Professional Documents
Culture Documents
4471 Mobile Device Security Handout
Uploaded by
DamnGo0d0 ratings0% found this document useful (0 votes)
118 views32 pagesdownloaded from internet
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentdownloaded from internet
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
118 views32 pages4471 Mobile Device Security Handout
Uploaded by
DamnGo0ddownloaded from internet
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 32
Mobile Device Security
Adam C. Champion and Dong Xuan
CSE 4471: Information Security
Based on materials from Tom Eston (SecureState),
Apple, Android Open Source Project, and William Enck (NCSU)
Organization
Quick Overview of Mobile Devices
Mobile Threats and Attacks
Countermeasures
Overview of Mobile Devices
Mobile computers:
Mainly smartphones, tablets
Sensors: GPS, camera,
accelerometer, etc.
Computation: powerful
CPUs ( 1 GHz, multi-core)
Communication: cellular/4G,
Wi-Fi, near field
communication (NFC), etc.
Many connect to cellular
networks: billing system
Cisco: 7 billion mobile
devices will have been sold
by 2012 [1]
Organization
Organization
Quick Overview of Mobile Devices
Mobile Threats and Attacks
Countermeasures
Mobile Threats and Attacks
Mobile devices make attractive targets:
People store much personal info on them: email,
calendars, contacts, pictures, etc.
Sensitive organizational info too
Can fit in pockets, easily lost/stolen
Built-in billing system: SMS/MMS (mobile operator),
in-app purchases (credit card), etc.
Many new devices have near field communications (NFC),
used for contactless payments, etc.
Your device becomes your credit card
Location privacy issues
NFC-based billing system vulnerabilities
Mobile Device Loss/Theft
Many mobile devices lost, stolen each year
113 mobile phones lost/stolen every minute in the U.S.
[15]
56% of us misplace our mobile phone or laptop each
month [15]
Lookout Security found $2.5 billion worth of phones
in 2011 via its Android app [16]
Symantec placed 50 lost smartphones throughout
U.S. cities [17]
96% were accessed by finders
80% of finders tried to access sensitive data on phone
Device Malware
iOS malware: very little
Juniper Networks: Major increase in Android
malware from 2010 to 2011 [18]
Android malware growth keeps increasing ($$$)
Main categories: [19]
Trojans
Monitoring apps/spyware
Adware
Botnets
Well look at notable malware examples
Device Search and Seizure
People v. Diaz: if youre arrested, police can
search your mobile device without warrant [26]
Rationale: prevent perpetrators destroying evidence
Quite easy to break the law (overcriminalization) [27]
Crime severity: murder, treason, etc. vs. unpaid citations
Tens of thousands of offenses on the books [26]
Easy for law enforcement to extract data from
mobile devices (forensics) [28]
Location Disclosure
MAC, Bluetooth Addresses, IMEI, IMSI etc. are
globally unique
Infrastructure based mobile communication
Peer-t-Peer ad hoc mobile communication
Organization
Quick Overview of Mobile Devices
Mobile Threats and Attacks
Countermeasures
Mobile Access Control
Very easy for attacker to control a mobile device
if he/she has physical access
Especially if theres no way to authenticate user
Then device can join botnet, send SMS spam, etc.
Need access controls for mobile devices
Authentication, authorization, accountability
Authentication workflow:
Request access
Supplication (user provides identity, e.g., John Smith)
Authentication (system determines user is John)
Authorization (system determines what John can/cannot do)
Authentication: Categories
Authentication generally based on:
Something supplicant knows
Password/passphrase
Unlock pattern
Something supplicant has
Magnetic key card
Smart card
Token device
Something supplicant is
Fingerprint
Retina scan
Authentication: Passwords
Cheapest, easiest form of authentication
Works well with most applications
Also the weakest form of access control
Lazy users passwords: 1234, password, letmein, etc.
Can be defeated using dictionary, brute force attacks
Requires administrative controls to be effective
Minimum length/complexity
Password aging
Limit failed attempts
Authentication: Smart Cards/
Security Tokens
More expensive, harder to implement
Vulnerability: prone to loss or theft
Very strong when combined with another form
of authentication, e.g., a password
Does not work well in all applications
Try carrying a smart card in addition to a mobile
device!
Authentication: Biometrics
More expensive/harder to implement
Prone to error:
False negatives: not authenticate authorized user
False positives: authenticate unauthorized user
Strong authentication when it works
Does not work well in all applications
Fingerprint readers becoming more common on
mobile devices (Atrix 4G)
Authentication: Pattern Lock
Swipe path of length
49 on 3 x 3 grid
Easy to use, suitable for
mobile devices
Problems: [30]
389,112 possible patterns;
(456,976 possible patterns
for 4-char case-insensitive
alphabetic password!)
Attacker can see pattern
from finger oils on screen
Authentication: Comparison
Passwords Smart Cards Biometrics Pattern Lock
Security Weak Strong Strong Weak
Ease of Use Easy Medium Hard Easy
Implementation Easy Hard Hard Easy
Works for phones Yes No Possible Yes
Deeper problem: mobile devices are designed with single-user
assumption
DiffUser (1)
Current smartphone access
control focus: 1 user (admin)
Hard to achieve fine-grained
mobile device management:
Control app installation/gaming
Parental controls
Lend phone to friend
We design DiffUser,
differentiated user access
control model [31]
Different users use smartphone
in different contexts
User classification: admin,
normal, guest
Smartphone
Privileges
Admin Normal Guest
Personal
Info
SMS
Contacts
Resource
Access
WiFi Limit
GPS Limit
Bluetooth Limit
Apps
App
Install
Limit
Sensitive
Apps
Limit
Source: [31], Table 1.
DiffUser (2)
Implement our system on Android using Java
Override Androids Home Activity for multi-user
authentication, profile configuration
Source: [31], Figure 2. From left to right: normal user screen;
user login and authentication; user profile configuration.
Mobile Device Information Leakage
Types of mobile device information sources:
Internal to device (e.g., GPS location, IMEI, etc.)
External sources (e.g., CNN, Chase Bank, etc.)
Third-party mobile apps can leak info to external sources [32]
Send out device ID (IMEI/EID), contacts, location, etc.
Apps ask permission to access such info; users can ignore!
Apps can intercept info sent to a source, send to different destination!
Motives:
Monitor employees activity using accelerometers (cited in [32])
Ads, market research (include user location, behavior, etc.)
Malice
How do we protect against such information leakage?
Information Flow Tracking (IFT)
IFT tracks each information
flow among internal,
external sources
Each flow is tagged, e.g.,
untrusted
Tag propagated as information
flows among internal, external
sources
Sound alarm if data sent to
third party
Challenges
Reasonable runtime, space
overhead
Many information sources
Information leakage on mobile devices
trusted
untrusted
TaintDroid
Enck et al., OSDI 2010 [32]
IFT system on Android 2.1
System firmware (not app)
Modifies Androids Dalvik
VM, tracks info flows across
methods, classes, files
Tracks the following info:
Sensors: GPS, camera,
accelerometer, microphone
Internal info: contacts, phone
#, IMEI, IMSI, Google acct
External info: network, SMS
Notifies user of info leakage
Systems and Internet Infrastructure Security Laboratory (SIIS) Page
TaintDroid
TaintDroid is a system-wide integration of taint
tracking into the Android platform
Variable tracking throughout Dalvik VM environment
Patches state after native method invocation
Extends tracking between applications and to storage
TaintDroid is a rmware modication, not an app
6
NetworkInterface
NativeSystemLibraries
Virtual
Machine
Virtual
Machine
ApplicationCode ApplicationCode Msg
SecondaryStorage
Message-level tracking
Variable-level
tracking
Method-level
tracking
File-level
tracking
Source: [33]
D2Taint (1)
Motivation
Mobile device users access many information sources,
e.g.
Online banks (like Chase)
Social networking (like Facebook)
News websites (like CNN)
Different info sources: different sensitivity levels
Applications diverse variable access patterns
challenge tag propagation
Users info source access patterns change over time
Need to track many information flows with moderate
space, runtime overhead
D2Taint (2)
Differentiated and dynamic tag strategy [34]
Information sources partitioned into differentiated
classes based on arbitrary criteria
Example (criterion=info sensitivity level):
Classes: highly sensitive, moderately sensitive,
not sensitive
Sources: Chase highly sensitive; Facebook
moderately sensitive; CNN not sensitive
Each classs sources stored in a location info table
Source indices (0, 1, ) source names (chase.com, )
D2Taint (3)
D2Taint uses fixed length tag (32 bits)
Tag includes segments corresponding to classes
Each segment stores representations of information sources in
its class
Representation: info sources class table index
Note: source table grows over time
Information source representation does not uniquely ID source
D2Taint (4)
D2Taint implemented on Android 2.2, Nexus One
smartphones
Evaluate D2Taint: 84 popular free apps from
Google Play
71/84 leak some data to third parties
E.g., Android system version, screen resolution
Often, third parties are cloud computing services
TaintDroid cannot detect external data leakage
1 bit in tag for network
Cannot track multiple external sources at once
12/84 leak highly sensitive data, e.g., IMEI/EID
(detected by both D2Taint, TaintDroid)
D2Taint has overhead similar to TaintDroids
Location Privacy Protection
Strong regulation
Corporate
Individual
Dynamic MAC and Bluetooth addresses?
Collision
How often to change?
Proxy-based communications
Dummy device as proxy
Group communications
Summary
Mobile devices are increasingly popular
There are many threats and attacks against
mobile devices, e.g., loss/theft, sensitive
information leakage, and location privacy
compromise
Mobile access control, information leakage
protection, and location privacy protection, etc.
References (1)
1. Cisco, Cisco Visual Networking Index: Global Mobile Data Traffic Forecast Update, 2011
2016, 14 Feb. 2012, http://www.cisco.com/en/US/solutions/collateral/ns341/ns525/ns537/
ns705/ns827/white_paper_c11-520862.html
2. Samsung, Exynos 5 Dual, 2012, http://www.samsung.com/global/business/semiconductor/
product/application/detail?productId=7668&iaId=2341
3. Nielsen Co., Two Thirds of All New Mobile Buyers Now Opting for Smartphones, 12 Jul.
2012, http://blog.nielsen.com/nielsenwire/online_mobile/two-thirds-of-new-mobile-buyers-
now-opting-for-smartphones/
4. K. De Vere, iOS leapfrogs Android with 410 million devices sold and 650,000 apps, 24 Jul.
2012, http://www.insidemobileapps.com/2012/07/24/ios-device-sales-leapfrog-android-with-
410-million-devices-sold/
5. K. Haslem, Macworld Expo: Optimised OS X sits on versatile Flash, 12 Jan. 2007,
Macworld, http://www.macworld.co.uk/ipod-itunes/news/index.cfm?newsid=16927
6. Wikipedia, iOS, updated 2012, http://en.wikipedia.org/wiki/iOS
7. Apple Inc., iPhone Developer University Program,
http://developer.apple.com/iphone/program/university.html
8. Apple Inc, iOS Security, http://images.apple.com/ipad/business/docs/
iOS_Security_May12.pdf
9. Android Open Source Project, Android Security Overview, http://source.android.com/tech/
security/index.html
Presentation organization inspired by T. Eston, Android vs. iOS Security Showdown, 2012,
http://www.slideshare.net/agent0x0/the-android-vs-apple-ios-security-showdown
References (2)
10. A. Rubin, 15 Feb. 2012, https://plus.google.com/u/0/112599748506977857728/
posts/Btey7rJBaLF
11. H. Lockheimer, Android and Security, 2 Feb. 2012, http://googlemobile.blogspot.com/
2012/02/android-and-security.html
12. Android Open Source Project, http://developer.android.com/about/dashboards/index.html
13. M. DeGusta, Android Orphans: Visualizing a Sad History of Support, 26 Oct. 2011,
http://theunderstatement.com/post/11982112928/android-orphans-visualizing-a-sad-history-
of-support
14. http://opensignalmaps.com/reports/fragmentation.php
15. http://www.micro-trax.com/statistics `
16. Lookout, Inc., Mobile Lost and Found, 2012, https://www.mylookout.com/resources/
reports/mobile-lost-and-found/
17. K. Haley, Introducing the Smartphone Honey Stick Project, 9 Mar. 2012,
http://www.symantec.com/connect/blogs/introducing-symantec-smartphone-honey-stick-
project
18. Juniper Networks, Inc., Global Research Shows Mobile Malware Accelerating, 15 Feb.
2012, http://newsroom.juniper.net/press-releases/global-research-shows-
mobile-malware-accelerating-nyse-jnpr-0851976
References (3)
19. F-Secure, Mobile Threat Report Q2 2012, 7 Aug. 2012, http://www.slideshare.net/fsecure/
mobile-threat-report-q2-2012
20. http://nakedsecurity.sophos.com/2012/04/12/a ndroid-malware-angry-birds-space-game/
21. Via Forensics LLC, Forensic Security Analysis of Google Wallet, 12 Dec. 2011,
https://viaforensics.com/mobile-security/forensics-security-analysis-google-wallet.html
22. Proxmark, http://www.proxmark.org/
23. libnfc, http://www.libnfc.org
24. D. Goodin, Android, Nokia smartphone security toppled by Near Field Communication hack,
25 Jul. 2012, http://arstechnica.com/security/2012/07/android-nokia-smartphone-hack/
25. B. Andersen, Australian admits creating first iPhone virus, 10 Nov. 2009,
http://www.abc.net.au/news/2009-11-09/australian-admits-creating-first-iphone-virus/1135474
26. R. Radia, Why you should always encrypt your smartphone, 16 Jan. 2011,
http://arstechnica.com/gadgets/2011/01/why-you-should-always-encrypt-your-smartphone/
27. Heritage Foundation, Solutions for America: Overcriminalization, 17 Aug. 2010,
http://www.heritage.org/research/reports/2010/08/overcriminalization
28. Wikipedia, http://en.wikipedia.org/wiki/Mobile_device_forensics
29. C. Quentin, http://www.slideshare.net/cooperq/your-cell-phone-is-covered-in-spiders
References (4)
30. A. J. Aviv, K. Gibson, E. Mossop, M. Blaze, and A. M. Smith, Smudge Attacks on
Smartphone Touch Screens, Proc. USENIX WOOT, 2010.
31. X. Ni, Z. Yang, X. Bai, A. C. Champion, and Dong Xuan, DiffUser: Differentiated User
Access Control on Smartphones, Proc. IEEE Intl. Workshop on Wireless and Sensor
Networks Security (WSNS), 2009.
32. W. Enck, P. Gilbert, B.-G. Chun, L. P. Cox, J. Jung, P. McDaniel, and A. N. Sheth,
TaintDroid: An Information-Flow Tracking System for Realtime Privacy Monitoring on
Smartphones, Proc. USENIX OSDI, 2010, http://appanalysis.org
33. W. Enck, P. Gilbert, B.-G. Chun, L. P. Cox, J. Jung, P. McDaniel, and A. N. Sheth,
TaintDroid: An Information-Flow Tracking System for Realtime Privacy Monitoring on
Smartphones, http://static.usenix.org/event/osdi10/tech/slides/enck.pdf
34. B. Gu, X. Li, G. Li, A. C. Champion, Z. Chen, F. Qin, and D. Xuan, D2Taint:
Differentiated and Dynamic Information Flow Tracking on Smartphones for Numerous
Data Sources, Technical Report, 2012.
You might also like
- Digital ForensicsDocument32 pagesDigital ForensicsKaashviNo ratings yet
- Remote Car Control via Mobile PhoneDocument15 pagesRemote Car Control via Mobile PhoneVincent KorieNo ratings yet
- GSM Sniffing - The TruthDocument2 pagesGSM Sniffing - The TruthSargoBallz100% (1)
- Lte Sim LockDocument23 pagesLte Sim LockmbozhoNo ratings yet
- GSMA - Report On Overaly SIM CardsDocument2 pagesGSMA - Report On Overaly SIM CardsWalu JohnNo ratings yet
- Mobile Phone Privacy ReportDocument106 pagesMobile Phone Privacy Reportamhosny64No ratings yet
- Pentesting Iphone ApplicationsDocument31 pagesPentesting Iphone ApplicationssatishbNo ratings yet
- Batman 017Document229 pagesBatman 017rehman khanNo ratings yet
- How A Criminal Might Infiltrate Your NetworkDocument15 pagesHow A Criminal Might Infiltrate Your NetworkHa GiangNo ratings yet
- ASA 019-23-0001 Potential Remote Code Execution On Opteva TerminalsDocument2 pagesASA 019-23-0001 Potential Remote Code Execution On Opteva TerminalsCatalin Cimpanu [ZDNet]No ratings yet
- Amlogic Burn Card Maker and How To Use ItDocument5 pagesAmlogic Burn Card Maker and How To Use Its.s.r.k.m. gupta100% (1)
- Smart Card Attacks Theory and PracticeDocument11 pagesSmart Card Attacks Theory and PracticeRicardo Jose Sarmiento MejiasNo ratings yet
- Writing ChecksDocument19 pagesWriting Checksapi-325621104No ratings yet
- Digital Code Lock System - WWW - BooknstuffDocument10 pagesDigital Code Lock System - WWW - Booknstuffyampire100% (2)
- Light Blue Touchpaper Blog Archive Chip and Skim: Cloning EMV Cards With The Pre-Play AttackDocument8 pagesLight Blue Touchpaper Blog Archive Chip and Skim: Cloning EMV Cards With The Pre-Play AttackJohn MooreNo ratings yet
- TMD Security Deep Insert Skimming and CPP Overview June 2016Document14 pagesTMD Security Deep Insert Skimming and CPP Overview June 2016rdfv rNo ratings yet
- ACTIVIST'S GUIDE TO INFORMATION SECURITYDocument19 pagesACTIVIST'S GUIDE TO INFORMATION SECURITYDante IrreraNo ratings yet
- CAR SNATCHING AND SECURITY TIPSDocument13 pagesCAR SNATCHING AND SECURITY TIPSorioghenebruruNo ratings yet
- Mass Snooping Fake Mobile Towers 'Uncovered in UK' - BBC NewsDocument3 pagesMass Snooping Fake Mobile Towers 'Uncovered in UK' - BBC NewsedgeNo ratings yet
- Computer Security Audit ChecklistDocument5 pagesComputer Security Audit ChecklistPetrrNo ratings yet
- MAD Full Manual PDFDocument182 pagesMAD Full Manual PDFYashNo ratings yet
- Cyber Security Password Attacks and ProtectionsDocument16 pagesCyber Security Password Attacks and Protectionssignup onsitesNo ratings yet
- Silence Group Targets Banks with Evolving ToolsetDocument87 pagesSilence Group Targets Banks with Evolving ToolsetJuanDevelop GiraldoNo ratings yet
- Us 13 Nohl Rooting SIM Cards Slides PDFDocument21 pagesUs 13 Nohl Rooting SIM Cards Slides PDFMephistoMarcanNo ratings yet
- WP Pos Ram Scraper MalwareDocument97 pagesWP Pos Ram Scraper MalwareAnonymous eXujyZNo ratings yet
- Secure iOS Application DevelopmentDocument20 pagesSecure iOS Application DevelopmentNicks FirkeNo ratings yet
- MB1500 Operator ManualDocument172 pagesMB1500 Operator Manualinkpusher4uNo ratings yet
- Android Permissions: User Attention, Comprehension, and BehaviorDocument14 pagesAndroid Permissions: User Attention, Comprehension, and BehaviorDeepuNo ratings yet
- Skimming AttacksDocument9 pagesSkimming AttacksNaratama SahalaNo ratings yet
- Combine Seminar On HackingDocument20 pagesCombine Seminar On HackingDr. Hitesh MohapatraNo ratings yet
- Computer Hacking Forensic Investigator Course Content: Module 01: Computer Forensics in Today's WorldDocument96 pagesComputer Hacking Forensic Investigator Course Content: Module 01: Computer Forensics in Today's WorldJuwono SulisNo ratings yet
- Shodan Comandos PrincipalesDocument1 pageShodan Comandos PrincipalesmayraNo ratings yet
- Detection and Remediation of Attack PDFDocument4 pagesDetection and Remediation of Attack PDFOlexander PylypenkoNo ratings yet
- How IP Spoofing WorksDocument37 pagesHow IP Spoofing WorksDilan D Almeida100% (2)
- Secure Your Android Based Smartphones enDocument10 pagesSecure Your Android Based Smartphones enKevinNo ratings yet
- Atm Surveillance SystemDocument6 pagesAtm Surveillance Systemjoshna guptaNo ratings yet
- Automated Teller Machine (ATM)Document31 pagesAutomated Teller Machine (ATM)pinkranger-4100% (1)
- Hacking and Networking ComponentsDocument14 pagesHacking and Networking ComponentsKhawaja SabbaqNo ratings yet
- BankingDocument8 pagesBankingpriya chaudhariNo ratings yet
- Car TradingDocument27 pagesCar TradingDenis NduvaNo ratings yet
- APSDocument52 pagesAPSneeraj kumar singhNo ratings yet
- One Sim Card ManualDocument16 pagesOne Sim Card ManualUkah FranklinNo ratings yet
- Cell Phone TrackingDocument10 pagesCell Phone TrackingRahulNo ratings yet
- ICIT Hacking CyborgsDocument56 pagesICIT Hacking Cyborgsfreiheit137174No ratings yet
- Location Leaks On The GSM Air InterfaceDocument13 pagesLocation Leaks On The GSM Air InterfacessthakurNo ratings yet
- Smart Cards Enable Wireless Value and SecurityDocument48 pagesSmart Cards Enable Wireless Value and SecurityZalak RakholiyaNo ratings yet
- Linux Mint Training GuideDocument24 pagesLinux Mint Training Guidefarai muzondoNo ratings yet
- Mobile Protection: Smartphone SecurityDocument36 pagesMobile Protection: Smartphone Securitysunny kentNo ratings yet
- How To Save A Webpage As A PDF - SmallpdfDocument9 pagesHow To Save A Webpage As A PDF - SmallpdfHzl ZlhNo ratings yet
- PL-2303 USB to Serial Install GuideDocument9 pagesPL-2303 USB to Serial Install GuideGraham WellingtonNo ratings yet
- Medeco Price Book 2012Document192 pagesMedeco Price Book 2012Security Lock DistributorsNo ratings yet
- Cash Repl. Images - NH-1800CEManualDocument215 pagesCash Repl. Images - NH-1800CEManualAhmed Mostafa AbdelRahmanNo ratings yet
- Drivers License Number Redaction SampleDocument3 pagesDrivers License Number Redaction SamplekysucoNo ratings yet
- Catalogo MauerDocument176 pagesCatalogo Mauermikehcs100% (1)
- Mind-blowing Signal 101 Guide for Beginners and Experts: Unravel the Best Signal Private Messenger Tips for Secured Calls and ChatsFrom EverandMind-blowing Signal 101 Guide for Beginners and Experts: Unravel the Best Signal Private Messenger Tips for Secured Calls and ChatsNo ratings yet
- Your Personal Information Is At Risk: A Guide For Protecting YourselfFrom EverandYour Personal Information Is At Risk: A Guide For Protecting YourselfNo ratings yet
- Research On CommandsDocument1,120 pagesResearch On CommandsDamnGo0dNo ratings yet
- Important Power Shell CommandsDocument18,778 pagesImportant Power Shell CommandsDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- Soft ArcDocument214 pagesSoft ArcDamnGo0dNo ratings yet
- FAQs On Partial Withdrawal RequestDocument4 pagesFAQs On Partial Withdrawal RequestarjunNo ratings yet
- Design and Implementation of Secure Electronic Passport SystemDocument8 pagesDesign and Implementation of Secure Electronic Passport SystemManish Kumar Reddy NangiNo ratings yet
- Realpdf VDocument1 pageRealpdf VDiana WashingtonNo ratings yet
- Biometric Attendance Monitoring With Payroll System (BAMAPS)Document90 pagesBiometric Attendance Monitoring With Payroll System (BAMAPS)Shane Emerald67% (3)
- Annex C - Checklist of Requirements and Omnibus Sworn StatementDocument2 pagesAnnex C - Checklist of Requirements and Omnibus Sworn StatementGian Carlo RebutocNo ratings yet
- JWT Social Auth with ASP.NET Core & Xamarin EssentialsDocument10 pagesJWT Social Auth with ASP.NET Core & Xamarin EssentialshsuyipNo ratings yet
- UntitledDocument15 pagesUntitledSarrie BerangoNo ratings yet
- The Impact of Investigated The Current System of ID-card Processing System in IMT EnuguDocument35 pagesThe Impact of Investigated The Current System of ID-card Processing System in IMT EnuguIbrahim BasiruNo ratings yet
- Im21 Sponsorship DeclarationDocument2 pagesIm21 Sponsorship DeclarationvishnuNo ratings yet
- 5G Security Analysis Threats SolutionsDocument7 pages5G Security Analysis Threats SolutionssplouvrosNo ratings yet
- File Migrator For Sharepoint User Guide Userguide 3140Document121 pagesFile Migrator For Sharepoint User Guide Userguide 3140Claudiu MireaNo ratings yet
- UID DDSVP Committee Report v1.0Document25 pagesUID DDSVP Committee Report v1.0Akhil K AshokNo ratings yet
- Bh558 458 Brochure Final Web 4th SepDocument4 pagesBh558 458 Brochure Final Web 4th SepPascu DanNo ratings yet
- APSRTC Reservation VoucherDocument1 pageAPSRTC Reservation VoucherprasannaNo ratings yet
- Sec Brksec-3540 PDFDocument94 pagesSec Brksec-3540 PDFSayaOtanashiNo ratings yet
- REVENUE COMPLAINTS Upto - 20091031Document57 pagesREVENUE COMPLAINTS Upto - 20091031api-25891275No ratings yet
- Completed Transcript 3789320Document3 pagesCompleted Transcript 3789320pfull7No ratings yet
- HACKDocument7 pagesHACKramarao pagadala75% (4)
- Case Study Naphtha Cracker ProjectDocument4 pagesCase Study Naphtha Cracker ProjectErica LindseyNo ratings yet
- Registration Report SSCDocument3 pagesRegistration Report SSCKhadar basha lNo ratings yet
- Mas NSEPDocument244 pagesMas NSEPRishit Sriwastava100% (1)
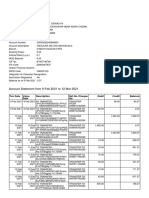
- Account Statement From 9 Feb 2021 To 12 Mar 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument5 pagesAccount Statement From 9 Feb 2021 To 12 Mar 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceABHINAV DEWALIYANo ratings yet
- Identification and Authentication Techniques: Midterm QuestionsDocument7 pagesIdentification and Authentication Techniques: Midterm QuestionsFarooqNo ratings yet
- Verify Foreign LicenseDocument10 pagesVerify Foreign Licensemamun22ndNo ratings yet
- Dated: 1 April 2019 To: Philippine Statistics Authority - Iloilo Subject: Authorization LetterDocument1 pageDated: 1 April 2019 To: Philippine Statistics Authority - Iloilo Subject: Authorization LetterIvy Balandra0% (1)
- AGCInfoSec2008 Private ProfilesDocument80 pagesAGCInfoSec2008 Private ProfilesFerit KanNo ratings yet
- Chapter 3 - Data Security &integrityDocument18 pagesChapter 3 - Data Security &integrityGetnete degemuNo ratings yet
- NishaDocument1 pageNishahotelmmhussainganjNo ratings yet
- Promlistmbbs OmDocument146 pagesPromlistmbbs OmAsad ullahNo ratings yet