustering method (bottom-up) adopted is used
techniques or not in finding file correlations. The to group all the files that are similar according to a
next subsection is dedicated to those strategies not given equivalence relation into equivalence classes.
based on DM techniques and the second is devoted The set of files in the same equivalence class are
to those using them. called correlative file sets. The experimental results
show that RSCA is effective and available.
A. Replication strategies not based on data mining Contrary to the other dynamic replication strategies
techniques used in the experiments, it has reduced not only the
average response time of client nodes, but also the
2) File reunion based data replication strategy bandwidth consumption.
(FIRE): FIRE is motivated by the observations that
a group of jobs in a site tend to demand a common 2) A pre-fetching based dynamic data replication
set of files distributed in a data grid. The main idea algorithm (PDDRA): PDDRA is based on an
of FIRE is to gather file sets through data assumption: members in a VO (Virtual
replication so that it resides with the job group on Organization) have similar interests in files. Based
the same site. Each site maintains a file access table on this assumption and also file access history,
to keep track of its local file access history. A site PDDRA predicts future needs of grid sites and pre-
makes independent decisions on whether or not fetches a sequence of files to the requester grid site,
deleting some old files to accommodate new files. so the next time that this site needs a file, it will be
On each site, this strategy analyses the site’s file locally available. PDDRA consists of three phases:
access table. If on a site FIRE detects that a storing file access patterns, requesting a file,
common set of files are frequently accessed by a performing replication, pre-fetching and
group of local jobs and a strong correlation exists replacement. The simulation results show that
between a group of local jobs and a set of PDDRA has better performance in comparison with
distributed files, FIRE will gather the set of files other algorithms in terms of job execution time,
onto a given site by replication. It is important to effective network usage, total number of
mention that the algorithm that computes file replications, hit ratio and percentage of storage
correlations is not addressed by the authors. filled.
Extensive experiments using OptorSim simulator
and synthetic benchmarks demonstrate that, 4) Predictive Hierarchical Fast spread (PHFS): By
compared with LRU and LFU, FIRE performs considering spatial locality, PHFS uses predictive
better in most scenarios. techniques to predict the future usage of files and
then pre replicates them in hierarchal manner on a
B. Replication strategies based on data mining path from source to client in order to increase
techniques locality in access. The correlation between files is
inferred from previous access patterns by
Data mining techniques, such as association rules and clustering techniques of data
association rules, frequent sequence mining, are mining. PHFS operates in three steps. In the first
used mainly to identify file correlations. This phase, a software agent in the root node collects the
section is limited to present replication strategies file access information from all the clients in the
with data mining approaches. system and puts them in a log file. In the second
phase, data mining techniques are applied on log
1) Replication strategy based on clustering analysis
files with the aim to find strongly related files that
(RSCA): The RSCA strategy is based on the
are accessed together. Finally, whenever a client
existence of correlations among the data files
requests a file, PHFS finds the predictive working
accessed according to the access history of users.
set (PWS) of that file. The PWS is composed by the
At the first stage, a clustering analysis is conducted
most related files to a requested file or in other
ISSN: 2347-8578 www.ijcstjournal.org Page 106
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
words the predicted subsequent requests after a correlated files. If the storage space is still in-
requested file. Then, PHFS replicates all members sufficient, files whose access number is less than a
of PWS along with the requested file on the path threshold will be deleted.
from the source to the client. Let us notice that in
this algorithm, the authors did not describe how to III. PROPOSED REPLICATION
mine the file correlations. However, they assumed STRATEGY
that correlations are found by data mining
techniques such as association rules and clustering Dynamic replication is an optimization method
without going into detail. In addition, they did not which targets to upsurge network bandwidth and
do experiments to compare the proposed algorithm convenience of data and decrease total access time
with other methods. They just used instances to by considering different issues. The above declared
compare the access latency with the Fast Spread issues have been talked in the suggested algorithm,
strategy. that is, FDDRA (Fuzzy based dynamic replication
algorithm) for replicating files.
5) Associated Replica Replacement Algorithm
based on Apriori approach (ARRA): ARRA is Model Creation. Data replication involves
introduced in two parts. In the first part, access choices like when to create a replica and how many
behaviours of data intensive jobs are analysed copies of a replica are mandatory. In FDDRA
based on the Apriori algorithm, which is a pioneer (Fuzzy based dynamic replication algorithm),
data mining algorithm. In the second part, replica replica is created if the file does not exist on the
replacement rules are generated and applied. node where the request has been programmed.
Accessed data files are considered as items in data
Model Obligation. After creating a replica, the
grid, while the required data files of each data
main objective is to decide where to place the
intensive job is regarded as each transaction. The
replica so as to get the fast access and less access
results of simulations which are performed on the
underdevelopment. The replica in FDDRA (Fuzzy
CMS grid show that ARRA has a relative
based dynamic replication algorithm) is placed on
advantage in mean job time of all jobs, number of
the basis of the reputation of the file and the
remote file access and effective network usage
available storage space on the node. The reputation
compared with LFU.
is based on the access frequency of the file on the
6) Based on support and confidence dynamic node.
replication algorithm in multi-tier data grid Model Assortment. After assignment, the next
(BSCA): The major idea of the algorithm is to pre- step is to select the best replica among the pool of
fetch frequently accessed files and their associated available replicas. The criterion for choosing the
files to the location near the access site. It finds out best replica in FDDRA (Fuzzy based dynamic
the correlation between the data files through data replication algorithm) is based on workload of the
access number and data access serial. It is based on node, availability status, available bandwidth, and
support, confidence and access numbers. BSCA has computing capacity of the node.
two sub algorithms: data mining algorithm and
replication algorithm. The data mining algorithm Loading Space. Before the placement of
applied to identify frequent files is FP Growth. replica, the amount of storage space should be
Moreover, support and confidence of association taken into account. If less storage space is
rules between these frequent files are computed. If available, then there should be some replacement
the support and the confidence values between files strategies involved in other algorithms. In FDDRA
exceed respective minimum thresholds, frequent (Fuzzy based dynamic replication algorithm), the
files and their associated ones are replicated. The storage space is calculated in and the file having
replication algorithm, which is applied in a less access frequency is replaced by the replica of
decentralized manner in each node, sorts the file the file which is being requested.
serially and finds out all files whose access
numbers are greater than a threshold. Then, the Suppleness. The data replication strategy must
algorithm constructs sets of related files and be adaptive to the dynamic nature of the grid in
replicate files that do not exist in nodes. If free order to provide better results. In FDDRA (Fuzzy
space is lacking, the algorithm deletes weakly based dynamic replication algorithm), if file is not
ISSN: 2347-8578 www.ijcstjournal.org Page 107
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
available at the time of execution of job, then Method:
replica of file is created so that grid can adapt
according to its dynamic nature. 1. If (needed replica is not in a site)
{
To demonstrate the role of units in grid Search replica within the
atmosphere and supposition has been made by region
considering the ordered structure of Internet setting 2. If (replica is within the region)
used these days. It is made of many wide and local Create list of candidate
area networks joined by joining devices and replica within the region
swapping places. The services of Internet Service Else
Providers (ISPs) are used by end users at different 3. {
levels. There are international service providers, Search replica in other region
national service providers, regional service 4. Create list of candidate replica on other
providers, and local service providers. At the top of region
the grading are the international ISPs to connect }
nations together [18]. Here, international ISPs are 5. }
considered as master node. The national ISPs are 6. Fetch the most availability replica in
maintained by some companies. In FDDRA (Fuzzy candidate replica list
based dynamic replication algorithm) algorithm, 7. If(there is sufficient space to store the
the national ISPs are similar to regions, and new replica)
companies can be considered as the head nodes {
which are responsible for the maintenance of the Store it;
region. Regional ISPs are small ISPs connected to Exit
one or more national ISPs Local ISPs provide 8. }
direct service to end users. The local ISPs can be 9. If(replica is in the same region)
connected to regional ISP or national ISP. Local {
ISP is entity that just provides internet services. Exit;// avoid duplication in the same
This is like the node in data grid where the file or region
the replica of the file is placed which is being }
requested by the user. 10. End process
IV. DESCRIPTION OF DMDR TESTED AND EBHR IMPLEMENTING
USING MATLAB:
ALGORITHM
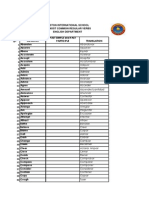
Table 1: job execution scenarios
Job execution values
The proposed FDDRA (Fuzzy based
scenarios
dynamic replication algorithm) also based on the
No of jobs 100,200,300,400,500
network level locality. The enhanced algorithm
No of job types 10
tried to replicate files from the neighbouring region
Size of single file 1G
and store replica in a site where the files has been
Scheduling Random
accessed frequently based on the assumption that it
algorithm
may require in the future.
Choice of execution Random Zip
FDDRA Region based algorithm patterns
No of file accessed 10
Inputs: Grid Topology, Bandwidth, Data and per job
Storage Space
Table 2: performance metrics
Output: Find best candidate for replication, Load
performance metrics Description
balancing, job execution time, No of replications,
Mean job execution time Time to execute the job
LFA (local file access), RFA (remote file access),
+ waiting time/number
Network usage, Network utilization, Creation of
of jobs completed
new replica.
Effective network usage Specifies the network
ISSN: 2347-8578 www.ijcstjournal.org Page 108
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
utilization Figure 1: Comparison of Mean Job Execution Time with
existing algorithm
Storage used(MB) Specifies spaces used
by files
b. NUMBER OF REPLICATIONS
The no of replications is calculated as time to
execute a file, the time spent by a job in waiting
queue divided by the number of jobs completed. It
V. RESULTS
can be represented as where is the number of jobs
The efficiency of is calculated based processed by the system, is the time to execute the
Performance Metrics, that is, characteristic path job, and is the waiting time of the job that has been
length, neighbourhood connectivity and shortest spent in the queue.The FDDRA (Fuzzy based
path. FDDRA (FDDRA (Fuzzy based dynamic dynamic replication algorithm) along with BHR,
replication algorithm)) is compared with one other FIRE, PHFS and PDDRA was tested using
dynamic replication strategy, that is, FDDRA. On different job numbers of jobs.The job execution
the MATLAB using the abovementioned time for Random Zipf Access Pattern Generator is
Performance Metrics. At the time of simulation in shown in Figure 2.
FDDRA, there exists only one replica in a region
based on the popularity of the file.
a. MJET
The Mean Job Execution Time is calculated as
time to execute a file, the time spent by a job in
waiting queue divided by the number of jobs
completed. It can be represented as where is the
number of jobs processed by the system, is the time
to execute the job, and is the waiting time of the job
that has been spent in the queue.The FDDRA
(Fuzzy based dynamic replication algorithm) along
with BHR, FIRE, PHFS and PDDRA was tested
using different job numbers of jobs. The job
execution time for Random Zipf Access Pattern
Generator is shown in Figure 1.
Figure 2: Comparison of characteristic path length with existing
algorithm
c. EFFECTIVE NETWORK USAGE
The effective network usage is calculated as
time to execute a file, the time spent by a job in
waiting queue divided by the number of jobs
completed. It can be represented as where is the
number of jobs processed by the system, is the time
to execute the job, and is the waiting time of the job
that has been spent in the queue.The FDDRA
(Fuzzy based dynamic replication algorithm) along
with BHR, FIRE, PHFS and PDDRA was tested
using different job numbers of jobs. The job
ISSN: 2347-8578 www.ijcstjournal.org Page 109
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
execution time for Random Zipf Access Pattern [3] William H. Bell, David G. Cameron, Ruben
Generator is shown in Figure 3. Carvajal-Schiaffino, A. Paul Millar, Kurt
Stockinger, and Floriano Zini.: Evaluation of
an Economy-Based File Replication Strategy
for a Data Grid. In International Workshop on
Agent based Cluster and Grid Computing at
CCGrid 2003, Tokyo, Japan, May 2003.
IEEE Computer Society Press.
[4] Mark Carman, Floriano Zini, Luciano Serafini,
and Kurt Stockinger.: Towards an Economy-
Based Optimisation of File Access and
Replication on a Data Grid. In International
Workshop on Agent based Cluster and Grid
Computing at International Symposium on
Cluster Computing and the Grid
(CCGrid'2002), Berlin, Germany, May 2002.
IEEE Computer Society Press.
[5] M. Tang, B.S. Lee, C.K. Yeo, X. Tang,
Dynamic replication algorithms for the multi-
tier data grid, Future Generation Computer
Figure 3: Effective network usagewith existing algorithm
Systems 21 (5) (2005), pp. 775– 790.
VI. CONCLUSION [6] Y. Yuan, Y. Wu, G. Yang, F. Yu, Dynamic
In this paper, presented a FDDRA(Fuzzy data replication based on local optimization
based dynamic replication algorithm)for data grids. principle in data grid, (2007).
Our strategy takes into account correlations
[7] A. Abdullah, M. Othman, H. Ibrahim, M.N.
between files and considers groups of correlated
Sulaiman, A.T. Othman, Decentralized
files as granularity for replication. Indeed,
replication strategies for P2P based scientific
considering correlated files for replication improves
data grid, in: Information Technology, ITSim,
significantly performance evaluation metrics
International Symposium on, (2008), pp. 1–
ofreplication strategies, including characteristic
8.
path length, neighbourhood connectivity and
shortest path. Compared with other algorithms that [8] Y. Ding, Y. Lu, Automatic data placement and
are BHR, FIRE, PHFS and PDDRA. The replication in grids, in: High Performance
experimental result shows that FDDRA (Fuzzy Computing, HiPC, International Conference
based dynamic replication algorithm) gives better on, (2009), pp. 30– 39.
performance than other two algorithms. As a part
of our future work, we plan to deploy our [9] Neeraj Nehra, R.B.Patel, V.K.Bhat, Distributed
replication strategy in a real grid environment. Parallel Resource Co-Allocation with Load
Balancing in Grid Computing, IJCSNS
REFERENCES International Journal of Computer Science
and Network Security, January (2007), pp.
[1] I. Foster, C. Kesselman and S. Tuecke. 2001. 282-291.
The Anatomy of the Grid: Enabling Scalable
Virtual Organizations, IJSA. [10] A. Horri, R. Sepahvand, Gh. Dastghaibyfard,
A Hierarchical Scheduling and Replication
[2] Kavitha Ranganathan and Ian Foster.: Strategy, IJCSNS International Journal of
Identifying Dynamic Replication Strategies Computer Science and Network 30 Security,
for a High Performance Data Grid. August (2008), pp. 30-35.
International Workshop on Grid Computing,
Denver, November 2001.
ISSN: 2347-8578 www.ijcstjournal.org Page 110
International Journal of Computer Science Trends and Technology (IJCST) – Volume 7 Issue 2, Mar - Apr 2019
[11] S. M. Park, J. H. Kim, Y. B. Ko, W. S. Yoon,
“Dynamic Data Replication Strategy Based
on Internet Hierarchy BHR”, in: Lecture
notes in Computer Science Publisher, 2004,
pp. 838-846.
[12] K. Sashi, A.S. Thanamani, Dynamic
replication in a data grid using a modified
BHR region based algorithm, Future
Generation Computer Systems 27 (2), (2011),
pp. 202–210.
[13] Q. Rasool, J. Li, S. Zhang, Replica placement
in multi-tier data grid, in: 2009 Eighth IEEE
International Conference on Dependable,
Autonomic and Secure Computing, (2009),
pp. 103–108.
[14] Y.F. Lin, J.J. Wu, P. Liu, A list-based strategy
for optimal replica placement in data grid
systems, in: 37th International Conference on
Parallel Processing, (2008), pp. 198–205.
[15] D. G. Cameron, R. C. Schiaffino, J. Ferguson
et al., “OptorSim v2.0 installation and user
guide,”2004,http://read.pudn.com/downloads
74/doc/fileformat/270400/Optorsim%20v2.0
%20Installation%20and%20User%20Guide.p
df.
[16] S.-M. Park, J.-H. Kim, Y.-B. Ko, and W.-S.
Yoon, “Dynamic data grid replication
strategy based on Internet hierarchy,” in Grid
and Cooperative Computing, vol. 3033
of Lecture Notes in Computer Science, pp.
838–846, Springer, Berlin, Germany, 2004.
[17] B. A. Forouzan, TCP/IP Protocol Suite, Tata
McGRAW-Hill, Noida, India, 3rd edition,
2006.
[18]The European Data Grid
Project, http://www.gridpp.ac.uk/papers/chep
04_optorsim.pdf.
[19] D. G. Cameron, R. C. Schiaffino, J. Ferguson
et al., “OptorSim v2.0 installation and user
guide,”.
ISSN: 2347-8578 www.ijcstjournal.org Page 111
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- (IJCST-V12I1P7) :tejinder Kaur, Jimmy SinglaDocument26 pages(IJCST-V12I1P7) :tejinder Kaur, Jimmy SinglaEighthSenseGroupNo ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- (IJCST-V12I1P4) :M. Sharmila, Dr. M. NatarajanDocument9 pages(IJCST-V12I1P4) :M. Sharmila, Dr. M. NatarajanEighthSenseGroupNo ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- (IJCST-V11I4P15) :M. I. Elalami, A. E. Amin, S. A. ElsaghierDocument8 pages(IJCST-V11I4P15) :M. I. Elalami, A. E. Amin, S. A. ElsaghierEighthSenseGroupNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- (IJCST-V11I4P5) :P Jayachandran, P.M Kavitha, Aravind R, S Hari, PR NithishwaranDocument4 pages(IJCST-V11I4P5) :P Jayachandran, P.M Kavitha, Aravind R, S Hari, PR NithishwaranEighthSenseGroupNo ratings yet
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- (IJCST-V11I6P8) :subhadip KumarDocument7 pages(IJCST-V11I6P8) :subhadip KumarEighthSenseGroupNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- (IJCST-V11I3P25) :pooja Patil, Swati J. PatelDocument5 pages(IJCST-V11I3P25) :pooja Patil, Swati J. PatelEighthSenseGroupNo ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- (IJCST-V11I6P5) :A.E.E. El-Alfi, M. E. A. Awad, F. A. A. KhalilDocument9 pages(IJCST-V11I6P5) :A.E.E. El-Alfi, M. E. A. Awad, F. A. A. KhalilEighthSenseGroupNo ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- (IJCST-V12I1P2) :DR .Elham Hamed HASSAN, Eng - Rahaf Mohamad WANNOUSDocument11 pages(IJCST-V12I1P2) :DR .Elham Hamed HASSAN, Eng - Rahaf Mohamad WANNOUSEighthSenseGroupNo ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- (IJCST-V11I6P8) :subhadip KumarDocument7 pages(IJCST-V11I6P8) :subhadip KumarEighthSenseGroupNo ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- (IJCST-V11I5P4) :abhirenjini K A, Candiz Rozario, Kripa Treasa, Juvariya Yoosuf, Vidya HariDocument7 pages(IJCST-V11I5P4) :abhirenjini K A, Candiz Rozario, Kripa Treasa, Juvariya Yoosuf, Vidya HariEighthSenseGroupNo ratings yet
- (IJCST-V11I4P9) :KiranbenV - Patel, Megha R. Dave, Dr. Harshadkumar P. PatelDocument18 pages(IJCST-V11I4P9) :KiranbenV - Patel, Megha R. Dave, Dr. Harshadkumar P. PatelEighthSenseGroupNo ratings yet
- (IJCST-V11I4P12) :N. Kalyani, G. Pradeep Reddy, K. SandhyaDocument16 pages(IJCST-V11I4P12) :N. Kalyani, G. Pradeep Reddy, K. SandhyaEighthSenseGroupNo ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- (Ijcst-V11i4p1) :fidaa Zayna, Waddah HatemDocument8 pages(Ijcst-V11i4p1) :fidaa Zayna, Waddah HatemEighthSenseGroupNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- (IJCST-V11I4P3) :tankou Tsomo Maurice Eddy, Bell Bitjoka Georges, Ngohe Ekam Paul SalomonDocument9 pages(IJCST-V11I4P3) :tankou Tsomo Maurice Eddy, Bell Bitjoka Georges, Ngohe Ekam Paul SalomonEighthSenseGroupNo ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- (IJCST-V11I3P20) :helmi Mulyadi, Fajar MasyaDocument8 pages(IJCST-V11I3P20) :helmi Mulyadi, Fajar MasyaEighthSenseGroupNo ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- (IJCST-V11I3P21) :ms. Deepali Bhimrao Chavan, Prof. Suraj Shivaji RedekarDocument4 pages(IJCST-V11I3P21) :ms. Deepali Bhimrao Chavan, Prof. Suraj Shivaji RedekarEighthSenseGroupNo ratings yet
- (IJCST-V11I3P17) :yash Vishwakarma, Akhilesh A. WaooDocument8 pages(IJCST-V11I3P17) :yash Vishwakarma, Akhilesh A. WaooEighthSenseGroupNo ratings yet
- (IJCST-V11I3P24) :R.Senthilkumar, Dr. R. SankarasubramanianDocument7 pages(IJCST-V11I3P24) :R.Senthilkumar, Dr. R. SankarasubramanianEighthSenseGroupNo ratings yet
- (IJCST-V11I3P13) : Binele Abana Alphonse, Abou Loume Gautier, Djimeli Dtiabou Berline, Bavoua Kenfack Patrick Dany, Tonye EmmanuelDocument31 pages(IJCST-V11I3P13) : Binele Abana Alphonse, Abou Loume Gautier, Djimeli Dtiabou Berline, Bavoua Kenfack Patrick Dany, Tonye EmmanuelEighthSenseGroupNo ratings yet
- (IJCST-V11I3P12) :prabhjot Kaur, Rupinder Singh, Rachhpal SinghDocument6 pages(IJCST-V11I3P12) :prabhjot Kaur, Rupinder Singh, Rachhpal SinghEighthSenseGroupNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- (IJCST-V11I3P7) :nikhil K. Pawanikar, R. SrivaramangaiDocument15 pages(IJCST-V11I3P7) :nikhil K. Pawanikar, R. SrivaramangaiEighthSenseGroupNo ratings yet
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- (IJCST-V11I3P11) :Kalaiselvi.P, Vasanth.G, Aravinth.P, Elamugilan.A, Prasanth.SDocument4 pages(IJCST-V11I3P11) :Kalaiselvi.P, Vasanth.G, Aravinth.P, Elamugilan.A, Prasanth.SEighthSenseGroupNo ratings yet
- (IJCST-V11I3P2) :K.Vivek, P.Kashi Naga Jyothi, G.Venkatakiran, SK - ShaheedDocument4 pages(IJCST-V11I3P2) :K.Vivek, P.Kashi Naga Jyothi, G.Venkatakiran, SK - ShaheedEighthSenseGroupNo ratings yet
- (IJCST-V11I3P9) :raghu Ram Chowdary VelevelaDocument6 pages(IJCST-V11I3P9) :raghu Ram Chowdary VelevelaEighthSenseGroupNo ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- (IJCST-V11I3P5) :P Adhi Lakshmi, M Tharak Ram, CH Sai Teja, M Vamsi Krishna, S Pavan MalyadriDocument4 pages(IJCST-V11I3P5) :P Adhi Lakshmi, M Tharak Ram, CH Sai Teja, M Vamsi Krishna, S Pavan MalyadriEighthSenseGroupNo ratings yet
- (IJCST-V11I2P18) :hanadi Yahya DarwishoDocument32 pages(IJCST-V11I2P18) :hanadi Yahya DarwishoEighthSenseGroupNo ratings yet
- (IJCST-V11I3P8) :pooja Patil, Swati J. PatelDocument5 pages(IJCST-V11I3P8) :pooja Patil, Swati J. PatelEighthSenseGroupNo ratings yet
- (IJCST-V11I3P4) :V Ramya, A Sai Deepika, K Rupa, M Leela Krishna, I Satya GirishDocument4 pages(IJCST-V11I3P4) :V Ramya, A Sai Deepika, K Rupa, M Leela Krishna, I Satya GirishEighthSenseGroupNo ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- (IJCST-V11I3P1) :Dr.P.Bhaskar Naidu, P.Mary Harika, J.Pavani, B.Divyadhatri, J.ChandanaDocument4 pages(IJCST-V11I3P1) :Dr.P.Bhaskar Naidu, P.Mary Harika, J.Pavani, B.Divyadhatri, J.ChandanaEighthSenseGroupNo ratings yet
- (IJCST-V11I2P19) :nikhil K. Pawanika, R. SrivaramangaiDocument15 pages(IJCST-V11I2P19) :nikhil K. Pawanika, R. SrivaramangaiEighthSenseGroupNo ratings yet
- The Power of Compounding: Why It's the 8th Wonder of the WorldDocument5 pagesThe Power of Compounding: Why It's the 8th Wonder of the WorldWaleed TariqNo ratings yet
- E.Coli Coliforms Chromogenic Medium: CAT Nº: 1340Document2 pagesE.Coli Coliforms Chromogenic Medium: CAT Nº: 1340Juan Manuel Ramos ReyesNo ratings yet
- Minotaur Transformation by LionWarrior (Script)Document7 pagesMinotaur Transformation by LionWarrior (Script)Arnt van HeldenNo ratings yet
- Swot AnalysisDocument6 pagesSwot AnalysisSneha SinhaNo ratings yet
- PSE Inc. V CA G.R. No. 125469, Oct 27, 1997Document7 pagesPSE Inc. V CA G.R. No. 125469, Oct 27, 1997mae ann rodolfoNo ratings yet
- Managment Information Question BankDocument302 pagesManagment Information Question BankLuca Papasizza100% (2)
- Toe Movement - v22 Print FormatDocument10 pagesToe Movement - v22 Print FormatbensonNo ratings yet
- U1 Presantation-MAK 032021Document15 pagesU1 Presantation-MAK 032021MD ANAYET ALI KHANNo ratings yet
- PAPC - Internal Notes PDFDocument4 pagesPAPC - Internal Notes PDFHrushi Km GowdaNo ratings yet
- Initial Data Base (Narrative)Document11 pagesInitial Data Base (Narrative)LEBADISOS KATE PRINCESSNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- 5.1 Physical Farming Constraints in Southern CaliforniaDocument1 page5.1 Physical Farming Constraints in Southern CaliforniaTom ChiuNo ratings yet
- Safe Handling of Solid Ammonium Nitrate: Recommendations For The Environmental Management of Commercial ExplosivesDocument48 pagesSafe Handling of Solid Ammonium Nitrate: Recommendations For The Environmental Management of Commercial ExplosivesCuesta AndresNo ratings yet
- The Ten Commandments For Network MarketersDocument3 pagesThe Ten Commandments For Network MarketersJustin Lloyd Narciso PachecoNo ratings yet
- 2009 WORD White Paper TemplateDocument4 pages2009 WORD White Paper Templateomegalpha777No ratings yet
- ESS 4104 AssignmentDocument9 pagesESS 4104 AssignmentSamlall RabindranauthNo ratings yet
- School Communication Flow ChartsDocument7 pagesSchool Communication Flow ChartsSarah Jane Lagura ReleNo ratings yet
- 20 Reasons Composers Fail 2019 Reprint PDFDocument30 pages20 Reasons Composers Fail 2019 Reprint PDFAlejandroNo ratings yet
- Standard Chartered BackgroundDocument6 pagesStandard Chartered BackgroundAwesum Allen MukiNo ratings yet
- GUCR Elections Information 2017-2018Document10 pagesGUCR Elections Information 2017-2018Alexandra WilliamsNo ratings yet
- All Over AgainDocument583 pagesAll Over AgainJamie Kris MendozaNo ratings yet
- 150 Most Common Regular VerbsDocument4 pages150 Most Common Regular VerbsyairherreraNo ratings yet
- Criminal Evidence Course OutlineDocument3 pagesCriminal Evidence Course OutlineChivas Gocela Dulguime100% (1)
- AMA Manual 10th Edition PDFDocument1,014 pagesAMA Manual 10th Edition PDFKannan Fangs S100% (2)
- Bluetooth Modules - Martyn Currey PDFDocument64 pagesBluetooth Modules - Martyn Currey PDFAng Tze Wern100% (1)
- Chinnamasta Sadhana PDFDocument1 pageChinnamasta Sadhana PDFSayan Majumdar100% (2)
- EDU101 Solution FileDocument2 pagesEDU101 Solution FileTahaNo ratings yet
- Preterite vs Imperfect in SpanishDocument16 pagesPreterite vs Imperfect in SpanishOsa NilefunNo ratings yet
- Service Manual Pioneer CDJ 2000-2 (RRV4163) (2010)Document28 pagesService Manual Pioneer CDJ 2000-2 (RRV4163) (2010)GiancaNo ratings yet
- Court Rules on Debt Collection Case and Abuse of Rights ClaimDocument3 pagesCourt Rules on Debt Collection Case and Abuse of Rights ClaimCesar CoNo ratings yet
- 2006 - Bykovskii - JPP22 (6) Continuous Spin DetonationsDocument13 pages2006 - Bykovskii - JPP22 (6) Continuous Spin DetonationsLiwei zhangNo ratings yet
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityFrom EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityRating: 5 out of 5 stars5/5 (1)
- Python for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldFrom EverandPython for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldNo ratings yet
- Ultimate Guide to LinkedIn for Business: Access more than 500 million people in 10 minutesFrom EverandUltimate Guide to LinkedIn for Business: Access more than 500 million people in 10 minutesRating: 5 out of 5 stars5/5 (5)
- So You Want to Start a Podcast: Finding Your Voice, Telling Your Story, and Building a Community that Will ListenFrom EverandSo You Want to Start a Podcast: Finding Your Voice, Telling Your Story, and Building a Community that Will ListenRating: 4.5 out of 5 stars4.5/5 (35)