Professional Documents
Culture Documents
Async Multistep Policy Datapower
Uploaded by
Chinna VadyalamOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Async Multistep Policy Datapower
Uploaded by
Chinna VadyalamCopyright:
Available Formats
IBM Software Group
DataPower Release 3.6.1 New Features
Ren JIngAn Cheng Long
IBM Corporation
IBM Software Group | WebSphere software / DataPower
IBM WebSphere DataPower SOA Appliances
Software
An SOA Appliance
Creating customer value through extreme SOA performance and security
Simplifies SOA with specialized devices Accelerates SOA with faster XML throughput Helps secure SOA XML implementations
Skills & Support
WebSphere DataPower SOA Appliances redefine the boundaries of middleware extending the SOA Foundation with specialized, consumable, dedicated SOA appliances that combine superior performance and hardened security for SOA implementations.
IBM Software Group | WebSphere software / DataPower
Why an Appliance for SOA
Hardened, specialized hardware for helping to integrate, secure & accelerate SOA Many functions integrated into a single device:
Impact: connectivity will require service level management, routing, policy, transformation
Higher levels of security assurance certifications require hardware:
Example: government FIPS Level 3 HSM, Common Criteria
Higher performance with hardware acceleration:
Impact: ability to perform more security checks without slow downs
Addresses the divergent needs of different groups:
Example: enterprise architects, network operations, security operations, identity management, web services developers
Simplified deployment and ongoing management:
Impact: reduces need for in-house SOA skills & accelerates time to SOA benefits
IBM Software Group | WebSphere software
IBM SOA Appliance Product Line
Specialized network devices simplify, help secure & accelerate SOA
XML Accelerator XA35
Accelerates XML processing and transformation Increases throughput and reduces latency Lowers development costs
XML Security Gateway XS40
Help secure SOA with XML threat protection and access control Combines Web services security, routing and management functions Drop-in, centralized policy enforcement Easily integrates with exiting infrastructure and processes Transforms messages (Binary to XML, Binary to Binary, XML to Binary) Bridges multiple protocols (e.g. MQ, HTTP, JMS) Routes messages based on content and policy Integrates message-level security and policy functions
Integration Appliance XI50
IBM Internal Use Only
IBM Software Group | WebSphere software / DataPower
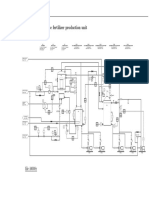
IBM SOA Appliance Deployment Summary
Web Tier
XML HTML WML
Client
XML XSL
Client or Server
XA35 Internet Application Server Web Server
Security
`
Internet IP Firewall
Tivoli Access Manager -----------Federated Identity Manager
XS40 Application Server
Integration & Management Tiers
R EP LY Q
LEGACY REQ
HTTP XML REQ HTTP XML RESPONSE XI50
ITCAM for SOA
LEGACY RESP
Web Services Client
IBM Software Group | WebSphere software / DataPower
DataPower 3.6.1 Feature Summary Multistep v3 processing features Configurable QoS SOAP 1.2 enhancements
Development Services Business Services Management Services Interaction Services Process Services Information Services
Reliable Messaging WS-Policy WS-I Profile enhancements DB2 v9 and IMS Connect Many more
Enterprise Service Bus
Partner Services Business App Services Infrastructure Services Access Services
Apps & Info Assets
IBM Software Group | WebSphere software / DataPower
MultiStep v3
New Processing Flow Features: Conditional action execution if then else If XPath = true then execute named Processing Action For-Each Loop: For each node in nodeset execute named Processing Action For each increment of counter execute named Processing Action
Parallel Processing Features: Mark any Processing Action Asynchronous Synchronize parallel asynchronous action execution to rule processing Target multiple Results destinations in parallel
IBM Software Group | WebSphere software / DataPower
MultiStep v3
Asynchronous Action Causes action to execute async to the rest of MultiStep. MultStep moves immediately to the next action in the rule without waiting for an async action to complete. Particularly good for fire/forget. Can reduce network I/O latency by executing multiple Actions in parallel. Must use Event-sink action to resync to rule. Beware the race condition!
Nearly any action can be marked Asynchronous!
IBM Software Group | WebSphere software / DataPower
MultiStep v3
Event-sink Action Causes MultiStep to wait for designated async actions to complete. Output contexts of included async actions become reliably available to other MultiStep actions. Limit wait time with Timeout value.
IBM Software Group | WebSphere software / DataPower
MultiStep v3
MultiWay Results New properties added to Results action allows for parallel execution of Results action with multiple destinations. User can control multiple destination behavior with Multi-Way Results input. May use Multiple Outputs feature to capture response from each destination in separate Output context. Creates contexts Outputname1,Outputname2, Outputname3, etc. Can mark entire action Asynchronous.
var://context/mine/dests: <url>http://host.domain.com/spp1</url> <url>http://host.domain.com/spp2</url> <url>http://host.domain.com/spp3</url>
IBM Software Group | WebSphere software / DataPower
Quality of Service
Service Priority Control the service scheduling priority. When system resources are in high demand, "high" priority services will be favored over lower priority services.
Look on the Advanced Settings page of the Service to set this.
Use the Priority twizzle on a Web Service Proxy Policy page to set this.
IBM Software Group | WebSphere software / DataPower
SOAP 1.2
Support includes, but is not limited to: Importing WSDLs with SOAP 1.2 bindings SOAP 1.2 envelope validation SOAP 1.2 message validation Co-existence of SOAP 1.1/1.2 service definitions Ability to convert between SOAP 1.1 and 1.2 requests
Configure WS-Proxy from WSDL with SOAP 1.2 (both document and rpc) Must support: SOAP Request-Response Message Exchange Pattern SOAP Response Message Exchange Pattern (support for HTTP GET binding) SOAP Web Method Feature SOAP Action Feature Configure a WS-Proxy from a WSDL with both SOAP 1.1 and 1.2 bindings SOAP 1.1 messages would be routed to the 1.1 endpoint and SOAP 1.2 messages to the 1.2 endpoint
IBM Software Group | WebSphere software / DataPower
SOAP 1.2
Mediation between SOAP 1.1 and 1.2 requests/responses (WS-Proxy) Scenario: Expose a SOAP 1.1 or 1.2 service and allow both SOAP 1.1 and 1.2 clients An "Additional bindings" GUI option will the administrator to direct the WS-Proxy to allow additional bindings, beyond what is specified in the WSDL. The option is additive, and specifying a binding already in the WSDL is harmless. Incoming requests will be processed using any of the allowed bindings, converted as necessary to what the WSDL specifies the server uses, and outgoing responses are similarly "back-converted" as necessary.
IBM Software Group | WebSphere software / DataPower
Reliable Messaging
WS-ReliableMessaging specification describes a protocol that allows messages to be transferred reliably between nodes implementing this protocol in the presence of software component, system, or network failures. The protocol is described in a transport-independent manner allowing it to be implemented using different network technologies. To support interoperable Web services, a SOAP binding is defined within its specification. The protocol depends upon other Web services specifications for the identification of service endpoint addresses and policies (notably WSAddressing).
IBM Software Group | WebSphere software / DataPower
Reliable Messaging
Supported Requirements RM Destination (MPGW front side): message acknowledgement, duplicate and "out-of-sequence" message detection. It also should be able to act as RM Source to deliver response messages as WS-RM Sequence RM Source (MPGW backend, "Results" action, "dp:soap-call" extension function): Sequence management (create, close, terminate), injecting RM headers in the outcoming SOAP message, ability to retransmit lost messages, Endpoint to receive Acknowledgement messages.
Non-Requirements No multibox WS-RM
IBM Software Group | WebSphere software / DataPower
Reliable Messaging
Users can enable Reliable Messaging through: WS-RM Policy Assertion embedded in the WSDL underlying a WS-Proxy. Enabling WS-RM through the GUI (shown at right). Options on ReliableMessaging tab control Global, Destination and Source behaviors. Reliable Messaging dependent on WS-Addressing mode for some configurations and for interoperability with some implementations (notably WebSphere).
Extensive Online Help on this page!
IBM Software Group | WebSphere software / DataPower
WS-Policy/WS-Security Policy
WS-Policy is a specification that defines metadata to enable interoperability between web service consumers and web service providers. The WS-Policy specifications enable organizations to automate their service governance models creating a concrete instance of web service governance. New Features: Parse WSDL with policy elements already included in the WSDL and recognize standardized policy domains [i.e. WS-SecurityPolicy, WSReliableMessaging Policy] Retrieve WSDLs from registries: WSRR or UDDI Includes customizable policy templates (e.g. UsernameSignEncrypt) Ability to attach policies to subjects not embedded in the WSDL
IBM Software Group | WebSphere software / DataPower
WS-Policy/WS-Security Policy
Configuration of WS-Policy begins with the WSDL. Once loaded into a Web Service Proxy, additional configuration actions become available through the Policy tab (shown below).
IBM Software Group | WebSphere software / DataPower
WS-Policy/WS-Security Policy
The interface affords the user methods for creating policy attachments, as well as enabling Policy Subjects.
IBM Software Group | WebSphere software / DataPower
Enhanced OASIS and WS-I Profile Support
SOAP with Attachments Profile 1.0/1.1 WS-I Attachments Profile 1.0 WS-I Basic Profile 1.1 WS-I Basic Security Profile 1.0
IBM Software Group | WebSphere software / DataPower
SOAP with Attachments Profile 1.0/1.1
The "encrypt" verb will provide options to: - WS-Sec encrypt SOAP Body only - WS-Sec encrypt the attachments of SwA message only - WS-Sec encrypt both SOAP Body and the attachments of SwA message When the attachments are encrypted the SwA Profile version is configurable. The result of the "encrypt" action for SwA Profile 1.1 [2] will conform to BSP10 [12]. The "decrypt" verb for both entire message/doc decryption and field-level decryption automatically decrypts the data in conformance with both WS-Sec and the SwA Profiles (1.0 [1], 1.1 [2]).
IBM Software Group | WebSphere software / DataPower
SOAP with Attachments Profile 1.0/1.1
The "sign" and "verify" actions will be enhanced to support all of the transformations identified in SwA Profile 1.0 [1] and 1.1 [2]. The "sign" verb will provide options to: - WS-Sec sign SOAP Body only - WS-Sec sign the attachments of SwA message only - WS-Sec sign both SOAP Body and the attachments of SwA message When the attachments are signed the SwA Profile version is configurable. The result of the "sign" action for SwA Profile 1.1 [2] will conform to BSP10 [12].
IBM Software Group | WebSphere software / DataPower
WS-I Attachment Profile
Supporting Attachment Profile in DataPower means all of the followings: 1. Verifying the incoming Soap Message with Attachments [SwA] is properly formed. 2. The fault message DataPower generates conforms to AP. 3. Any SwA messages DataPower generates conform to AP.
IBM Software Group | WebSphere software / DataPower
WS-I Basic/Basic Security Profile
These profiles can be applied to messages passing through a Web Service Proxy. The device can take a number of actions depending upon the results of the analysis. Shown here is the complete Conformance Policy object. This object is the result of using the Conformance interface offered by the Web Service Proxy Policy page (shown on the next page).
IBM Software Group | WebSphere software / DataPower
WS-I Basic/Basic Security Profile
The WS-I Conformance buttons on the Web Service Proxy Policy page offer the user the ability to configure these policy conformance checkers. Note also the Validate Conformance link to check the configuration of the service itself.
IBM Software Group | WebSphere software / DataPower
VLAN
The DataPower device can participate in a virtual LAN using the VLAN Sub-Interface. Note that implementing a VLAN on a physical Ethernet interface enables that interface, even if no real IP address has been assigned to it. VLAN can be configured in the default domain only.
IBM Software Group | WebSphere software / DataPower
PKIX Enhancements
Full PKIX certificate chain checking now applies to all uses of a validation credential, not just in SSL. Note that this will not apply to messages with multiple signature certificates.
IBM Software Group | WebSphere software / DataPower
DB2 v9 support
The device can now connect natively to a DB2 v9 database, running a range of platforms including z/OS. The DataPower device can use the XML capabilities built into v9 to: Insert XML directly into the DB Modify XML stored in the DB Query XML using XQuery & SQL Retrieve XML
IBM Software Group | WebSphere software / DataPower
NFS v4
Authentication protocol to use for this NFS mount. AUTH_SYS : Use the original system level authentication, based solely on IP address and host name. krb5 : Use Kerberos Version 5 for authentication of mounts, with no protection of the integrity or confidentiality of NFS data. krb5i : Use Kerberos Version 5 for authentication of mounts, with a secure hash to provide data integrity protection. krb5p : Use Kerberos Version 5 for authentication of mounts, with date confidentiality protection. Uses encryption to protect the data from being read by the network, in addition to using a secure hash to protect against undetected corruption by the network.
IBM Software Group | WebSphere software / DataPower
ICAP Enhancements
New Anti-Virus Processing Action eases configuration and use of this capability. Additional Host Types added. Policy can be set directly on the Action configuration page.
IBM Software Group | WebSphere software / DataPower
WSDM II
Enhanced query and status support through WSDM interface. Request Response
<s12:Header> <wsa:Action> http://docs.oasis-open.org/wsrf/2004/06/WSResourceProperties/GetResourceProperty </wsa:Action> <wsa:To s12:mustUnderstand="1"> https://127.0.0.1:5550/service/wsdm10 </wsa:To> <dpt:DomainDisambiguator>default</dpt:DomainDisambiguator> </s12:Header> <s12:Body> <wsrp:GetResourceProperty> dpm:status.system </wsrp:GetResourceProperty> </s12:Body> </s12:Envelope>
<s12:Body> <wsrp:GetResourcePropertyResponse xmlns:mows1-1="http://docs.oasis-open.org/wsdm/mows-2.xsd"> <status.system xmlns="http://www.datapower.com/schemas/manage ment"> <SystemUsage> <Interval>1000</Interval> <Load>37</Load> <WorkList>0</WorkList> </SystemUsage> </status.system> </wsrp:GetResourcePropertyResponse> </s12:Body>
IBM Software Group | WebSphere software / DataPower
WebSphere MQ Enhancements
Ability to use either SSL Proxy Profile or backward-compatible SSL Key/Cipher config Channel Heartbeat added Under-the-covers code refresh with full backward compatibility
IBM Software Group | WebSphere software / DataPower
RBM for CLI
RBM can now apply to CLI access. Note: Turning ON RBM for CLI and then clicking Apply causes RBM to extend to the CLI immediately. When RBM uses any Auth Method other that Local Usergroup, it is possible to configure Fallback Users to ensure ongoing access in the event of Auth Method failure. Admin user can be restricted to the Serial Port only for added security.
IBM Software Group | WebSphere software / DataPower
Configuration Comparison II
Enhanced Configuration Comparison includes ability to do the following: Determine Checkpoint Limit
Set Checkpoints per Application Domain Roll Back Application Domain to Checkpoint
Compare Checkpoint Config to Other Targets
IBM Software Group | WebSphere software / DataPower
IMS
IBM Software Group | WebSphere software / DataPower
IMS
IBM Software Group | WebSphere software / DataPower
IMS
IMS Connect Front Side Protocol Handler for accepting IMS-based client requests passing through a MultiProtocol Gateway
IMS Connect object for basic connection configuration values. Note Default Header tab for critical connection values.
MPGW IMS Destination URL with URL Builder help. Uses IMS Connect object.
IBM Software Group | WebSphere software / DataPower
Questions
You might also like
- Datapower Soa Appliances: AgendaDocument24 pagesDatapower Soa Appliances: AgendaRomarMroNo ratings yet
- Application Development for IBM WebSphere Process Server 7 and Enterprise Service Bus 7From EverandApplication Development for IBM WebSphere Process Server 7 and Enterprise Service Bus 7No ratings yet
- Rest PDFDocument17 pagesRest PDFlilianaNo ratings yet
- Web Sphere Log inDocument15 pagesWeb Sphere Log inkameshwar2004No ratings yet
- Tivoli Access Manager Problem Determination Using Logging and Tracing FeaturesDocument41 pagesTivoli Access Manager Problem Determination Using Logging and Tracing FeaturescotjoeyNo ratings yet
- ZQ410 Unit 2 Transcript: Configuring Components and Component ProcessesDocument37 pagesZQ410 Unit 2 Transcript: Configuring Components and Component ProcessesVhikram Lakshmi Narasimhan100% (1)
- Wasv8 131205081814 Phpapp02Document34 pagesWasv8 131205081814 Phpapp02srinivasrajaNo ratings yet
- Config SSO IBM WebSphere Portal and DominoDocument25 pagesConfig SSO IBM WebSphere Portal and DominoFernando Rodrigo DriNo ratings yet
- AIX Db2cmdDocument34 pagesAIX Db2cmdjames0834No ratings yet
- Front Cover: Introduction To Html5 and Javascript ProgrammingDocument24 pagesFront Cover: Introduction To Html5 and Javascript Programmingmoila_dNo ratings yet
- ZQ410 Unit 5 Transcript: Setting Up Server Security, Approvals, and Quality GatesDocument36 pagesZQ410 Unit 5 Transcript: Setting Up Server Security, Approvals, and Quality GatesVhikram Lakshmi Narasimhan100% (1)
- DataPower 70 NetworkingDocument39 pagesDataPower 70 NetworkingAdmin sdNo ratings yet
- Aix DetailsDocument46 pagesAix DetailsSaurav TripathyNo ratings yet
- Useful UNIX Commands For WebSphereDocument10 pagesUseful UNIX Commands For WebSphereoracleconsultant75No ratings yet
- JythonDocument25 pagesJythonjanaranjani.k100% (1)
- IDG - Referecne CLI Aug 2020 - Sri PDFDocument1,180 pagesIDG - Referecne CLI Aug 2020 - Sri PDFSridhara ShastryNo ratings yet
- Administrator's Guide DatastageDocument177 pagesAdministrator's Guide DatastageRasool ShaikNo ratings yet
- ZQ410 Unit 3 Transcript: Defining Deployments With Resources, Environments, and Application ProcessesDocument36 pagesZQ410 Unit 3 Transcript: Defining Deployments With Resources, Environments, and Application ProcessesVhikram Lakshmi NarasimhanNo ratings yet
- Websphereinterview 100725022705 Phpapp02Document193 pagesWebsphereinterview 100725022705 Phpapp02Venkatt PendyalaNo ratings yet
- AIX QuickStartDocument22 pagesAIX QuickStartDjGorkhali Khatri NepaliNo ratings yet
- Common SSL Configuration Issues and SolutionsDocument54 pagesCommon SSL Configuration Issues and SolutionsVamsi Krishna GarimellaNo ratings yet
- AIX Install GuideDocument78 pagesAIX Install Guidepleasantpartner100% (1)
- Clustering WebsphereDocument132 pagesClustering WebsphereMrperfect GuruNo ratings yet
- 5.2.1 AIX-ORA-AD-WAS INST c1939384Document240 pages5.2.1 AIX-ORA-AD-WAS INST c1939384choraNo ratings yet
- WAS 101 EditedDocument132 pagesWAS 101 EditedJateni joteNo ratings yet
- Quicksheet Aix Quickstart HTML PDFDocument35 pagesQuicksheet Aix Quickstart HTML PDFarm_max78No ratings yet
- Datastage 8.5 Installation GuideDocument503 pagesDatastage 8.5 Installation Guidenkrdwh6354100% (1)
- Tuning IBM AIX 5.3 and AIX 6.1 For Oracle DatabaseDocument37 pagesTuning IBM AIX 5.3 and AIX 6.1 For Oracle DatabasegasparsantibNo ratings yet
- ZQ410 Unit 1 Transcript: Designing Software Deployment and Deploying ApplicationsDocument21 pagesZQ410 Unit 1 Transcript: Designing Software Deployment and Deploying ApplicationsVhikram Lakshmi Narasimhan100% (1)
- Websphere 6 HandbookDocument598 pagesWebsphere 6 Handbookapi-3840237No ratings yet
- Power HaDocument726 pagesPower HadanilaixNo ratings yet
- IBM DataPower Operations Dashboard Provides Real-Time VisibilityDocument8 pagesIBM DataPower Operations Dashboard Provides Real-Time VisibilityRohit ChaubeyNo ratings yet
- Ricardo Tapia Cesena: Java Solution Architect / SR FULL STACK Java DeveloperDocument9 pagesRicardo Tapia Cesena: Java Solution Architect / SR FULL STACK Java Developerkiran2710No ratings yet
- WebSphere Application Server Installation Problem DeterminationDocument48 pagesWebSphere Application Server Installation Problem DeterminationdeisecairoNo ratings yet
- Problem Determination IBM Websphere ProductsDocument408 pagesProblem Determination IBM Websphere ProductskarthickmsitNo ratings yet
- Ibm Webshere Application Server Vertical ClusteringDocument34 pagesIbm Webshere Application Server Vertical ClusteringfilenetdirectorNo ratings yet
- Unit4 DevOps v2021Document69 pagesUnit4 DevOps v2021Benali Hamdi100% (1)
- WB812G Formation Ibm Business Process Manager Standard v8 5 Administration PDFDocument2 pagesWB812G Formation Ibm Business Process Manager Standard v8 5 Administration PDFCertyouFormationNo ratings yet
- Session16385 WAS TimeoutsDocument75 pagesSession16385 WAS Timeoutsshashank_w85m_312965No ratings yet
- WebSphere DataPower SOA Appliances and XSLT Part 1Document23 pagesWebSphere DataPower SOA Appliances and XSLT Part 1Gema Alcolado AyusoNo ratings yet
- CICS TS Application Programming GuideDocument317 pagesCICS TS Application Programming GuidekaiserbeitoNo ratings yet
- BASH Programming GuideDocument20 pagesBASH Programming GuideDenis MkwatiNo ratings yet
- Performance and Workload ManagementDocument34 pagesPerformance and Workload ManagementjaragiNo ratings yet
- API Connect On Docker PDFDocument19 pagesAPI Connect On Docker PDFSureshkumar SingampallikNo ratings yet
- Aix ReportDocument453 pagesAix Reportapi-3764104No ratings yet
- Linux AIX ComparisonDocument5 pagesLinux AIX ComparisondanilaixNo ratings yet
- Code Review JavaDocument3 pagesCode Review Javaanarki85No ratings yet
- Ford SOADocument41 pagesFord SOAapi-27629632No ratings yet
- 20 Spring BootDocument181 pages20 Spring BootAnil ChowdaryNo ratings yet
- Websphere v9Document3 pagesWebsphere v9Thirumala KakaniNo ratings yet
- Case Study - Tuning WebSphere Application Server V7 and V8 For PerformanceDocument25 pagesCase Study - Tuning WebSphere Application Server V7 and V8 For PerformanceAnandGNo ratings yet
- KSH - Korn Shell TutorialDocument5 pagesKSH - Korn Shell Tutorialramaniqbal123No ratings yet
- DB2 For Linux, Unix, and Windows: Version 11 HighlightsDocument161 pagesDB2 For Linux, Unix, and Windows: Version 11 HighlightsDucBonNo ratings yet
- WebSEAL Administration GuideDocument1,182 pagesWebSEAL Administration GuideRameez XaveriNo ratings yet
- Ibm Infosphere Admin CourseDocument4 pagesIbm Infosphere Admin CourseArpan GuptaNo ratings yet
- AIX Authentication To An LDAP Server PDFDocument67 pagesAIX Authentication To An LDAP Server PDFDavidNo ratings yet
- Master Repository Deployment Manager Configuration FilesDocument5 pagesMaster Repository Deployment Manager Configuration FilesKiran Kumar VakkalaNo ratings yet
- What Is WASDocument118 pagesWhat Is WASArunSiddesh KBNo ratings yet
- Retail Banking: by Prof Santosh KumarDocument30 pagesRetail Banking: by Prof Santosh KumarSuraj KumarNo ratings yet
- Quantitative Analysis For Business Midterm - SolutionDocument6 pagesQuantitative Analysis For Business Midterm - SolutionYiPingHungNo ratings yet
- Chapter 11-Facility Location DecisionsDocument23 pagesChapter 11-Facility Location Decisionsমেহনাজ তাবাসসুম মিরুNo ratings yet
- AquaponicsDocument5 pagesAquaponicsapi-346838508No ratings yet
- (Springer Texts in Statistics) Peter K. Dunn, Gordon K. Smyth - Generalized Linear Models With Examples in R-Springer (2018)-228-258Document31 pages(Springer Texts in Statistics) Peter K. Dunn, Gordon K. Smyth - Generalized Linear Models With Examples in R-Springer (2018)-228-258Huy NguyenNo ratings yet
- Binary Search TreeDocument47 pagesBinary Search TreeAman Pushpinder BirdiNo ratings yet
- Contiki RPL TimersDocument7 pagesContiki RPL TimersĐông thành đạiNo ratings yet
- Blue Ocean Vs Five ForcesDocument1 pageBlue Ocean Vs Five ForcesMuffaddal OanaliNo ratings yet
- Health Informatics - An International Journal (HIIJ)Document2 pagesHealth Informatics - An International Journal (HIIJ)hiijjournalNo ratings yet
- Ecological Design, A New CritiqueDocument12 pagesEcological Design, A New CritiqueBerrak Kırbaş Akyürek0% (1)
- Norcold 462 Combination ControlDocument31 pagesNorcold 462 Combination ControlJohn SmithNo ratings yet
- Rule of Ultra Vires With Respect To The Power of A CompanyDocument19 pagesRule of Ultra Vires With Respect To The Power of A CompanyAbbas HaiderNo ratings yet
- Client-Mutiara D'angkasaDocument11 pagesClient-Mutiara D'angkasaSyukri SupanganNo ratings yet
- Answer Sheet Grade 12 Online/BlendedDocument3 pagesAnswer Sheet Grade 12 Online/BlendedMark Earvin CervantesNo ratings yet
- Diagrama P ID Ammonium Nitrate Fertilizer Production Unit PDFDocument1 pageDiagrama P ID Ammonium Nitrate Fertilizer Production Unit PDFYecid Fabian AlvaradoNo ratings yet
- Architectural Programming and Analysis Space PlanningDocument17 pagesArchitectural Programming and Analysis Space PlanningFranz Joseph Natino NicerioNo ratings yet
- CPT-720 Portable Terminal Power and Environmental SpecsDocument2 pagesCPT-720 Portable Terminal Power and Environmental SpecsSantoso LeonardiNo ratings yet
- CH 6Document16 pagesCH 6tareqkh1No ratings yet
- TPMDocument58 pagesTPMVinodh ManiNo ratings yet
- Wung Jessica ResumeDocument1 pageWung Jessica Resumeapi-418022315No ratings yet
- Determinants of Green Competitive AdvantageDocument23 pagesDeterminants of Green Competitive AdvantageInsiya AbbasNo ratings yet
- Git-Checkout (1) : Git Commit (-A - Interactive - Patch) (-S) (-V) (-U) ( - Amend)Document10 pagesGit-Checkout (1) : Git Commit (-A - Interactive - Patch) (-S) (-V) (-U) ( - Amend)Daniela CrisNo ratings yet
- Sample Paper 01 - Dropper NEET 2024 - Botany - Raja Sir - Vijay Gupta - Questions 2Document7 pagesSample Paper 01 - Dropper NEET 2024 - Botany - Raja Sir - Vijay Gupta - Questions 2Raghuram SheshadriNo ratings yet
- KP Astrology-Who Will Marry To Whom-1Document4 pagesKP Astrology-Who Will Marry To Whom-1rahul106No ratings yet
- GE8151 Python Programming Unit 3 Question Bank With Sample CodeDocument25 pagesGE8151 Python Programming Unit 3 Question Bank With Sample CodeN.VivekananthamoorthyNo ratings yet
- Board Resolution IOBDocument1 pageBoard Resolution IOBrambo_ramanNo ratings yet
- Contextualized-Teacher-Resource-in-Arts-2 v3 PDFDocument4 pagesContextualized-Teacher-Resource-in-Arts-2 v3 PDFDonna Mae Castillo KatimbangNo ratings yet
- DSL Oral QuestionDocument5 pagesDSL Oral QuestionAmit SangaleNo ratings yet
- RDS Case Study: Preterm Infant with Respiratory DistressDocument4 pagesRDS Case Study: Preterm Infant with Respiratory DistressE.R.ONo ratings yet
- Research Paper Worksheet Middle SchoolDocument5 pagesResearch Paper Worksheet Middle Schoolorotmbbkf100% (1)